Bug bounty programs are a game-changer in the world of cybersecurity. By harnessing the power of crowdsourcing, organizations can tap into the collective expertise of security researchers around the globe to strengthen their cyber defenses.
These programs, also known as vulnerability rewards programs, offer monetary incentives to ethical hackers for uncovering and reporting vulnerabilities in a company’s systems. It’s a win-win situation, where organizations benefit from the knowledge and skills of the broader security community, while researchers are rewarded for their efforts.
Crowdsourcing cybersecurity through bug bounties allows organizations to access a diverse pool of talent and perspectives. This enables them to identify a wider range of vulnerabilities and potential attack vectors, ultimately leading to stronger defenses against cyber threats.
Key Takeaways:
- Bug bounty programs leverage the expertise of security researchers to identify and report vulnerabilities.
- Ethical hackers are rewarded monetarily for their efforts in finding and disclosing bugs.
- Crowdsourcing cybersecurity through bug bounties allows organizations to tap into a global talent pool.
- Bug bounties promote collaboration between organizations and ethical hackers.
- Bug bounty programs contribute to the strengthening of cybersecurity defenses.
The Benefits of Bug Bounty Programs
Bug bounty programs offer several benefits to organizations. Firstly, they provide access to a diverse pool of security researchers who have different backgrounds, perspectives, and expertise. This helps organizations to identify a wider range of vulnerabilities and potential attack vectors.
Additionally, bug bounties promote collaboration between organizations and ethical hackers, creating a mutually beneficial relationship where both parties work together to improve cybersecurity. By incentivizing researchers with rewards, organizations encourage sustained engagement and build long-term relationships with skilled hackers.
“Bug bounty programs provide a platform for organizations to collaborate with ethical hackers from around the world, leveraging their collective expertise to strengthen cybersecurity defenses.”
Bug bounty programs also contribute to the strengthening of cybersecurity defenses by continuously identifying and addressing vulnerabilities. The collaborative nature of bug bounties enables organizations to stay ahead of potential threats and proactively enhance their security posture.
Enhanced Security Expertise and Perspective
Bug bounty programs bring together security researchers with diverse backgrounds and expertise, allowing organizations to tap into a broader range of knowledge and skills. This facilitates the identification of vulnerabilities that may have been overlooked by internal security teams. By embracing the collective wisdom of ethical hackers, organizations gain a fresh perspective on their systems and can better understand potential attack vectors.
Collaboration and Knowledge Sharing
In bug bounty programs, organizations and ethical hackers collaborate closely to identify and fix vulnerabilities. This partnership fosters knowledge sharing and promotes a culture of cybersecurity awareness. By working together, organizations can gain insights into emerging threats and adopt proactive measures to protect their networks, systems, and data.
Continuous Improvement of Cybersecurity Defenses
Bug bounties provide a continuous feedback loop for organizations to strengthen their cybersecurity defenses. As researchers find and report vulnerabilities, organizations can take swift action to address them, making their systems more resilient against potential attacks. Regular engagement with ethical hackers through bug bounty programs allows organizations to stay proactive, adapt to evolving threats, and ensure that their security measures are up to date.
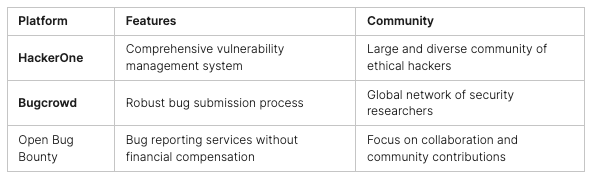
Selecting Bug Bounty Platforms and Companies
When implementing a bug bounty program, organizations have the option to choose from various bug bounty platforms and companies. These platforms provide the necessary infrastructure for managing bug bounty programs and offer communication channels for researchers to submit vulnerability reports and interact with organizations. Two popular bug bounty platforms are HackerOne and Bugcrowd, which have built a reputation for their robust services and large communities of ethical hackers.
In addition to bug bounty platforms, organizations can also run their bug bounty programs independently. This gives them more control over the program structure and requirements. However, running an independent bug bounty program requires dedicated resources and expertise to manage the program effectively.
Alternatively, organizations can opt to utilize open bug bounty platforms like Open Bug Bounty. These platforms offer bug reporting services without requiring financial compensation. Open Bug Bounty focuses on building a collaborative community and provides opportunities for researchers to contribute to the security of smaller organizations that may not have the resources to run their bug bounty programs.
Benefits of Bug Bounty Platforms and Companies:
- Infrastructure for managing bug bounty programs
- Communication channels for researchers and organizations
- Diverse communities of ethical hackers
- Access to a wide range of expertise and perspectives
- Opportunity for collaboration and knowledge exchange
Comparison of Bug Bounty Platforms and Open Bug Bounty:
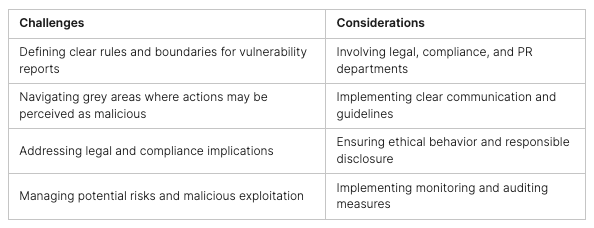
Challenges and Considerations in Bug Bounty Programs
Implementing a bug bounty program presents organizations with a unique set of challenges that must be carefully addressed. One of the major considerations is establishing clear rules and boundaries for determining what constitutes an acceptable vulnerability report and how these vulnerabilities will be addressed.
Organizations must also navigate the legal and compliance implications of bug bounty programs, involving not just technical teams, but also legal, compliance, and PR departments. By involving these stakeholders, organizations can ensure that bug bounty programs align with legal frameworks and comply with regulatory requirements.
Another challenge arises in the grey areas where the actions of security researchers may be perceived as malicious rather than helpful. It is essential to establish clear communication channels and guidelines to avoid misunderstandings and potential conflicts between organizations and researchers.
Additionally, bug bounty programs pose legal implications that must be considered. Organizations should adhere to ethical guidelines and respect user privacy while conducting vulnerability testing. By prioritizing responsible disclosure and ensuring that ethical hackers do not exploit identified vulnerabilities, organizations can avoid potential legal ramifications.
The potential risks associated with bug bounty programs also cannot be ignored. Malicious individuals may exploit bug bounty programs for malicious purposes, such as extortion or unauthorized access. Organizations must implement measures to mitigate these risks and ensure that program activities are closely monitored and audited.
“Ensuring clear rules, engaging multiple stakeholders, promoting responsible disclosure, and mitigating risks are key considerations in implementing bug bounty programs.”
To summarize, the challenges and considerations in bug bounty programs revolve around defining rules, addressing legal implications, navigating grey areas, and mitigating potential risks. By proactively addressing these challenges, organizations can create a secure environment for bug bounty programs and effectively harness the collective expertise of ethical hackers to strengthen their cybersecurity defenses.
Building a Mature Security Culture for Bug Bounties
To effectively implement bug bounty programs, organizations need to have a mature security culture in place. This involves ensuring that all stakeholders, including management, employees, and third-party suppliers, understand the importance of cybersecurity and are committed to it. By fostering a strong security culture, organizations can strengthen their defenses and collaborate more effectively with ethical hackers.
Clear Rules and Processes
Establishing clear rules, boundaries, and processes for vulnerability reporting and handling is essential. This ensures that everyone involved understands their roles and responsibilities, minimizing confusion and streamlining the bug bounty program. Clear guidelines contribute to effective collaboration and help organizations make the most of the expertise offered by ethical hackers.
Involvement of All Departments
It’s crucial to involve not just technical teams but also legal, compliance, and PR departments in bug bounty programs. This interdisciplinary approach helps address legal and compliance implications, communicate with ethical hackers effectively, and manage public relations. By engaging all relevant departments, organizations can ensure a comprehensive and well-coordinated response to vulnerabilities.
Efficient Vulnerability Triage and Resolution
Organizations must have the capability to triage and fix vulnerabilities efficiently. This requires establishing effective communication channels with the security researcher community and having a structured process in place to prioritize and address reported vulnerabilities. Regular and prompt communication helps build trust and encourages ethical hackers to continue collaborating with the organization.
Collaboration with Ethical Hackers
Creating a mature security culture involves fostering collaboration with ethical hackers. Organizations should establish open lines of communication and encourage ethical hackers to provide feedback and suggestions for improving cybersecurity. Recognizing their efforts and offering vulnerability rewards not only incentivizes ethical hackers to participate but also strengthens the relationship between the organization and the wider security community.
Building a mature security culture sets the foundation for successful bug bounty programs. It ensures that bug bounty initiatives are integrated into the organization’s overall cybersecurity strategy and supported by a collaborative and responsive approach. By embracing a mature security culture, organizations can effectively harness the power of bug bounties to strengthen their cybersecurity defenses.

Bug Bounty Programs: Are You Ready?
Bug bounty programs can offer significant benefits to organizations seeking to enhance their cybersecurity defenses by tapping into the expertise of external security researchers. However, these programs may not be suitable for every organization. Before embarking on a bug bounty program, it is crucial to assess your readiness and preparedness.
Organizations should have existing security measures in place, including robust vulnerability disclosure programs that allow for the responsible reporting of bugs. A culture of security internally is also essential, ensuring that all employees understand the importance of cybersecurity and their roles in maintaining it.
Furthermore, organizations should be capable of handling and fixing known vulnerabilities before inviting external researchers to identify new ones. Establishing a bug bounty program requires resources and investment, including the potential hiring of security consultants or a Chief Security Officer (CSO).
Refining and enhancing your vulnerability disclosure program is another key aspect to consider. Clear processes for receiving, evaluating, and addressing vulnerability reports must be established to ensure efficient collaboration between your organization and external researchers.
It is important to note that bug bounty programs should be seen as a supplementary step to build upon existing security efforts, rather than a replacement for them. Organizations need to have a solid foundation of security practices in place before engaging in bug bounty programs.
To summarize, before diving into bug bounty programs, assess your organization’s readiness, ensure you have established security measures and a culture of security, and be prepared to refine and enhance your vulnerability disclosure program. By taking these steps, you can maximize the effectiveness of your bug bounty program and leverage the collective expertise of security researchers to strengthen your cybersecurity defenses.
Key considerations for bug bounty program readiness:
- Existing security measures, including vulnerability disclosure programs
- A culture of security internally
- Capacity to handle and fix known vulnerabilities
- Resources and investment, including potential hiring of security consultants or a CSO
- Refinement and enhancement of vulnerability disclosure program

Implementing a bug bounty program requires careful consideration and preparation. It is not a one-size-fits-all solution, and organizations should evaluate their readiness before diving in.
Bug Bounty Programs for Beginners
Bug bounty programs provide not only advanced hackers but also beginners with opportunities to learn and develop their skills in cybersecurity. These programs have designed their public platforms to be beginner-friendly, offering approachable entry points for researchers at any skill level.
As a beginner, you can start small and gradually work your way up in bug bounty programs. This allows you to gain hands-on experience in probing production systems without causing any damage or legal trouble. By participating in bug bounty programs, you enter a supportive learning environment where you can build your track record and reputation as you submit valid bug reports.
Successful submissions and eventual recognition in bug bounty programs can open up new opportunities and career advancements in the cybersecurity field. Whether you’re aspiring to become a cybersecurity professional or looking to enhance your existing skills, bug bounty programs provide a platform for learning and growth.

Bug Bounty Platforms: Overview and Key Details
Several bug bounty platforms offer opportunities for security researchers to participate in bug bounty programs. These platforms provide a structured environment for organizations to collaborate with ethical hackers and strengthen their cybersecurity defenses. Here, we provide an overview of some popular bug bounty platforms along with their key features and characteristics.
HackerOne
HackerOne is a widely recognized bug bounty platform that boasts a large and diverse community of ethical hackers. They offer various programs that cater to different organizations and industries. With their robust platform and comprehensive communication tools, HackerOne facilitates effective collaboration between organizations and researchers.
Bugcrowd
Bugcrowd focuses on vulnerability disclosure and bug bounty programs for diverse organizations, ranging from small businesses to large enterprises. Their platform is known for its comprehensive triage and verification processes to ensure high-quality bug submissions. Bugcrowd also emphasizes researcher engagement and offers rewards based on researcher reputation and expertise.
Intigriti
Intigriti is a bug bounty platform that specializes in serving European companies. They have a strong focus on responsible disclosure and ethical hacking practices. Intigriti utilizes their extensive network of security researchers to help European organizations identify and address vulnerabilities effectively.
Open Bug Bounty
Open Bug Bounty distinguishes itself as a non-profit platform that offers bug reporting services without requiring financial compensation. It provides an accessible option for smaller organizations with limited budgets to engage with the security research community. Open Bug Bounty aims to promote the responsible disclosure of vulnerabilities.
HackenProof
HackenProof is a bug bounty platform that focuses on linking ethical hackers to various Web3 projects. With their expertise in blockchain and decentralized technologies, HackenProof enables organizations operating in the Web3 ecosystem to leverage the skills of ethical hackers and enhance their security measures.
Each bug bounty platform offers its unique set of features and characteristics, catering to the diverse needs of organizations and the security research community. Researchers can choose the platform that aligns with their expertise and preferences, ensuring effective collaboration and the discovery of vulnerabilities.
In the next section, we will conclude our exploration of bug bounty programs and their role in strengthening cybersecurity.
Conclusion
In today’s cyber-centric world, where digital threats loom at every corner, the need for comprehensive vulnerability testing has never been more acute. Peris.ai Korava emerges as the ultimate solution in this domain, offering an unparalleled Bug Bounty Platform that leverages the collective expertise of a global community of ethical hackers. This crowdsourced approach to vulnerability testing not only enhances the security posture of organizations but also introduces a level of customization and efficiency unprecedented in the cybersecurity landscape.
Peris.ai Korava distinguishes itself by allowing organizations to tailor their bug bounty programs to their specific requirements. With a variety of customization options, clients can define the scope of their programs and set appropriate rewards, ensuring alignment with their cybersecurity goals and budget. This bespoke approach guarantees optimal results, delivering value that far surpasses traditional vulnerability assessment methods.
At the heart of Korava’s effectiveness is our formidable assembly of guardians—verified ethical hackers from around the globe. Each hacker undergoes a rigorous verification process before participating in any program, ensuring that only the most skilled and ethical professionals contribute to safeguarding your systems. This global network of cybersecurity experts stands ready to identify and report vulnerabilities, providing your organization with the critical insights needed to fortify its defenses.
A standout feature of Korava is its double review process. Before any vulnerability report reaches a client, it undergoes a thorough review by three other ethical hackers. This meticulous process ensures the highest quality of reporting, virtually eliminating the risk of false positives. Such a level of scrutiny not only saves clients valuable time and resources in addressing security issues but also instills confidence in the remediation process.
Peris.ai Korava is more than just a platform; it’s a strategic ally in the ongoing battle against cyber threats. By harnessing the collective intelligence and ethical prowess of a worldwide hacker community, Korava empowers organizations to stay one step ahead of potential vulnerabilities, ensuring their digital assets are secure and resilient against attacks.
To explore how Peris.ai Korava can revolutionize your approach to cybersecurity and vulnerability management, we invite you to visit Peris.ai Cybersecurity. Discover the power of crowdsourced security testing and how our customizable programs, backed by a double review process, can provide your organization with the ultimate in cyber protection. Embrace the future of cybersecurity with Peris.ai Korava and secure your digital landscape today.
FAQ
What are bug bounty programs?
Bug bounty programs are initiatives by companies to enlist the help of security researchers, or ethical hackers, to identify and report vulnerabilities in their systems. Researchers are rewarded with monetary incentives for their efforts.
What are the benefits of bug bounty programs?
Bug bounty programs offer access to a diverse pool of security researchers, promote collaboration between organizations and ethical hackers, and help strengthen cybersecurity defenses by identifying vulnerabilities.
How do I select bug bounty platforms or companies?
There are various bug bounty platforms available, such as HackerOne and Bugcrowd, which provide the infrastructure for managing bug bounty programs. Open Bug Bounty is a platform that offers bug reporting services without financial compensation.
What challenges are involved in bug bounty programs?
Challenges include defining clear rules and boundaries, addressing legal and compliance implications, and navigating potential misunderstandings between organizations and security researchers.
How do I build a mature security culture for bug bounties?
Building a mature security culture involves ensuring all stakeholders understand cybersecurity’s importance, establishing clear rules and processes for vulnerability reporting, and maintaining regular communication with the security researcher community.
Are bug bounty programs suitable for every organization?
Bug bounty programs require organizations to have existing security measures in place, the capacity to handle and fix known vulnerabilities, and resources and investment for implementation. They should be seen as an enhancement to existing security efforts.
Can beginners participate in bug bounty programs?
Bug bounty programs provide opportunities for beginners to learn and develop their skills. Many platforms have designed public programs to be approachable to researchers at any skill level.
What bug bounty platforms are available?
Popular bug bounty platforms include HackerOne, Bugcrowd, Intigriti, Open Bug Bounty, and HackenProof. Each platform has its own unique features and characteristics.
How do bug bounty programs contribute to cybersecurity?
Bug bounties play a crucial role in enhancing cybersecurity by enabling collaboration between organizations and ethical hackers, leveraging their expertise to fortify defenses, and creating a safer digital landscape.