As we approach the new year, it is crucial for businesses to familiarize themselves with the potential cloud security threats that could jeopardize their operations. With the increasing innovation of attackers and the advancements in technologies such as AI and quantum computing, organizations must be proactive in developing a flexible and comprehensive security strategy. By staying prepared and informed, businesses can safeguard their digital assets and maintain the trust of their customers.
Key Takeaways:
- Businesses need to be aware of the potential cloud security threats that could impact their operations.
- Developing a flexible and comprehensive security strategy is crucial in safeguarding digital assets.
- Technologies such as AI and quantum computing are expected to bring changes to the cloud landscape.
- Organizations must adopt quantum-resistant encryption algorithms and protocols to defend against quantum threats.
- AI-powered attacks can pose both positive and negative implications for cybersecurity, necessitating robust security controls.
Quantum Disrupting Security: A Growing Threat
Quantum computing is a rapidly emerging technology that has the potential to revolutionize various fields, including encryption and security. With its extraordinary computational power, quantum computers pose a serious threat to the security of current encryption standards.
“As quantum computers become more powerful and accessible, traditional encryption methods may become obsolete.”
Traditional encryption algorithms, such as RSA and AES, rely on the difficulty of certain mathematical problems, such as factoring large numbers, to protect sensitive data. However, quantum computers can solve these problems much faster than classical computers, rendering these encryption methods vulnerable.
To defend against the impending quantum threat, organizations need to adopt quantum-resistant encryption algorithms and protocols. These cryptographic techniques are specifically designed to withstand quantum attacks and provide robust security in the post-quantum era.
It is crucial for organizations to stay proactive and vigilant in monitoring the quantum computing landscape. By staying updated on the latest developments and best practices, businesses can ensure they are well-prepared to mitigate the risks associated with quantum computing.
Quantum-Resistant Encryption Algorithms
Quantum-resistant encryption algorithms, also known as post-quantum cryptography, are designed to resist attacks from both classical and quantum computers. These algorithms are based on mathematical problems that are believed to be hard for both types of computers to solve.
Some of the prominent quantum-resistant encryption algorithms include:
- Lattice-based cryptography
- Code-based cryptography
- Multivariate cryptography
- Hash-based cryptography
- Isogeny-based cryptography
Implementing these quantum-resistant encryption algorithms and protocols can significantly enhance the security of organizations’ sensitive information in the face of evolving threats from quantum computing.
Staying Ahead of the Quantum Threat
As quantum computing continues to advance, it is essential for businesses and security professionals to stay informed and proactive. Adopting quantum-resistant encryption algorithms is just one aspect of defending against the quantum threat.
Organizations should also:
- Regularly assess their security infrastructure and protocols
- Upgrade their encryption standards to be quantum-resistant
- Monitor the progress in quantum computing research and its potential implications for security
- Collaborate with experts and institutions in the field to establish best practices
By taking these proactive measures, businesses can better prepare themselves for the challenges posed by quantum computing and safeguard their sensitive data from future security breaches.

AI-Powered Attacks: Harnessing New Technologies for Malicious Purposes
Artificial intelligence (AI) is revolutionizing various industries, including cybersecurity. While AI presents opportunities for improving security measures, it also introduces new risks and challenges. Cybercriminals are harnessing AI to launch sophisticated and stealthy attacks, posing significant threats to businesses and individuals alike.
Deepfake Attacks: Manipulating Reality for Ill Intent
One alarming application of AI in cyber attacks is deepfake technology. Deepfake refers to the use of AI algorithms to manipulate images, videos, and audio, creating hyper-realistic fake content that is difficult to discern from authentic media. Malicious actors leverage deepfake technology to spread misinformation, engage in identity theft, and perpetrate social engineering attacks.
Deepfake attacks can have severe consequences for individuals and organizations. By convincingly impersonating someone, attackers can deceive users into sharing sensitive information, compromising personal and corporate security. As deepfake technology evolves, it becomes increasingly challenging to detect and prevent these malicious activities.
Adversarial AI: Outsmarting Defenses with AI
Another concerning aspect of AI-powered attacks is the use of adversarial AI. Adversarial AI refers to AI algorithms that are designed to exploit vulnerabilities in machine learning systems. These attacks aim to manipulate AI models by subtly altering input data, leading to incorrect outputs or system failures.
Adversarial AI attacks have the potential to bypass traditional security defenses, evade detection mechanisms, and compromise the integrity of AI-powered systems. By exploiting vulnerabilities in AI algorithms or training data, attackers can undermine the reliability and trustworthiness of AI-driven technologies.
Counteracting AI-Powered Attacks: Building Resilient Cybersecurity
To defend against AI-powered attacks, organizations must proactively invest in AI-based cybersecurity solutions. Utilizing AI technologies can help augment security defenses, automate threat detection and response, and enhance incident management capabilities. By leveraging AI, cybersecurity professionals can better analyze vast amounts of data, identify patterns, and detect anomalies in real-time.
However, simply relying on AI-based solutions is not enough. Organizations must also implement robust security controls and policies. This includes implementing multi-factor authentication, regular vulnerability assessments and penetration testing, and user awareness training. Maintaining an educated and proactive workforce is crucial to prevent falling victim to AI-powered attacks.
Moreover, collaboration and information sharing among businesses, cybersecurity experts, and law enforcement agencies are essential. By working together, organizations can strengthen their defenses, share knowledge on emerging threats, and develop effective countermeasures against AI-powered attacks.
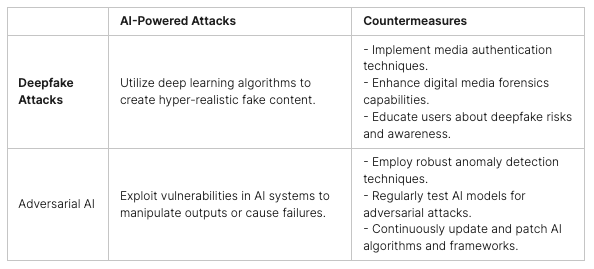
In conclusion, the rise of AI-powered attacks poses significant challenges to cybersecurity. Deepfake attacks and adversarial AI techniques are growing threats that require immediate attention. By investing in AI-based cybersecurity solutions, implementing robust security controls, and fostering collaboration within the industry, organizations can effectively counter these malicious AI-driven activities and safeguard their digital assets.
Ransomware: A Persistent and Evolving Threat
Ransomware continues to pose a significant threat in the realm of cybersecurity. This form of malware encrypts victims’ files and holds them hostage until a ransom is paid, often in the form of cryptocurrency.
What makes ransomware especially dangerous is its adaptability. Attackers are constantly evolving their tactics, employing advanced encryption algorithms and sophisticated extortion techniques to maximize their profits and avoid detection.
Organizations must take a proactive approach to protect themselves from ransomware attacks. This involves implementing a comprehensive cybersecurity strategy that encompasses prevention, detection, response, and recovery.
Patching systems and keeping software up to date is crucial in mitigating vulnerabilities that attackers may exploit. Additionally, organizations must employ robust security measures to limit network exposure and ensure proper user education on recognizing and handling phishing emails and suspicious links.
Awareness and preparedness are key to minimizing the impact of ransomware attacks. Regularly backing up important files and storing them offline or in a secure cloud environment can help organizations recover their data without succumbing to the demands of attackers.
It is also essential to have a well-defined incident response plan in place. This plan should include steps to isolate infected systems, identify the type of ransomware, and notify the appropriate authorities.
By understanding the persistent nature of ransomware and implementing effective protection measures, organizations can minimize the risks associated with this ever-evolving cyber threat.

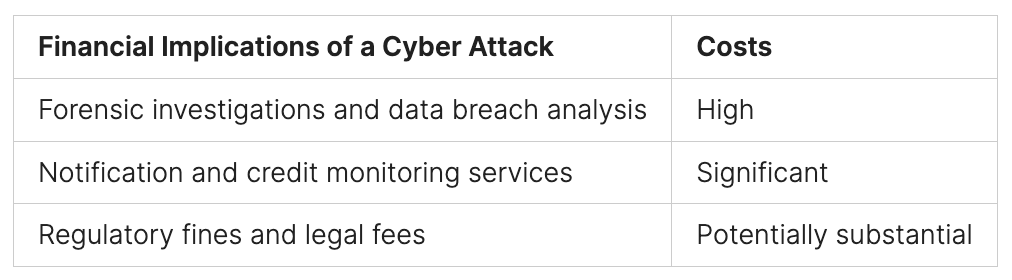
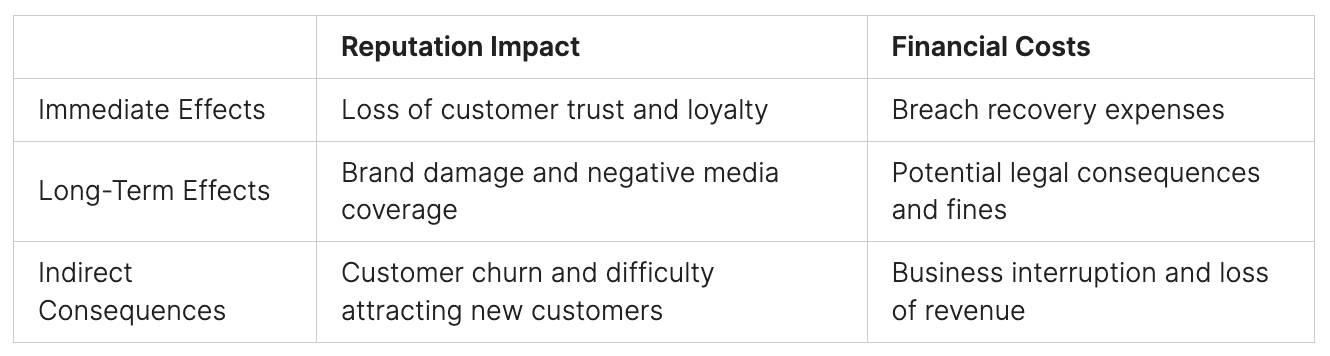
The Impact of Ransomware Attacks
Ransomware attacks can cause significant financial losses and reputational damage for businesses. Organizations that fall victim to ransomware may experience operational disruptions, loss of sensitive data, and potential legal and regulatory liabilities.
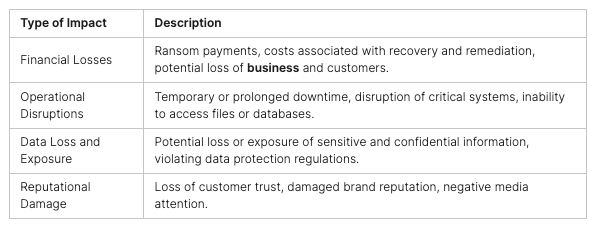
It is vital for businesses to prioritize ransomware prevention and preparedness as part of their overall cybersecurity strategy. By investing in robust defenses, regular employee training, and incident response planning, organizations can mitigate the risks and consequences associated with this persistent and evolving threat.
Cloud Computing Challenges: Navigating Data Security and Compliance
While cloud computing offers numerous advantages, it also introduces new challenges in terms of data security and compliance. With the increasing adoption of cloud services, organizations must ensure that their sensitive information is protected and that they meet regulatory requirements.
One of the main challenges is the risk of misconfigured cloud storage accounts. Improperly configured storage settings can expose sensitive data to unauthorized access and increase the likelihood of data breaches. It is essential for businesses to implement proper access controls and regularly audit their cloud storage settings to prevent these vulnerabilities.
Infrastructure vulnerabilities also pose a significant threat to cloud data security. Weaknesses in the underlying cloud infrastructure can be exploited by attackers to gain unauthorized access to data. Organizations must work closely with cloud service providers to ensure that robust security measures are in place to protect their data.
“Ensuring data security and compliance in the cloud is a shared responsibility between the organization and the service provider.”
Organizations must prioritize access control mechanisms to limit who can access their cloud resources and data. Implementing strong authentication methods, such as multi-factor authentication, can help prevent unauthorized access. Additionally, regular monitoring and logging of access activities can provide insight into potential security breaches and aid in incident response.
Compliance with regulations and industry standards is critical in cloud environments. Organizations need to stay up to date with evolving data protection laws and compliance requirements to ensure their cloud operations align with legal and regulatory obligations. Conducting regular compliance assessments and audits can identify any gaps and help organizations address them effectively.
Best Practices for Cloud Data Security and Compliance:
- Implement strong access controls, including multi-factor authentication
- Regularly review and update cloud storage settings to prevent misconfigurations
- Work closely with cloud service providers to ensure robust security measures are in place
- Monitor and log access activities for early detection of security breaches
- Stay up to date with data protection laws and compliance requirements
- Conduct regular compliance assessments and audits
- Train employees on cloud security best practices
By addressing these cloud computing challenges and prioritizing data security and compliance, organizations can leverage the benefits of cloud technology while mitigating potential risks and ensuring the confidentiality, integrity, and availability of their data.

Complexity in Multi-Cloud Environments: Managing Security in a Sprawling Landscape
Managing security in multi-cloud environments can be a daunting task due to the complexity and variety of cloud platforms and services. With businesses relying on multiple cloud providers to meet their diverse needs, administrators often struggle to maintain control over their sprawling estates. This complexity introduces potential vulnerabilities, making it crucial for organizations to prioritize cloud security and implement effective security controls.
One of the main challenges in managing security in a multi-cloud environment is ensuring consistent security practices across different platforms. Each cloud provider has its own set of security features and configurations, requiring administrators to have a deep understanding of each provider’s security controls. This can be time-consuming and error-prone, increasing the risk of misconfigurations and leaving cloud environments exposed to cyber threats.
To address these challenges, organizations must adopt a comprehensive security strategy that includes a centralized platform for managing all their cloud assets and configurations. This centralized platform allows administrators to enforce consistent security policies and controls across all cloud providers, simplifying the management process and reducing the risk of human errors. Additionally, it provides a holistic view of the entire multi-cloud environment, enabling administrators to identify potential security gaps and take proactive measures to mitigate them.
Implementing strong security controls is crucial in a multi-cloud environment. This includes deploying robust access management policies, applying encryption to protect sensitive data at rest and in transit, and regularly monitoring the cloud environment for any suspicious activities or vulnerabilities. By leveraging cloud security solutions that offer advanced threat detection and automated security measures, organizations can strengthen their security posture and effectively mitigate the risk of cyber attacks.
Benefits of Centralized Security Management in Multi-Cloud Environments
Centralized security management brings several benefits to organizations operating in multi-cloud environments. Firstly, it provides a unified view of security across all cloud platforms, enabling administrators to monitor security events, investigate incidents, and respond quickly and efficiently. This level of visibility enhances the overall security posture of the organization and simplifies compliance with regulatory requirements.
Secondly, a centralized approach allows for the consistent enforcement of security policies and controls across multiple cloud providers. Administrators can define a set of standardized security configurations and apply them uniformly across all cloud environments, reducing the risk of misconfigurations and ensuring a high level of protection against potential threats.
Finally, centralized security management minimizes complexity in multi-cloud environments. Instead of juggling different security tools and interfaces for each cloud provider, administrators can leverage a single platform that integrates with all their cloud environments. This streamlines security operations, improves efficiency, and enables administrators to focus their time and resources on addressing real security risks rather than managing disparate security systems.
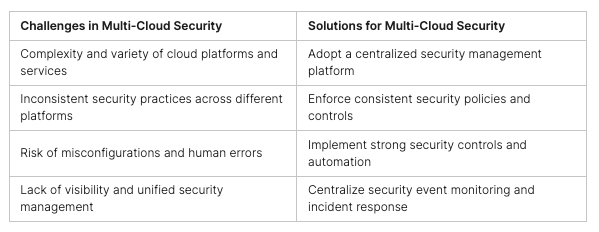

In conclusion, managing security in multi-cloud environments requires organizations to navigate through the complexity and variety of cloud platforms while ensuring consistent security practices across different providers. By adopting a centralized security management approach, organizations can streamline security operations, reduce complexity, and improve their overall security posture. With robust security controls and automated measures in place, businesses can confidently embrace the benefits of multi-cloud environments while effectively mitigating the risks and challenges they present.
Conclusion
As we advance into 2024, the imperative for businesses to intensify their cybersecurity initiatives has never been more critical, especially with the escalating threats in cloud security. The advent of quantum computing, AI-powered attacks, sophisticated ransomware, and the inherent challenges of cloud computing and multi-cloud environments demand a proactive and informed approach to cybersecurity. Businesses must stay abreast of the latest threats and advancements, embrace cutting-edge security solutions, and adopt best practices to safeguard their digital assets effectively.
The landscape of cloud security is continually evolving, necessitating that organizations adopt robust cybersecurity strategies to stay ahead of potential threats. By investing in the latest technologies and solutions, businesses can enhance their defenses and solidify their security postures. Cultivating a culture of awareness and preparedness is essential for mitigating risks associated with cloud security threats.
Furthermore, compliance with regulatory requirements and the implementation of effective access control measures are crucial for maintaining security integrity. Regular security assessments and audits play a vital role in identifying vulnerabilities and fostering continuous improvement in security practices. Additionally, establishing strong partnerships with reliable security providers and engaging actively in industry forums and networks are strategic moves that can significantly boost a business’s preparedness against cloud security challenges.
At Peris.ai Cybersecurity, we are dedicated to equipping businesses with the tools and expertise needed to navigate the complexities of cloud security. Our advanced solutions are designed to address the unique challenges of your business, ensuring compliance, enhancing security, and fostering a resilient cybersecurity posture. Visit us at Peris.ai Cybersecurity to explore how our tailored cybersecurity solutions can help protect your business against the emerging threats of the digital age. Let us help you stay one step ahead in the rapidly evolving world of cloud security.
FAQ
What are the top cloud security threats that businesses should prepare for in 2024?
The top cloud security threats that businesses should prepare for in 2024 include quantum computing disruptions, AI-powered attacks, ransomware, challenges of cloud computing, and managing security in multi-cloud environments.
How does quantum computing pose a threat to encryption and security?
Quantum computing has the potential to render traditional encryption methods obsolete. As quantum computers become more powerful, the encryption standards currently in use may no longer be sufficient. To defend against this threat, organizations need to adopt quantum-resistant encryption algorithms and protocols.
What are AI-powered attacks and how can organizations protect against them?
AI-powered attacks leverage artificial intelligence to create sophisticated and stealthy cyberattacks. To protect against these attacks, organizations need to invest in AI-based cybersecurity solutions, implement robust security controls and policies, and stay updated on the latest developments and best practices.
How can organizations protect themselves from ransomware attacks?
To protect against ransomware attacks, organizations should adopt a comprehensive strategy that includes patching systems, limiting network exposure, educating users, and having a plan to detect, respond to, and recover from attacks.
What are the main challenges of cloud computing in terms of data security and compliance?
The challenges of cloud computing in terms of data security and compliance include misconfigured cloud storage accounts, infrastructure vulnerabilities, and the potential exposure of sensitive information. Organizations must prioritize data security, access control, and compliance by implementing robust security measures, conducting regular assessments, and staying updated on evolving regulations and standards.
How can organizations manage security in multi-cloud environments?
Managing security in multi-cloud environments can be challenging due to the complexity and variety of cloud platforms and services. Organizations can improve security by adopting a comprehensive security strategy that includes a centralized platform for managing all cloud assets and configurations, reducing complexity and providing better control over the sprawling landscape.
How can businesses enhance their preparedness for cloud security threats?
Businesses can enhance their preparedness for cloud security threats by staying informed about the latest threats, adopting advanced security solutions, and implementing best practices such as proactive monitoring, continuous security training, and regular security assessments.