Multi-threading is a powerful technique in the realm of network security that has the potential to transform cybersecurity performance. By allowing programs to execute multiple tasks simultaneously on different cores or processors, multi-threading significantly improves efficiency and response time. This, in turn, enhances the overall effectiveness of network security systems.
Key Takeaways:
- Multi-threading enables real-time packet analysis and intrusion detection, enhancing network security.
- It improves security efficiency by reducing the impact of network latency.
- Multi-threading increases the scalability of game servers, allowing them to handle larger amounts of data and more players.
- Challenges like synchronization, concurrency, and performance optimization need to be carefully addressed when implementing multi-threading in network security.
- Best practices such as the use of message queues, locks, and state machines can overcome the challenges of multi-threading.
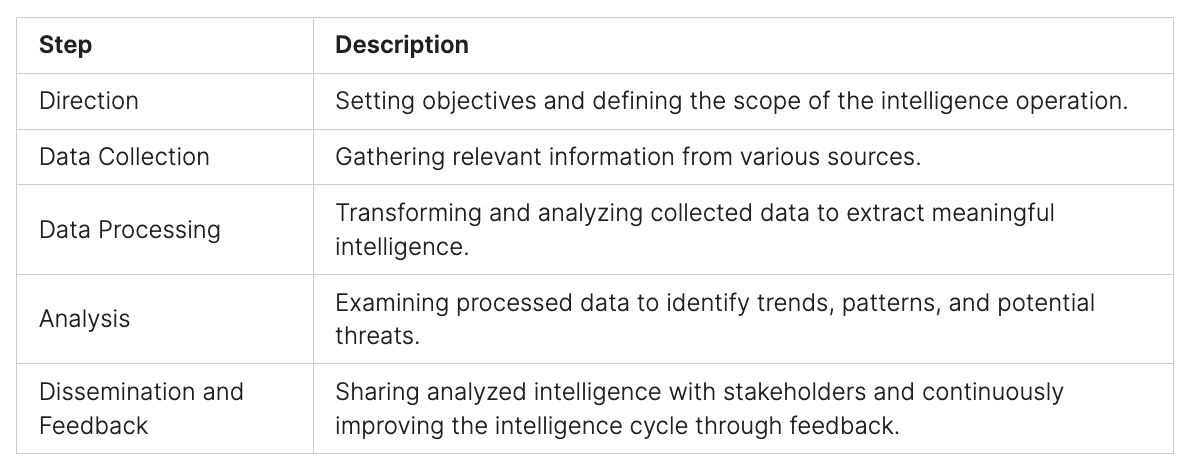
Benefits of Multi-Threading in Network Security
Multi-threading provides numerous benefits in the domain of network security. By utilizing separate threads for network communication, it effectively reduces the impact of network latency, resulting in a smooth and responsive user experience.
One major advantage of multi-threading is the increased throughput and scalability it offers to game servers. With the ability to handle larger amounts of data and accommodate more players, multi-threading enables advanced networking functions that enhance the overall performance of game servers.
Furthermore, multi-threading intensifies the security and reliability of network connections. By dedicating separate threads to encryption, compression, and error correction, network security systems can protect against malicious attacks and prevent data corruption, ensuring the integrity of sensitive information.
These benefits demonstrate the pivotal role of multi-threading in network security. Its ability to streamline network communication, improve server performance, and fortify data protection makes it an indispensable tool in the field of advanced networking.
Challenges of Multi-Threading in Network Security
While multi-threading can greatly enhance network security, it also introduces certain challenges. Synchronization, concurrency, and performance optimization are the key hurdles that need to be addressed for successful implementation.
Synchronization:
Synchronization is a critical aspect of multi-threading in network security. It involves coordinating and maintaining data consistency across different threads to prevent data corruption and race conditions. Ensuring proper synchronization is essential for maintaining the integrity and reliability of network security systems.
Concurrency:
Concurrent execution is a fundamental characteristic of multi-threading. In network security, multiple events may occur simultaneously, requiring effective management of concurrent threads. Managing concurrency involves handling shared resources, avoiding deadlocks and livelocks, and coordinating thread execution to minimize conflicts and maximize efficiency.
Performance Optimization:
Performance optimization is crucial for achieving optimal network speed and quality in a multi-threaded environment. Efficient resource utilization and minimizing overhead are key factors in improving the performance of multithreaded code. Performance optimization techniques, such as load balancing, thread pool management, and algorithmic improvements, are essential for maximizing the benefits of multi-threading in network security.
To overcome these challenges, careful attention to design and implementation is necessary. It requires expertise in synchronization mechanisms, concurrency control, and performance profiling.
“Effective synchronization, concurrency management, and performance optimization are pivotal for harnessing the full potential of multi-threading in network security.”
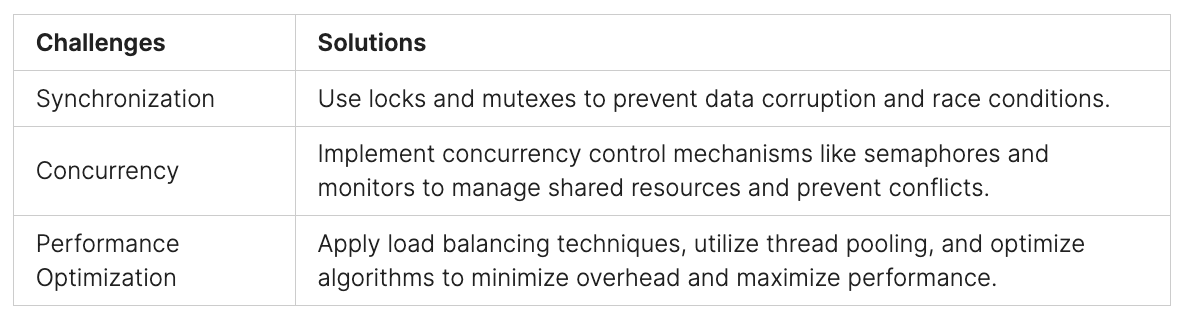
Addressing these challenges effectively ensures that multi-threading in network security delivers superior performance, scalability, and responsiveness.

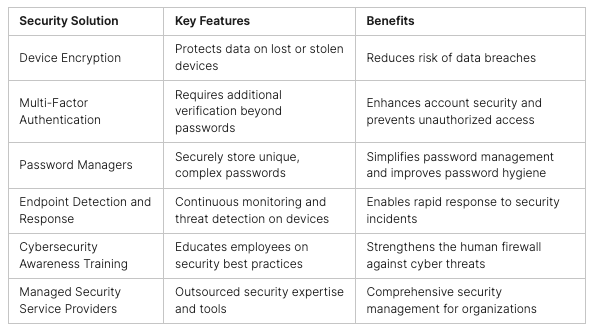
Solutions for Multi-Threading in Network Security
To overcome the challenges of multithreading in network security, several best practices can be implemented. The following solutions provide effective ways to address these challenges:
1. Message Queue
Implementing a message queue or buffer can facilitate efficient communication between threads in a multithreaded network security system. By reducing direct data access and modification, a message queue allows for seamless information exchange, improving overall performance and concurrency.
2. Locks and Mutexes
Utilizing locks and mutexes is crucial in protecting shared data or resources from simultaneous access. By employing these mechanisms, you can ensure data integrity and prevent race conditions, minimizing the risk of data corruption or security vulnerabilities.
3. State Machines and Protocols
Managing concurrency issues can be achieved through the use of state machines and protocols. By defining rules or steps for network event processing, these components enable efficient coordination and synchronization of multithreaded operations, ensuring consistent and reliable network security functionality.
4. Timeouts and Retry Mechanisms
Handling network failures and errors is essential in maintaining network integrity. By implementing timeouts and retry mechanisms, you can effectively manage and recover from network disruptions, enhancing the resilience and reliability of the network security system.
5. Profilers and Debuggers
To optimize the performance of a multithreaded network security system, profilers and debuggers can be utilized. These tools help identify performance bottlenecks, contention sources, or any other issues that may impact the efficiency of the system. With their insights, you can fine-tune the system for optimal performance and effectiveness.
By implementing these solutions, network security systems can successfully address the challenges associated with multithreading, ensuring robustness, efficiency, and effectiveness in safeguarding network resources and data.
Implementation of Multi-Threading in Network Security
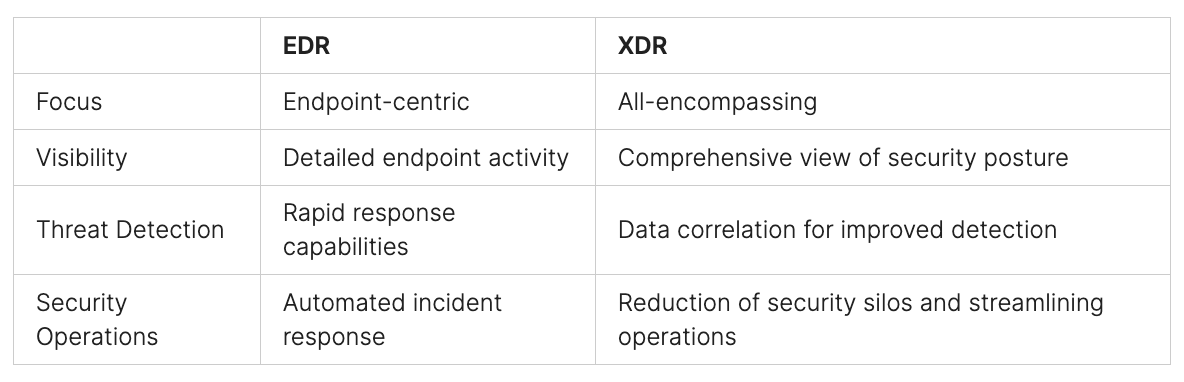
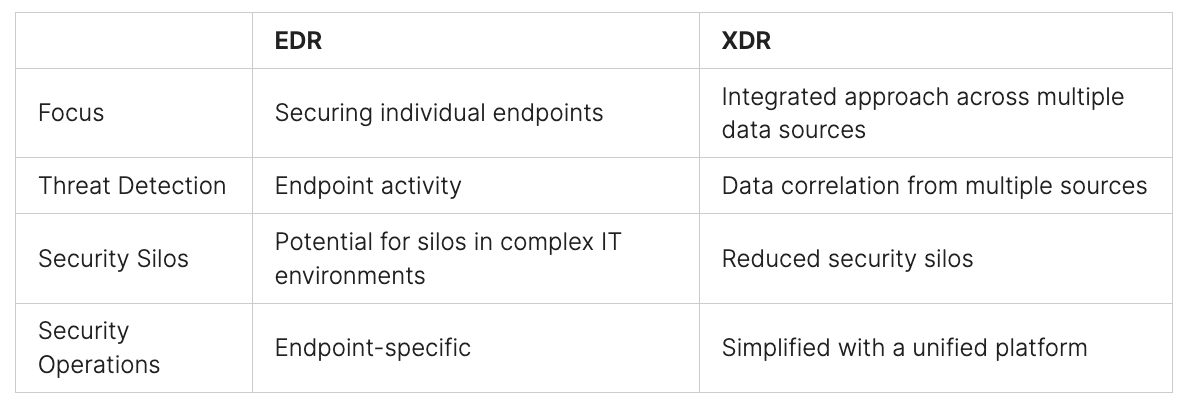
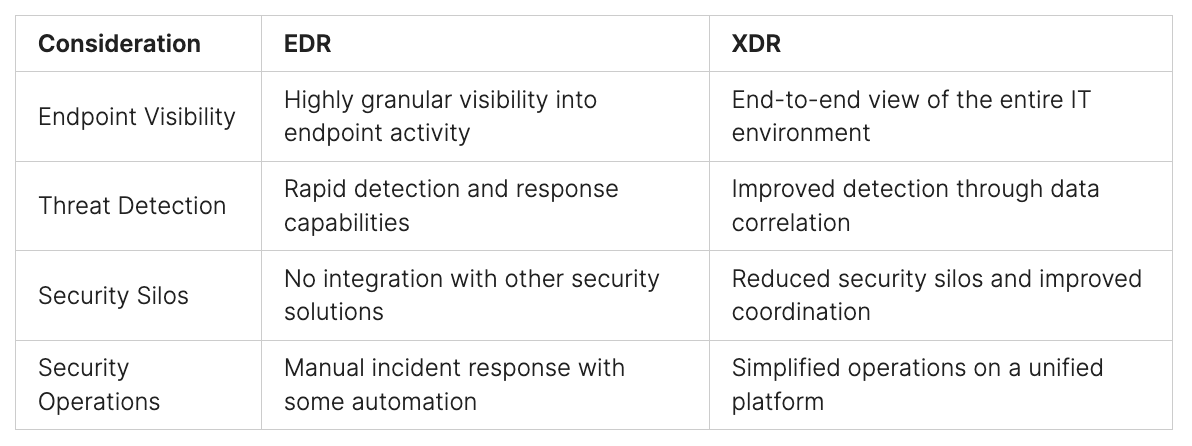
The implementation of multi-threading in network security relies on the chosen game engine or framework, each offering its own set of tools, libraries, APIs, and interfaces. These resources are instrumental in creating and managing threads and facilitating network communication. For instance, Unity provides the System.Threading namespace for multi-threading and the UnityEngine.Networking namespace for network communication. In comparison, Unreal Engine offers classes like FRunnable and FRunnableThread for multi-threading, and UNetDriver and UNetConnection for network communication. It is vital to consult the engine or framework’s documentation and examples to adhere to their implementation guidelines and conventions for multi-threading and network programming.
“The implementation of multi-threading in network security depends on the chosen game engine or framework.”
Table:
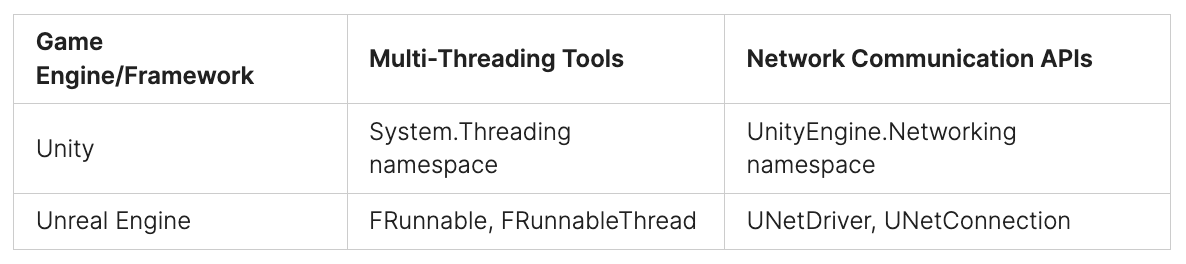
Please note that the table above illustrates some examples of game engines and corresponding multi-threading tools and network communication APIs.
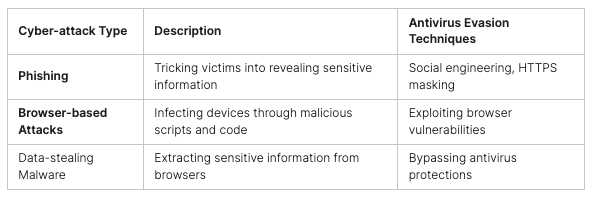
Examples of Multi-Threading in Network Security
Many games leverage multi-threading techniques to enhance network security. Here are a few notable examples:
Counter-Strike: Global Offensive
In Counter-Strike: Global Offensive, a separate thread is dedicated to network communication, reducing latency and improving responsiveness. By utilizing multi-threading, the game ensures smooth and seamless online gameplay, enhancing network security.
World of Warcraft
World of Warcraft, with its massive player base, utilizes multiple threads for network communication to handle high volumes of data. The implementation of multi-threading in the game enhances throughput, scalability, and network security, providing a smooth gaming experience for millions of players.
Fortnite
Fortnite employs a separate thread for network encryption, bolstering security and reliability. By dedicating a thread to this critical aspect of network communication, Fortnite enhances network security, protecting player data and ensuring a secure gaming environment.
These examples highlight the effectiveness of multi-threading in improving network security performance in the gaming industry.

The Science Behind Multi-Threading in Packet Analysis
Packet analysis systems traditionally employ sequential processing, analyzing packets one at a time. However, for large-scale networks, this can become a bottleneck. Multi-threading overcomes this limitation by allowing concurrent execution of packet capture, processing, and analysis tasks, utilizing CPU or GPU resources more efficiently. By parallelizing these tasks, multi-threaded systems achieve higher throughput and responsiveness, enabling real-time threat detection in high-traffic network environments.
When it comes to packet analysis, real-time processing is essential for effective network security. By leveraging multi-threading, packet analysis systems can process multiple packets simultaneously, reducing latency and improving overall system performance. This approach ensures that critical network events are detected and analyzed in real-time, allowing for more proactive and timely security measures.
The power of multi-threading lies in its ability to make optimal use of available CPU and GPU resources. By dividing the workload into multiple threads, each assigned to an individual core or processor, multi-threaded systems can efficiently distribute the processing load and achieve faster packet analysis. This results in higher throughput, enabling the system to handle larger amounts of network traffic with minimal impact on responsiveness.
“Multi-threading in packet analysis allows for concurrent execution of packet capture, processing, and analysis, enhancing system throughput and responsiveness.”
The responsiveness of a packet analysis system is crucial for real-time threat detection. Multi-threading enables faster processing of network packets, allowing the system to respond quickly to potential security threats. By analyzing packets in parallel, multi-threaded systems can achieve near-instantaneous threat detection, ensuring the prompt identification and mitigation of any malicious activity.
Overall, multi-threading revolutionizes packet analysis by enabling real-time processing, improving CPU and GPU utilization, and enhancing system throughput and responsiveness. This technology plays a key role in modern network security, allowing for proactive threat detection and mitigation in high-traffic environments.
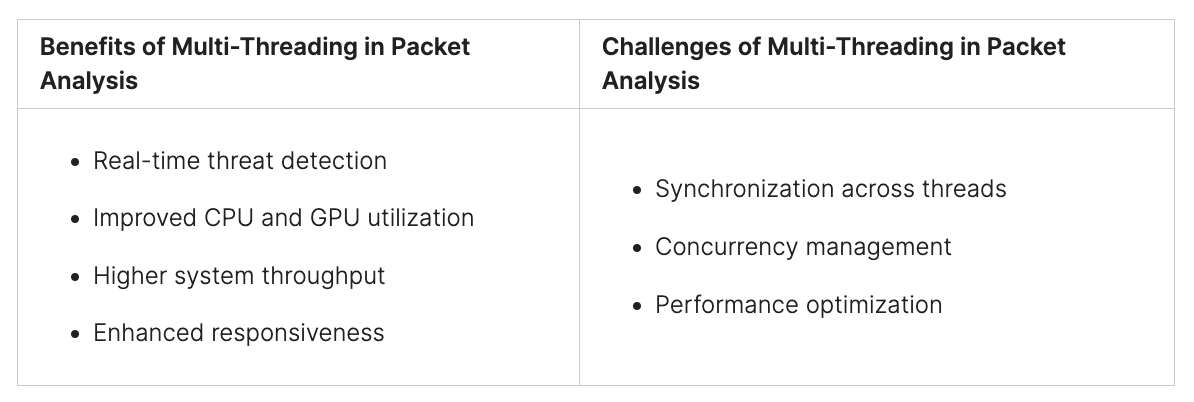
Implementing Multi-Threading in Packet Analysis
Implementing multi-threading in packet analysis allows for leveraging concurrent execution of tasks, resulting in enhanced throughput and responsiveness. By optimizing system performance through parallelizing packet capture, processing, and analysis, network security systems can achieve higher efficiency and real-time threat detection capabilities.
Code snippets can be helpful in illustrating the implementation details of multi-threaded packet capture techniques. These snippets provide a visual representation of how threads can be utilized to perform simultaneous packet analysis, improving the overall performance of network security systems.
The rationale behind implementing multi-threading in packet analysis is to maximize throughput and responsiveness. By distributing the computational load among multiple threads, the system can process packets concurrently, increasing the speed at which they are analyzed and reducing packet analysis time.
The implementation of multi-threading in packet analysis is crucial for optimizing system performance and achieving real-time threat detection capabilities. By leveraging concurrent execution, network security systems can enhance their throughput, responsiveness, and overall cybersecurity performance.
By adopting multi-threading in packet analysis, network security systems can significantly improve their ability to detect and mitigate threats efficiently. The concurrent execution of packet analysis tasks enables better utilization of system resources, resulting in enhanced throughput and real-time responsiveness.
Benefits of Implementing Multi-Threading in Packet Analysis
- Improved throughput: Multi-threading allows for parallel processing of packet analysis tasks, enabling the system to handle a higher volume of packets, thereby increasing overall throughput.
- Enhanced responsiveness: Concurrent execution of packet analysis tasks reduces the time taken to analyze packets, providing real-time responsiveness in detecting and responding to potential threats.
- Optimized resource utilization: Multi-threading optimizes the use of system resources by distributing the computational load across multiple threads, ensuring efficient utilization of CPU and GPU resources.
Implementing multi-threading in packet analysis involves careful consideration of thread synchronization, load balancing, and data sharing among threads. Through proper design and coding practices, network security systems can leverage multi-threading to achieve higher levels of throughput, responsiveness, and overall cybersecurity performance.
Conclusion
Multi-threading stands as a pivotal innovation in network security, fundamentally transforming how efficiency and response times are approached in this field. By harnessing the power of parallel processing and optimized resource allocation, multi-threading facilitates real-time analysis of network traffic, efficient intrusion detection, and the execution of advanced networking tasks. This technological leap significantly boosts the speed and efficacy of network security systems, marking a new era in cybersecurity performance.
For network security professionals, the adoption of best practices in multi-threading is vital for harnessing its full potential. Key focus areas include effective synchronization, adept concurrency management, and strategic performance optimization. Through meticulous design and implementation of multi-threaded systems, professionals in this field can markedly enhance operational efficiency, responsiveness, and overall cybersecurity effectiveness.
In essence, multi-threading serves as an invaluable asset in the realm of network security, offering the capability for concurrent task execution and efficient resource utilization, leading to expedited threat detection and bolstered network defenses. By adopting multi-threading and skillfully navigating its complexities, organizations are well-positioned to elevate their cybersecurity capabilities, ensuring a more secure and proficient network infrastructure.
To delve deeper into the world of multi-threading and discover how it can revolutionize your organization’s network security, visit Peris.ai Cybersecurity. Explore our range of solutions and learn how our expertise in multi-threading can enhance your cybersecurity strategy, providing you with a more secure, responsive, and efficient network system.
FAQ
What is multi-threading and how does it relate to network security?
Multi-threading is a technique that allows a program to execute multiple tasks simultaneously on different cores or processors. In the context of network security, multi-threading enhances efficiency and response time, improving the overall cybersecurity performance.
What are the benefits of multi-threading in network security?
Multi-threading reduces network latency, increases throughput and scalability, enhances security and reliability of network connections, and protects against malicious attacks.
What challenges does multi-threading present in network security?
Synchronization, concurrency, and performance optimization are key challenges in implementing multi-threading in network security.
What solutions can address the challenges of multi-threading in network security?
Best practices include using message queues or buffers, employing locks and mutexes, implementing state machines and protocols, using timeouts and retry mechanisms, and utilizing profilers and debuggers.
How can multi-threading be implemented in network security?
The implementation of multi-threading depends on the chosen game engine or framework, which provide tools, libraries, APIs, and interfaces for creating and managing threads and handling network communication.
Can you provide examples of multi-threading in network security?
Examples include Counter-Strike: Global Offensive, World of Warcraft, and Fortnite, which use separate threads for network communication, throughput, scalability, and encryption.
How does multi-threading enhance packet analysis in network security?
Multi-threading allows for concurrent execution of packet capture, processing, and analysis tasks, enabling real-time threat detection, improving CPU and GPU resource utilization, and achieving higher throughput and responsiveness.
What is involved in implementing multi-threading in packet analysis?
Implementing multi-threading in packet analysis involves leveraging concurrent execution of tasks, using code snippets, parallelizing packet capture, processing, and analysis, and optimizing system performance.
In conclusion, what is the impact of multi-threading in network security?
Multi-threading enhances efficiency and response time in network security, leading to improved cybersecurity performance.