Welcome to our comprehensive guide on the Cybersecurity Triangle for Organizations. In today’s digital landscape, businesses face numerous cyber threats that can compromise their sensitive data and disrupt their operations. Organizations need a strategic approach that balances price, quality, and time in their cybersecurity initiatives to protect their assets. This guideline provides valuable insights into how organizations can make informed decisions, optimize resources, and prioritize cybersecurity investments.
Key Takeaways:
- The Cybersecurity Triangle for Organizations helps businesses find the right balance between price, quality, and time in their cybersecurity initiatives.
- Price considerations involve budgeting and cost allocation for cybersecurity measures.
- Quality focuses on implementing robust and reliable cybersecurity measures.
- Time management strategies ensure efficient implementation and management of cybersecurity strategies.
- Organizations can prioritize their cybersecurity investments by understanding and implementing the Cybersecurity Triangle.
Understanding the Cybersecurity Triangle Concept
The cybersecurity triangle concept is a fundamental framework that organizations must grasp to implement cybersecurity measures effectively. It centers around three key factors: price, quality, and time. By balancing these factors, organizations can develop a comprehensive approach to cybersecurity that addresses their specific needs and maximizes the protection of their assets.
Defining the Cybersecurity Triangle
The cybersecurity triangle comprises three crucial elements:
- Price: This factor involves budgeting and cost allocation for cybersecurity initiatives. Organizations must consider their financial resources carefully and allocate budgetary provisions to support robust cybersecurity measures.
- Quality: Ensuring the effectiveness and reliability of cybersecurity measures is the core focus of this factor. Organizations should implement robust and innovative technologies, adhere to industry best practices, and conduct regular security assessments to maintain high-quality cybersecurity resilience.
- Time: Efficient time management is critical in implementing and managing cybersecurity strategies. Organizations must develop swift incident response plans, deploy rapid deployment security protocols, and conduct thorough disaster recovery planning and analysis to minimize downtime and maintain business continuity.
The Evolution of Cybersecurity Prioritization
Over time, the prioritization of cybersecurity factors has evolved as organizations recognize the increasing importance of a balanced approach:
In the past, organizations often prioritized cost over quality and time, focusing primarily on budgetary concerns. However, cybersecurity incidents and the subsequent financial and reputational damage have shifted the mindset. Organizations have come to understand that compromising quality and neglecting time management can lead to severe consequences. As a result, there has been a paradigm shift towards a comprehensive approach that balances all three factors of the cybersecurity triangle.
By comprehending and implementing the cybersecurity triangle concept, organizations can navigate the complex cybersecurity landscape and make informed decisions safeguarding their digital assets.
Price in Cybersecurity: Budgeting and Costs
Price plays a crucial role in cybersecurity as organizations must budget and allocate sufficient resources to protect their assets effectively. Allocating budgets for cybersecurity involves assessing the specific needs and risks of the organization, understanding the potential impact of cyber threats, and determining the financial investment required to mitigate those risks. This process requires careful consideration of various factors, including the organization’s size, industry regulations, and risk tolerance.
Allocating Budgets for Cybersecurity in Organizations
When allocating budgets for cybersecurity, organizations must take a strategic approach. It starts with assessing the unique needs and risks faced by the organization. By thoroughly evaluating current security measures, vulnerabilities, and potential threats, organizations can identify gaps and prioritize their budget allocation accordingly.
Moreover, organizations should consider the potential impact of cyber threats on their business operations and reputation. This includes evaluating the financial losses that could occur in a data breach or system outage and the costs associated with recovering from such incidents.
Organizations should also consider industry regulations and compliance requirements when allocating budgets for cybersecurity. Organizations must adhere to Different industries’ specific data protection and privacy regulations. This may require additional investments in security technologies, personnel training, and compliance audits.
It is also essential for organizations to balance their budget allocation between preventive, detective, and responsive cybersecurity measures. Preventive measures, such as firewalls and antivirus software, help protect systems and data from cyber threats. Detective measures like intrusion detection systems and security monitoring help identify and respond to potential threats. Responsive measures, such as incident response plans and data recovery solutions, ensure a quick and effective response during a security incident.
Understanding Cybersecurity Expense Categories
When budgeting for cybersecurity, organizations should consider various expense categories to ensure comprehensive coverage. These expense categories include:
- Security personnel: Allocating budget for cybersecurity professionals responsible for implementing and managing security measures.
- Security technologies: Invest in security solutions such as firewalls, antivirus software, encryption tools, and intrusion detection systems.
- Security assessments and audits: Conduct regular assessments and audits to identify vulnerabilities and ensure compliance with industry standards and regulations.
- Employee training and awareness: Budgeting for training programs that help employees understand their role in maintaining cybersecurity and raise awareness about potential threats.
- Incident response and recovery: Allocating resources for developing and implementing incident response plans and investing in data recovery solutions.
By understanding the expense categories and their importance, organizations can allocate their budgets effectively, ensuring that all aspects of cybersecurity are adequately covered.
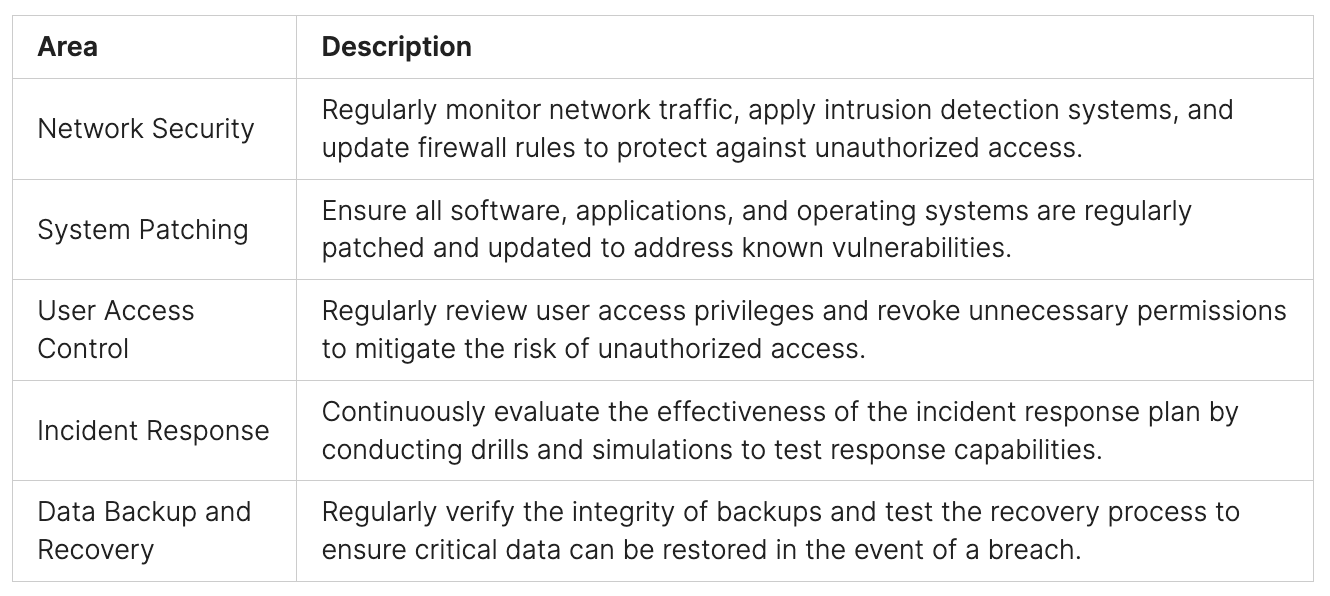
Ensuring Quality in Cybersecurity Measures
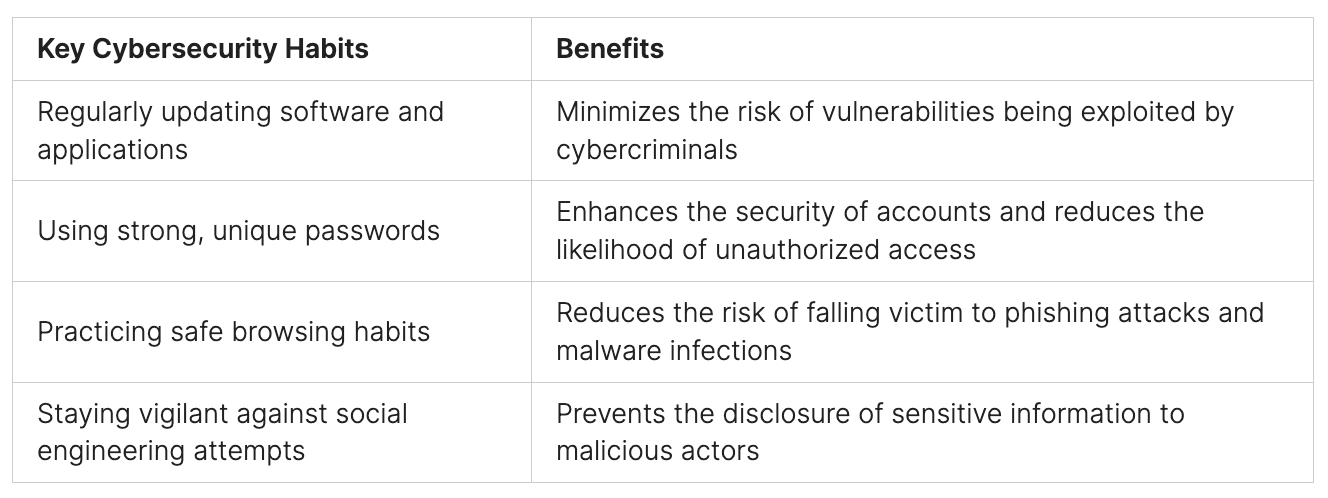
Ensuring quality in cybersecurity measures is vital for organizations to protect their assets from cyber threats effectively. Quality in cybersecurity involves implementing robust and reliable measures that can effectively detect, prevent, and respond to cyber-attacks. This includes using advanced technologies, adherence to industry best practices, regular security assessments and audits, and continuous employee training and awareness programs.
By prioritizing quality in cybersecurity, organizations can enhance their overall security posture and minimize the risk of data breaches and cyber incidents. It is essential to have a comprehensive approach that combines advanced technologies and industry standards for protection against evolving threats.
Organizations need to employ a multi-layered security approach to strengthen their defenses and create a resilient cybersecurity environment. By implementing a range of measures, such as firewalls, intrusion detection systems, encryption, and security information and event management (SIEM) solutions, organizations can detect and prevent cyber attacks. Regular security assessments and audits help identify vulnerabilities and ensure that cybersecurity measures are up to date.
Continuous employee training and awareness programs play a crucial role in ensuring the effectiveness of cybersecurity measures. By educating employees about common cyber threats, phishing attacks, and best practices for data protection, organizations can significantly reduce the risk of human error leading to security breaches.
By adopting a proactive and comprehensive approach to cybersecurity, organizations can stay ahead of cyber threats and safeguard their critical assets.
Key Elements of Ensuring Quality in Cybersecurity Measures
- Implementing advanced technologies
- Adhering to industry best practices
- Conducting regular security assessments and audits
- Providing continuous employee training and awareness programs
Balancing Time Management in Cybersecurity Strategies
Effective time management is essential in cybersecurity strategies to ensure organizations promptly respond to cyber threats while minimizing downtime and disruption. Time management encompasses various practices and processes that optimize time use in cybersecurity initiatives.
One crucial aspect of time management is the development of efficient incident response plans. These plans outline the steps to be taken during a cyber incident, allowing organizations to respond quickly and effectively. By having well-defined incident response plans in place, organizations can minimize the impact of cyber incidents and swiftly mitigate the risks posed by threats.
Rapid deployment security protocols also play a vital role in time management. These protocols enable organizations to rapidly deploy and activate security measures in response to emerging threats. By implementing these protocols, organizations can reduce the time it takes to protect their systems and data, preventing potential security breaches and minimizing the window of vulnerability.
Regular disaster recovery planning and analysis are crucial time management practices in cybersecurity. Organizations need to plan for potential disasters and develop robust recovery strategies proactively. Regular analysis allows organizations to identify vulnerabilities and weaknesses in their disaster recovery plans, enabling them to make necessary improvements and ensure optimal readiness.
By effectively managing time in cybersecurity strategies, organizations can minimize the impact of cyber incidents, reduce recovery time, and ensure the continuous availability of critical systems and data. Time management practices enable organizations to optimize their response to cyber threats and safeguard their assets efficiently and timely.
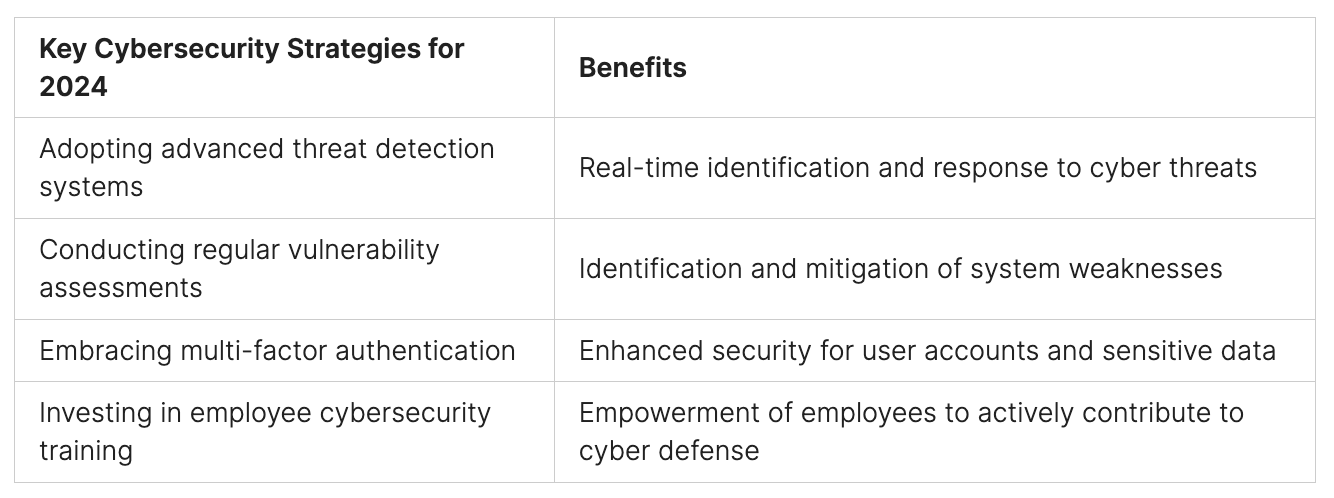
Cybersecurity Investment Decisions: Combining Price, Quality, and Time
Cybersecurity investment decisions require organizations to consider the interplay between price, quality, and time. Achieving a balance among these factors is essential for developing effective cybersecurity strategies that align with organizational goals and resource availability. This section explores case studies and implementation strategies demonstrating successful approaches to combining price, quality, and time in cybersecurity initiatives.
Case Studies and Implementation Strategies
Examining real-world case studies provides valuable insights into how organizations effectively combine price, quality, and time in their cybersecurity investments. These case studies highlight the importance of evaluating and prioritizing cybersecurity needs, understanding the potential impact of cyber threats, and allocating resources accordingly. Organizations can adapt and apply successful strategies to their unique contexts by learning from these examples.
Implementing a comprehensive cybersecurity strategy requires a thoughtful approach that addresses the specific needs and resources of the organization. By considering factors such as budget constraints, risk tolerance, and desired quality of security measures, organizations can make informed decisions on allocating their resources effectively. The implementation strategies from case studies provide practical guidance on integrating price, quality, and time considerations into the overall cybersecurity investment decision-making process.
Public Policy Implications and Corporate Theory
Cybersecurity investment decisions impact individual organizations and have broader implications at the public policy level. Public policy plays a crucial role in shaping the cybersecurity landscape and establishing standards and regulations organizations must adhere to. Understanding the public policy implications of cybersecurity investment decisions is essential for organizations to navigate compliance requirements and ensure the security of their assets.
Corporate theory also influences cybersecurity investment decisions as organizations strive to align their cybersecurity strategies with their overall business strategies. By considering factors such as the organization’s risk appetite, strategic objectives, and stakeholder expectations, organizations can make investment decisions that enhance their resilience to cyber threats while supporting their long-term goals.
Organizations can make informed and strategic cybersecurity investment decisions by analyzing real-world case studies, considering public policy implications, and incorporating corporate theory. This holistic approach ensures that organizations invest in the right cybersecurity measures, combining price, quality, and time to protect their assets effectively and mitigate cyber risks.
Time-Efficient Cybersecurity Strategies for Immediate Threat Response
Time is of the essence when it comes to cybersecurity. Organizations need to act swiftly and decisively to combat immediate cyber threats. This section explores time-efficient cybersecurity strategies that enable organizations to respond promptly and effectively.
Development of Rapid Deployment Security Protocols
Organizations should focus on developing rapid deployment security protocols to combat emerging threats quickly. These protocols allow for the swift deployment and activation of security measures in response to immediate cyber threats. By having predefined procedures and processes in place, organizations can reduce response times and minimize the impact of cyber incidents.
Implementing rapid deployment security protocols involves:
- Establishing a dedicated incident response team that can be activated at a moment’s notice.
- It is developing predefined incident response plans that outline the necessary steps to be taken in the event of a cyber attack.
- Regularly conducting drills and simulations to test the effectiveness and efficiency of the response protocols.
- It integrates automated threat detection and response systems to identify and mitigate cyber threats quickly.
By adopting these rapid deployment security protocols, organizations can significantly enhance their ability to respond to immediate cyber threats, minimize potential damages, and safeguard their critical assets and data.
Disaster Recovery Planning and Analysis
Disaster recovery planning and analysis are essential components of time-efficient cybersecurity strategies. By proactively preparing for potential cyber incidents, organizations can minimize downtime, mitigate damages, and ensure a swift recovery.
Key steps in disaster recovery planning and analysis include:
- Conducting a thorough risk assessment to identify potential vulnerabilities and prioritize critical systems and data.
- Developing comprehensive disaster recovery plans that outline the steps to be taken during a cyber incident.
- Regularly test and update the disaster recovery plans to ensure their effectiveness and relevance.
- Implement backup and data recovery mechanisms to restore critical systems and data quickly.
- Performing post-incident analysis to identify areas for improvement and refine the disaster recovery strategies.
By incorporating disaster recovery planning and analysis into their cybersecurity strategies, organizations can minimize the impact of cyber incidents, reduce downtime, and ensure the continuity of their operations.
Benefits of Time-Efficient Cybersecurity Strategies
- Minimized Response Time – Rapid deployment security protocols allow organizations to respond quickly to cyber threats, reducing the time it takes to identify and mitigate potential damages.
- 2. Reduced Impact of Cyber Incidents – By promptly activating security measures and implementing disaster recovery plans, organizations can minimize the impact of cyber incidents, preventing significant disruptions to their operations.
- Improved Resilience – Time-efficient cybersecurity strategies enhance an organization’s resilience against cyber threats, enabling it to recover quickly and effectively in the face of an incident.
- Enhanced Protection of Assets and Data – Rapid deployment security protocols and disaster recovery planning help organizations safeguard their critical assets and data by implementing proactive measures and efficient response mechanisms.
Achieving Cost-Quality-Time Balance in Cybersecurity
When it comes to cybersecurity, organizations often face the challenge of finding the right balance between cost, quality, and time. Allocating resources efficiently while ensuring adequate protection against cyber threats requires careful analysis and decision-making. This section explores the trade-offs of different cybersecurity approaches and provides practical frameworks for achieving a cost-quality-time balance.
Analyzing the Trade-offs in Cybersecurity Approaches
When implementing cybersecurity measures, organizations must consider various factors and make trade-offs to optimize their investments. One of the key trade-offs is cost versus quality. While investing in high-quality cybersecurity solutions can provide better protection, it often comes at a higher cost. On the other hand, opting for cheaper solutions may compromise the effectiveness of the security measures.
Another trade-off to consider is the balance between cost and time. Implementing comprehensive cybersecurity strategies takes time and effort, which may result in delays or disruptions to business operations. Therefore, organizations must analyze the trade-off between investing sufficient time in cybersecurity measures and the potential impact on productivity and efficiency.
Lastly, there is also a trade-off between quality and time. Implementing high-quality cybersecurity measures requires thorough planning, testing, and implementation. This may slow down the process compared to quick fixes or shortcuts, prioritizing speed over quality. Organizations need to weigh the benefits of investing time in quality measures against the urgency of immediate protection.
Practical Frameworks for Cybersecurity Balance
To help organizations achieve a cost-quality-time balance in cybersecurity, practical frameworks can guide decision-making and resource allocation. These frameworks consider each organization’s unique needs and resources and provide structured approaches to striking the right balance. Here are some practical frameworks to consider:
- Risk-Based Approach: This framework identifies and prioritizes the most critical cyber risks based on their potential impact and likelihood of occurrence. Organizations can allocate resources effectively by aligning cybersecurity investments with risk assessments while addressing the most significant threats.
- Cost-Benefit Analysis: This framework evaluates the costs and benefits of different cybersecurity measures. By quantifying the potential risks and potential savings associated with each measure, organizations can make informed decisions on where to invest their resources.
- Resource Optimization Model: This framework considers the available resources and constraints of the organization, such as budget, manpower, and technology. By optimizing the allocation of resources, organizations can maximize the impact of their cybersecurity measures within the given limitations.
- Continuous Improvement Framework: This framework emphasizes the iterative and continuous improvement of cybersecurity measures. By implementing an ongoing monitoring and evaluation process, organizations can identify areas for improvement and make adjustments to achieve a better cost-quality-time balance.
Implementing these practical frameworks can enable organizations to make informed decisions, optimize their cybersecurity investments, and maintain an effective balance between cost, quality, and time. By finding this balance, organizations can enhance their security posture, mitigate risks, and protect their valuable assets.
Cybersecurity Budgeting for Organizations: A Structured Approach
Cybersecurity budgeting for organizations requires a structured approach that considers the specific needs and resources of the organization. By following a structured approach, organizations can ensure that their cybersecurity investments are aligned with their strategic objectives while effectively protecting their assets.
One key step in the structured approach to cybersecurity budgeting is assessing risk. Organizations must evaluate the potential risks, such as the likelihood and impact of different cyber threats. This assessment helps identify the areas where cybersecurity investments are most crucial, ensuring that resources are allocated where they are most needed.
Once the risk assessment is complete, organizations can prioritize their investments. This involves determining the order in which cybersecurity initiatives should be implemented based on their potential impact on risk reduction. By prioritizing investments, organizations can first ensure that limited resources are allocated to the most critical areas.
Another important step is aligning the budget with strategic objectives. Organizations must consider their overall business goals and how cybersecurity investments can support them. This alignment ensures cybersecurity becomes integral to the organization’s strategic planning, with resources allocated accordingly.
It is crucial to involve key stakeholders in the cybersecurity budgeting process. This includes representatives from different departments and levels of the organization who can provide valuable insights and perspectives. By involving stakeholders, organizations can gather diverse input and ensure that the budget reflects the needs and priorities of the entire organization.
Organizations should conduct thorough assessments and regularly review and adjust the budget based on evolving cyber threats and organizational priorities to maintain effectiveness. By staying proactive and adaptive, organizations can ensure that their cybersecurity budget remains aligned with the changing threat landscape and the organization’s strategic goals.
Effective cybersecurity budgeting is essential for organizations to allocate their resources efficiently and effectively, ensuring the protection of their assets. By following a structured approach and considering the specific needs and resources of the organization, organizations can optimize their cybersecurity investments and enhance their overall security posture.
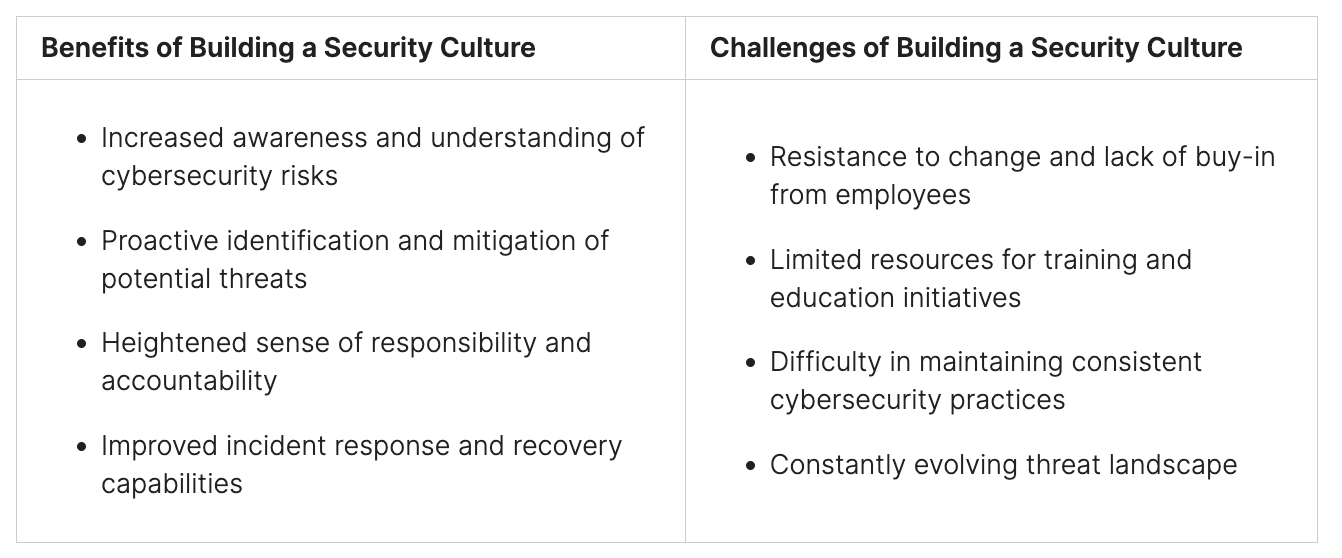
Conclusion: Harmonizing the Cybersecurity Triangle with Corporate Strategy
In summary, organizations must weave the principles of the cybersecurity triangle into their corporate strategy to safeguard their assets against digital threats effectively. The interplay of cost, excellence, and timeliness forms the crux of this approach, guiding businesses in formulating an all-encompassing cybersecurity plan that resonates with their overarching business goals.
The cybersecurity triangle acts as a strategic compass, guiding the allocation of resources and the management of risks. This paradigm aids companies in striking a balance between financial limitations and the imperative for dependable, high-caliber cyber defense mechanisms. Embedding this model into their strategic framework empowers organizations to elevate their cybersecurity standing, mitigate potential risks, and secure their assets for the long haul.
Implementing the cybersecurity triangle into an organization’s strategy demands a comprehensive viewpoint. Companies must weigh the fiscal aspects of their cybersecurity ventures, ensuring ample allocation of resources to combat the continually changing cyber threats. High-quality cybersecurity solutions, incorporating cutting-edge technology and best practices, are paramount for effective threat detection, prevention, and response.
Moreover, time is a critical element in cybersecurity strategies. Quick and effective incident response plans, swift security protocol implementation, and thorough disaster recovery plans are essential. These steps enable organizations to swiftly tackle emerging threats and reduce the impact of any operational disruptions.
Fusing the cybersecurity triangle with corporate strategy lays the groundwork for a resilient, forward-thinking cybersecurity posture. This strategy equips businesses to defend their valuable assets robustly, uphold customer trust, and successfully navigate the intricate and evolving realm of cyber threats.
For tailored cybersecurity solutions that align with this approach, we encourage you to contact us or visit Peris.ai Cybersecurity.
FAQ
What is the cybersecurity triangle for organizations?
The cybersecurity triangle for organizations is a comprehensive guideline that helps businesses find the right balance between price, quality, and time in their cybersecurity initiatives. It allows organizations to effectively protect their assets from cyber threats while optimizing their resources.
What does the price aspect of the cybersecurity triangle involve?
The price aspect involves budgeting and cost allocation for cybersecurity initiatives. Organizations must assess their needs and risks, understand the potential impact of cyber threats, and determine the financial investment required to mitigate those risks.
How can organizations ensure quality in their cybersecurity measures?
Organizations can ensure quality in cybersecurity by implementing robust and reliable measures that effectively detect, prevent, and respond to cyber-attacks. This includes using advanced technologies, adhering to industry best practices, conducting regular security assessments, and providing continuous employee training and awareness programs.
Why is time management important in cybersecurity strategies?
Time management is crucial in cybersecurity strategies to effectively respond to cyber threats, minimize downtime, and ensure the continuous availability of critical systems and data. It involves developing efficient incident response plans, implementing rapid deployment security protocols, and conducting regular disaster recovery planning and analysis.
How can organizations make cost-effective cybersecurity investment decisions?
Organizations can make cost-effective cybersecurity investment decisions by considering the interplay between price, quality, and time. This involves analyzing budget constraints, resource availability, risk tolerance and prioritizing investments based on specific needs and resources.
What are some key considerations for implementing high-quality cybersecurity solutions?
Implementing high-quality cybersecurity solutions requires using cryptography and access management techniques to ensure the confidentiality and integrity of sensitive data. Organizations should also implement data integrity and protection mechanisms such as encryption and data backup strategies to safeguard their data against unauthorized access and tampering.
How can organizations develop time-efficient cybersecurity strategies for immediate threat response?
Organizations can develop time-efficient cybersecurity strategies by establishing rapid deployment security protocols that enable quick activation of security measures in response to emerging threats. They should also have robust disaster recovery plans and procedures to recover from cyber incidents and minimize the impact of disruptions.
How can organizations strike the right balance between cost, quality, and time in their cybersecurity strategies?
Organizations can achieve a cost-quality-time balance in cybersecurity by analyzing trade-offs in different approaches, considering budget constraints, resource availability, and risk tolerance. Practical frameworks can help organizations make informed decisions and allocate resources efficiently and effectively.
What is a structured approach to cybersecurity budgeting for organizations?
A structured approach to cybersecurity budgeting involves assessing risk, prioritizing investments, and aligning the budget with strategic objectives. It requires involving key stakeholders, conducting thorough assessments, and regularly reviewing and adjusting the budget based on evolving threats and priorities.
How can organizations integrate the cybersecurity triangle into their corporate strategy?
Integrating the cybersecurity triangle into corporate strategy allows organizations to develop a comprehensive cybersecurity approach that aligns with their business objectives. It provides a framework for decision-making, resource allocation, and risk management, enhancing an organization’s overall cybersecurity posture and ensuring the long-term security of assets.