Cybersecurity is undergoing a fundamental shift. Organizations once relied on reactive defenses to block known threats. But today’s attacks are stealthier, faster, and more dynamic than ever. Threat actors now leverage automation, artificial intelligence, and globally distributed infrastructure to launch campaigns that bypass conventional defenses within seconds.
In this volatile environment, defending against yesterday’s threats is no longer sufficient. What organizations now need is predictive cybersecurity—a strategy focused on anticipating threats before they strike, identifying vulnerabilities before they are exploited, and automating defense mechanisms to stay ahead of adversaries.
This article explores the persistent pain points in modern cybersecurity, highlights the limitations of reactive strategies, and demonstrates how predictive cybersecurity—when effectively implemented—transforms risk management from passive defense into proactive resilience. It also shows how Peris.ai’s focused and integrated solutions enable this evolution, without relying on a hard sell of its full product lineup.
Pain Points: Why Traditional Cybersecurity Fails to Keep Up
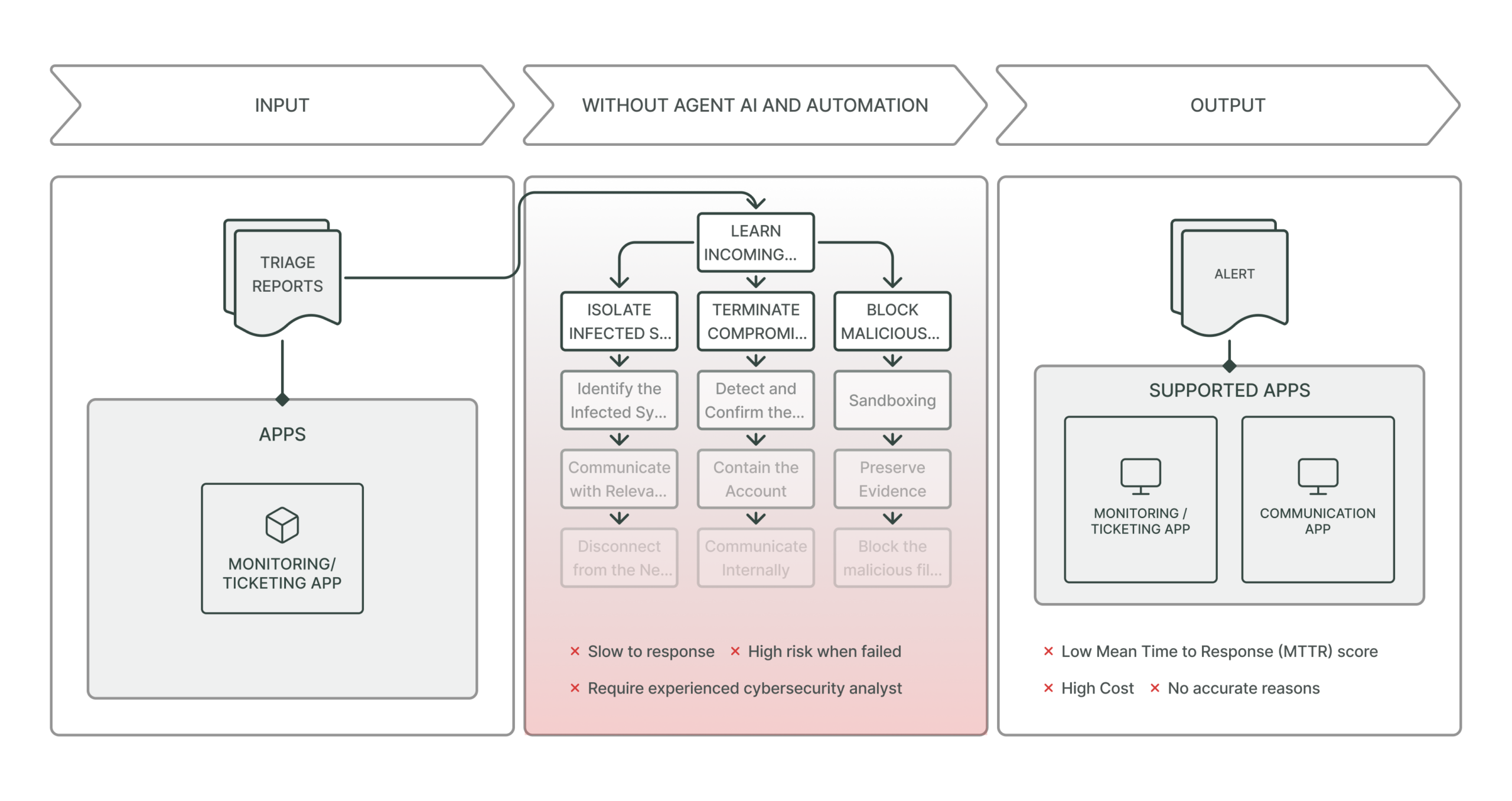
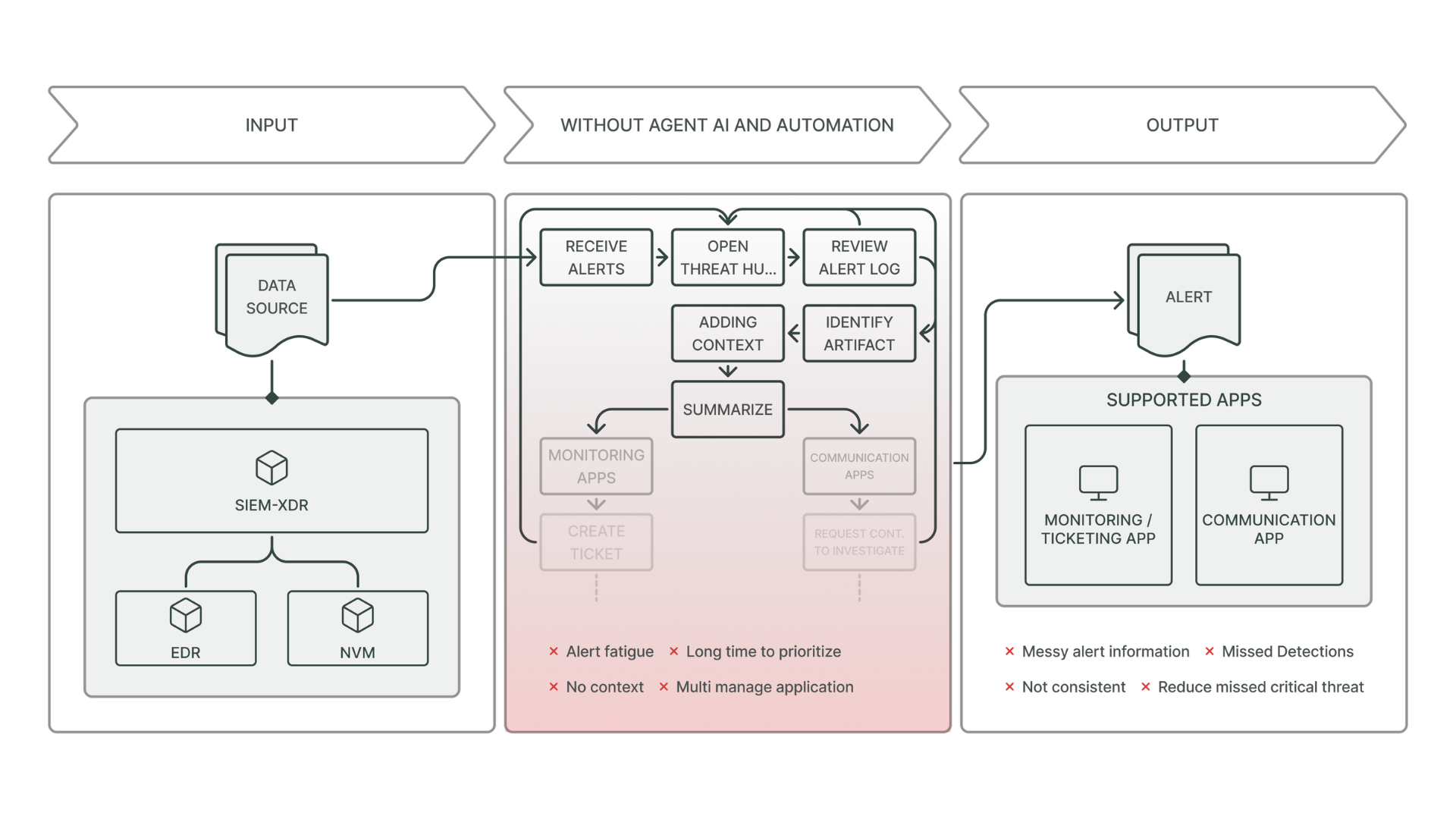
1. Alert Fatigue and Missed Threats
Security teams are inundated with thousands of alerts daily from SIEMs, EDRs, and firewalls. Most are false positives or redundant. As a result, genuine threats are often overlooked, delayed, or ignored—making quick and accurate responses nearly impossible.
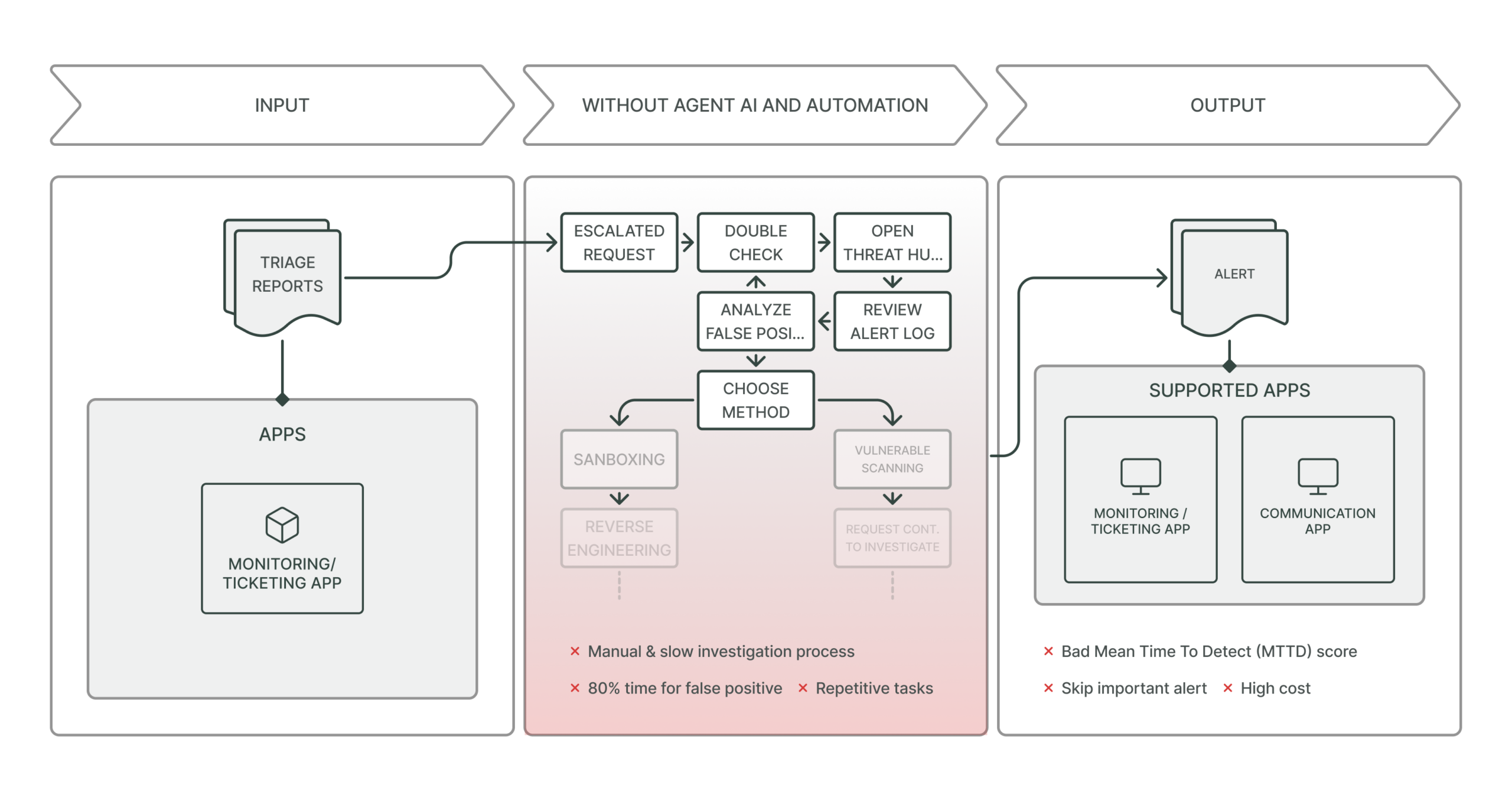
2. Delayed Detection and Response
In many cases, detection occurs after an attacker has already established a foothold in the system. In numerous sectors, average dwell time still exceeds 200 days. By the time a breach is discovered and investigated, the damage has often become irreversible.
3. Lack of Context and Threat Intelligence
Without real-time, contextual threat intelligence, alerts lack actionable meaning. Security analysts struggle to prioritize incidents or determine which threats pose an immediate and significant risk.
4. Reactive Security Postures
Most organizations maintain static security policies and controls that fail to adapt to evolving adversary tactics. Reactive postures focus on firewalls and traditional endpoints, offering little defense against social engineering, insider threats, or cloud misconfigurations.
5. Limited Human Resources
The global talent shortage in cybersecurity leaves many teams under-resourced. Most security operations centers (SOCs) don’t have enough analysts to monitor threats around the clock or investigate anomalies in real time.
The Case for Predictive Cybersecurity
From Indicators to Anticipation
Predictive cybersecurity fundamentally changes how organizations approach threats. Instead of reacting post-breach, predictive strategies identify early indicators, model attacker behavior, and trigger preemptive actions to mitigate risk.
This includes capabilities such as:
- Behavioral analytics and anomaly detection
- Threat hunting powered by machine learning
- Continuous asset and vulnerability scanning
- Real-time correlation with external threat intelligence
- Simulation of likely attack paths before they’re exploited
Strategic Benefits
- Early Threat Containment: Stop threats before lateral movement begins
- Faster Incident Response: Reduce the time between signal and action
- Reduced False Positives: Improve alert fidelity and triage speed
- Better Resource Allocation: Focus teams on high-impact tasks
- Proactive Vulnerability Management: Prioritize exposures before exploitation
Predictive cybersecurity is especially critical in hybrid environments, where the attack surface spans cloud infrastructure, mobile endpoints, on-premise systems, and third-party platforms.
Key Capabilities for Predictive Defense
To implement predictive cybersecurity effectively, organizations must build or adopt the following capabilities:
1. Behavioral Detection and Baseline Analysis
Machine learning algorithms establish baseline behavior for users, devices, and networks—then flag anomalies in real time. This allows organizations to detect threats such as credential misuse or insider attacks before they escalate.
2. Continuous Asset Discovery and Risk Assessment
A dynamic asset inventory, enriched with external scanning and internal telemetry, helps identify which systems are most exposed. Open ports, outdated configurations, and internet-facing services must be continuously monitored and assessed.
3. Threat Intelligence Integration
Aggregating threat data from global sources—including malware campaigns, dark web chatter, and APT activity—enables organizations to anticipate attacks targeted at their industry, geography, or tech stack.
4. Automation Playbooks
Standardized response workflows triggered by specific behavioral patterns (e.g., brute-force login attempts, beaconing activity) reduce response times and eliminate human delay in high-confidence scenarios.
5. Red Team Simulation and Retesting
Regular simulation of adversary techniques allows teams to validate their detection capabilities. Retesting ensures defensive improvements are effective and continuously aligned with evolving threat tactics.
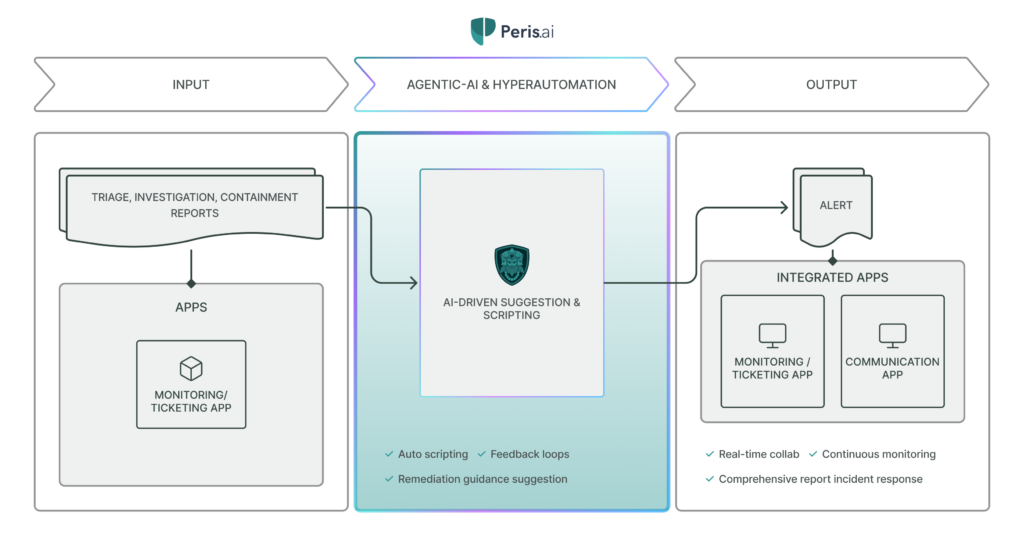
How Peris.ai Enables Predictive Cybersecurity
Instead of offering a bloated array of disjointed tools, Peris.ai delivers targeted, deeply integrated solutions that empower predictive defense without overwhelming security teams.
INDRA: Threat Intelligence Integration That Adds Context
One of the biggest challenges in predictive cybersecurity is turning data into actionable insight. INDRA solves this by:
- Correlating real-time threat data with internal activity patterns
- Prioritizing alerts based on known attacker infrastructure and intent
- Enriching detections with context from ongoing APT campaigns or malware families
INDRA goes beyond collecting indicators—it helps organizations anticipate what’s coming next and prepare accordingly.
BimaRed: Mapping the Most Probable Entry Points
Visibility is foundational to prediction. BimaRed delivers this by:
- Continuously scanning for exposed cloud, on-prem, IoT, and SaaS assets
- Assigning adaptive risk scores based on attacker reconnaissance trends
- Simulating the external view of attackers to identify where they’re most likely to strike
This allows organizations to reinforce vulnerable points before they’re targeted.
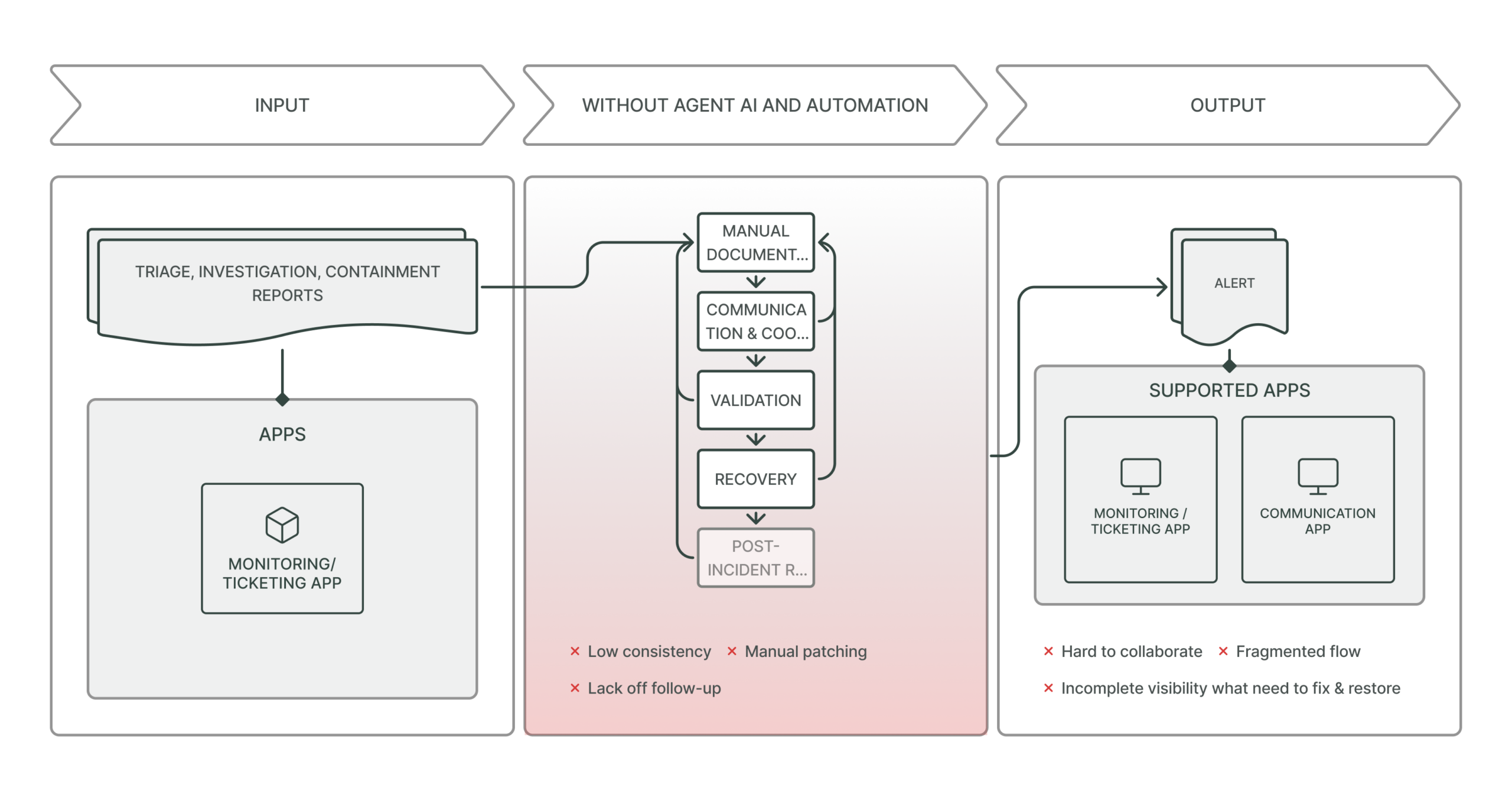
Brahma Fusion: Automating Pre-Incident Response
Knowing a threat exists is only useful if you can respond in time. Brahma Fusion closes the gap by:
- Auto-triaging alerts and suppressing benign patterns
- Activating playbooks based on behavioral deviation or threat context
- Simulating expert analyst decisions to reduce mean time to response (MTTR)
Brahma Fusion empowers SOCs to act on early signals, not just react to confirmed breaches.
Real-World Scenarios: Predictive Defense in Action
Scenario 1: Anticipating a Credential Stuffing Attack
Anomalous login attempts are detected across a public-facing portal. INDRA correlates this with a recently reported breach of a third-party service used by the client.
Action: Brahma Fusion initiates conditional MFA, blocks risky IPs, and flags the accounts for verification—before any compromise occurs.
Scenario 2: Preventing Cloud Exploitation
BimaRed discovers a misconfigured S3 bucket with write permissions open to the public. Based on trending attack vectors in INDRA’s feed, this is flagged as a high-probability target.
Action: The system preemptively restricts permissions and notifies the cloud security team—closing the gap before it’s weaponized.
Scenario 3: Early Containment of Insider Threats
A developer begins accessing large volumes of R&D files at abnormal hours. INDRA identifies that the access pattern resembles known espionage tactics.
Action: Brahma Fusion temporarily limits access, initiates a full session audit, and Pandava launches a simulated exfiltration test. The threat is neutralized internally without user disruption.
Key Outcomes of Predictive Cybersecurity with Peris.ai
- Reduced Investigation Time: Alerts arrive enriched with relevant threat context, minimizing triage cycles
- Early Warning: See patterns that predict attacks before payloads are delivered
- Smarter Prioritization: Distinguish between anomalies and genuine threats quickly
- Operational Efficiency: Automate early-stage detection and containment
- Adaptive Resilience: Defenses improve over time by learning from every event, not just attacks
Best Practices for Building a Predictive Cybersecurity Strategy
1. Start with What You Know
- Map all existing assets and user behaviors
- Identify critical systems and data flows
2. Integrate Threat Intelligence Early
- Don’t just collect threat feeds—use them to drive risk scoring and automated actions
3. Test Continuously
- Simulate common attack scenarios such as phishing, credential stuffing, and API abuse regularly
4. Use Machine Learning Thoughtfully
- Focus on augmenting analysts—not replacing them—with predictive insights and baselines
5. Automate with Confidence Thresholds
- Set risk-based triggers for containment that balance speed with accuracy to avoid false flags or downtime
Predictive Cybersecurity Isn’t a Luxury—It’s a Necessity
Today’s threats move fast. Tomorrow’s will move faster.
Predictive cybersecurity is how modern organizations stay ahead. It’s how they protect sensitive data, meet compliance mandates, reduce response times, and ensure business continuity in an ever-evolving threat landscape.
Peris.ai makes this possible—not through a flood of tools, but through intelligence, automation, and integrated action embedded across critical defense layers.
Conclusion: Don’t Just Defend—Anticipate
Proactive organizations don’t just react to cyberattacks. They anticipate them. They prepare in advance. They disrupt the attack chain before it begins.
Predictive cybersecurity with Peris.ai means:
- Seeing beyond the immediate alert
- Acting before an attacker makes a move
- Building systems that learn, adapt, and respond on your behalf
Start defending forward. Predict what’s coming. Secure what matters.
Learn more at https://peris.ai/