In today’s world, cybersecurity threats are a big concern for all kinds of organizations. Imagine having a detailed, adaptable, and widely used framework to help manage these risks. That’s what the NIST Cybersecurity Framework (NIST CSF) offers. It’s a set of guidelines created by the National Institute of Standards and Technology (NIST) to simplify cybersecurity for organizations.
But you might wonder: What is the NIST Cybersecurity Framework, and how can it help your business? Let’s explore the NIST CSF’s main parts, how to put it into action, and its big impact on cybersecurity.
Key Takeaways
- The NIST Cybersecurity Framework offers a flexible, voluntary, and repeatable way to handle cybersecurity risks.
- It has five core functions: Identify, Protect, Detect, Respond, and Recover.
- The Identify function is key, focusing on managing assets, assessing risks, and setting policies.
- This framework matches up with other top security standards, making it a full solution.
- Using the NIST CSF can boost your organization’s security and resilience.
Introduction to the NIST Cybersecurity Framework
Definition and Overview
The NIST Cybersecurity Framework is a set of guidelines that helps organizations improve their cybersecurity. It’s made by the National Institute of Standards and Technology (NIST). This framework fills the gap of missing standards in cybersecurity, offering a common set of advice for all kinds of organizations. It’s seen as the top choice for boosting an organization’s cybersecurity skills, no matter its size or type.
Importance and Relevance
This framework is key for making organizations more secure against cyber threats. It helps them spot, protect, detect, respond to, and bounce back from cyber attacks. By setting a cybersecurity policy, using security steps like access control and encryption, watching for unauthorized actions, and having clear response and recovery plans, companies can lessen the damage from cyber attacks. With cyber threats on the rise, the NIST Cybersecurity Framework is vital for businesses and groups in many fields to handle and lower their cybersecurity risks.
The framework is optional and uses current standards, guidelines, and practices. It has three main parts: the Core, Implementation Tiers, and Profiles. The Core lists what cybersecurity activities and results are wanted, in simple language. The Implementation Tiers and Profiles help organizations see and focus on areas to improve their cybersecurity.
*CertMike Explains NIST Cybersecurity Framework: https://youtube.com/watch?v=_KXqDNVmpu8
“The NIST Cybersecurity Framework is a voluntary tool designed to help businesses manage and reduce cybersecurity risks.”
Core Structure of the NIST Cybersecurity Framework
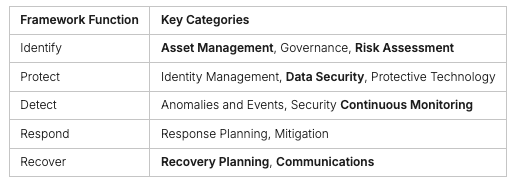
The NIST Cybersecurity Framework has five core functions. These functions help an organization manage its cybersecurity risks. The functions are: Identify, Protect, Detect, Respond, and Recover. Each function has categories and subcategories that detail specific security practices and controls.
Five Core Functions
The Identify function helps understand and manage cybersecurity risks. It includes Asset Management, Governance, and Risk Assessment. The Protect function focuses on safeguarding critical infrastructure. It includes Identity Management, Data Security, and Protective Technology. The Detect function is about finding cybersecurity events quickly. It covers Anomalies and Events and Security Continuous Monitoring. The Respond function is about reacting to cybersecurity incidents. It includes Response Planning and Mitigation. The Recover function helps restore capabilities or services after an incident. It includes Recovery Planning and Communications.
Categories and Subcategories
The NIST Cybersecurity Framework has 108 Subcategories in the Core. These help create or improve a cybersecurity program. They let organizations customize the framework to fit their needs. This ensures a thorough and coordinated approach to cybersecurity.
The NIST Cybersecurity Framework is focused on outcomes. It helps organizations build a strong base for following new rules. Using the NIST Framework helps organizations deal with cybersecurity issues quickly.
“The NIST Cybersecurity Framework 2.0 provides guidance to industry, government agencies, and other organizations to manage cybersecurity risks.”
Identify Function
The Identify function of the NIST Cybersecurity Framework (NIST CSF) helps organizations understand how to manage cybersecurity risks. It covers systems, people, assets, data, and capabilities. This includes managing assets and assessing risks to find ways to reduce them. By focusing on this, organizations can protect their most important resources.
Asset Management
Asset management is crucial in the Identify function of the NIST CSF. It means listing all the assets an organization has, like hardware and software. Knowing what they have helps organizations see where they might be vulnerable and focus on securing those areas.
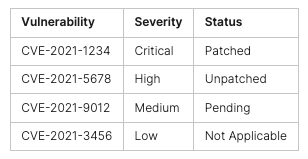
Risk Assessment and Management
Risk assessment and management are also key parts of the Identify function. They help spot potential weaknesses and threats, and plan how to deal with them. This way, organizations can plan how to use their resources wisely and keep their software safe.
*NIST CSF – Identify Function ((Asset Management)) Implementation: https://youtube.com/watch?v=VcC_KabV_Ho
“The NIST Cybersecurity Framework provides a comprehensive approach to enhance an organization’s cybersecurity posture, with the Identify function serving as the foundational first step in this process.”
Protect Function
The Protect function of the NIST Cybersecurity Framework helps keep critical infrastructure safe. It also helps limit the damage from cyber threats. This includes steps for managing identities, securing data, and training staff on security. It also means keeping information systems and assets safe.
By focusing on the Protect function, companies can lower the risk of cyber attacks. This makes it easier to handle security issues.
The NIST Cybersecurity Framework gives detailed advice for better data security and managing access. It suggests ways to create secure keys, protect networks, and keep web servers safe. It also talks about using smart cards for access control and secure ways to send data.
It also has tips on recovering from data breaches and securing email systems. By following these protect function nist csf, cybersecurity controls, and data security steps, companies can better protect their important assets.
“The Protect function of the NIST Cybersecurity Framework is essential for organizations to develop and implement the necessary security measures to reduce the likelihood and impact of cyber threats.”
Detect Function
The Detect function of the NIST Cybersecurity Framework (NIST CSF) is key to spotting and tackling cybersecurity threats fast. It helps in creating and using the right steps to notice when cybersecurity events happen. This way, organizations can lessen their effects and get better at handling cybersecurity.
Anomaly and Event Detection
This function is about finding odd or suspicious actions in an organization’s systems and networks. It means setting up what’s normal for data, looking into cybersecurity events, linking event data, and figuring out how big the impact is. By setting clear alert levels, companies can spot and act on threats quickly, lowering the chance of attacks.
Continuous Monitoring
Continuous monitoring is key to the Detect function, making sure to always find security problems. It means watching the network, the physical place, how people work, and who they work with, and finding bad code and weaknesses. By keeping and testing how you find these issues, companies can share info on finding events and keep getting better at cybersecurity.
Having a strong Detect function is vital for companies to find and deal with cyber threats fast. By using the advice and best practices from the NIST CSF, businesses can make their cybersecurity stronger and fight off new cyber threats.
*NIST CSF Identify Function: https://youtube.com/watch?v=XGZyrWcUrJQ
“Detecting cybersecurity events quickly can help lessen their effects and is key for a strong cybersecurity program.”
Respond Function
The Respond function of the NIST Cybersecurity Framework helps when a cybersecurity incident is detected. It includes planning for responses, communicating with others, and analyzing the incident to help recover. This way, organizations can limit the damage from a cyber attack and get back to normal.
Response Planning
Response Planning means having a plan ready for when a cyber attack happens. It includes knowing who to notify and what steps to take quickly.
Communications and Analysis
Good communication is key during a cyber attack. It’s important to talk to the right people fast, following the law or company rules. Analysis helps figure out what was hit, how bad it is, and gathers evidence for legal cases. Stopping the attack quickly is vital, and learning from it helps improve how we handle risks. After an attack, looking back to see what worked and what didn’t helps us get better. Practicing with exercises helps us be ready for real attacks, like ransomware.
“The Respond function of the NIST Cybersecurity Framework is crucial for effectively containing the impact of a cybersecurity event and restoring normal operations.”
Recover Function
The Recover function of the NIST Cybersecurity Framework is key to an organization’s cybersecurity plan. It focuses on how to get back to normal after a security issue. This includes making plans, improving things, and talking to people – all important for staying strong and keeping business going.
Recovery Planning
Recovery planning is a big part of the Recover function. It’s about fixing systems and assets hit by a cyber attack. You need to know what depends on each other, who’s key people, and how to talk and work from other places. Also, having a plan for cyber events is a must. Doing recovery tests helps find and fix problems before they hit hard.
Improvements and Communications
Improving and talking with others are big parts of the Recover function too. By learning from past events and working with others, companies can get better at bouncing back. This makes them stronger against future attacks. Talking well with teams, customers, and groups that make rules is key to being open and trusted during recovery.
The Recover function of the NIST Cybersecurity Framework is super important for a company’s cybersecurity plan. It helps fix important stuff, lessen the blow of incidents, and make things stronger overall.
What the NIST Cybersecurity Framework Is All About
The NIST Cybersecurity Framework offers guidelines and best practices for all types of organizations. It helps them manage their cybersecurity risks and improve their security. This framework focuses on five core functions: Identify, Protect, Detect, Respond, and Recover.
It’s flexible and matches well with other security standards. This makes it a great tool for improving cybersecurity and lowering the risk of cyber threats. It helps organizations make smart choices about cybersecurity investments and talk about their security with leaders and the board.
The framework stresses the importance of knowing the business and its risks. It guides organizations to focus on what’s most important for their risk management and business goals. This ensures their cybersecurity efforts match their overall goals.
It also offers advice on how to protect identities, control access, and secure data. Plus, it helps set up strong detection and response plans for cybersecurity incidents. By following these five core functions, organizations can boost their cybersecurity and aim for higher levels of security, like the Adaptive tier.
In summary, the NIST Cybersecurity Framework is a key resource for all kinds of organizations. It helps them improve their cybersecurity, lower risks, and stay strong against new cyber threats.
Implementation Tiers and Maturity Levels
The NIST Cybersecurity Framework (NIST CSF) helps organizations track their cybersecurity progress. It has four implementation tiers that show how well an organization does in cybersecurity. These tiers also show the cybersecurity maturity.
At the lowest tier, Partial, organizations react to threats without a plan. They don’t really think about risks. Moving up to the Risk-Informed tier, they start to understand cybersecurity risks better. But, they don’t have a standard way to manage these risks across the company.
The Repeatable tier means organizations have a plan for managing risks. They update this plan as needed to keep up with threats. At the top, the Adaptive tier, organizations keep getting better. They use new tech and learn from past experiences.
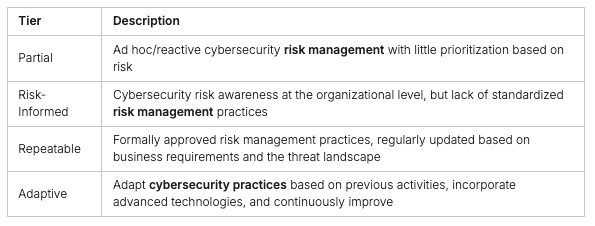
The NIST CSF also talks about maturity levels. These levels help organizations improve their cybersecurity maturity. They go from basic security knowledge to a full, automated, and growing security program.
Knowing where they stand in tiers and levels helps organizations see what they need to work on. They can make a plan to get better at security. This way, businesses can check their cybersecurity maturity and make smart choices about their risk management program.
Using the NIST Cybersecurity Framework and moving up in maturity levels is a big job. But, it’s key for organizations wanting to boost their nist csf implementation tiers and handle cybersecurity risks.
Getting Started with the NIST Cybersecurity Framework
Using the NIST Cybersecurity Framework is a smart move for companies wanting to boost their cybersecurity and manage risks better. First, set clear goals and figure out what risks you can take. Then, check where you stand in cybersecurity, find laws that apply to you, and do a deep risk check.
After that, make a plan for the security level you want to reach and see where you’re short. Then, make a plan to fix those gaps. This way, you can improve your cybersecurity and get safer, following the NIST Framework.
The NIST Cybersecurity Framework has five main parts: Identify, Protect, Detect, Respond, and Recover. Here’s how to start:
- Set your project goals and risk limits.
- Check your current cybersecurity and find laws that apply.
- Do a full risk check to see what threats you face.
- Make a target profile for your risk goals.
- Plan and act on what you need to improve.
This step-by-step plan helps you use the NIST Cybersecurity Framework well. It makes your cybersecurity and risk management better.
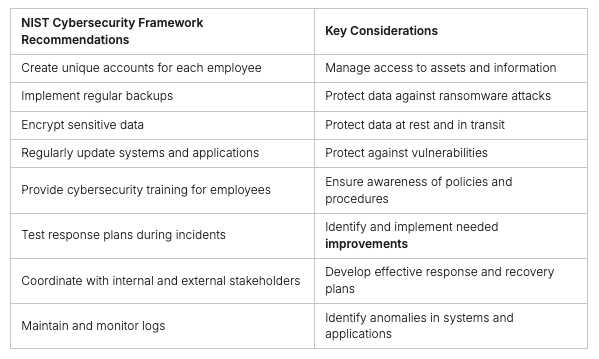
Follow these tips and use the NIST Cybersecurity Framework to make your cybersecurity and risk management better.
“The NIST Cybersecurity Framework provides a common language and structure for managing and reducing cybersecurity risk – a critical component of any successful business strategy.”
Conclusion
The NIST Cybersecurity Framework has become the leading standard for managing cybersecurity risks across various industries and organization sizes. It provides a structured approach for developing and implementing a robust cybersecurity strategy, protecting critical assets, identifying and mitigating cyber threats, and recovering swiftly and resiliently from security incidents.
In today’s complex and ever-evolving threat landscape, the NIST Cybersecurity Framework exemplifies the power of collaboration and unified goals. Developed with input from over 3,000 industry professionals and cybersecurity experts, it serves as an essential tool for organizations looking to enhance their cybersecurity best practices, risk management, and information security measures. As the framework continues to evolve to address new challenges, it remains crucial for businesses striving to lead in the fight against cyber threats.
For more information on how to strengthen your cybersecurity posture using the NIST Cybersecurity Framework and other best practices, visit Peris.ai Cybersecurity. Explore our wide range of products and services designed to help you navigate and mitigate the complexities of today’s digital threats. Secure your business with Peris.ai today!
FAQ
What is the NIST Cybersecurity Framework?
The NIST Cybersecurity Framework is a set of guidelines from the National Institute of Standards and Technology (NIST). It helps organizations of all sizes manage and reduce their cybersecurity risk. It offers a clear way to understand and handle cybersecurity threats.
What are the core functions of the NIST Cybersecurity Framework?
The framework has five core functions: Identify, Protect, Detect, Respond, and Recover. These functions outline the main cybersecurity tasks an organization should do. They help manage risk effectively.
How does the Identify function of the NIST Cybersecurity Framework work?
The Identify function helps an organization understand its cybersecurity risk. It focuses on managing risks to systems, people, assets, data, and capabilities. This includes managing assets and assessing risks.
What is the purpose of the Protect function in the NIST Cybersecurity Framework?
The Protect function ensures critical infrastructure services are safe. It helps limit the impact of a cybersecurity event. This includes controls for identity management, access control, data security, and system security.
How does the Detect function of the NIST Cybersecurity Framework help organizations?
The Detect function helps spot cybersecurity events quickly. It includes detecting anomalies and monitoring continuously. This ensures protective measures work well and finds potential security issues.
What is the purpose of the Respond function in the NIST Cybersecurity Framework?
The Respond function is about taking action when a cybersecurity incident happens. It includes planning for responses, communicating, and analyzing to help with recovery.
How does the Recover function of the NIST Cybersecurity Framework help organizations?
The Recover function helps restore services or capabilities lost due to a cybersecurity incident. It includes planning for recovery and improving resilience to ensure business continuity.
What are the implementation tiers of the NIST Cybersecurity Framework?
The framework has four implementation tiers: Partial, Risk Informed, Repeatable, and Adaptive. These tiers show an organization’s level of cybersecurity risk management. Partial is the least mature, and Adaptive is the most advanced.
How can organizations get started with the NIST Cybersecurity Framework?
To start, organizations should set priorities and scope their project. They should assess their current cybersecurity, identify relevant regulations, and conduct a risk assessment. Then, create a target profile and develop an action plan to fill the gaps.