Pentesting, also known as penetration testing, is a crucial practice in the field of cybersecurity. It involves rigorously scrutinizing computer systems, networks, and web applications to identify and expose vulnerabilities that attackers could exploit. By proactively testing and reinforcing the security of digital infrastructures, pentesting plays a vital role in defending against constantly evolving cyber threats.
This article will delve into the intricacies of pentesting, exploring its meaning, a pentester’s career path, and the practice’s technicalities. It will also discuss specialized areas of pentesting, such as network penetration testing and physical penetration testing, highlighting the importance of this proactive approach to cybersecurity.
Key Takeaways:
- Pentesting is a proactive approach to cybersecurity, identifying and addressing vulnerabilities before attackers can exploit them.
- It involves rigorous testing and reinforcement of computer systems, networks, and web applications.
- A career in pentesting requires a strong foundation in IT fundamentals, specialized skills, and continuous learning.
- Specialized areas within pentesting, such as network penetration testing and physical penetration testing, further enhance cybersecurity measures.
- As social engineering attacks evolve, organizations need to stay vigilant and invest in advanced security tools and awareness programs.
The Essence of Penetration Testing in Cyber Security
Penetration testing, also known as pen testing, is a fundamental practice in the realm of cybersecurity. It involves thoroughly examining computer systems, networks, or web applications to identify vulnerabilities that attackers could potentially exploit. By simulating cyber-attacks and pinpointing weaknesses, penetration testing helps organizations assess the effectiveness of their security measures and fortify their defenses. This proactive approach is essential in an era where cyber threats are constantly evolving, making the role of a pentester indispensable in the ongoing battle against cybercrime.
To better understand the significance of penetration testing, let’s explore some key aspects related to this important field:
- The proactive nature: Penetration testing takes a proactive approach to cybersecurity. Instead of waiting for an attack, organizations employ pentesters to actively search for vulnerabilities and address them before they can be exploited. This proactive stance enables businesses to stay one step ahead of cybercriminals, minimizing the potential damage and loss.
- Vulnerability assessment: Penetration testing involves thoroughly assessing vulnerabilities within computer systems, networks, or web applications. It encompasses various techniques and methodologies to identify weaknesses and potential entry points for attackers. By conducting vulnerability assessments, organizations can comprehensively understand their security posture and develop effective strategies to enhance their defenses.
- Cybersecurity optimization: The primary objective of penetration testing is to optimize cybersecurity measures. Organizations can implement targeted solutions to address these gaps by identifying vulnerabilities and weaknesses. Regular penetration testing allows businesses to measure the effectiveness of their security measures, identify areas that require improvement, and make informed decisions regarding resource allocation for maximum cyber defense.
Overall, penetration testing is crucial in fortifying cybersecurity by identifying vulnerabilities, assessing their potential impact, and implementing proactive measures to mitigate risks. It enables organizations to proactively approach cybersecurity, optimize their defenses, and stay ahead of the ever-evolving cyber threat landscape.
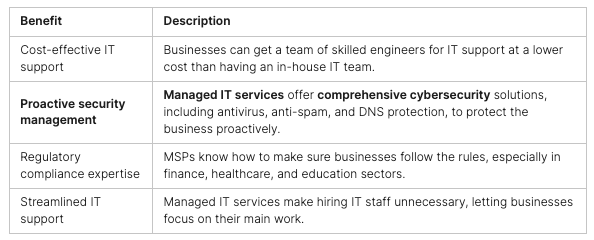
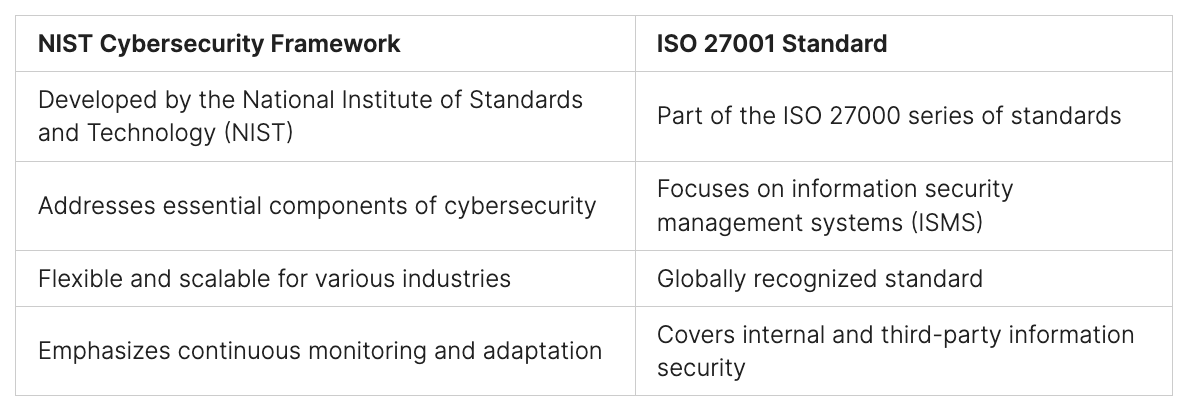
Benefits of Penetration Testing:
The Pentester Career Path
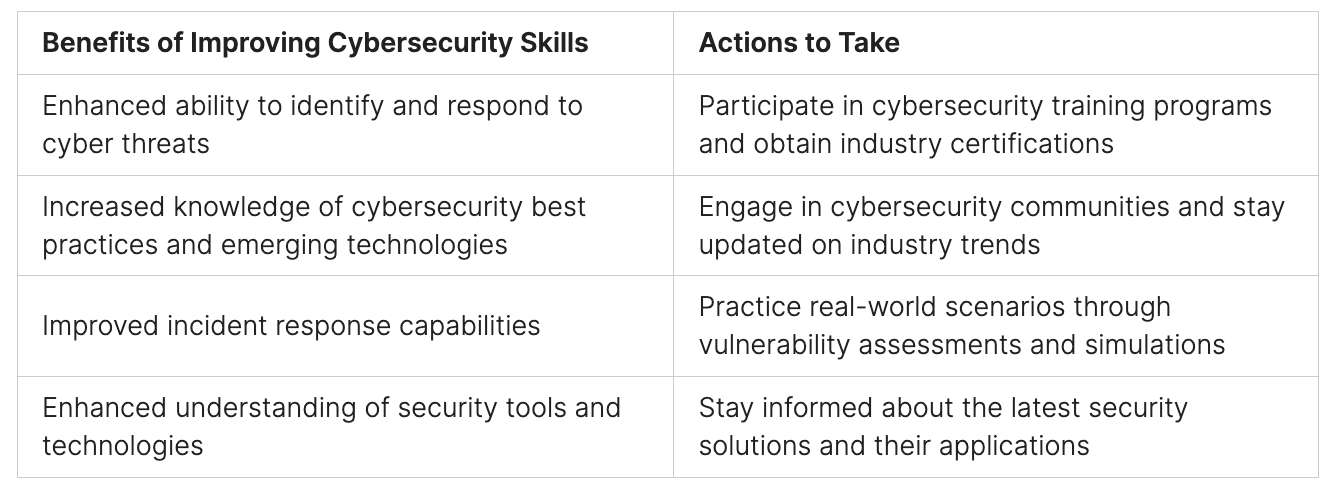
The career path of a pentester is an exciting journey into the dynamic world of cybersecurity. Aspiring pentesters need to develop a strong foundation in IT fundamentals and progressively specialize in security pen and cyber penetration testing. Gaining experience in roles such as network security analyst or IT security consultant can pave the way for advancement.
Continuous learning is crucial in this field, as cybersecurity is ever-evolving. Pentesters must stay current with the latest hacking techniques, defensive strategies, and emerging technologies. Engaging in certifications, such as the Certified Ethical Hacker (CEH) certification, demonstrates a commitment to enhancing skills and knowledge.
Hands-on experience is invaluable for pentesters. Intrusion testing and computer security and penetration testing provide real-world exposure to identify and exploit vulnerabilities in digital systems.
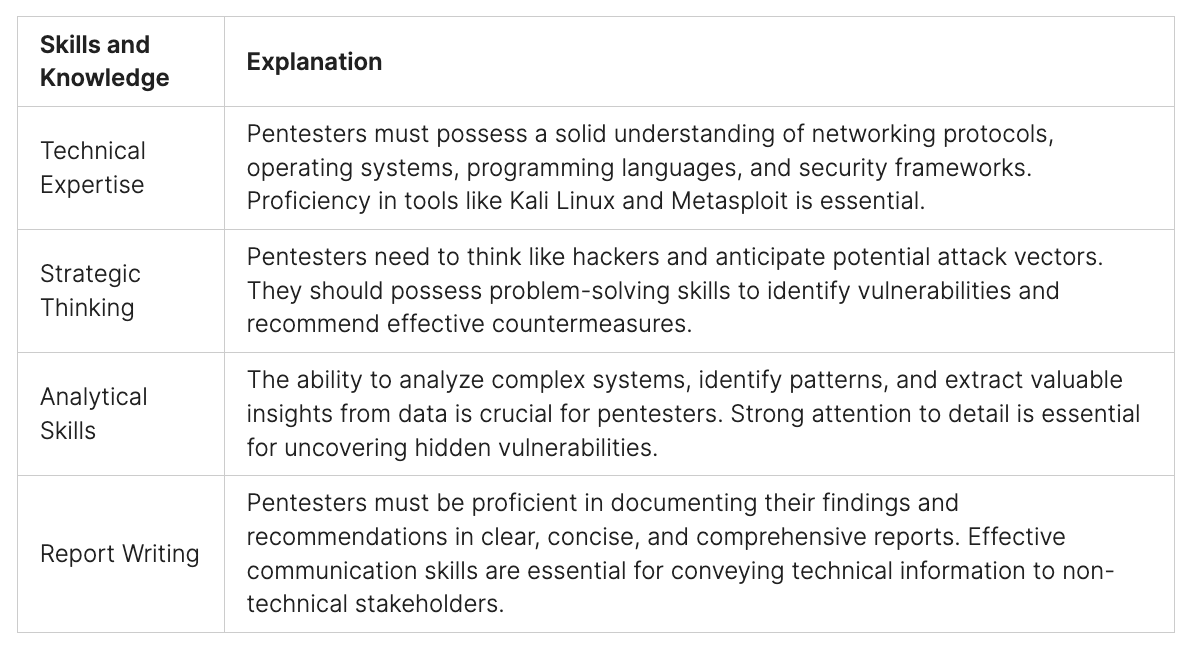
The role of a pentester requires not only technical expertise but also ethical conduct. It is essential to work within legal frameworks and adhere to professional ethics. Pentesters are critical in enhancing cybersecurity by identifying weaknesses and helping organizations strengthen their defenses.

The Technicalities of Penetration Testing
Penetration testing is a systematic approach to identifying and exploiting network, system, and application security vulnerabilities. It plays a crucial role in maintaining network security, evaluating entry points, identifying weaknesses, and simulating cyber-attacks to gauge potential impact. By employing various techniques and methodologies, pentesters uncover vulnerabilities that can be further mitigated through security optimization.
Penetration Testing Techniques
Penetration testing involves a range of techniques tailored to address different security aspects. These techniques include:
- Social Engineering: This technique exploits human vulnerabilities through deception and manipulation.
- Technical System Hacking: It involves identifying and exploiting weaknesses in the target system’s infrastructure and software.
- Network Sniffing: This technique captures and analyzes network traffic to uncover potential security vulnerabilities.
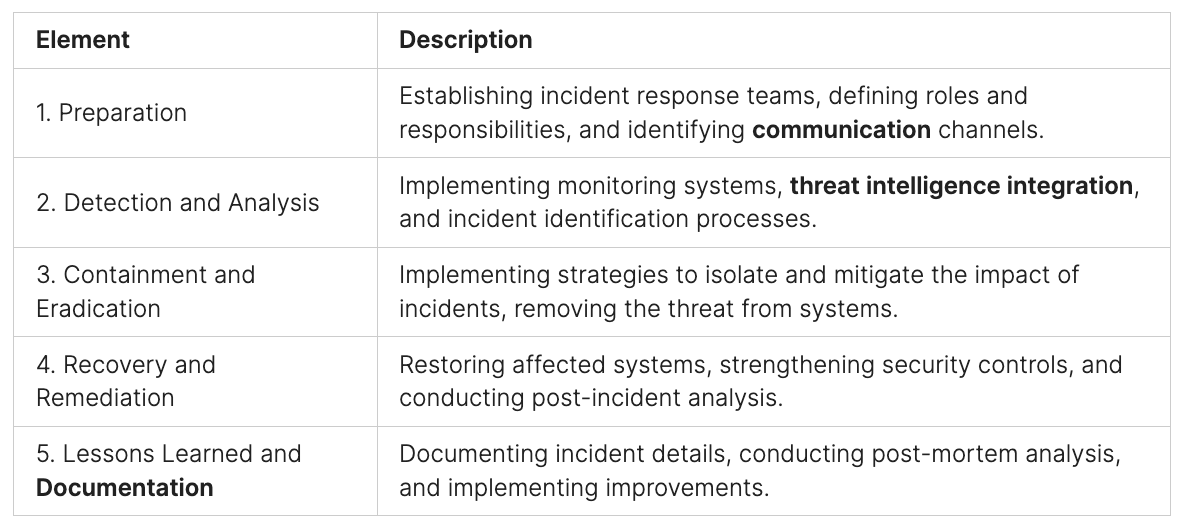
The Penetration Testing Process
The penetration testing process typically follows a structured methodology, ensuring a comprehensive assessment of security vulnerabilities:
- Reconnaissance: Gathering information about the target system to understand its architecture and potential vulnerabilities.
- Scanning and Gaining Access: Identifying and exploiting vulnerabilities to access the target system.
- Maintaining Access: Sustaining the compromised access to analyze potential impacts and uncover deeper vulnerabilities.
- Reporting and Suggesting Improvements: Document findings and provide recommendations to enhance network security and mitigate vulnerabilities.
Network Security and Vulnerability Identification
Network security penetration testing is an essential component of penetration testing, focusing on maintaining the integrity and confidentiality of a network. By evaluating entry points, identifying weaknesses, and simulating cyber-attacks, pentesters play a critical role in fortifying network defenses. Through meticulous vulnerability identification, organizations can proactively address security gaps, optimize security measures, and ensure a robust cyber defense strategy.

Specialized Areas in Penetration Testing
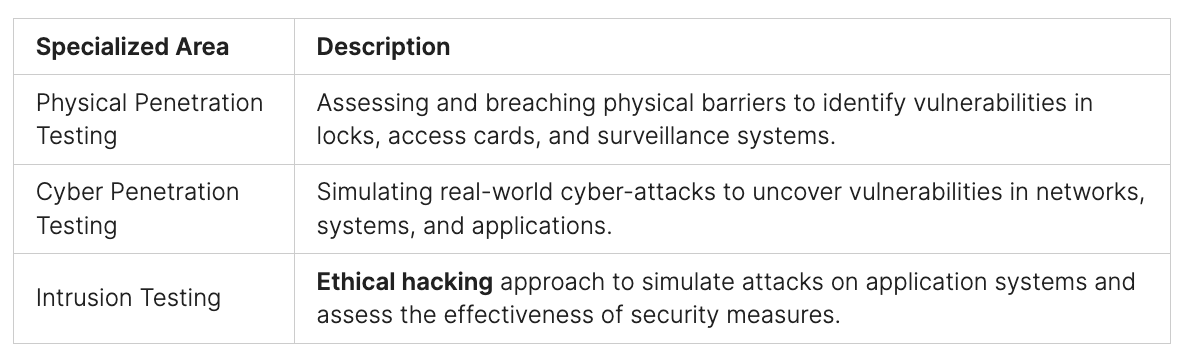
Penetration testing, a vital practice in cybersecurity, extends beyond traditional network testing to specialized areas that further fortify digital defense systems. These specialized areas include physical penetration testing, cyber penetration testing, and intrusion testing, each serving a distinct purpose in ensuring comprehensive security.
Physical Penetration Testing
Physical penetration testing focuses on assessing and breaching physical barriers, such as locks, access cards, and surveillance systems. This branch of penetration testing requires a unique blend of skills and expertise, encompassing familiarity with digital and physical security protocols, social engineering tactics, and knowledge of modern security systems. By scrutinizing physical security measures, organizations can identify vulnerabilities and fortify their physical defenses.
Cyber Penetration Testing
Cyber penetration testing is crucial in safeguarding digital assets against various cyber threats. It involves simulating real-world cyber-attacks to identify network, system, and application vulnerabilities. By thoroughly examining the digital infrastructure, cyber penetration testing enables organizations to identify and address weaknesses, preventing potential breaches, data theft, or system compromise.
Intrusion Testing
Intrusion testing, or ethical hacking, is a branch of penetration testing that simulates attacks on various application systems. By adopting the perspective of a malicious actor, intrusion testers identify vulnerabilities and exploit them to assess the effectiveness of security measures. This testing methodology gives organizations critical insights into their application’s security posture, enabling them to mitigate risks and enhance their overall cybersecurity proactively.
These specialized areas within penetration testing underscore the importance of a comprehensive and proactive approach to cybersecurity. By combining physical penetration testing, cyber penetration testing, and intrusion testing, organizations can build robust defense mechanisms that effectively safeguard their digital assets from ever-evolving threas.

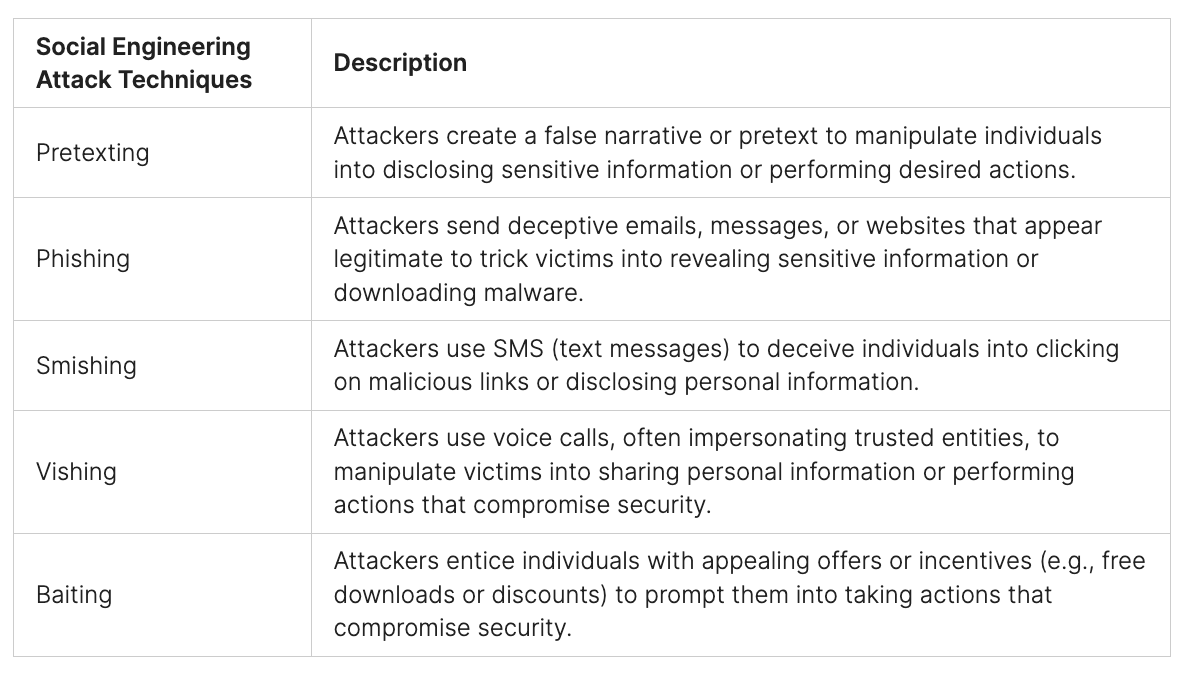
Social Engineering in Cybersecurity
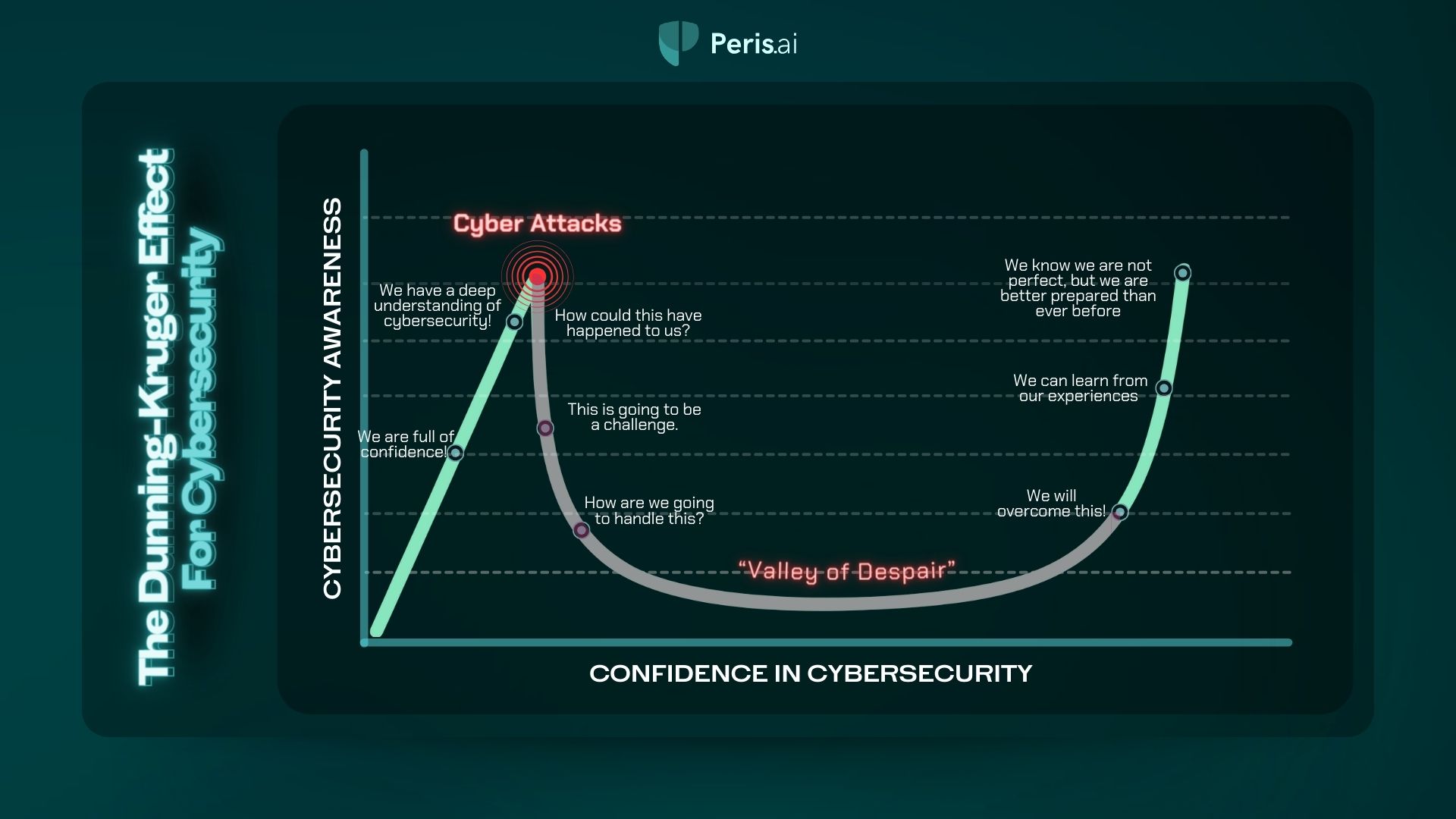
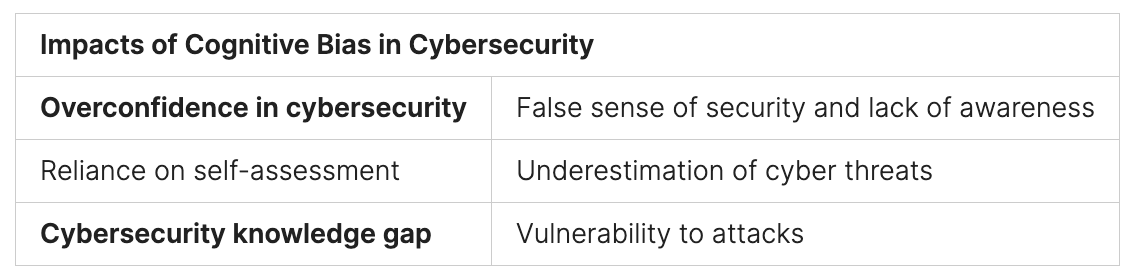
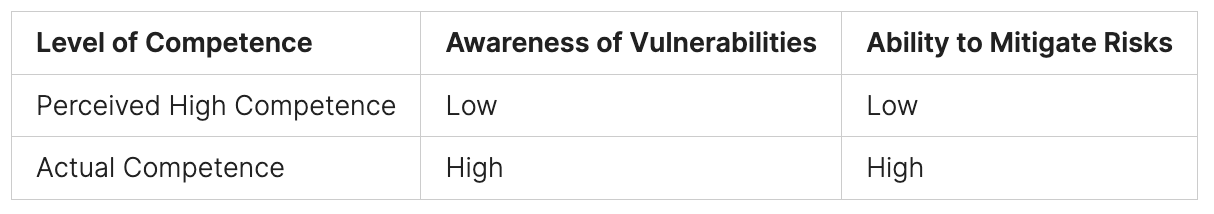
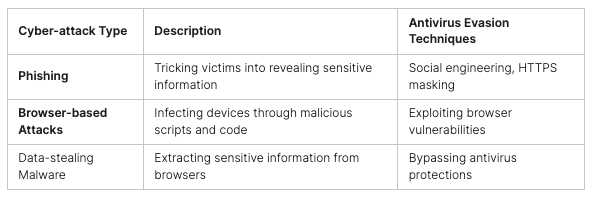
Social engineering is an insidious tactic employed by attackers to exploit psychological vulnerabilities and manipulate individuals into providing sensitive information or performing actions that compromise cybersecurity. These attacks capitalize on human psychology and trust to deceive individuals and gain unauthorized access to sensitive data or systems. In the digital age, social engineering attacks have become increasingly sophisticated, leveraging advanced technologies such as AI-powered attacks to enhance their effectiveness.
The Social Engineering Attack Cycle
Social engineering attacks typically follow a cycle that involves several stages:
- Information Gathering: Attackers collect personal, organizational, or technical information about their targets, often using open-source intelligence (OSINT) techniques.
- Relationship Establishment: Using the gathered information, attackers build rapport or establish a relationship with the target, exploiting their trust.
- Exploitation: Attackers manipulate the target into performing actions that benefit the attacker, such as disclosing sensitive information or clicking on malicious links.
- Culmination: The attack reaches its intended goal, which may involve unauthorized access, data theft, financial fraud, or other malicious activities.
An understanding of this attack cycle is crucial for individuals and organizations to recognize and defend against social engineering attacks effectively.
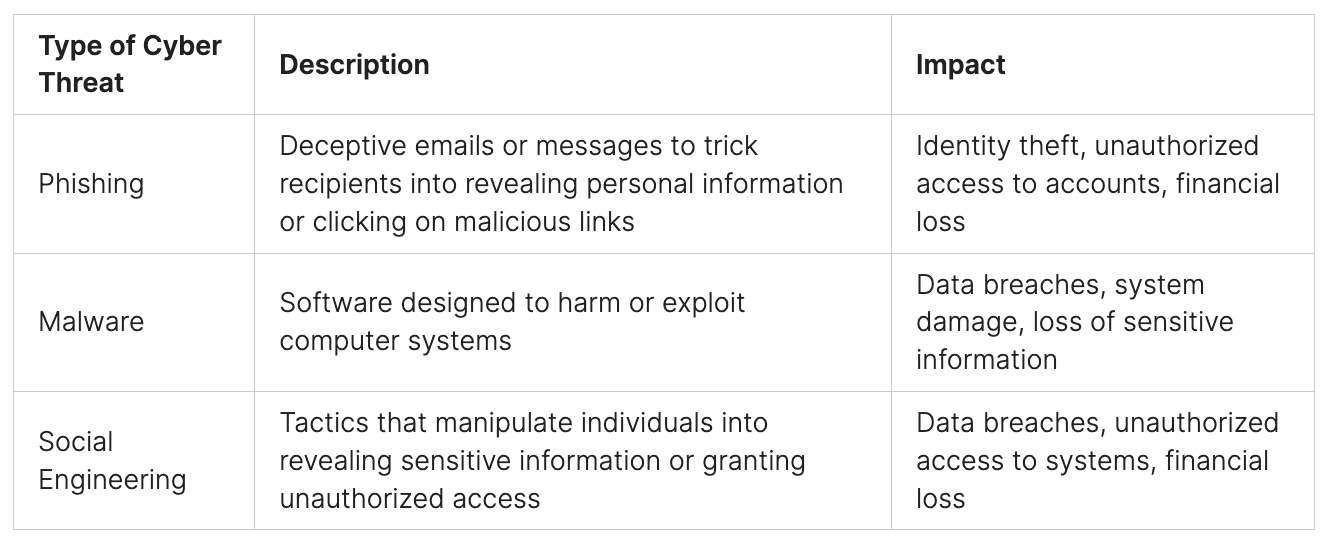
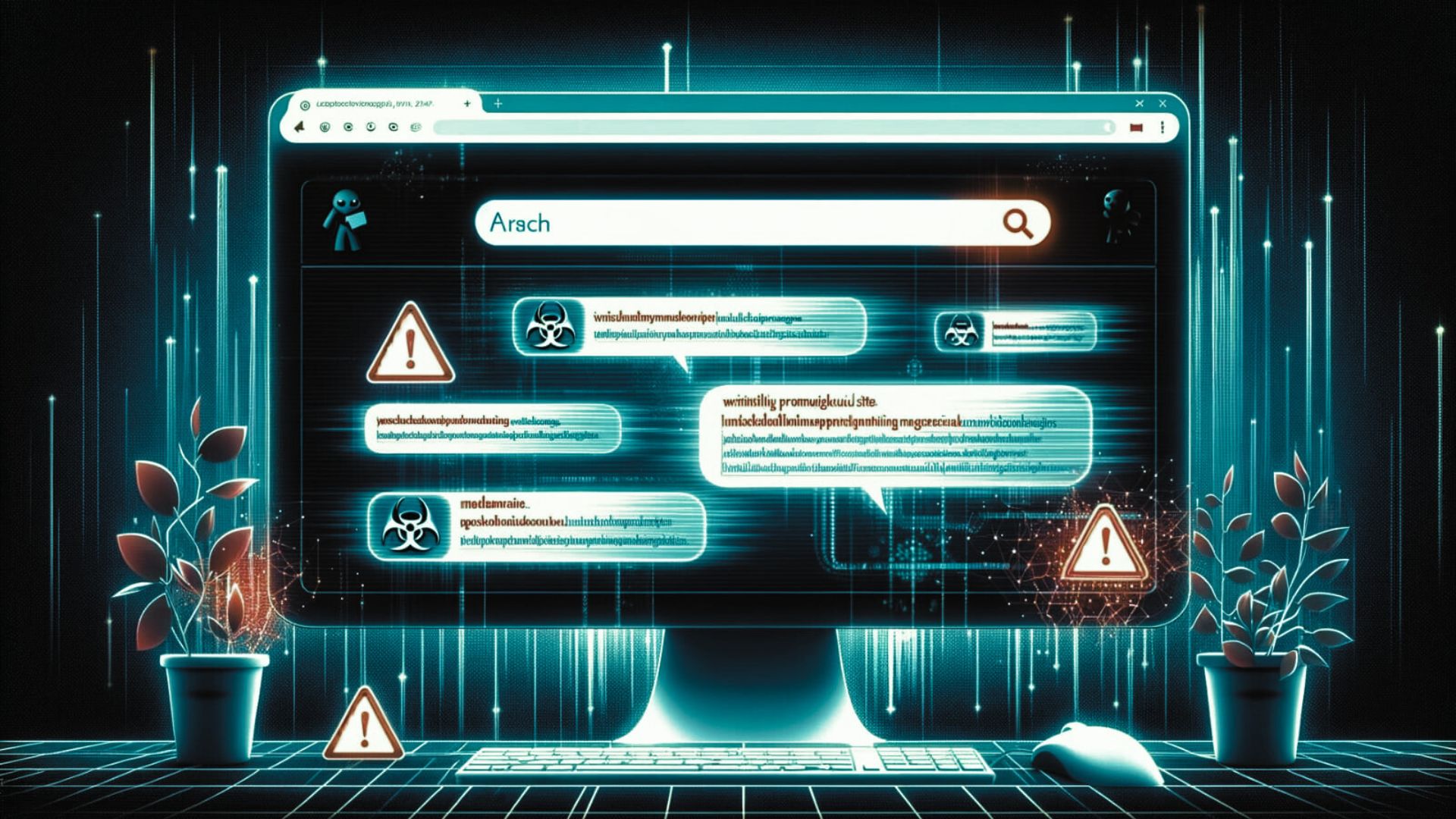
Email Phishing: A Prevalent Form of Social Engineering
One of the most prevalent forms of social engineering is email phishing, where attackers send deceptive emails posing as legitimate entities to trick recipients into disclosing sensitive information, downloading malware, or initiating unauthorized actions. Phishing attacks often exploit psychological factors such as urgency, curiosity, or fear to manipulate victims into taking the desired action.
Email analysis and detection techniques are crucial in identifying and preventing phishing attacks. By analyzing email headers, content, and attachments, security professionals can assess their legitimacy and detect red flags that indicate phishing attempts.
A Role of AI in Social Engineering Attacks
“Artificial intelligence is increasingly being leveraged by attackers to craft convincing messages and enhance the effectiveness of social engineering attacks. Machine learning algorithms can analyze vast amounts of data to create highly personalized and persuasive communications.”
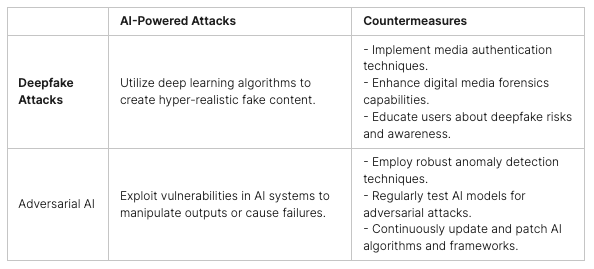
The integration of AI technology in social engineering attacks poses a new level of threat. AI-powered attacks can generate emails, messages, or voice calls that closely mimic human communication styles and patterns, making it more challenging to distinguish between genuine and malicious communications.
Addressing AI-powered social engineering attacks requires a multi-faceted approach that combines advanced security measures with user awareness and education. Organizations should deploy AI-driven tools and solutions to analyze incoming communications and identify potential phishing attempts. Additionally, ongoing training and awareness programs can help individuals recognize and report suspicious activities, mitigating the risks associated with social engineering attacks.
By understanding the tactics employed in social engineering attacks, organizations can implement robust security measures and educate their users to stay vigilant and protect against this constantly evolving threat.
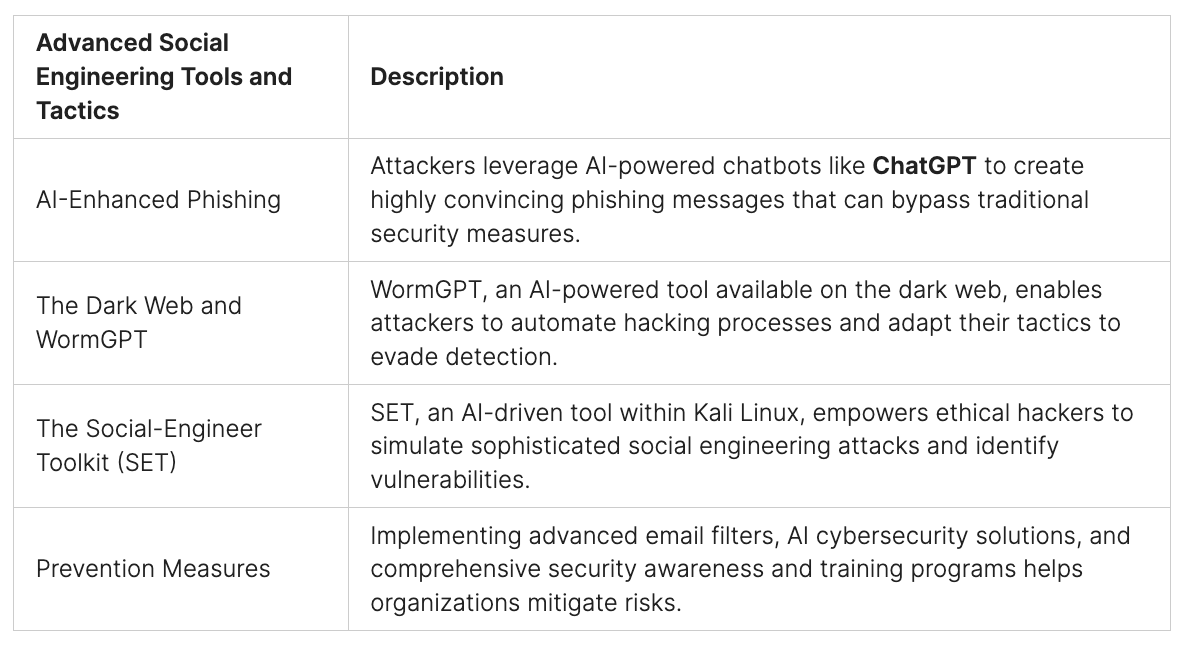
Advanced Social Engineering Tools and Tactics
With the rapid advancement of AI technology, social engineering attacks have become more sophisticated. Attackers are leveraging emerging tools and tactics, including the integration of AI in phishing campaigns, to increase their success rates and evade detection. Organizations must stay informed about these evolving techniques and implement robust prevention measures.
AI-Enhanced Phishing
One of the latest advancements in social engineering attacks is using AI technology to enhance phishing campaigns. Attackers leverage AI-powered chatbots like ChatGPT to create compelling messages that mimic human conversation. These AI-driven phishing attempts can bypass traditional cybersecurity defenses, making it challenging for users to discern between genuine and malicious communications.
To illustrate the potential impact of AI-enhanced phishing, consider the example of a banking phishing attack. Attackers can use AI algorithms to analyze a target’s social media profiles, blog posts, and other publicly available information to craft personalized and plausible phishing emails. These emails may appear to come from a trusted institution, tricking recipients into revealing sensitive information or downloading malicious attachments.
The Dark Web and WormGPT
The dark web is a hidden part of the internet where anonymous activities occur, including buying and selling hacking tools and services. Within this underground economy, a new threat has emerged, and it is known as WormGPT. This AI-powered tool is offered as a paid service on the dark web, providing attackers with automated hacking capabilities.
WormGPT is designed to mimic the behavior of a human hacker, autonomously scanning systems, identifying vulnerabilities, and launching attacks. Its AI capabilities enable it to adapt and evolve its tactics, making detecting and defending against it even more challenging. This tool is a stark reminder of the evolving nature of social engineering attacks and the need to enhance cybersecurity measures continuously.
The Social-Engineer Toolkit (SET)
While the emergence of AI in social engineering attacks raises concerns, ethical hackers and penetration testers can also leverage AI-driven tools to enhance their defensive strategies. One such tool is the Social-Engineer Toolkit (SET) within Kali Linux. With its AI capabilities, the SET empowers security professionals to simulate sophisticated social engineering attacks and identify vulnerabilities within an organization’s defenses.
The SET offers a wide range of features, including email spoofing, spear-phishing attacks, and website cloning, enabling testers to evaluate the effectiveness of an organization’s security awareness and prevention measures. By embracing AI-driven tools like the SET, organizations can better understand their vulnerabilities and take proactive steps to strengthen their cybersecurity defenses.
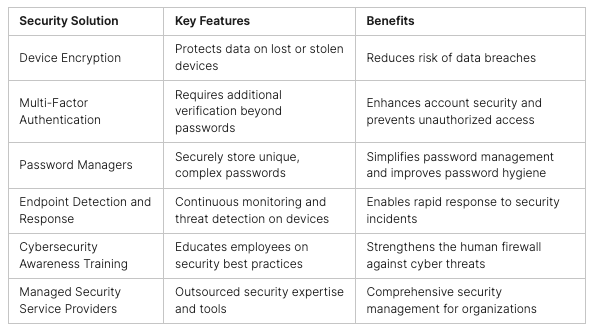
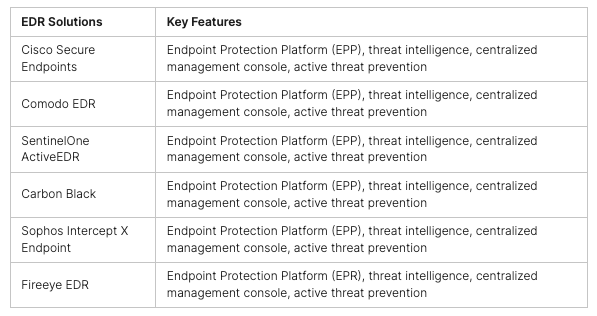
Prevention Measures
Mitigating the risks associated with advanced social engineering attacks requires a comprehensive approach that combines technical solutions, employee awareness, and stringent prevention measures. Organizations should focus on implementing advanced email filters to detect and block AI-enhanced phishing attempts.
Investing in AI-driven cybersecurity solutions can provide organizations with improved threat intelligence, enabling swift identification and response to emerging social engineering tactics. Regular security awareness and training programs are essential to educate employees about the evolving nature of social engineering attacks and equip them with the knowledge to identify and report potential threats.
By staying vigilant, leveraging advanced prevention measures, and keeping pace with the rapidly evolving social engineering landscape, organizations can enhance their cybersecurity posture and protect themselves against the growing threat of AI-enhanced phishing attacks. Taking a proactive approach to security and embracing AI technology as a defensive tool is crucial in the ongoing fight against social engineering threats.
Conclusion
In today’s digital era, where cyber threats loom larger and more sophisticated than ever, pentesting emerges as a cornerstone practice for preemptive cybersecurity. This critical exercise empowers organizations to uncover and remediate vulnerabilities before they become gateways for malicious actors. Through meticulous evaluation of computer systems, networks, and web applications, pentesting significantly bolsters an organization’s cyber defenses and enhances its security stance.
Delving deeper, specialized domains such as physical and cyber penetration testing amplify the breadth and depth of proactive cybersecurity efforts. These nuanced approaches enable organizations to fortify not only their digital landscapes but also their physical perimeters, thereby securing their essential assets against a spectrum of potential threats.
As attackers increasingly leverage artificial intelligence to sophisticate their social engineering schemes, the imperative for organizations to stay alert and proactive skyrockets. The adoption of cutting-edge security solutions, along with the implementation of exhaustive awareness and training initiatives, is vital for cultivating a pervasive culture of cybersecurity awareness among staff. These measures are instrumental in navigating the complexities of modern cyber threats.
Adopting pentesting as a proactive defense strategy, coupled with a vigilant stance against social engineering tactics, positions organizations to significantly enhance their security frameworks. This forward-looking approach, underpinned by ethical hacking methodologies, equips organizations with the readiness to protect their invaluable data and maintain their reputational integrity amidst the evolving cyber threat landscape.
Peris.ai Cybersecurity introduces Peris.ai Pandava, a service designed with the philosophy that your organization’s security and competitive edge in the market are paramount. Sleep peacefully, knowing that our team of ethical hackers is diligently conducting penetration tests, reminiscent of a “Mission Impossible” scenario, to identify vulnerabilities within your digital and physical infrastructures. With Peris.ai Pandava, the daunting task of securing your digital platform becomes a manageable and reassuring endeavor.
We invite you to explore how Peris.ai Pandava can transform your organization’s approach to cybersecurity. Visit Peris.ai Cybersecurity to learn more about our penetration testing services and how we can help you navigate the complexities of safeguarding your digital and physical assets against the ever-evolving cyber threats. Secure your peace of mind and give your business the protective edge it deserves with Peris.ai Pandava.
FAQ
What is pentesting?
Pentesting, also known as penetration testing, is the practice of rigorously scrutinizing computer systems, networks, and web applications to identify and expose vulnerabilities that attackers could exploit.
Why is pentesting important?
Pentesting plays a vital role in defending against constantly evolving cyber threats. It helps organizations proactively test and reinforce the security of their digital infrastructures, making their defenses stronger and more resilient.
What is the career path of a pentester?
Aspiring pentesters need to develop a strong foundation in IT fundamentals and progressively specialize in security pen and cyber penetration testing. Gaining experience in roles such as network security analyst or IT security consultant can pave the way for advancement.
What are the technicalities of pentesting?
Pentesting involves various techniques, including social engineering, technical system hacking, and network sniffing. These techniques serve the purpose of uncovering different types of vulnerabilities and simulating cyber-attacks to assess the effectiveness of security measures.
What are the specialized areas in pentesting?
Specialized areas in pentesting include physical penetration testing, which assesses and breaches physical barriers, and cyber penetration testing, which safeguards digital assets against a wide range of cyber threats. Intrusion testing focuses explicitly on ethical hacking and simulating attacks on various application systems to identify vulnerabilities.
What is social engineering in cybersecurity?
Social engineering is an insidious tactic employed by attackers to exploit psychological vulnerabilities and manipulate individuals into providing sensitive information or performing actions that compromise cybersecurity.
What are the advanced social engineering tools and tactics?
With the rapid advancement of AI technology, social engineering attacks have become more sophisticated. Attackers are integrating AI in phishing campaigns and leveraging tools like the Social-Engineer Toolkit (SET) within Kali Linux. Organizations must implement advanced email filters, AI cybersecurity solutions, and comprehensive awareness and training programs to mitigate the risks associated with advanced social engineering attacks.
Why is proactive cybersecurity essential?
Proactive cybersecurity practices, such as pentesting, are crucial in identifying and addressing vulnerabilities before attackers can exploit them. Organizations can optimize their security posture and protect their digital assets by constantly fortifying cyber defenses and staying one step ahead of evolving threats.