In today’s digital age, IT security and penetration testing are critical for organizations of all shapes and sizes. The growing risk of cyber threats means that a robust IT security system is more important than ever.
However, procuring the right penetration testing service provider for your business can be challenging. That’s why we’ve created this comprehensive guide for IT security teams in penetration testing procurement. Our guide will take you through the entire process, from understanding IT security and penetration testing to managing the engagement and leveraging results.
Key Takeaways:
- IT security and penetration testing are crucial for organizations to safeguard systems in today’s digital age.
- Procuring the right penetration testing service provider can be challenging, but it’s essential for effective IT security.
- This comprehensive guide will take you through the entire penetration testing procurement process, from assessment to ongoing monitoring and improvement.
- By following the best practices outlined in our guide, IT security teams can optimize the procurement process to ensure maximum effectiveness.
- Our guide provides actionable insights organizations can use to enhance their security posture.
1. Understanding IT Security and Penetration Testing
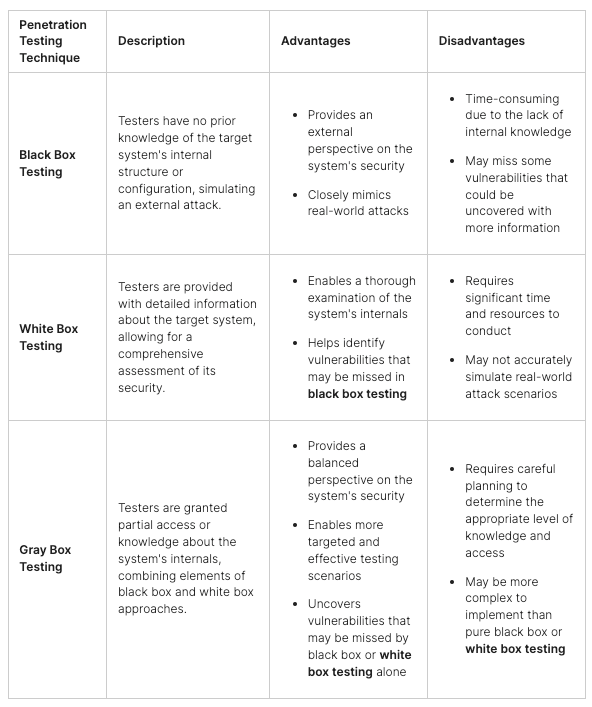
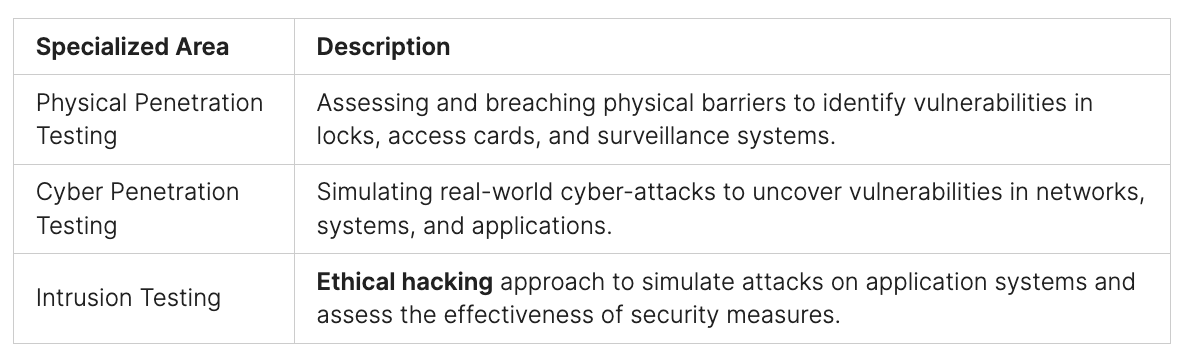
IT security and penetration testing are essential components of any organization’s security strategy. IT security involves protecting an organization’s information, data, and systems from unauthorized access, theft, or damage. Penetration testing, on the other hand, is a simulated attack on an organization’s systems to identify potential vulnerabilities that attackers could exploit.
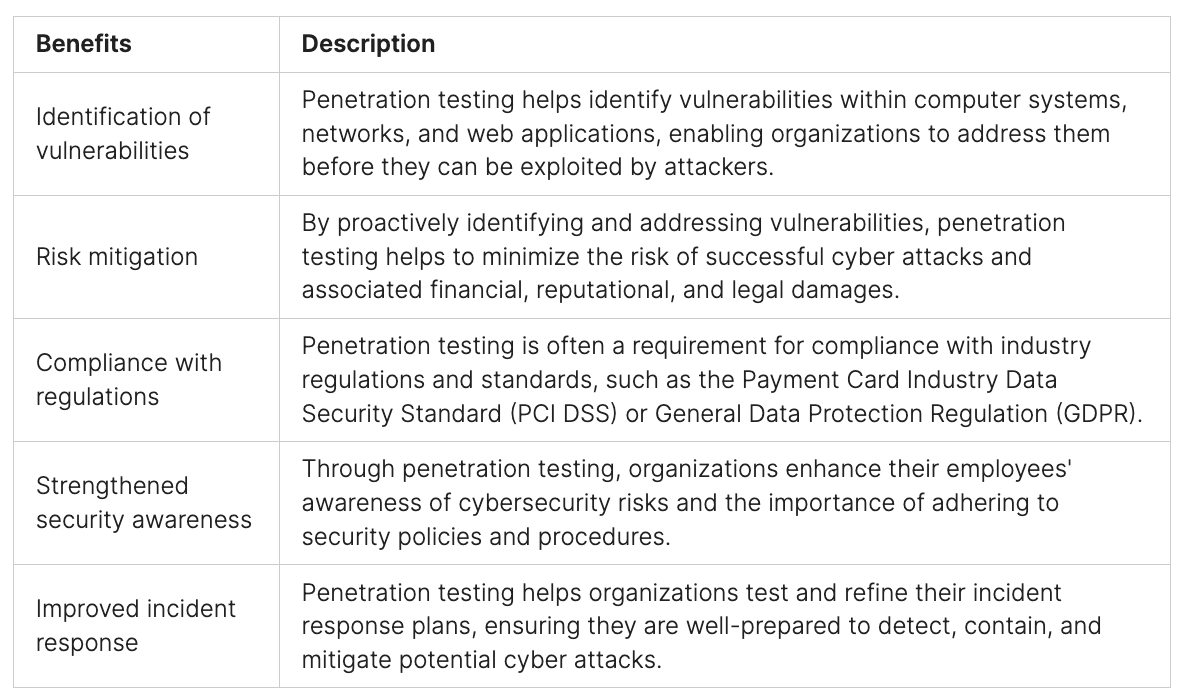
Effective IT security requires a comprehensive approach that includes preventive measures, such as firewalls, encryption, and access controls, and proactive activities, such as vulnerability scanning and penetration testing. Penetration testing helps identify vulnerabilities that may have been missed during the initial security assessment and provides an opportunity to validate the effectiveness of existing security controls.
Penetration testing can be conducted externally, simulating an attack from outside the organization, or internally, simulating an attack from within. Both methods are essential to ensure that an organization’s network and data are fully protected from cyber threats.
IT security teams must understand the importance of penetration testing and its role in identifying and mitigating cybersecurity risks. They are responsible for overseeing the testing process, ensuring that it is conducted in a controlled and safe manner, and working with penetration testing providers to address any vulnerabilities that are identified. By conducting regular penetration testing, organizations can reduce the risk of a cyber-attack and protect their sensitive information from theft or damage.
2. The Role of IT Security Teams in Procuring Penetration Testing Services
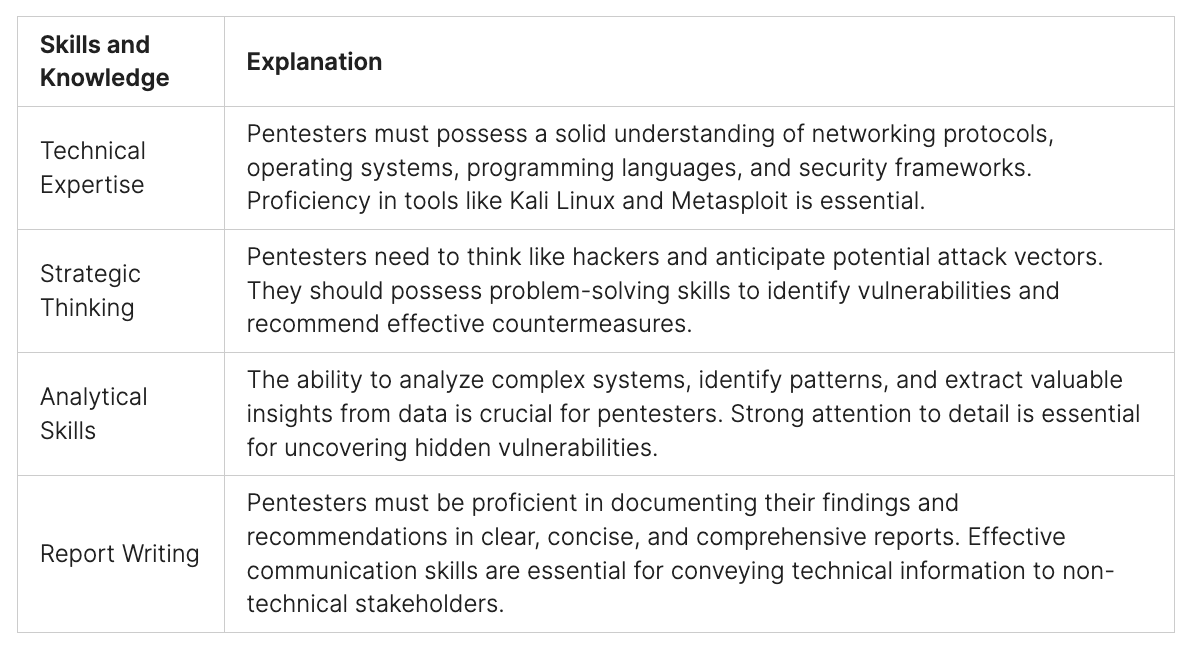
IT security teams are critical stakeholders in the procurement process of penetration testing services. Their involvement and expertise can ensure that the right testing methodology is selected, adequate scope of testing is defined, and the engagement results are thoroughly evaluated and utilized to improve the organization’s security posture.
IT security teams should participate in all phases of the procurement process in partnership with the procurement team. During the scoping phase, IT security teams should work closely with business and technical stakeholders to understand the systems, applications, and data that need to be tested. They should ensure that all stakeholders understand the goals of the engagement, the testing methodology, and the expected deliverables.
During the vendor evaluation phase, IT security teams should use their expertise to identify and vet potential penetration testing providers. They should consider the vendor’s experience, certifications, references, and reputation in the industry. They should also ensure that the vendor has the expertise and experience to test the systems, applications, and data in scope.
During the proposal evaluation phase, IT security teams should evaluate the vendor proposals against the project goals, scope, and expected deliverables. They should ensure that the proposal includes a detailed methodology, testing approach, and scope of testing. They should also ensure that the pricing is reasonable and competitive.
Finally, during the engagement phase, IT security teams should closely manage the vendor to ensure that the testing is performed according to the project goals, scope, and methodology. They should ensure that the vendor has access to the systems, applications, and data in scope and performs testing securely and non-disruptively.
3. Assessing the Organization’s Security Needs
Before procuring penetration testing services, assessing an organization’s security needs is critical. This involves identifying potential vulnerabilities, understanding the scope of testing required, and aligning it with business objectives. An IT security team plays a crucial role in this process, leveraging their expertise to determine the appropriate testing approach.
The first step is conducting a comprehensive security assessment, identifying potential weaknesses in the organization’s systems. This can include assessing network security, system configuration, user access controls, and data encryption protocols. The IT security team can then prioritize the identified vulnerabilities based on their severity and likelihood of exploitation.
Once vulnerabilities have been identified, the IT security team can determine the testing scope required to address them adequately. This can include determining the systems or applications to be tested, the level of detail required, and the testing methodology to be used. The team should also take into account any compliance requirements the organization may be subject to.
The scope of testing should be aligned with the organization’s business objectives, ensuring that the testing helps achieve the desired outcomes. This can involve evaluating the impact of potential security breaches on the business and identifying critical systems that require additional testing. The IT security team should also consider the organization’s risk appetite and tolerance when determining the appropriate level of testing.
Assessing an organization’s security needs is a critical step in the penetration testing procurement process. By identifying potential vulnerabilities, determining the scope of testing required, and aligning it with business objectives, IT security teams can ensure that their organization is adequately protected from security threats.
4. Identifying Suitable Penetration Testing Providers
Once an organization has assessed its security needs, the next step is to identify suitable penetration testing providers. The IT procurement team should be involved in this process to ensure that the provider selected aligns with the organization’s IT procurement policies and procedures. Factors to consider include:
- Experience and expertise in the type of testing required
- Certifications and accreditations, such as ISO 27001
- Reputation, including reviews from other organizations and references
- Availability and flexibility to accommodate the organization’s schedule and requirements
- Cost and pricing model
It is important to take the time to research and evaluate potential providers thoroughly. Seeking recommendations from other industry colleagues or security experts can be helpful in identifying reliable and effective penetration testing providers.
5. Evaluating Penetration Testing Proposals
Once the IT security team has identified potential penetration testing providers, the next step is to evaluate the proposals received from these providers. This evaluation process is critical to ensure that the selected provider aligns with the organization’s requirements and that the engagement delivers the desired outcomes.
When evaluating proposals, several key criteria must be considered. One of these is the provider’s methodology. The methodology should be well-defined, structured, and aligned with industry best practices. The methodology must also include appropriate tools and techniques to identify vulnerabilities and mitigate risks.
Tip: Ensure to check whether the provider has experience in assessing the specific systems and applications that require testing. They should also be skilled in handling the testing of cloud environments.
The scope coverage is another critical factor to consider. The proposal should outline precisely what systems, software, and networks the engagement covers. This includes the types of vulnerabilities to be targeted and the depth of testing required.
Tip: Ensure that the scope of work is well defined and includes all systems, applications, and networks that are critical to the organization’s operations.
Finally, pricing is also a critical consideration. Providers should provide clear and transparent pricing information for the proposed engagement. This should be aligned with the scope of work and the requirements identified during the initial scoping process.
Tip: Consider whether pricing is competitive for the services offered. Ensure to consider the cost of any supplementary services, such as retesting, that may be required post-engagement.
Evaluating proposals requires significant expertise and experience. Therefore, it is crucial that IT security teams involve appropriate stakeholders, including management and procurement professionals, in the decision-making process.
Conclusion:
Evaluating penetration testing proposals is a crucial aspect of the procurement process. IT security teams must ensure that they evaluate provider methodologies, scope coverage, and pricing in detail before making a decision. By conducting a thorough evaluation, teams can select a provider that aligns with their organization’s requirements and delivers an effective engagement.
6. The Role of IT Security Teams in Procuring Penetration Testing Services
Procuring penetration testing services requires a thorough understanding of the organization’s IT security needs and the expertise to evaluate potential providers. IT security teams play a critical role in this process, ensuring that the penetration testing engagement is aligned with business objectives and effectively addresses potential vulnerabilities.
To successfully navigate contract negotiations for penetration testing procurement, IT security teams should prioritize establishing clear expectations and defining essential terms. This includes outlining the scope of testing, delivery timelines, and pricing considerations, among others.
During the negotiation process, IT security teams should also focus on assessing and mitigating any potential legal or financial risks. This includes identifying areas of potential liability and ensuring that the provider has adequate insurance coverage.
By engaging effectively with potential providers and negotiating favorable terms, IT security teams can ensure that the procurement process meets the organization’s needs and aligns with its IT security priorities.
7. Managing the Penetration Testing Engagement
Once a suitable provider has been selected and a contract has been negotiated and signed, it is essential to manage the penetration testing engagement effectively. This involves ensuring that the testing objectives are achieved, communication is maintained between the IT security and penetration testing teams, and any challenges that arise during the engagement are addressed.
A key factor in the engagement’s success is clearly understanding the scope and methodology of the testing. The IT security team should work closely with the penetration testing team to ensure that the scope covers all critical assets and vulnerabilities and that the methodology is thorough and effective.
Regular communication between the IT security and penetration testing teams is also crucial throughout the engagement. This includes providing updates on the progress of testing, sharing findings and recommendations, and addressing any questions or concerns that may arise.
It is important to establish clear lines of communication and set expectations for the frequency and content of updates from the penetration testing team. Additionally, it is beneficial to designate a point person from the IT security team to serve as the primary contact for the penetration testing team.
Should any challenges arise during the engagement, it is important to address them promptly and effectively. This may involve reassessing the scope of testing, adjusting the methodology, or working collaboratively to address technical issues.
By effectively managing the penetration testing engagement, IT security teams can ensure that the testing objectives are met, vulnerabilities are identified and addressed, and the organization’s overall security posture is strengthened.
Penetration testing teams can help facilitate the management of the engagement by providing clear and concise updates, being responsive to questions and concerns, and collaborating with the IT security team to address challenges and ensure a successful engagement.
8. Leveraging Penetration Testing Results
After conducting a comprehensive penetration testing exercise, IT security teams must leverage the results to enhance their organization’s overall security posture.
The first step in leveraging the penetration testing results is to carefully analyze the findings and identify any vulnerabilities that were discovered. These vulnerabilities must be prioritized based on their potential impact on the organization’s operations and their likelihood of exploitation by attackers.
Once the vulnerabilities have been identified and prioritized, IT security teams must plan and implement remediation measures to address them. This may include patching systems, updating software, and improving security configurations.
Documenting the remediation measures taken and monitoring their effectiveness is also important. Regular testing should be conducted to confirm that the vulnerabilities have been successfully mitigated.
In addition to remediation, IT security teams can leverage the results of the penetration testing exercise to identify areas for improvement in their overall security posture. For example, if the testing reveals weaknesses in access controls, the team may implement stronger authentication mechanisms or more granular access policies.
Overall, the results of a penetration testing exercise can provide valuable insights into an organization’s security posture. By leveraging these insights and taking appropriate actions, IT security teams can strengthen their organization’s defenses against cyber threats.
9. Monitoring and Continuous Improvement
IT security and penetration testing procurement are crucial for any organization hoping to maintain an effective security posture. However, it doesn’t end there. Continuous monitoring and improvement are essential components of any robust security strategy.
Penetration testing provides valuable insights into an organization’s security vulnerabilities, but these need to be acted upon. IT security teams must take action based on the findings and recommendations to enhance their organization’s security measures.
This process includes ongoing monitoring of potential security threats and reassessing existing security measures. Regular penetration testing should also be conducted to ensure the measures remain effective and up-to-date.
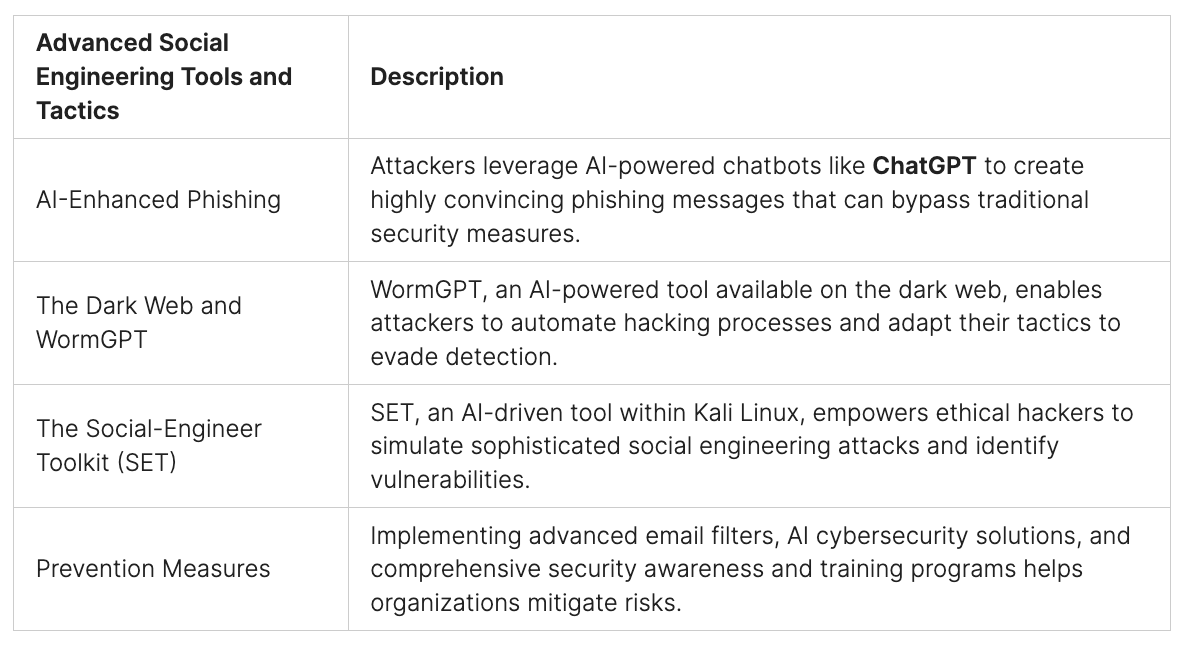
Staying updated on emerging threats is critical, as cyberattacks are continually evolving. IT security teams must remain vigilant and adapt their measures accordingly to protect their organization against these threats effectively.
- Regularly reassess security measures.
- Stay updated on emerging threats.
- Conduct regular penetration testing.
- Respond to findings and recommendations.
Organizations can stay ahead of potential threats by adopting a proactive approach to IT security and maintain a robust security posture. Continuous improvement is essential to ensure they are well-prepared for any security breaches, and penetration testing plays a crucial role in achieving this goal.
10. Best Practices in Penetration Testing Procurement
Effective IT security management involves thorough and considered procurement practices for penetration testing services. Here are some key best practices to aid in the process:
- Understand your organization’s security needs. Conduct a thorough assessment of potential vulnerabilities and align penetration testing scope with business objectives.
- Involve IT security teams in every step of the procurement process. IT security teams bring essential expertise to the table and should actively identify providers, evaluate proposals, and negotiate contracts.
- Consider provider experience, certifications, and reputation. These factors can help determine the provider’s capabilities and reliability in delivering quality penetration testing services.
- Evaluate proposals based on methodology, scope coverage, and pricing. Ensure the provider’s approach aligns with organization needs and budget.
- Negotiate contracts effectively. Pay attention to essential terms such as confidentiality, liability, deliverables, and the provider’s obligations and warranties.
- Manage the engagement effectively. Streamline communication between the IT security team and the provider, ensure testing objectives are met, and address any issues that arise promptly.
- Utilize penetration testing results to enhance overall security posture. Take action based on findings and recommendations to strengthen system security effectively.
- Stay updated on emerging threats and reassess security measures regularly. Regular penetration testing and implementing security measures that align with industry standards can help continuously enhance an organization’s security posture.
By following these best practices, IT security teams can ensure the procurement process for penetration testing services is optimized, effective, and aligned with the organization’s overall security objectives.
Conclusion
In summary, the significance of IT security and penetration testing procurement cannot be overstated as fundamental elements of an organization’s overarching security strategy. Understanding the pivotal role of IT security teams in the procurement process, assessing security requisites, selecting suitable providers, and proficient management of the engagement all collectively empower organizations to fortify their security defenses and minimize potential vulnerabilities.
The outcomes of penetration testing offer invaluable insights, enabling IT security teams to pinpoint vulnerabilities and take prompt corrective actions. Sustained vigilance and a commitment to ongoing enhancements are indispensable in upholding a robust security stance.
Best Practices in Penetration Testing Procurement To optimize the penetration testing procurement process, adhering to best practices is imperative:
- Involve IT security teams at every stage of procurement.
- Clearly articulate the testing objectives and scope.
- Evaluate potential providers based on their experience, certifications, and reputation.
- Thoroughly assess received proposals.
- Negotiate contracts that unambiguously delineate responsibilities, deliverables, and liability.
- Efficiently manage the engagement to ensure objectives are met, and challenges are addressed.
- Harness the results of penetration testing to elevate overall security defenses.
- Continuously monitor and refine security measures.
By steadfastly adhering to these best practices, organizations can streamline their penetration testing procurement process, guaranteeing the acquisition of the most effective testing services.
In essence, IT security and penetration testing procurement serve as the cornerstones for an organization’s safety and security. By following the guidelines presented in this guide and embracing best practices, IT security teams can fortify their organization’s security posture, thereby reducing potential risks. Take action now to safeguard your digital assets and gain the upper hand in the realm of cybersecurity. Visit our website to explore Perisai Pandava – Pentest & Assessment services and rest easy, knowing that your business is shielded from potential threats. Sleep soundly, for your data is in secure hands.
FAQ
What is IT security?
IT security protects information and systems from unauthorized access, use, disclosure, disruption, modification, or destruction. It aims to ensure data and technology resources’ confidentiality, integrity, and availability.
What is penetration testing?
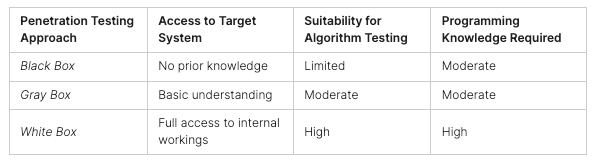
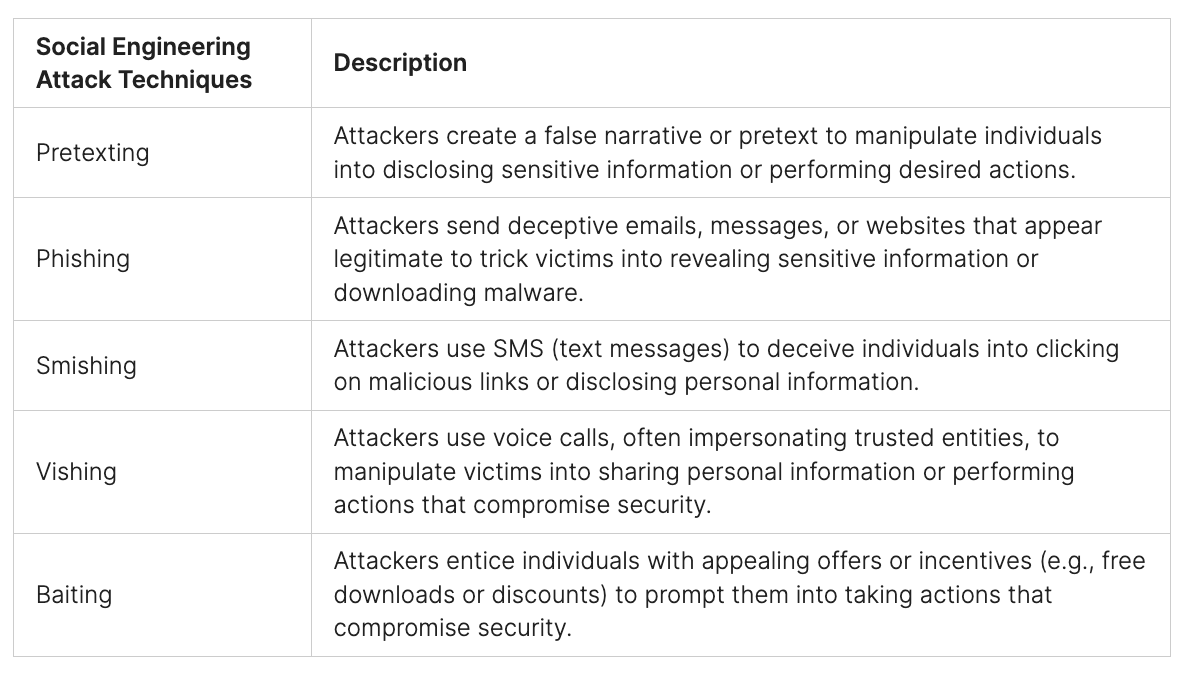
Penetration testing, also known as ethical hacking or white-hat hacking, is a method of assessing the security of a computer system, network, or application by simulating real-world attacks. It involves identifying vulnerabilities and weaknesses to help organizations strengthen their defenses.
Why is IT security and penetration testing important for organizations?
IT security and penetration testing are crucial for organizations to safeguard their sensitive information, protect against data breaches, and maintain the trust of their customers. They help identify vulnerabilities before malicious actors can exploit them and ensure that appropriate security measures are in place.
What is the role of IT security teams in procuring penetration testing services?
IT security teams play a vital role in the procurement process for penetration testing services. They are responsible for assessing the organization’s security needs, identifying suitable providers, evaluating proposals, negotiating contracts, managing the engagement, and leveraging the results to enhance security.
How can organizations assess their security needs?
Assessing an organization’s security needs involves identifying potential vulnerabilities, understanding the scope of testing required, and aligning it with business objectives. This can be done through risk assessments, vulnerability scans, and consultations with IT security experts.
How can IT security teams identify suitable penetration testing providers?
IT security teams can identify suitable penetration testing providers by considering factors such as experience, certifications, reputation, expertise in specific industry sectors, methodologies used, and the ability to meet the organization’s unique requirements.
What should be evaluated when reviewing penetration testing proposals?
When reviewing penetration testing proposals, key criteria to consider include the provider’s methodology, scope coverage, deliverables, pricing, turnaround time, reporting format, and the level of support and collaboration offered during and after the engagement.
What should be considered during contract negotiations for penetration testing?
During contract negotiations, essential terms to consider include confidentiality agreements, liability provisions, intellectual property rights, dispute resolution mechanisms, compliance with legal and regulatory requirements, and the specific objectives and deliverables of the engagement.
How can IT security teams effectively manage the penetration testing engagement?
IT security teams can effectively manage the penetration testing engagement by establishing clear communication channels, setting realistic objectives, providing necessary documentation and access, monitoring progress, addressing any challenges promptly, and ensuring that findings and recommendations are acted upon.
How can organizations leverage the results of penetration testing?
Organizations can leverage penetration testing results by using the findings and recommendations to enhance their overall security posture. This may involve implementing remediation measures, conducting additional testing in specific areas, and raising awareness among employees about potential vulnerabilities.
Why is continuous monitoring and improvement important in IT security?
Continuous monitoring and improvement in IT security are essential because the threat landscape is constantly evolving. Regular monitoring helps detect and respond to emerging threats, reassess security measures, and validate the effectiveness of existing controls. Penetration testing should be conducted regularly to ensure ongoing security readiness.
What are the best practices for penetration testing procurement?
Some best practices for penetration testing procurement include defining clear objectives and expectations, conducting thorough research on potential providers, involving IT security teams throughout the process, evaluating proposals based on technical capabilities and alignment with business needs, and establishing robust communication and reporting mechanisms.