In an age of AI-driven threats, zero-day exploits, and polymorphic malware, Mean Time to Detect (MTTD) is more than a metric—it’s a survival line. A fast MTTD doesn’t just minimize the scope of an incident; it determines whether an organization will stay operational, suffer a public breach, or even face regulatory fines.
Despite record investments in cybersecurity tools, organizations are still struggling with MTTD, often taking days or even weeks to detect the presence of an attacker. Why? Because detection today is no longer about more tools—it’s about smarter coordination, deeper context, and automation that works at analyst speed.
This article dives deep into the pain points organizations face around MTTD—and how Peris.ai, through its Agentic AI capabilities in Brahma Fusion and INDRA, slashes detection time from hours to minutes. You’ll explore real-world scenarios, automation strategies, and the future of AI-driven SOC operations without the hard sell—just relevance.
Understanding the True Cost of Delayed Detection
The Financial Impact
A 2024 IBM report pegged the average cost of a breach at $4.45 million. The longer a threat remains undetected, the higher the cost. Breaches detected within 200 days cost 33% more than those found earlier.
The Operational Fallout
- Extended dwell time leads to deeper system infiltration.
- Delayed detection allows attackers to laterally move, exfiltrate data, and set up persistent access.
- Post-breach forensics and cleanup become exponentially more complex.
Brand and Trust Damage
For heavily regulated industries—banking, healthcare, defense—even a single breach due to slow detection undermines years of trust, triggers public relations crises, and potentially stalls business expansion.
Why MTTD Is Still Stubbornly High
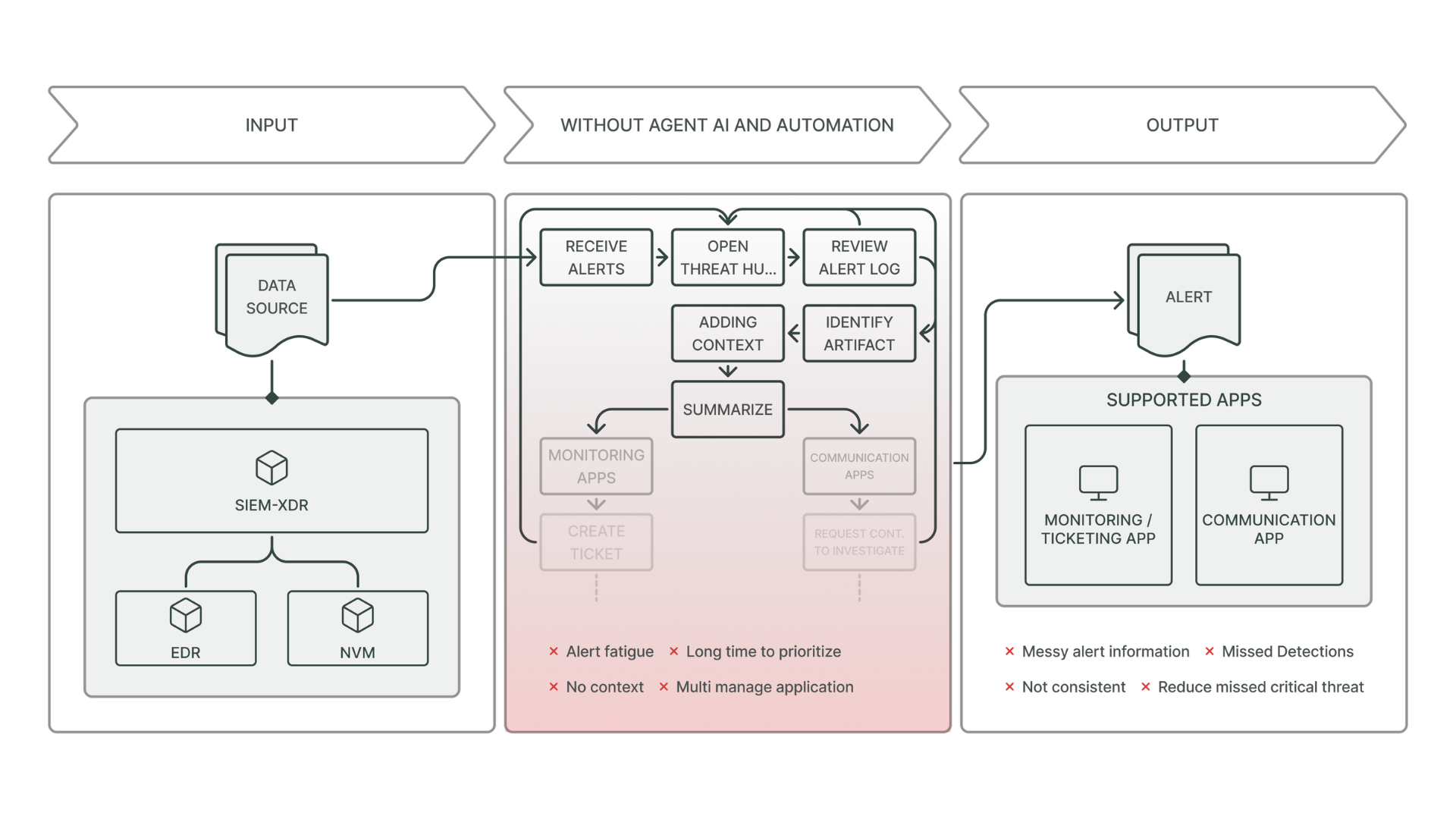
Despite widespread adoption of EDR, SIEM, XDR, and log aggregation platforms, organizations struggle to bring MTTD below several hours—and in many cases, days.
Here’s why:
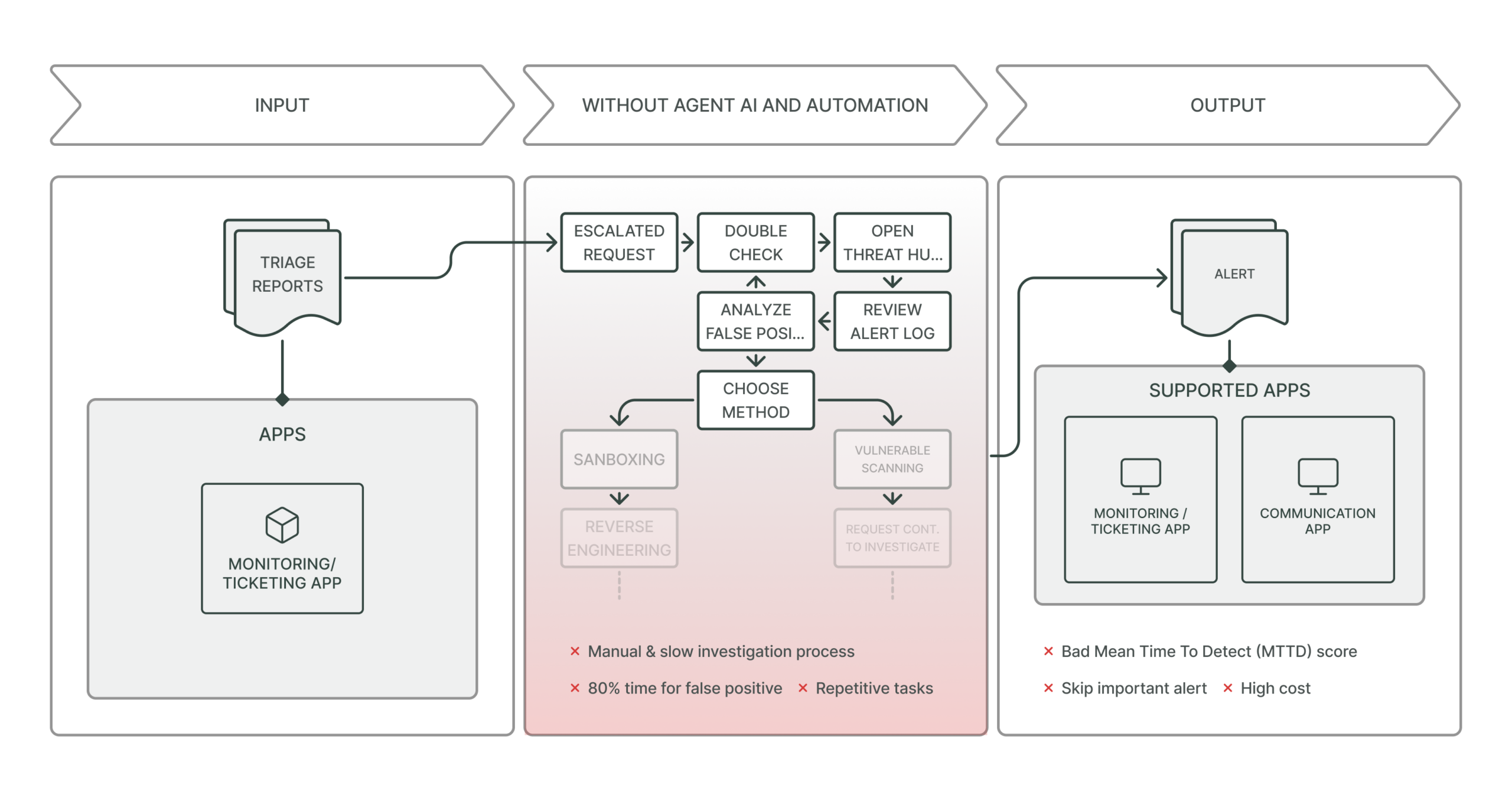
Alert Overload
SOC teams are inundated with thousands of alerts daily, 90% of which are false positives or non-actionable.
“Security analysts spend more time triaging noise than detecting real threats.”
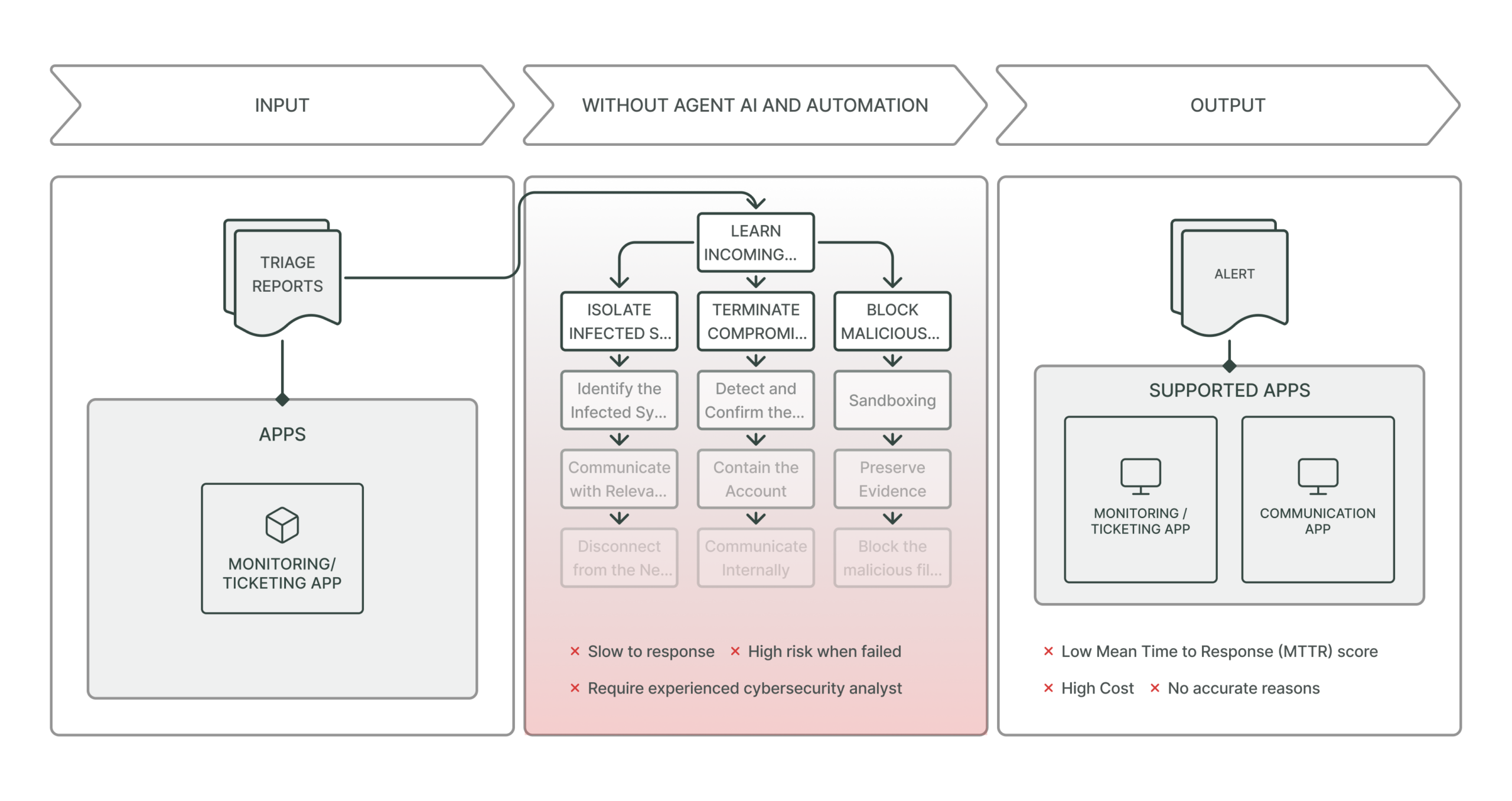
Disconnected Toolchains
Many security tools are siloed:
- One platform detects anomalies.
- Another ingests logs.
- A third sends out alerts.
- Yet none of them share context in real time.
This leads to slow correlation and response.
Context-Free Alerts
Without correlated threat intelligence or historical behavioral context, analysts can’t distinguish between a misconfigured script and an active breach—leading to paralysis or incorrect prioritization.
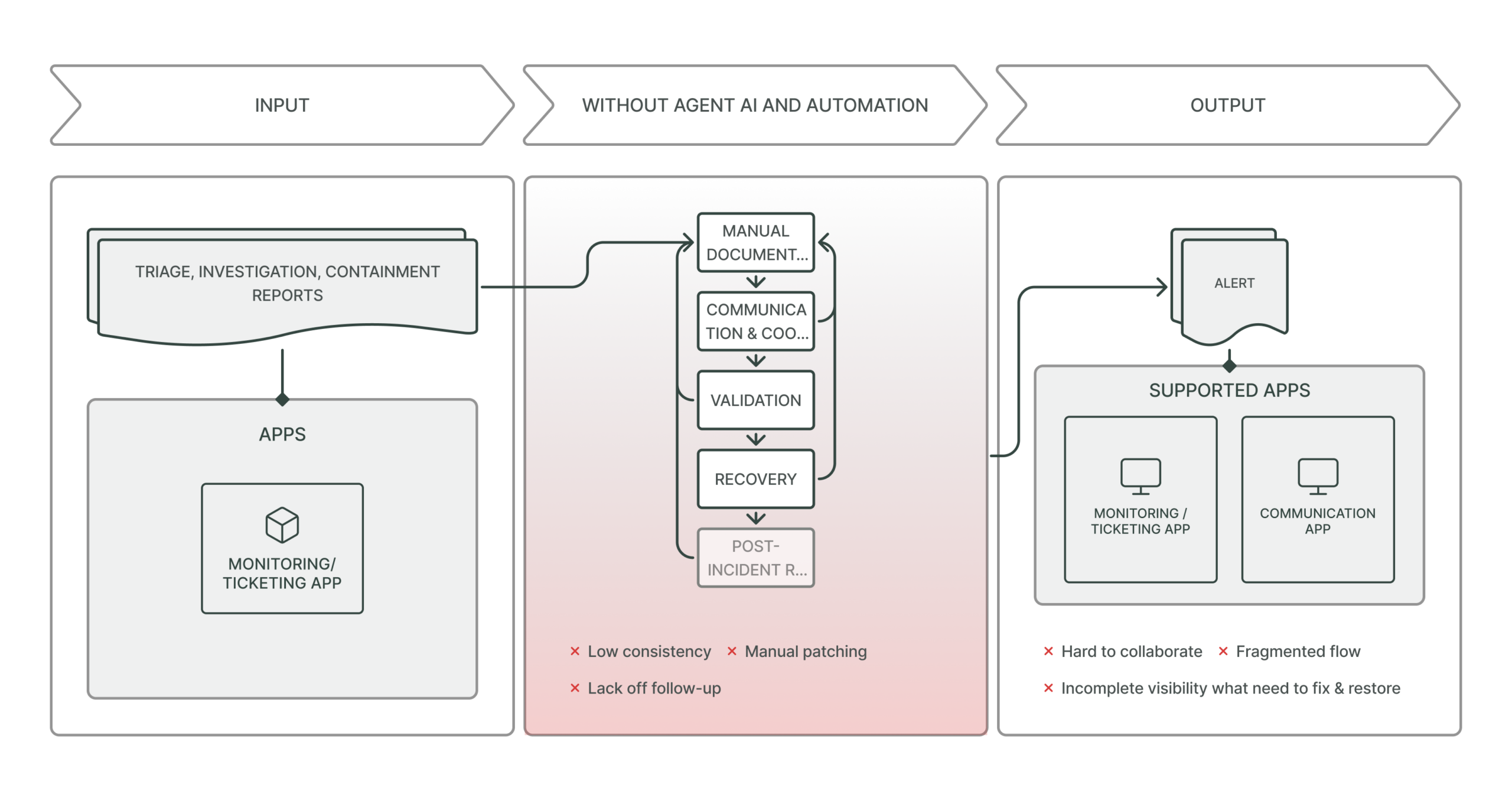
Manual Investigations
After initial alert triage, investigations often involve manual steps:
- Querying threat databases
- Pivoting across logs
- Checking asset ownership
- Mapping to MITRE ATT&CK
These delays compound MTTD and analyst fatigue.
The Analyst Burnout Spiral
SOC analyst roles are among the most stressful in tech:
- High stakes, low visibility
- Repetitive triage work
- Constant pressure to “not miss anything”
This leads to:
- Cognitive fatigue → Slower reaction time
- High turnover → Inconsistent skill levels
- Increased hiring costs → Diminished ROI
In many organizations, burnout becomes a root cause of extended MTTD.
What Organizations Actually Need to Improve MTTD
Improving MTTD is not about deploying more tools—it’s about integrating intelligence, automating grunt work, and enhancing analyst decision-making.
Here’s what’s required:
- Real-time correlation: Alerts must be enriched with contextual data instantly.
- Threat intelligence: Alerts should indicate whether the behavior matches active campaigns or known tactics.
- Automation: Playbooks must auto-handle repetitive triage tasks.
- Visibility: All security data (endpoint, network, identity) must be unified and searchable.
- Integration: Data pipelines must allow seamless flow between SIEM, CTI, and response platforms.
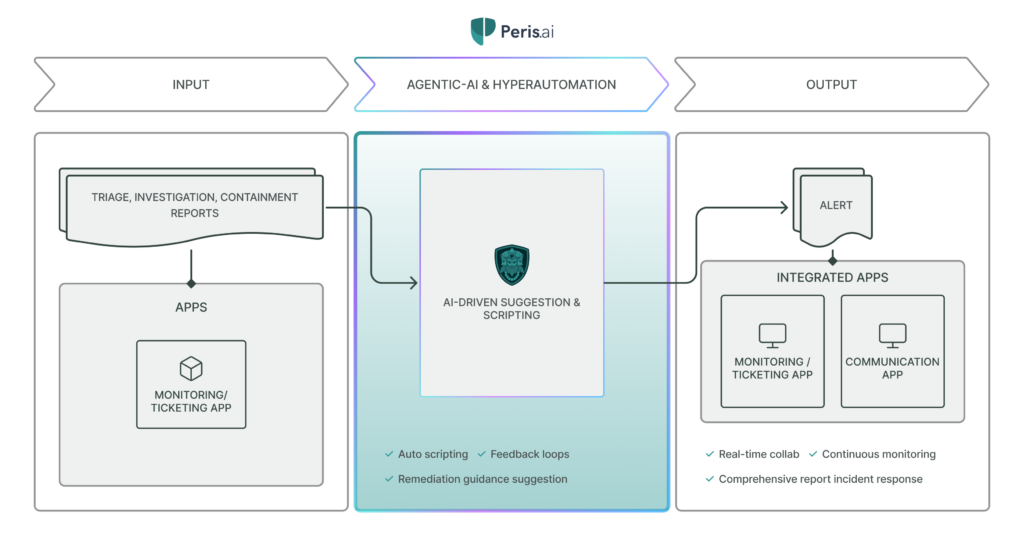
This is exactly where Peris.ai steps in—not as a suite of disconnected tools, but as an AI-orchestrated security nervous system.
Introducing Brahma Fusion & INDRA: The Agentic AI Core of Peris.ai
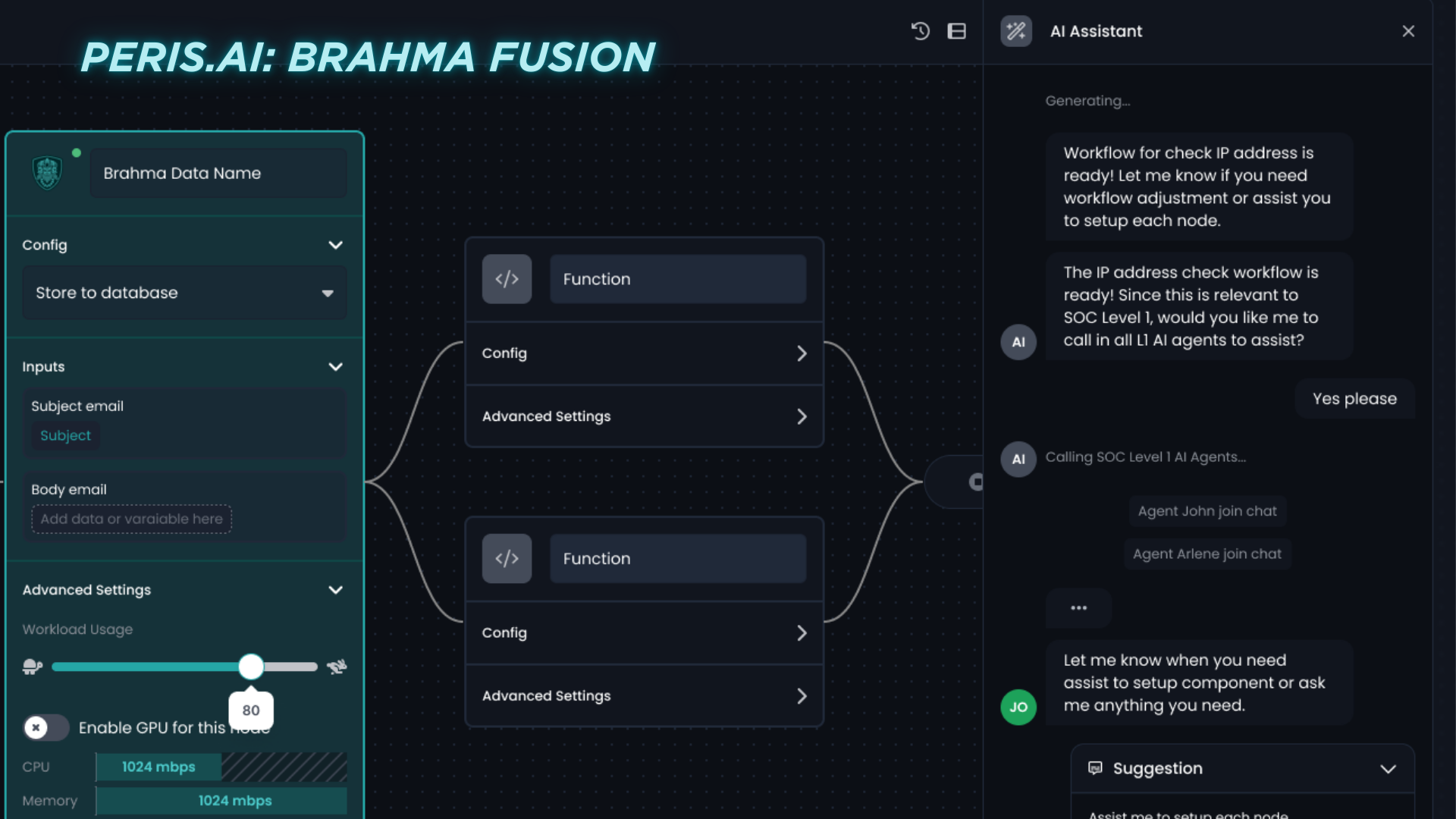
Brahma Fusion: Hyperautomation & SOAR for the Modern SOC
Brahma Fusion is Peris.ai’s intelligent security automation platform—think of it as the brain that integrates data, automates workflows, and recommends actions.
Key Features:
- AI Playbook Builder: Generates and adapts detection and response sequences.
- Real-time Alert Enrichment: Automatically queries CTI, past behavior, asset context.
- Agentic AI: Makes autonomous decisions based on severity, threat context, and business impact.
- Integration-first: Compatible with SIEM, EDR, XDR, firewall logs, and ticketing systems.
“Brahma Fusion reduces triage time by up to 44% by replacing manual steps with intelligent agents.”
INDRA: The Contextual CTI Engine
INDRA is the Cyber Threat Intelligence (CTI) layer that feeds Brahma Fusion with real-time, actionable threat context.
Key Features:
- Global threat actor tracking
- Mapping to MITRE ATT&CK
- Threat trending (e.g. what CVEs are currently being exploited in the wild)
- Exploit maturity, campaign correlations
- AI-driven prioritization scoring
By integrating INDRA into the SOC workflow, analysts no longer make decisions in a vacuum. They know who the attacker likely is, how they operate, and whether an alert matches current threat activity.
AI Playbooks: Not Just Rules, But Reasoning
Unlike traditional SOAR scripts, Peris.ai’s AI Playbooks are dynamic and agentic—they don’t just run static actions; they reason based on evolving context.
Example:
- Detects abnormal outbound traffic.
- Queries INDRA: Is this IP in threat feeds? Yes.
- Checks: Is this asset high-value? Yes—finance server.
- Decision: Escalate to Incident Response, block traffic, and trigger containment.
All of this happens autonomously, reducing analyst workload while increasing precision.
Benefits Observed in Deployments
Reduced MTTD
Peris.ai clients reported mean time to detect dropping from 30 minutes to under 5 minutes post-deployment.
SOC Analyst Retention
By offloading repetitive triage tasks, analyst stress is reduced, and burnout rates drop by 40–50%.
Threat Awareness
With INDRA, alerts come pre-tagged with adversary mapping, enabling faster decisions and more confident actions.
Continuous Learning
Brahma Fusion’s AI learns from every case, every action, every analyst override—making the next detection faster and smarter.
Why Soft, Smart Automation Is Better Than Full Black-Box AI
Peris.ai doesn’t sell the dream of “no humans required.” Instead, it delivers trusted, contextual automation that empowers humans.
Key principles:
- Humans define guardrails
- AI handles grunt work
- Collaboration between AI, CTI, and humans ensures precision
This is agentic AI—intelligent agents operating semi-autonomously, adjusting based on mission needs, and continuously learning from analysts.
Roadmap for Organizations Looking to Cut MTTD
Here’s how any enterprise can begin:
- Step 1: Audit current detection timelines across alerts and incident types.
- Step 2: Identify manual steps in triage/investigation.
- Step 3: Integrate threat intelligence into detection rules.
- Step 4: Deploy automation (like Brahma Fusion) to handle low-tier alerts.
- Step 5: Monitor, tune, and measure detection effectiveness weekly.
- Step 6: Expand AI Playbooks across use cases (ransomware, phishing, insider threats, etc.).
The ROI isn’t just in metrics. It’s in resilience.
Conclusion: MTTD Can’t Be Measured in Minutes Alone—It’s Measured in Impact
Every second between detection and containment is an opportunity—for an attacker to exfiltrate, encrypt, or destroy.
Most organizations don’t lack tools. They lack orchestration, intelligence, and precision.
With Peris.ai’s Brahma Fusion and INDRA, enterprises move from reactive triage to proactive defense, reducing MTTD and freeing analysts to focus on what really matters: thinking like defenders, not acting like robots.
Ready to reduce your detection time before attackers act? Visit peris.ai to learn more about agentic AI for your SOC. #YouBuild #WeGuard