In today’s world, the risk of cyber attacks is high. Organizations must deal with many threats, like advanced malware and persistent attacks. To protect your systems, a good vulnerability management plan is crucial. This plan must focus on risks, fixing the most important vulnerabilities first.
It can be hard to handle all the security updates and patches. You might be wondering how to use your resources wisely to tackle major risks. This guide will show you how to use a risk-focused strategy. It will help you guard against new threats effectively.
Key Takeaways
- Understand the key stages of a vulnerability management program, including identification, prioritization, remediation, and reporting.
- Learn how to define your environment and risks, creating and maintaining a comprehensive asset inventory.
- Discover the importance of continuous network scanning and vulnerability assessments to stay ahead of threats.
- Explore strategies for prioritizing vulnerabilities based on risk, including exploitability and system criticality.
- Gain insights into effective remediation approaches, from patching and upgrading to implementing compensating controls.
Understanding Vulnerability Management
Vulnerability management is about finding, checking, and fixing holes in a system’s security. It looks at threats like service denial, data exposure, and financial losses. And checks how these can affect the business and its compliance.
What is Vulnerability Management?
This is a way to search for and fix security issues in a company’s systems and apps. It’s key for catching problems before hackers can use them. This approach is a must-have for a strong cyber threat detection and risk assessment plan.
Why Do You Need a Vulnerability Management Program?
Having a solid vulnerability management setup is crucial for many reasons. It keeps security strong, follows the rules, and fights off new threats. It also lessens the risks of data theft, system attacks, and harm to the business’s name and money.
The 4 Stages of a Vulnerability Management Program
Good vulnerability management has four main steps:
- Identification: Keep checking the network to find and list all weaknesses.
- Assessment: Look at the found issues to see how they could harm the company. This includes things like patch management and risk assessment.
- Prioritization: Sort out weaknesses by how harmful they could be and how easy to use for hackers. This helps focus on fixing the worst ones first.
- Remediation: Fix the main vulnerabilities by applying patches or other controls. This cuts down on cyber risk.
By sticking to these steps, businesses can stay ahead of cyber threats by managing their vulnerabilities well.
Defining Your Environment and Risks
Starting vulnerability management means knowing your tech world well. It includes checking your network, apps, and work settings for weak spots. When you know where these weak points are, you can act to protect your stuff better.
Evaluating Vulnerabilities in Your Infrastructure
Evaluating your network’s safety is vital. Look for any flaws in firewalls, servers, and more. This helps pinpoint what areas need the most attention to stay secure.
Assessing Vulnerabilities in Applications
It’s also critical to check how safe your apps are. This means seeing if things like who can access what are in good shape. Finding and fixing these spots stops big problems before they happen.
Understanding Your Production Environment
Knowing all about where you make things work is essential. This part is about seeing how everything in your tech world is linked. It helps in finding what must be protected the most to avoid major issues.
Creating and Maintaining an Asset Inventory
Keeping an updated asset inventory is key to a strong vulnerability management program. This list should include all hardware, software, and network assets. It’s helpful to note software versions and patch levels. , Asset management tools can make this job easier, helping to keep information current for vulnerability scanning tools.
A good asset inventory does a lot. It helps security teams spot where attacks might come from. With this info, they can focus on fixing the most important problems first. Plus, knowing about different software helps teams patch things up before they get hacked.
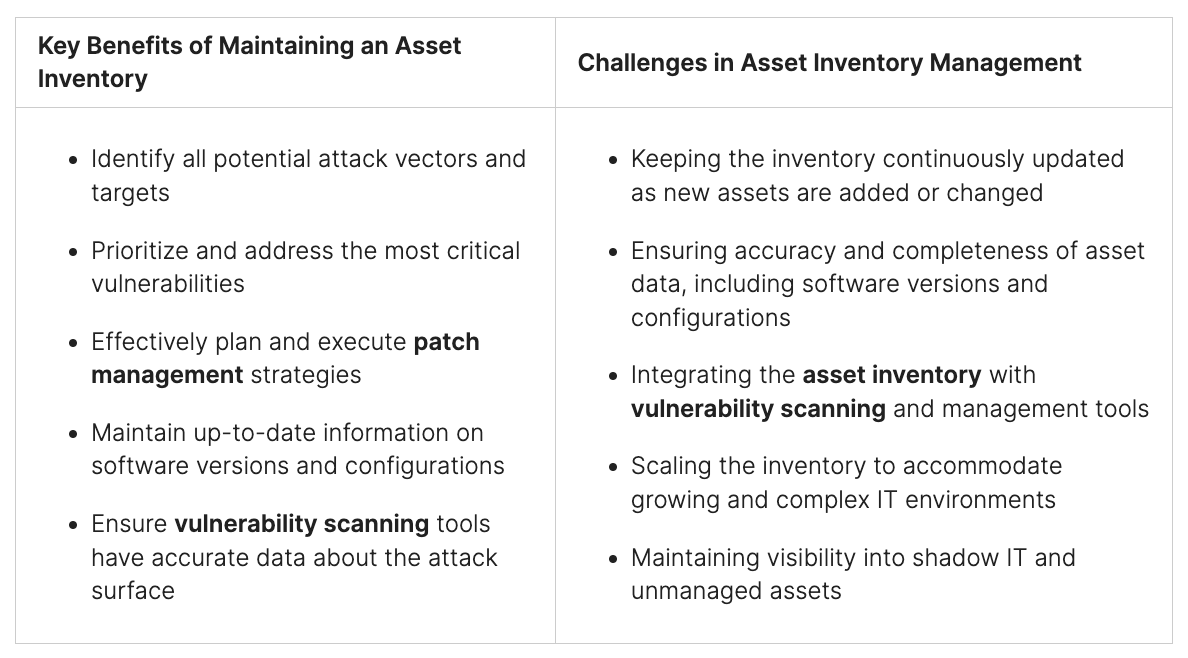
Dealing with these tasks, organizations should turn to asset management solutions. These can automatically find, sort, and keep track of assets. They connect with vulnerability tools too, keeping the data fresh and reflecting real risks.
Using asset inventory well helps improve overall vulnerability management. It lowers the chance of cyber attacks and makes companies more secure.
Continuous Network Scanning
Nowadays, vulnerability scanning happens all the time, not just occasionally. This change meets the need for organizations to always be ready against new threats. Having a system that scans vulnerabilities both inside and outside is a key part of good security. It helps keep systems safe around the clock by finding and fixing weak spots before attackers can use them.
External Vulnerability Scans
When we talk about external scans, we mean checking how a hacker might attack from the outside. These scans look for open doors in security, like weak points in websites or servers. By doing external scans often, companies can close these doors before any harm is done.
Internal Vulnerability Scans
Internal scans, on the other hand, look within a company’s own network and devices. They help find hidden vulnerabilities, like old software or mistakes in setup. This ongoing check lets companies fix problems fast. It stops attacks and protects important information and services.
Doing both external and internal scans, along with keeping software updated, is crucial. It makes sure businesses are always ready to face new security challenges.
Vulnerability Assessments vs Vulnerability Management
A vulnerability assessment is like taking a picture of a company’s security at one moment. But, vulnerability management is a constant process. It includes scanning, looking for problems, deciding what’s most important to fix first, and then fixing them. This helps companies keep up with the ever-changing threats online.
Vulnerability Assessments: A Snapshot in Time
In a vulnerability assessment, experts check an organization’s IT setup. They are looking for spots that cyber attackers might target. They use network scans, test programs, and check system setups for weak points. This work shows the company’s security status at that time, but it doesn’t give a full picture of possible threats.
Vulnerability Management: An Ongoing Process
Vulnerability management means always watching for and fixing IT weaknesses. This includes frequently scanning the network, deciding which threats are most urgent, and applying fixes. By keeping up with these measures, a company can reduce risks and keep their systems secure.
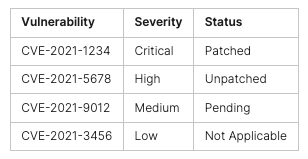
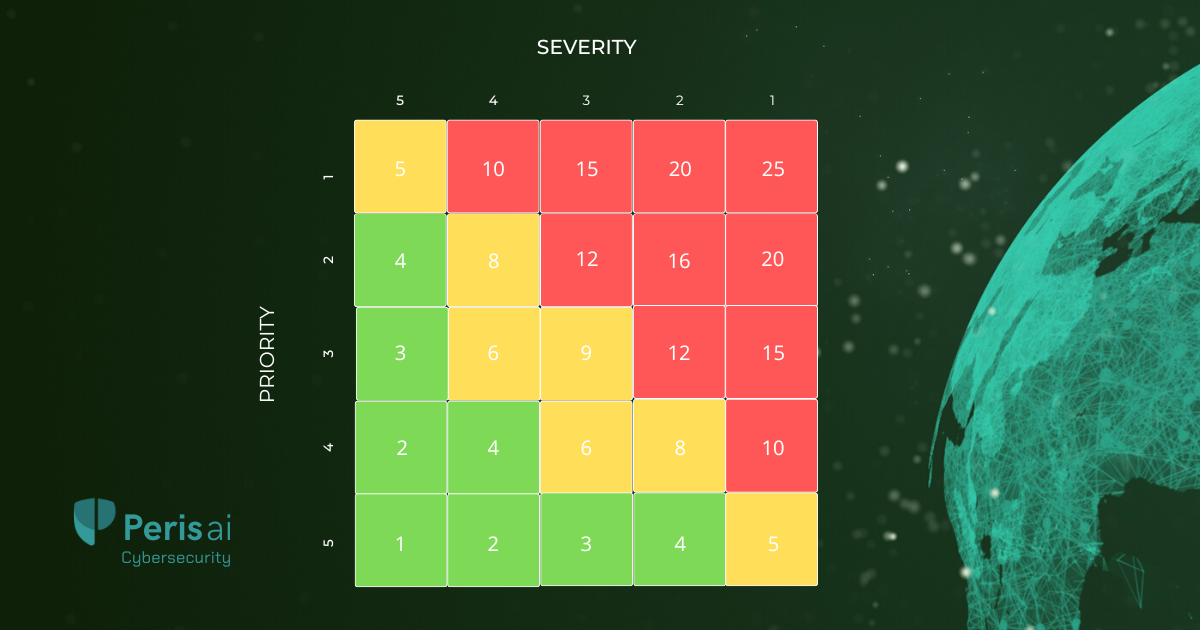
Prioritizing Vulnerabilities Based on Risk
Deciding which vulnerabilities to deal with first is a key part of managing risks. It’s not just about the vulnerability’s CVSS score. It’s also about how likely it is to be used by hackers in the real world.
Assessing Vulnerability Exploitability
We must figure out how likely a bug is to be used by bad actors. We look at whether there are any known ways to ‘exploit’ the bug out in the open. We also consider how skilled a hacker needs to be and what damage they could do.
By looking deeply into what makes a bug risky, security teams can tackle the most important threats first. This ensures they use their time and effort where it matters most.
Considering System Value and Vulnerability Criticality
It’s also vital to think about what a bug could harm and how crucial that thing is. For example, a bug that threatens a key system is more important to fix fast. This is compared to one that targets something less important.
Organizations should weigh both a bug’s danger and the worth of what it targets. This balanced view helps in creating a strong strategy to fight off cyber dangers. It protects their top assets effectively.
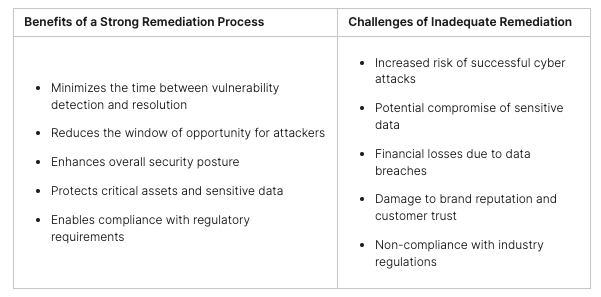
Remediation Strategies
After finding and ranking vulnerabilities, the next step is to fix them. This fix might mean updating software, changing how systems work, or adding extra security measures.
Patching and Upgrading Software
Updating software is a key way to fix problems and strengthen security. Known as patch management, this strategy includes adding new updates and security fixes. This helps to make sure your systems are current and less likely to be targeted by hackers.
Adjusting System Configurations
Besides updating, setting up your systems differently can help. This might involve turning off services you don’t need, controlling who can access what, and using firewalls better. Making these setup changes can be a quick way to fill security holes, especially when updates are still on the way.
Implementing Compensating Controls
At times, fixing problems directly isn’t possible right away. Then, security compliance steps are crucial. This could mean putting in more firewalls, systems to detect intruders or extra security tools. They won’t solve the problem forever, but they add an important shield until the core issues can be solved.
Vulnerability Management and Compliance
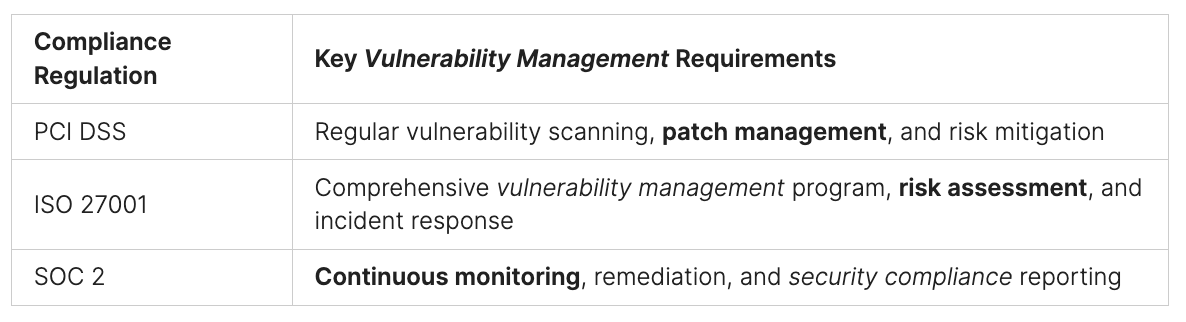
Vulnerability management is very important for a company’s online safety. It also helps with meeting rules in different industries. These rules, like PCI DSS, ISO 27001, and SOC 2, say companies must have strong strategies to keep data and systems safe.
Industry-Specific Regulations
Each type of business has its own set of rules to follow. Good vulnerability management is critical for this. For instance, PCI DSS asks for regular checks on weaknesses and fixing them to keep credit card info safe. ISO 27001 wants companies to set up and keep up detailed vulnerability management plans.
Reporting for Audits and Compliance
Keeping good records is vital for proving your company’s vulnerability management is on point. This helps during checks and audits. The records should show what checks were done, how problems were fixed, and if the plan works well. This kind of reporting shows your company is serious about protecting important info and assets.
Vulnerability Management Best Practices
To succeed in vulnerability management, you need to follow top practices. These include automating important steps and connecting with other security tools. Plus, you must keep an eye on things all the time and be ready to change.
Automating Vulnerability Management Processes
Using automation for every part of handling vulnerabilities makes your safety steps better and quicker. It means you use tools that do tasks like checking for problems, deciding which ones to fix first, and then applying those fixes. This lets your team work on bigger plans.
Integrating with Other Security Tools
For a full view of security, it’s key to connect your vulnerability management with other safety tools. This includes bringing together your systems to watch out for issues, handling incidents, and meeting rules. By doing this, you see your security status better and can fix problems faster and smarter.
Continuously Monitoring and Adapting
Managing vulnerabilities is all about always watching and being ready to change. You need to be on the lookout for new threats and updates on problems. Regular checks and adding new ways from experts help keep your safety plan strong against new dangers.
Vulnerability Management Tools and Resources
Organizations are working hard to set up good vulnerability management programs. Many special tools and resources help with this important work in cybersecurity. Notable vulnerability management tools include Qualys, Tenable, Rapid7, and ServiceNow. They provide everything needed for finding assets, doing vulnerability scanning, assessing risks, and keeping track of fixes.
These tools let companies see their weak points. This way, security teams can find and fix problems in their network and apps fast. Using the power of these vulnerability management tools, companies can improve their cybersecurity and make their defenses stronger.
- Qualys: Asset discovery, vulnerability scanning, risk assessment, compliance management, remediation tracking
- Tenable: Continuous monitoring, vulnerability assessment, threat detection, compliance reporting, risk-based prioritization.
- Rapid7: Vulnerability management, penetration testing, incident detection and response, cloud security.
- ServiceNow: Integrated vulnerability management, asset management, patch management, compliance tracking.
Besides the top vulnerability management tools, organizations can use many cybersecurity resources. These include trade publications, online groups, and professional organizations. They help companies stay up to date with the best advice, trends, and new threats. By using the best tools and resources, companies can build a strong vulnerability management plan. This plan helps prevent risks and keep vital assets secure.
Conclusion
In today’s dynamic digital landscape, a robust vulnerability management plan is essential for organizations striving to maintain strong security defenses and combat cyber threats effectively. Understanding and implementing comprehensive vulnerability management helps organizations identify their risks, conduct regular network assessments, and address critical issues before they can be exploited.
Staying informed and adopting the latest technologies empowers companies to safeguard their data against emerging cyber threats. Additionally, a solid vulnerability management strategy ensures compliance with industry security standards, further strengthening overall security measures.
As the online environment continues to evolve, the importance of vulnerability management cannot be overstated. By leveraging the right tools and methodologies, organizations can significantly reduce risks and protect their most valuable assets, thereby maintaining the trust and confidence of their stakeholders.
Explore our range of advanced cybersecurity products and services at Peris.ai to learn how we can help your organization enhance its security posture and stay ahead of cyber threats. Secure your future with Peris.ai and ensure your business thrives in the ever-changing digital world.
FAQ
What is vulnerability management?
Vulnerability management deals with finding and fixing security holes. It focuses on an organization’s weak points that attackers might target.
Why do you need a vulnerability management program?
It’s vital for keeping the organization safe from cyber threats. Effective management spots risk early and take action to prevent possible harm.
What are the key stages of a vulnerability management program?
The main steps include finding vulnerabilities, deciding which ones are most urgent, fixing them, and then telling others what you did.
How do you define your environment and risks in vulnerability management?
Start by truly understanding your tech world. Look closely at your network, apps, and how data moves. This insight helps find and fix the most critical risks.
Why is maintaining an asset inventory important for vulnerability management?
Keeping track of every IT asset is key. This list should have everything from hardware to software details. It helps in knowing what needs protection the most.
What is the difference between vulnerability assessments and vulnerability management?
An assessment checks security at a single point. But, management keeps looking and fixing, making security stronger over time.
How do you prioritize vulnerabilities based on risk?
Recognize which ones are urgent by their possible danger and how easy it is to attack. The Common Vulnerability Scoring System score helps with this.
What are some common remediation strategies for vulnerabilities?
Usually, you update software, tweak settings, or add security measures. But sometimes, quick fixes aren’t an option, so you might need temporary solutions.
How does vulnerability management relate to compliance?
It’s essential for good security and keeping up with rules. Many regulations demand strong management of vulnerabilities to stay compliant.
What are the best practices for implementing a successful vulnerability management program?
Key steps include using automated tools, connecting with other security solutions, and always checking and improving your defenses.
What are some popular vulnerability management tools and resources?
Some top tools are Qualys, Tenable, and Rapid7. They help with everything from finding assets to fixing issues and tracking progress.