In the rapidly evolving landscape of cybersecurity, organizations are continually searching for the best solutions to protect their data and assets. Two prominent contenders in this field are Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR). While both offer robust threat detection and response capabilities, they differ in several key aspects. This article will explore the differences between EDR and XDR, as well as Network Detection and Response (NDR), to help you understand which solution offers the best protection for your network.
Key Takeaways:
- EDR and XDR are both powerful cybersecurity solutions.
- EDR focuses on securing individual endpoints, providing detailed visibility into endpoint activity.
- XDR takes a holistic approach, integrating data from multiple sources to provide a comprehensive view of the organization’s security posture.
- The choice between EDR and XDR depends on the organization’s specific needs and security posture.
EDR: Focus on the Endpoint
Endpoint Detection and Response (EDR) solutions are designed to prioritize the security of individual endpoints, such as laptops, desktops, and servers. These solutions offer comprehensive visibility into endpoint activity, allowing security teams to closely monitor and analyze various aspects, including process execution, network connections, and file access. With this granular level of insight, organizations can swiftly and effectively detect and respond to potential threats.
One of the key advantages of EDR is its deep visibility into endpoint activity. By continuously monitoring endpoint behavior, EDR tools can identify anomalies and suspicious activities in real-time, enabling timely threat detection and response. This proactive approach helps prevent security incidents from escalating and minimizes the potential damage caused by malicious actors.
EDR solutions not only provide visibility but also offer rapid threat detection and response capabilities. Through advanced detection mechanisms and analytics, these tools can quickly identify indicators of compromise and potential security breaches, ensuring that immediate action can be taken to mitigate the risks involved. With EDR, organizations can enhance their incident response capabilities and speed up the resolution process.
Automated incident response is another significant advantage of EDR solutions. By automating routine tasks and response actions, security teams can streamline their operations, enhance efficiency, and reduce human error. This automation ensures that potential threats are promptly addressed, allowing security personnel to focus on more critical and complex security issues.
Overall, EDR solutions offer a powerful and specialized approach to endpoint security. With their deep visibility, rapid threat detection and response, and automated incident response, EDR tools prove invaluable for organizations managing a large number of endpoints.
Key Features of EDR
- Comprehensive visibility into endpoint activity
- Rapid threat detection and response capabilities
- Automated incident response

XDR: A Unified Approach
XDR (Extended Detection and Response) takes a holistic approach to security by integrating data from multiple sources, such as endpoints, networks, cloud workloads, and email. This unified platform provides a comprehensive view of the organization’s security posture across the entire IT environment, allowing for more effective threat detection and response.
Unlike traditional security solutions that focus on individual components, XDR breaks down security silos and correlates data from various sources. By analyzing and correlating data from endpoints, networks, and other sources, XDR can detect threats that may go unnoticed by individual security tools. This comprehensive and unified approach maximizes the organization’s ability to identify and respond to potential security incidents.
XDR also simplifies security operations by providing a single platform for managing all security data and activities. This centralized approach streamlines the security workflow, reduces the complexity of managing multiple tools, and improves overall efficiency.
By implementing XDR, organizations can improve their security posture by gaining a deeper understanding of their network’s vulnerabilities, identifying potential threats faster, and responding more effectively. This proactive approach to security helps organizations stay one step ahead of cyber threats and mitigate risks more efficiently.
The Benefits of XDR
XDR offers several key benefits for organizations looking to enhance their threat detection capabilities and strengthen their security posture:
- Improved Threat Detection: By correlating data from multiple sources, XDR provides a more comprehensive view of potential threats, allowing organizations to detect and respond to security incidents more effectively.
- Reduced Security Silos: XDR breaks down the barriers between different security tools and data sources, enabling a more coordinated and integrated approach to security.
- Simplified Security Operations: With a central platform for managing security activities, XDR simplifies the management and orchestration of security processes, reducing complexity and improving operational efficiency.
XDR vs. EDR: A Comparison
To better understand the benefits of XDR, it is important to compare it to Endpoint Detection and Response (EDR), a widely adopted security solution. While EDR focuses on securing individual endpoints, XDR takes a broader and more integrated approach to threat detection and response.
Here is a comparison of XDR and EDR in terms of their core features:
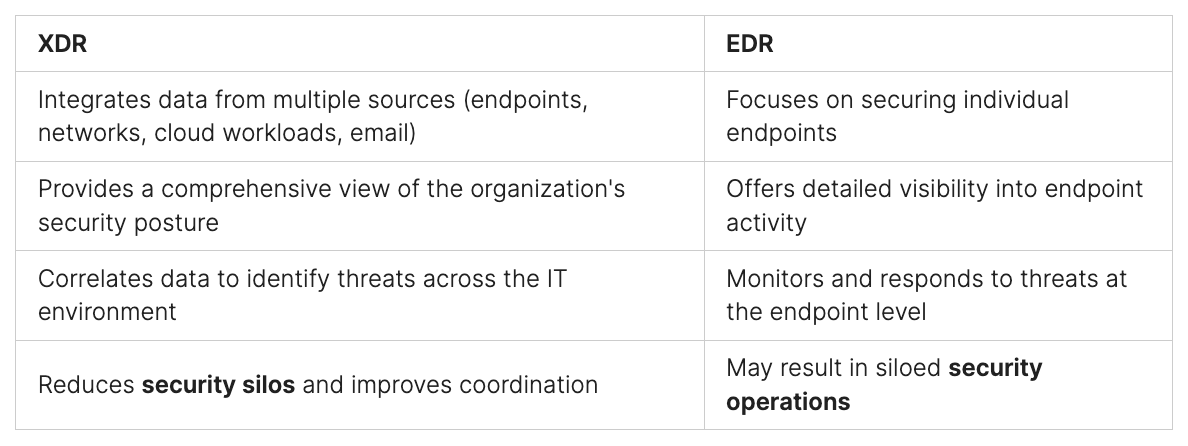
As the table illustrates, XDR provides a more comprehensive and integrated approach to security by incorporating data from various sources. This broader scope improves threat detection capabilities and reduces security silos.
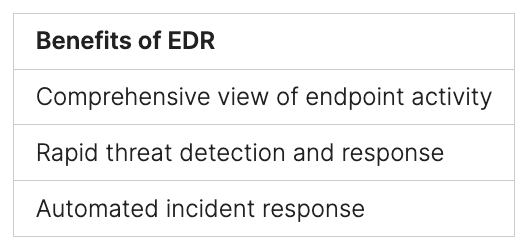
Benefits of EDR
EDR solutions offer several key benefits that enhance the cybersecurity posture of organizations. By providing a comprehensive view of endpoint activity, EDR enables security teams to gain deep insights into the behavior of individual endpoints. This level of visibility makes it easier to detect anomalous activity and identify potential threats.
With EDR, organizations can quickly and effectively respond to incidents, minimizing the potential damage caused by cyberattacks. The rapid threat detection capabilities of EDR solutions enable security teams to stay one step ahead of malicious actors, proactively mitigating potential risks.
Automated incident response is another significant advantage of EDR. By automating routine tasks, such as isolating compromised endpoints or blocking malicious processes, EDR tools free up valuable time for security teams. This allows them to focus on more strategic and higher-value activities, such as threat hunting and analysis.
“EDR solutions provide comprehensive visibility into endpoint activity, enabling faster threat detection and response.”
Overall, EDR solutions play a critical role in bolstering an organization’s cybersecurity defenses. By offering detailed endpoint activity visibility, rapid threat detection, and automated incident response capabilities, EDR empowers organizations to proactively protect their networks and minimize the impact of security incidents.
Benefits of XDR
Extended Detection and Response (XDR) offers a range of benefits that significantly enhance an organization’s threat detection capabilities, streamline security operations, and break down security silos. By correlating data from multiple sources, XDR provides a more comprehensive view of potential threats, enabling a quicker and more effective response. Here are the key advantages of implementing XDR:
- Improved Threat Detection: XDR leverages data from endpoints, networks, cloud workloads, and email to identify threats that may go unnoticed by individual security solutions. By analyzing and correlating data from multiple sources, XDR offers enhanced detection capabilities, enabling proactive threat hunting and rapid incident response.
- Reduced Security Silos: Traditional security solutions often operate in silos, making it challenging for security teams to gain a comprehensive view of the threat landscape. XDR breaks down these silos by integrating data from various sources into a unified platform. This integrated approach empowers security teams to identify patterns and trends across the entire IT environment, improving their understanding of potential threats and enabling a more coordinated and effective response.
- Simplified Security Operations: Managing security operations can be complex and time-consuming when dealing with multiple security tools and platforms. XDR simplifies security operations by providing a single platform for managing all security data and activities. This centralized approach streamlines workflows, eliminates duplicate efforts, and enables efficient collaboration between security teams, resulting in improved productivity and reduced operational costs.
Implementing XDR allows organizations to take a proactive stance against cyber threats, leveraging comprehensive threat detection capabilities, breaking down security silos, and simplifying security operations. By investing in XDR, organizations can elevate their security postures and stay one step ahead of evolving threats.
Which is Better: EDR or XDR?
The decision of whether EDR or XDR is the better cybersecurity solution depends on an organization’s specific needs and security posture. Both EDR and XDR offer unique capabilities that cater to different requirements.
EDR:
EDR, or Endpoint Detection and Response, is an ideal choice for organizations that manage a large number of endpoints and require detailed visibility into endpoint activity. EDR solutions provide a granular level of insight into processes, network connections, and file access on individual endpoints. This enhanced visibility enables security teams to quickly detect and respond to threats. With automated incident response capabilities, EDR tools streamline the management of security incidents and free up valuable time for security personnel.
XDR:
XDR, or Extended Detection and Response, takes a more holistic approach to cybersecurity. It integrates data from multiple sources, including endpoints, networks, cloud workloads, and email, providing a comprehensive view of an organization’s security posture. XDR offers improved threat detection by correlating data from various sources, which can uncover threats that may have been missed by individual security solutions. Additionally, XDR reduces security silos and simplifies security operations by consolidating security data and activities onto a single platform.
The Future of Cybersecurity
As organizations navigate the ever-evolving landscape of cybersecurity, the need for effective threat detection and response is paramount. Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) have emerged as powerful solutions in combating cybercrime. While both EDR and XDR offer valuable features, XDR represents the future of cybersecurity with its unified approach and improved security posture.
EDR focuses on securing individual endpoints, providing in-depth visibility into endpoint activity for threat detection and response. While EDR solutions excel in endpoint protection, their limited scope may lead to security gaps in complex IT environments.
XDR, on the other hand, takes a holistic approach to security by integrating data from multiple sources such as endpoints, networks, cloud workloads, and email. This unified platform offers a comprehensive view of an organization’s security posture, enabling improved threat detection and a more coordinated response to emerging threats.
By correlating data across different sources, XDR eliminates security silos and provides a single platform for managing all security activities. As organizations embrace XDR solutions, we can anticipate a significant enhancement in their overall security posture.
“The integration capabilities of XDR are key in taking cybersecurity to the next level. By breaking down silos and fostering collaboration among security tools, XDR enables organizations to stay one step ahead of sophisticated threats.”
With the ever-increasing sophistication of cyber threats, a unified approach like XDR offers unparalleled visibility and protection. By leveraging the power of XDR, organizations can proactively defend against advanced attacks and strengthen their security defenses across the entire IT infrastructure.
Benefits of XDR:
- Improved threat detection through correlation of data from multiple sources
- Reduced security silos for a more coordinated response to threats
- Simplified security operations with a single platform for managing all security activities
Organizations that prioritize a unified approach and an improved security posture should consider adopting XDR as their cybersecurity solution of choice.
Additional Factors to Consider
When choosing between EDR and XDR, there are several additional factors to consider. These factors can help organizations make an informed decision based on their specific needs and requirements. Take a closer look at the following considerations:
Cost
XDR solutions often come with additional features and functionality, which can make them more expensive than EDR solutions. Organizations should carefully evaluate their budget and determine the level of investment they are willing to make in their cybersecurity solution.
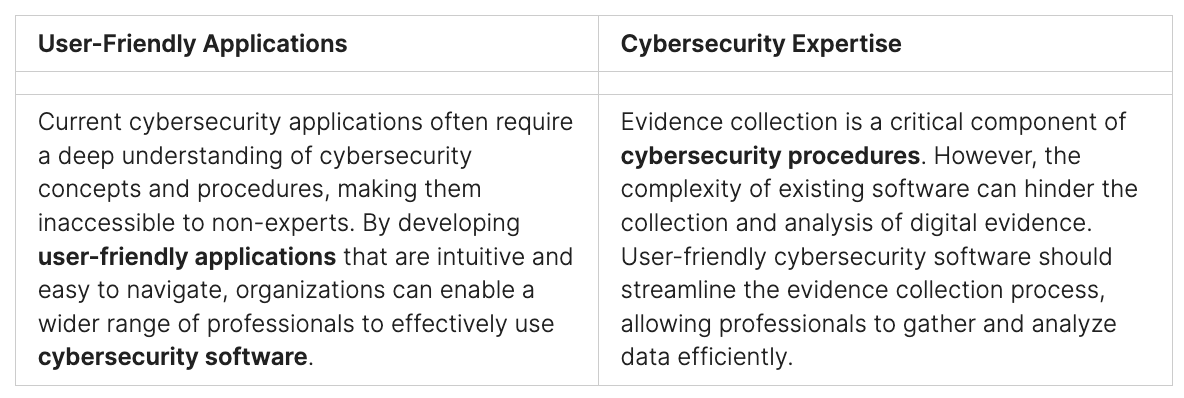
Security Expertise
Implementing and managing an XDR solution requires more security expertise compared to EDR. Organizations should assess their internal resources and determine if they have the necessary skills and knowledge to effectively handle an XDR solution. If not, they may need to consider hiring external security experts or seeking assistance from trusted cybersecurity providers.
Integration
Integration with other security tools in the organization’s environment is a vital consideration. EDR and XDR solutions should seamlessly integrate with existing security infrastructure to ensure a cohesive and effective defense strategy. Organizations should verify compatibility and ensure that the chosen solution can integrate smoothly with their current security stack.
Organization’s Specific Needs
Every organization has unique security requirements. It is essential to carefully evaluate these needs before making a decision between EDR and XDR. Consider factors such as the size of the organization, the complexity of the IT environment, and the level of threat exposure. Each solution offers different capabilities, and organizations should choose the one that aligns best with their specific needs and addresses their most critical security challenges.
By considering these additional factors, organizations can make an informed decision about whether EDR or XDR is the best fit for their cybersecurity strategy. It’s crucial to find the right balance between cost-effectiveness, security expertise, integration capabilities, and meeting the organization’s specific needs.
Conclusion
In conclusion, both EDR and XDR are powerful tools that can play a vital role in an organization’s cybersecurity strategy. EDR offers detailed visibility into endpoint activity and rapid threat detection and response capabilities, making it a suitable choice for organizations with a large number of endpoints to manage. XDR, on the other hand, offers a more comprehensive and unified approach to security, providing improved threat detection, reduced security silos, and simplified security operations. The choice between EDR and XDR depends on the organization’s specific needs and security posture.
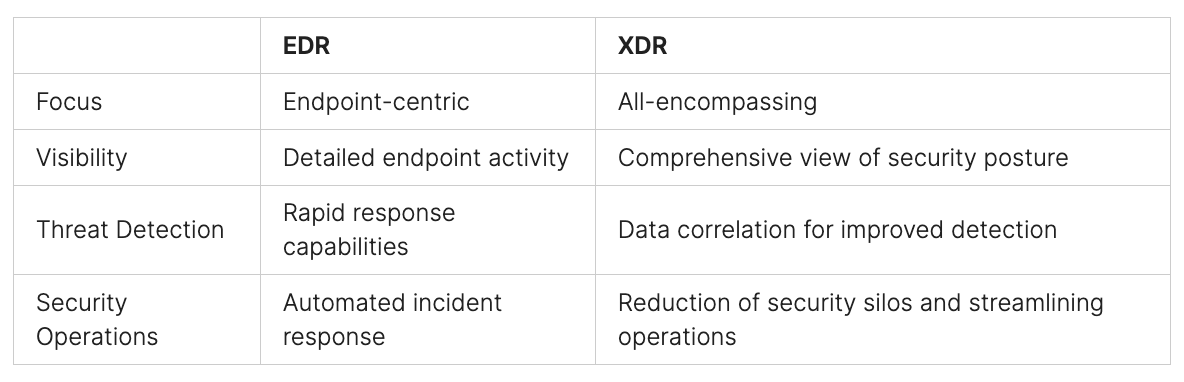
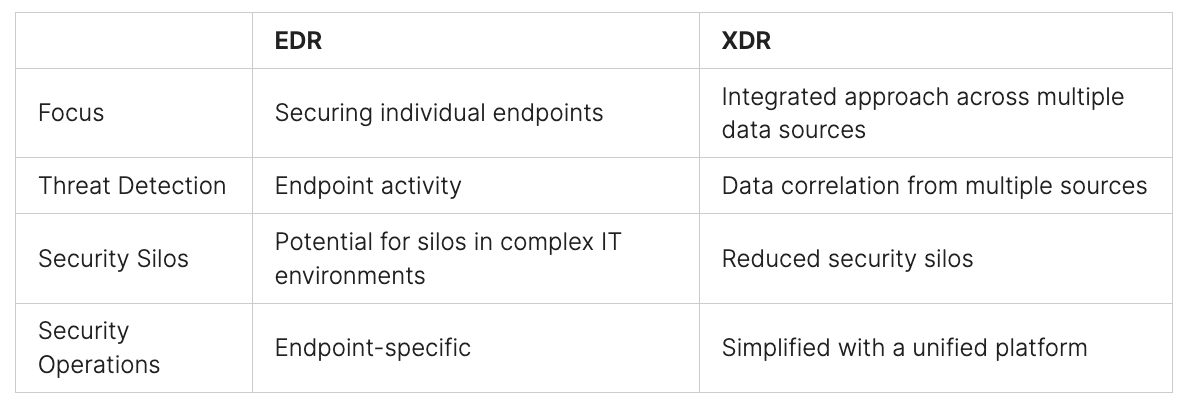
Comparative Analysis: EDR vs. XDR
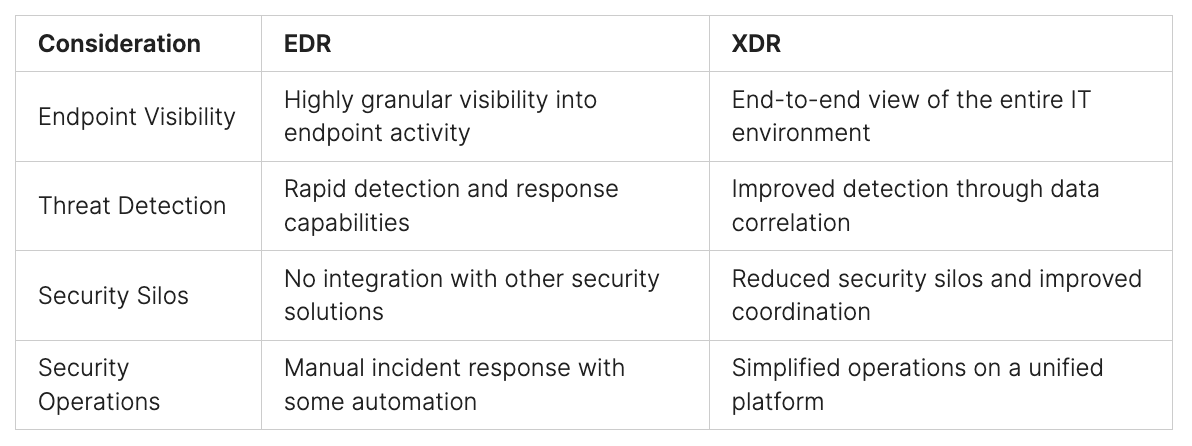
Based on this comparison, EDR excels in providing detailed visibility into endpoint activity and offering rapid threat detection and response capabilities. On the other hand, XDR goes beyond individual endpoints and provides a comprehensive view of the entire IT environment, enabling improved threat detection, reduced security silos, and simplified security operations.
EDR focuses on securing individual endpoints, while XDR takes a more holistic approach by integrating data from multiple sources. This comprehensive approach offered by XDR can detect threats that might be missed by EDR solutions, making it an increasingly attractive choice for organizations.
When selecting between EDR and XDR, organizations should assess their specific needs, IT environment complexity, and desired level of security. Ultimately, the right choice will depend on achieving a comprehensive approach to cybersecurity and comprehensive detection of threats across the organization.
Do You Need Expert Advice?
If you’re uncertain about which cybersecurity solution is best for your business, don’t worry. The Peris.ai Cybersecurity team is here to help you make an informed decision based on your specific needs and requirements. With our expert advice, you can find the perfect cybersecurity solution that offers the optimal level of protection for your business.
Book a call with Peris.ai Cybersecurity today to consult with our professionals. We’ll provide you with guidance and insights to ensure you choose the best cybersecurity solution that is tailored to your business needs. With our expertise, you can navigate through the complex landscape of cybersecurity and implement the solution that’s best for your business.
The Importance of Choosing the Right Cybersecurity Solution
Ensuring the protection of your network and critical data is paramount in today’s digital landscape. With various cybersecurity solutions available, selecting the right one can make all the difference. As you navigate through the options, it is crucial to understand the differences between EDR, NDR, and XDR, and assess your organization’s specific needs.
Endpoint Detection and Response (EDR) focuses on securing individual endpoints, offering detailed visibility into endpoint activity and rapid threat detection and response capabilities. Network Detection and Response (NDR) focuses on monitoring and analyzing network traffic to identify and respond to potential threats. Extended Detection and Response (XDR) takes a more holistic approach, integrating data from multiple sources to provide a comprehensive view of your organization’s security posture.
By evaluating your organization’s specific needs and considering the unique benefits and capabilities of EDR, NDR, and XDR, you can make an informed decision. Protecting your network and critical data requires a cybersecurity solution that aligns with your requirements, ensuring optimal security and peace of mind.
FAQ
What is Endpoint Detection and Response (EDR)?
EDR solutions focus on securing individual endpoints such as laptops, desktops, and servers, providing detailed visibility into endpoint activity, threat detection, and incident response capabilities.
What is Extended Detection and Response (XDR)?
XDR takes a holistic approach to security by integrating data from multiple sources, offering improved threat detection, reduced security silos, and simplified security operations across the entire IT environment.
How does EDR differ from Network Detection and Response (NDR)?
EDR focuses on securing individual endpoints, while NDR focuses on detecting and responding to threats within the network infrastructure.
What are the benefits of EDR?
EDR provides in-depth visibility into endpoint activity, rapid threat detection and response capabilities, and automated incident response, enhancing an organization’s security posture.
What are the benefits of XDR?
XDR offers improved threat detection by correlating data from multiple sources, reduces security silos, and simplifies security operations by providing a unified platform for managing all security data and activities.
Which is better, EDR or XDR?
The choice between EDR and XDR depends on an organization’s specific needs and security posture. EDR is suitable for organizations with a large number of endpoints, while XDR is ideal for those with a complex IT environment.
What is the future of cybersecurity?
XDR represents the future of cybersecurity, offering a unified and comprehensive approach to threat detection and response, improving overall security posture.
What additional factors should be considered when choosing between EDR and XDR?
Factors such as cost, security expertise, and integration with existing security tools should be considered when choosing between EDR and XDR.
How important is it to choose the right cybersecurity solution?
Choosing the right cybersecurity solution is crucial to ensure the protection of your network and critical data.