As businesses increasingly rely on technology to operate, ensuring cybersecurity has become a critical concern. However, managing security infrastructure can be complex, costly, and time-consuming, especially for small and medium-sized businesses.
Fortunately, Security as a Service (SecaaS) offers a solution that can help businesses protect their digital assets without the hassle and expense of maintaining their security infrastructure in-house. SecaaS provides a range of benefits, including cost-effectiveness, enhanced data protection, and proactive threat monitoring.
This article explores the advantages of implementing Security as a Service (SecaaS) and managed security services, including cloud-based security services. We’ll examine the different types of SecaaS solutions, how they can benefit businesses, and the cost savings compared to traditional security solutions. We’ll also delve into the advanced security measures and technologies utilized in SecaaS solutions and how they can protect against potential threats.
Key Takeaways
- Security as a Service (SecaaS) can provide businesses with cost-effective and efficient security solutions.
- Cloud-based security services and outsourcing cybersecurity can offer significant advantages for businesses of all sizes.
- SecaaS solutions utilize advanced security measures and technologies to enhance data protection and provide proactive threat monitoring.
- Managed security services can offer expert guidance and support in maintaining a business’s security infrastructure.
- SecaaS solutions can enable businesses to secure their productivity and operate more efficiently.
Understanding Security as a Service (SecaaS)
Security as a Service (SecaaS) is a cloud-based security solution that provides businesses with advanced security measures and technologies without the need for expensive hardware or software. SecaaS solutions allow businesses to outsource cybersecurity and benefit from expert guidance and support while reducing costs.
Cloud-based security services are a popular form of SecaaS. These solutions utilize cloud computing for enhanced security measures, allowing businesses to store and protect sensitive data and applications in the cloud. By outsourcing cybersecurity to a trusted provider, businesses can free up resources to focus on core operations.
SecaaS Solutions
SecaaS solutions come in various forms, including:

By outsourcing cybersecurity to SecaaS providers, businesses can benefit from the latest security technologies and expertise without incurring high hardware and software maintenance costs.
Cybersecurity Outsourcing
Outsourcing cybersecurity through SecaaS solutions can provide significant benefits for businesses. By partnering with a trusted provider, businesses can benefit from:
- Expert guidance and support in maintaining their security infrastructure
- Access to the latest security technologies and solutions
- Enhanced security measures and protection against advanced threats
- Flexible and scalable security solutions that can adapt to changing needs
- Reduced costs compared to traditional security solutions
Overall, Security as a Service (SecaaS) offers businesses a cost-effective and efficient way to enhance their cybersecurity posture and protect against advanced threats.

Cost-Effectiveness of SecaaS
Implementing Security as a Service (SecaaS) can provide businesses with cost-effective security services that can help them save money in the long run. This is because SecaaS solutions eliminate the need for businesses to invest in expensive hardware and software, which can be both costly and time-consuming to maintain.
By outsourcing their cybersecurity needs to a trusted SecaaS provider, businesses can benefit from the latest security technologies without having to shoulder the high costs associated with them. Additionally, because SecaaS providers have the expertise and resources to monitor and manage a business’s security infrastructure continuously, there is less risk of security breaches or other related issues that can be costly to remediate.
Comparison of Costs

As shown in the comparison table above, implementing SecaaS solutions can provide businesses with significant cost savings when compared to traditional security solutions. This is particularly true for small to medium-sized businesses without the resources or budget to invest in expensive security infrastructure and personnel.
Furthermore, SecaaS providers typically offer flexible pricing models that allow businesses to scale their security services according to their needs and budgets. This means that businesses can enjoy the benefits of advanced security technologies without committing to long-term contracts or overpaying for services they don’t need.
In conclusion, implementing Security as a Service (SecaaS) can provide businesses with cost-effective security solutions that can help them save money while benefitting from advanced security measures and technologies. By outsourcing their cybersecurity needs, businesses can focus on their core competencies and leave the management of their security infrastructure to trusted experts.
Enhanced Data Protection with SecaaS
One of the most significant benefits of implementing Security as a Service (SecaaS) is the enhanced data protection it provides for businesses. SecaaS solutions utilize advanced security measures and technologies to safeguard sensitive information against potential cyberattacks.
With SecaaS, businesses can enjoy heightened protection against data breaches and other security threats. This is particularly important in today’s digital landscape, where cyberattacks are becoming increasingly common. In fact, according to a report by Accenture, the average cost of a data breach for companies worldwide is $3.86 million.
One way SecaaS enhances data protection is by providing continuous monitoring for potential threats. This means that any suspicious activity can be detected and addressed in real time, preventing any damage or serious consequences.
Moreover, SecaaS solutions offer encryption services that help protect data while in transit or at rest. This added layer of security ensures that even if data is accessed by unauthorized personnel, it remains undecipherable and unusable to them.
Example of SecaaS Data Protection
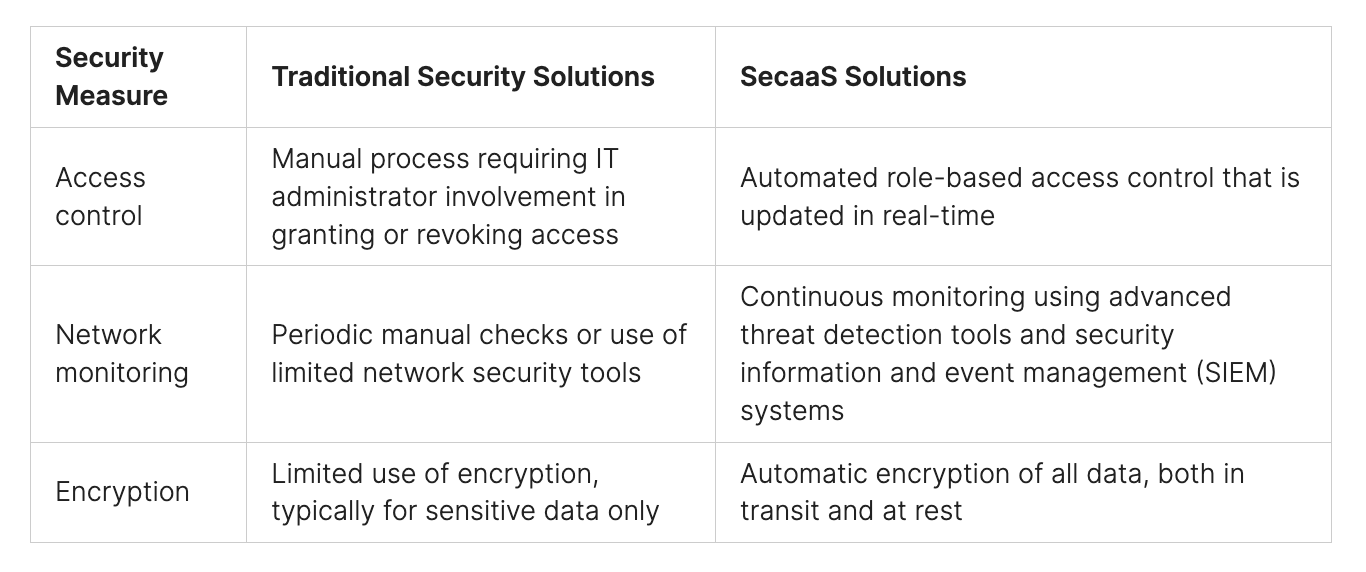
As illustrated in the table above, SecaaS solutions offer an array of advanced security measures that go beyond what traditional security solutions can provide. This translates to better data protection and a reduced risk of costly data breaches that can severely impact a business.
In addition, enhanced data protection can also improve a company’s reputation, as customers and partners are more likely to trust businesses that prioritize their data security.

Proactive Threat Monitoring
One of the key advantages of Security as a Service (SecaaS) is its proactive threat monitoring capabilities. With continuous monitoring, businesses can detect potential security threats in real time and take action before they cause any damage.
Proactive threat monitoring involves monitoring networks, systems, and applications for suspicious activity and identifying potential security breaches. This approach helps businesses stay ahead of threats and take appropriate action to mitigate risk.

By leveraging SecaaS solutions for proactive threat monitoring, businesses can benefit from improved incident response times and reduced risk of data breaches. Managed security services, cloud-based security services, and scalable security solutions are all examples of SecaaS solutions that provide proactive threat monitoring capabilities.
In addition to reducing the risk of security breaches, proactive threat monitoring can help businesses save money in the long run. Businesses can avoid costly security incidents by detecting and addressing potential threats before they cause any damage.
Overall, proactive threat monitoring is a key benefit of Security as a Service (SecaaS). By continuously monitoring for potential security threats, businesses can stay ahead of the curve and take appropriate action to mitigate risk, leading to increased security and peace of mind.

Scalable Security Solutions
One of the key benefits of implementing Security as a Service (SecaaS) is the scalability it provides. Unlike traditional security solutions, SecaaS offers businesses the flexibility to adjust their security measures based on their changing needs. This means that businesses can easily scale up or down their security measures as required without the need for costly hardware or software investments.
Scalability is particularly important for businesses that are growing rapidly or experiencing fluctuations in demand. With SecaaS, businesses can easily add or remove security measures as required, making it a cost-effective and efficient solution.
Another advantage of SecaaS is that it allows businesses to access advanced security technologies that may otherwise be prohibitively expensive. By leveraging cloud-based security services, for example, businesses can benefit from cutting-edge security measures without the need for significant investment.
Scalable Security Solutions in Action
To illustrate the benefits of scalable security solutions, consider the following example:

As this example illustrates, SecaaS provides businesses with a cost-effective and flexible solution for managing their security needs. By leveraging scalable security solutions, businesses can ensure that they have the right level of security measures in place to protect their data and systems without breaking the bank.

Managed Security Services
Implementing Security as a Service (SecaaS) solutions can be challenging for organizations with limited IT expertise. That’s where managed security services come in. Managed security services refer to outsourcing security measures to a third party specializing in IT security management. This third party can provide expert guidance and support in maintaining an organization’s security infrastructure.
Managed security services can be particularly beneficial for small- to medium-sized businesses. Often, these organizations do not have the resources to employ a dedicated IT security team. By outsourcing security measures to a managed security services provider, businesses can free up resources to focus on their core competencies. Additionally, managed security services provide a cost-effective alternative to hiring full-time employees with specialized security expertise.
Managed security services can include a wide variety of services, such as:

Managed security services can also be customized to meet an organization’s specific needs. By working with a managed security services provider, businesses can have peace of mind knowing that experts in the field are managing their security measures.

Outsourcing security measures to a managed security services provider as part of a SecaaS solution can provide numerous benefits for organizations. By leveraging managed security services, businesses can improve their security posture, free up resources, and ensure compliance with industry regulations and standards.
Cloud-Based Security Services
One of the key advantages of Security as a Service (SecaaS) is the availability of cloud-based security services. These services leverage cloud computing to deliver advanced security features and protect against a wide range of threats, from malware and viruses to insider attacks.
Cloud-based security services are designed to be flexible and scalable, making them ideal for businesses of all sizes. They can be quickly and easily deployed, with no need for expensive hardware or infrastructure investments. This makes them a cost-effective solution for businesses looking to enhance their security measures.

Overall, cloud-based security services are a crucial component of any SecaaS solution. They provide businesses with the flexibility, scalability, and cost-effectiveness they need to enhance their security measures and protect against a wide range of threats.

Securing Productivity with SecaaS
One of the key benefits of Security as a Service (SecaaS) is the ability to secure productivity within a business environment. By leveraging advanced security technologies and practices, businesses can ensure that their operations remain safe and efficient.
One way that SecaaS can enhance secure productivity is through the implementation of strict access controls. With the ability to restrict access to sensitive data and systems, businesses can prevent unauthorized access and protect against potential security threats. This enables employees to work confidently and efficiently, without fear of compromising the security of the organization.
In addition, SecaaS solutions can provide real-time threat detection and response capabilities. By continuously monitoring for potential security threats, businesses can address issues as soon as they arise, minimizing the impact on operations and reducing downtime. This enables employees to work without interruption, further enhancing productivity.

“By leveraging advanced security technologies and practices, businesses can ensure that their operations remain safe and efficient.”
Overall, the benefits of secure productivity with SecaaS are clear. By protecting against security threats and implementing effective access controls, businesses can operate more efficiently and with confidence.
Benefits of SecaaS for Businesses
Implementing Security as a Service (SecaaS) can provide numerous benefits for businesses seeking to enhance their security measures. The advantages of SecaaS solutions are numerous and effective, making it an ideal choice for businesses of all sizes. Here are some of the key benefits of implementing SecaaS solutions:
- Cost Savings: SecaaS solutions can provide significant cost savings compared to traditional security solutions. With SecaaS, businesses can avoid the high upfront costs of purchasing and maintaining their security infrastructure and instead pay a predictable monthly fee for managed security services.
- Enhanced Data Protection: SecaaS solutions incorporate advanced security measures and technologies that can significantly enhance data protection for businesses. This can include features such as encryption, multi-factor authentication, and real-time threat monitoring that can detect and address potential security threats before they become a problem.
- Proactive Threat Monitoring: SecaaS solutions continuously monitor and address potential security threats in real time. This enables businesses to proactively respond to security threats and prevent damage or data loss from occurring.
- Scalable Security Solutions: SecaaS solutions are designed to adjust easily and flexibly based on a business’s changing security needs. This means that businesses can scale their security measures up or down as needed without the need for additional hardware or infrastructure.
- Managed Security Services: Implementing managed security services as part of a SecaaS solution can provide businesses with expert guidance and support in maintaining their security infrastructure. This can include services such as 24/7 support, vulnerability assessments, and training to help businesses stay ahead of emerging security threats.
- Cloud-Based Security Services: SecaaS solutions often incorporate cloud-based security services, which can provide additional benefits such as increased agility, flexibility, and scalability. Cloud-based security services can also help businesses reduce their reliance on physical hardware and infrastructure, saving additional costs.
- Secure Productivity: SecaaS solutions can secure and enhance productivity within a business environment by protecting against security threats and enabling employees to work efficiently. This can include features such as secure remote access, data backup and recovery solutions, and anti-virus and anti-malware protection.

The benefits of implementing Security as a Service (SecaaS) are numerous and can significantly enhance a business’s security measures. From cost savings to enhanced data protection, SecaaS solutions can provide businesses with the peace of mind they need to focus on growth and innovation.
Conclusion
Safeguarding your business from the relentless onslaught of security threats is more crucial than ever. That’s where BIMA comes in, offering a comprehensive Cybersecurity-as-a-Service platform that operates 24/7, providing you with the ultimate cybersecurity solution. Don’t wait any longer to protect your digital world; start securing your business with BIMA today!
With BIMA, you can fortify your defenses against even the most advanced cyberattacks. Our array of cybersecurity tools and tailored monitoring solutions are designed to meet the unique requirements of your business. Powered by a combination of potent proprietary and open-source tools, along with access to the latest threat intelligence through our subscription-based scanners, BIMA ensures unparalleled security. And with our pay-as-you-go service, you’ll only pay for what you need, with no upfront costs or hidden fees.
Whether your business is a small startup or a large enterprise, BIMA has got you covered. Our user-friendly platform simplifies the process of monitoring and safeguarding your business from start to finish. With BIMA, you can take control of your cybersecurity and shield your business from any potential threat.
So why leave your digital world vulnerable? Take action today and visit our website, Peris.ai, to explore how BIMA can be the shield your business needs to stay secure in an ever-evolving digital landscape.
Protect your digital world with BIMA because security is paramount in the digital realm.
FAQ
What is Security as a Service (SecaaS)?
Security as a Service (SecaaS) is a cloud-based security solution where businesses outsource their security needs to a third-party provider. It offers a range of security services, including threat monitoring, data protection, and managed security services.
What are the benefits of SecaaS?
SecaaS provides several advantages for businesses, including cost-effectiveness, enhanced data protection, proactive threat monitoring, scalable security solutions, and access to managed security services. It can also secure productivity and provide expert guidance and support.
How does SecaaS enhance data protection?
SecaaS utilizes advanced security measures and technologies to enhance data protection. It employs encryption, access controls, and data loss prevention techniques to safeguard sensitive information from unauthorized access or breaches.
How does SecaaS enable proactive threat monitoring?
With SecaaS, continuous real-time monitoring is implemented to detect and address potential security threats. Advanced threat detection systems and security analytics are used to identify and respond to suspicious activities, ensuring proactive protection against cyber threats.
What do scalable security solutions mean in the context of SecaaS?
Scalable security solutions in SecaaS refer to the ability to easily adjust and adapt security measures to meet changing business needs. Businesses can scale their security infrastructure up or down based on their requirements without the need for significant investments in hardware or personnel.
What are managed security services in SecaaS?
Managed security services are an integral part of SecaaS solutions. They involve outsourcing security management and monitoring to a specialized provider who offers expertise and guidance in maintaining and optimizing a business’s security infrastructure.
How do cloud-based security services fit into the SecaaS framework?
Cloud-based security services are a type of SecaaS solution where security measures are delivered and managed through cloud computing technology. This approach offers numerous benefits, including scalability, flexibility, and the ability to leverage the cloud’s extensive computing resources for enhanced security.
How does SecaaS secure productivity?
SecaaS secures productivity by protecting against security threats that can disrupt or compromise business operations. It ensures that employees can work efficiently and confidently, knowing that their digital assets and communications are safeguarded from potential cyber risks.
What are the main benefits of SecaaS for businesses?
The main benefits of SecaaS for businesses include cost savings, enhanced data protection, proactive threat monitoring, scalability, access to managed security services, cloud-based security solutions, and increased productivity. SecaaS offers a comprehensive and efficient approach to securing an organization’s digital assets.









