For Software-as-a-Service (SaaS) companies, growth is both the goal and the challenge. Rapid user adoption, global expansion, and infrastructure complexity are signs of success—but they also multiply security risks. As you scale, your attack surface widens, compliance requirements become tougher, and downtime becomes costlier.
SaaS teams often face a harsh reality: security can’t keep up with the pace of product innovation. Manual processes, patchwork tools, siloed teams, and reactive incident handling create a dangerous gap between speed and safety.
Peris.ai Cybersecurity was built to close that gap—by enabling SaaS companies to scale securely, intelligently, and efficiently using a modular, AI-powered cybersecurity platform tailored for fast-moving digital products.
This article explores how Peris.ai helps modern SaaS platforms scale without compromise.
Chapter 1: The Hidden Security Struggles of Scaling SaaS
While SaaS companies chase product-market fit, they often overlook how their security posture evolves (or degrades) with scale. Common challenges include:
1. Expanding Attack Surface
Each new integration, subdomain, or feature release potentially opens a new door for attackers. From exposed APIs to forgotten staging servers, SaaS growth often leaves security blind spots.
⚙️ 2. DevSecOps Misalignment
Engineering teams push new features fast. Security teams chase vulnerabilities slower. This disconnect delays releases, frustrates developers, and leads to friction that slows innovation—or worse, leads to risky shortcuts.
3. Inconsistent Identity & Access Management
As teams grow and roles shift, access rights are rarely updated. SaaS platforms face risks from overprivileged users, ex-employee credentials, and misconfigured IAM.
4. Patchwork Security Stack
Most SaaS teams start with point solutions—an EDR here, a vulnerability scanner there—but lack orchestration. The result? Alert fatigue, disconnected workflows, and no single source of truth.
5. Compliance Lag
New markets often bring new regulations. GDPR, SOC 2, ISO 27001, HIPAA—each one adds overhead. Without automation, compliance becomes a bottleneck instead of a growth enabler.
Chapter 2: Peris.ai’s Modular Security Architecture for SaaS
Peris.ai offers a hyperautomated, modular platform that adapts to your architecture, use case, and growth stage. Unlike monolithic tools that force rigid workflows, Peris.ai allows SaaS providers to plug in exactly what they need—across visibility, threat detection, automation, and compliance.
Core Modules for Scaling SaaS Securely
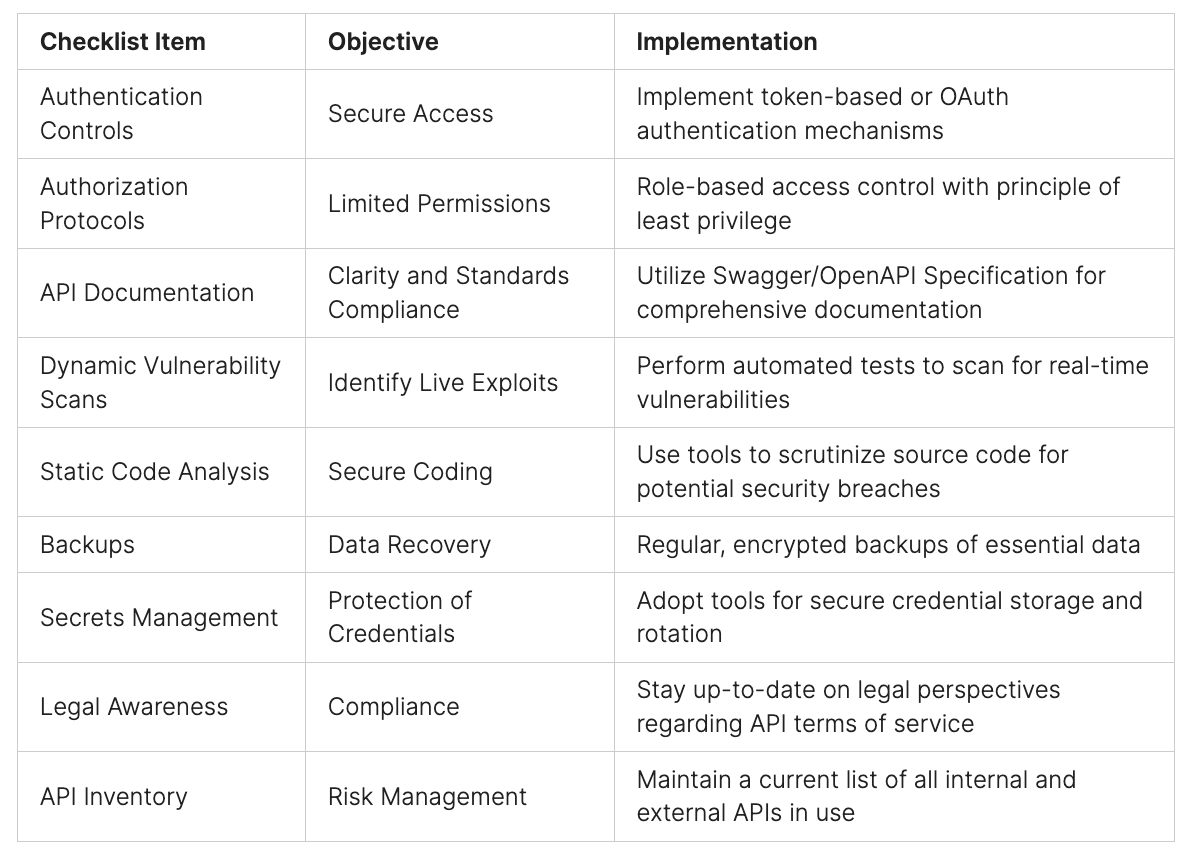
️ 1. BimaRed – Attack Surface Management (ASM)
As you add new endpoints, domains, and microservices, BimaRed continuously scans your environment, identifies vulnerabilities, and prioritizes them based on exploitability and business impact.
Benefits for SaaS:
- Discover shadow APIs and forgotten subdomains
- Prioritize CVEs based on exposure level
- Enable developers to patch via integrated ticketing (e.g., JIRA, GitLab)
Use Case Example: A SaaS analytics provider used BimaRed to reduce their public-facing vulnerabilities by 62% in 3 weeks—without disrupting development sprints.
2. IndraCTI – Contextual Threat Intelligence (CTI)
Scaling introduces exposure to targeted attacks, phishing, and zero-day exploits. IndraCTI ingests global threat feeds, correlates them with internal telemetry, and provides context-aware alerts.
Benefits for SaaS:
- Detects emerging threats relevant to your tech stack
- Correlates phishing campaigns with targeted domains
- Prioritizes response based on industry-specific risks
Use Case: A SaaS HR tech company prevented credential stuffing attacks after IndraCTI detected dark web chatter about a targeted email campaign.
⚙️ 3. BrahmaFusion – Hyperautomation & SOAR-like Engine
At the heart of Peris.ai’s platform is BrahmaFusion—an AI-driven orchestration and automation engine. It replaces repetitive tasks, speeds up triage, and connects all your tools and teams.
Capabilities:
- Automated alert triage & ticket creation
- Real-time compliance control checks
- Response playbooks with auto-remediation actions
Impact for SaaS Teams:
- Cut Mean Time to Respond (MTTR) by over 40%
- Eliminate 35% of manual workloads
- Scale security workflows across cloud environments
4. Pandava – Pentest-as-a-Platform
Every SaaS product needs periodic penetration testing—especially to meet SOC 2, ISO 27001, and investor diligence. Pandava brings this in-house with a real-time dashboard, verified ethical hackers, and continuous testing workflows.
Features:
- Collaborative dashboard between dev and security
- Track remediation in real time
- Support for ISO, OWASP, and custom frameworks
5. IRP – Incident Response Platform
SaaS teams can’t afford downtime or reputation damage. The IRP module ensures rapid, orchestrated response across IT, security, and engineering.
Includes:
- Centralized incident case management
- Playbook builder for breach response
- Integration with email, Slack, ticketing, and firewalls
Chapter 3: Business Benefits of Peris.ai for SaaS Companies
1. Security That Scales with You
Peris.ai grows as you grow—supporting everything from early-stage MVPs to enterprise-grade multi-cloud systems.
2. Compliance Simplified
With automation and real-time mapping to frameworks like SOC 2 and ISO 27001, compliance becomes an ongoing advantage—not an annual headache.
3. Data-Driven Security Decisions
Get real-time visibility into threats, compliance gaps, and asset exposure—turning security from a black box into a business driver.
Chapter 4: Real-World Case Studies
Case Study 1: SaaS Fintech Scaling to Southeast Asia
Problem: The company lacked visibility over its cloud attack surface and was unprepared for SOC 2 audits as it expanded into three new countries.
Solution with Peris.ai:
- BimaRed scanned and prioritized over 300 exposed assets
- BrahmaFusion automated compliance control checks for SOC 2
- IRP handled 3 security incidents with under 5-minute response times
Outcome: The company passed its SOC 2 audit with zero findings, cut response time by 66%, and onboarded 10,000+ new users confidently.
⚙️ Case Study 2: AI SaaS Startup Using Multi-Cloud
Problem: Rapid releases and infrastructure sprawl across AWS and GCP led to misconfigurations and IAM drift.
Solution with Peris.ai:
- IndraCTI detected abnormal login behavior tied to leaked credentials
- Pandava helped simulate attacks across cloud environments
- BrahmaFusion automated revocation of suspicious tokens
Impact: Prevented breach escalation, tightened access controls, and built executive confidence in security maturity—essential for Series A fundraising.
Chapter 5: Why Modular Matters in SaaS Security
Peris.ai’s modular approach means you don’t need to over-engineer your security stack. You can:
- Start with ASM and CTI
- Add IRP and Pandava during scale
- Enable full compliance automation as you expand into regulated sectors
This flexibility lowers friction, reduces costs, and increases adoption across both technical and non-technical teams.
Conclusion: Secure Growth Starts with Smart Architecture
Scaling a SaaS product is hard. Doing it securely is harder. But it shouldn’t be.
Peris.ai brings the modularity, automation, and intelligence needed to build a secure SaaS company without slowing down growth. From discovery to detection, compliance to containment, you get a scalable cybersecurity framework built for agility—not bureaucracy.
Whether you’re building your first MVP or entering new markets, Peris.ai is the security partner that helps you move fast—without breaking things.
Ready to Secure Your SaaS Platform?
Discover how Peris.ai helps SaaS companies accelerate growth securely with modular, AI-driven security automation.
Learn more at www.peris.ai Contact our team: contact@peris.ai