In the ever-expanding battlefield of cybersecurity, the spotlight often falls on firewalls, encryption, and zero-day exploits. Yet, the vast majority of successful cyberattacks don’t start with brute force or nation-state toolkits. They begin with something far more mundane: a human mistake.
Employees click phishing links, reuse passwords, mishandle sensitive data, and sometimes unintentionally open the door to attackers. It’s a painful truth: your people can be your greatest strength or your weakest link.
But the answer isn’t to blame employees. It’s to empower them, monitor intelligently, and design your defenses to detect, contain, and respond to human-driven incidents. That’s the role of the Blue Team.
This article unpacks the real pain points organizations face when human error becomes the gateway for breaches. It explains the role of Blue Team services in hardening your people, processes, and technology. And it shows how Peris.ai’s Blue Team capabilities provide a comprehensive defense strategy that transforms employees from liabilities into allies.
Pain Points: When Employees Unwittingly Invite the Attack
1. Phishing and Social Engineering
Phishing remains a leading initial attack vector across industries. According to the 2025 Verizon Data Breach Investigations Report (DBIR), approximately 60% of breaches involved a human element, including errors and social engineering attacks .(Mimecast)
Spear-phishing emails often impersonate executives, mimic vendors, or use fake security alerts. Even trained employees can be fooled by highly targeted lures.
2. Credential Misuse and Weak Passwords
Users often reuse passwords across personal and professional accounts. A major cybersecurity incident revealed that over 19 billion real passwords were leaked online between April 2024 and April 2025, with a vast majority—94%—being reused across multiple accounts .(New York Post)
Even with MFA, session hijacking and credential stuffing remain serious threats.
3. Data Handling Errors
From misconfigured Google Drive links to emailing unencrypted spreadsheets, employees frequently mishandle sensitive data. These errors lead to compliance violations, regulatory fines, and reputational damage.
4. Shadow IT and Unauthorized Tools
Employees often install unapproved software, use unsanctioned cloud services, or bypass controls to “get the job done.” These systems often lack monitoring, patching, or proper access controls.
5. Insider Threats
While rare, some employees knowingly steal data, sabotage systems, or aid external attackers. More commonly, negligence—not malice—creates insider risk. According to Cybersecurity Insiders’ 2024 Insider Threat Report, 83% of organizations reported at least one insider attack in the last year .(IBM)
Case Examples: Real Damage from Human Mistakes
- Healthcare breach caused by an employee falling for a phishing email requesting login credentials to access scheduling software. Result: ransomware encrypted critical systems for 3 days.
- Manufacturing incident where a VPN password was reused from a previous LinkedIn breach. The attacker gained network access and exfiltrated proprietary designs.
- Finance firm suffered a data leak when a junior analyst shared an internal spreadsheet with a third-party via Google Docs, forgetting to restrict access.
Why Technology Alone Isn’t Enough
Even the most advanced tools can’t fully mitigate human risk without proper strategy. Consider:
- Email filters miss zero-day phishing payloads.
- MFA doesn’t stop users from entering credentials on fake portals.
- DLP solutions can’t judge business context for every shared file.
- SIEM alerts require context to detect social engineering patterns.
What’s needed is a human-aware defense layer. One that combines training, simulation, detection, and response. That’s where the Blue Team steps in.
Blue Team Services: Your Human-Centric Defense
The Blue Team focuses on proactive defense: monitoring, detection, response, and improvement. Unlike red teams that simulate attackers, blue teams operate inside the network to defend in real-time.
At Peris.ai, our Blue Team services are designed to:
- Reduce risk from human error
- Detect early indicators of compromise
- Contain and respond to incidents quickly
- Build organizational cyber resilience
Core Blue Team Capabilities
1. Phishing Simulation & Awareness Training
- Realistic phishing campaigns targeting specific roles and departments
- Behavioral analytics to track who clicked, reported, or ignored
- Adaptive training modules based on user performance
2. Endpoint Detection & Response (EDR)
- Continuous monitoring for signs of compromise
- Behavioral analysis to detect anomalous activity (e.g., odd login times, lateral movement)
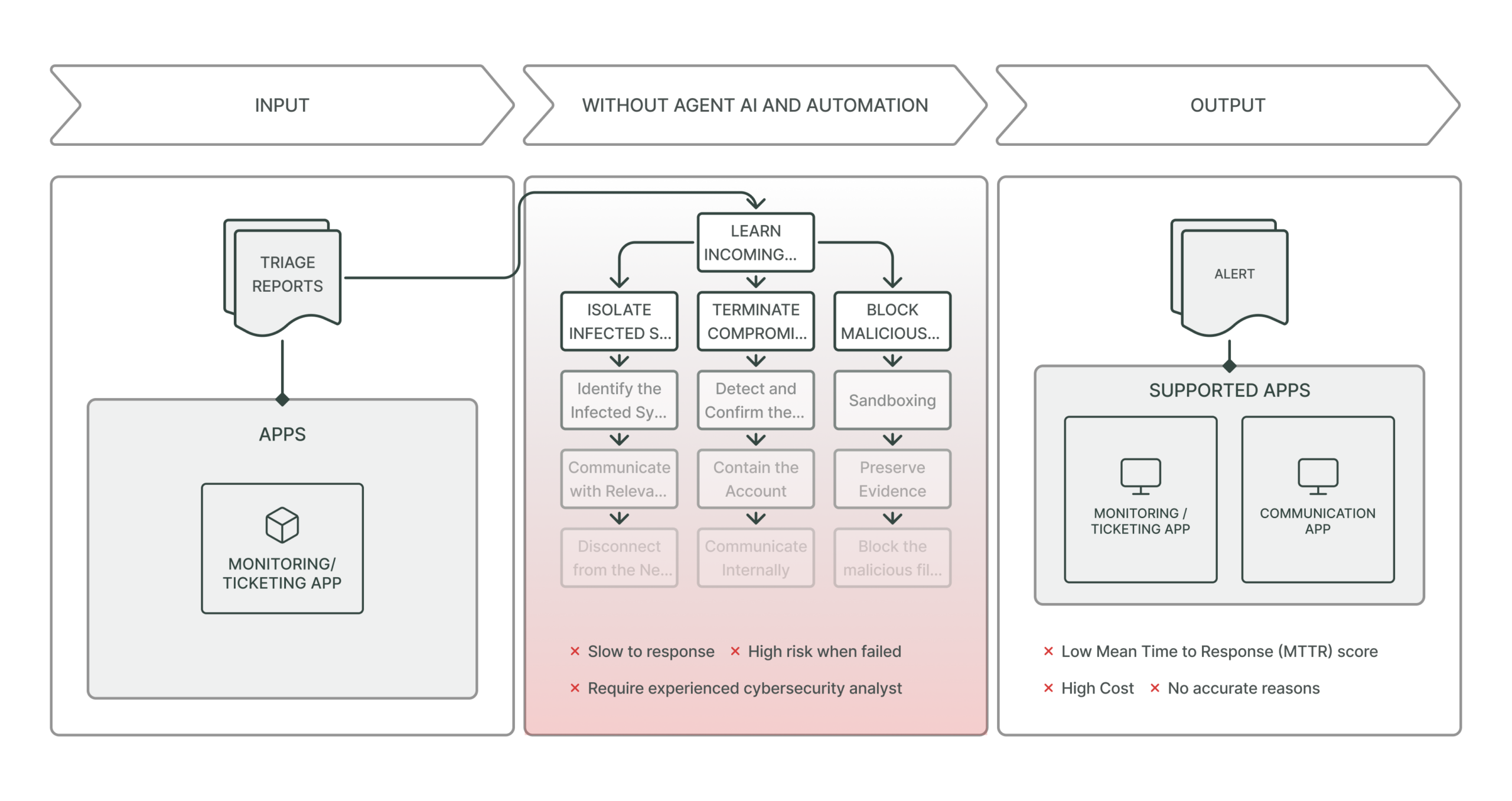
- Rapid containment actions like isolating infected hosts
3. Insider Threat Monitoring
- Baseline analysis of user behavior across email, files, and access patterns
- Detection of anomalies like large file transfers, login irregularities, or privilege escalations
- Integration with HR and access management for joint investigations
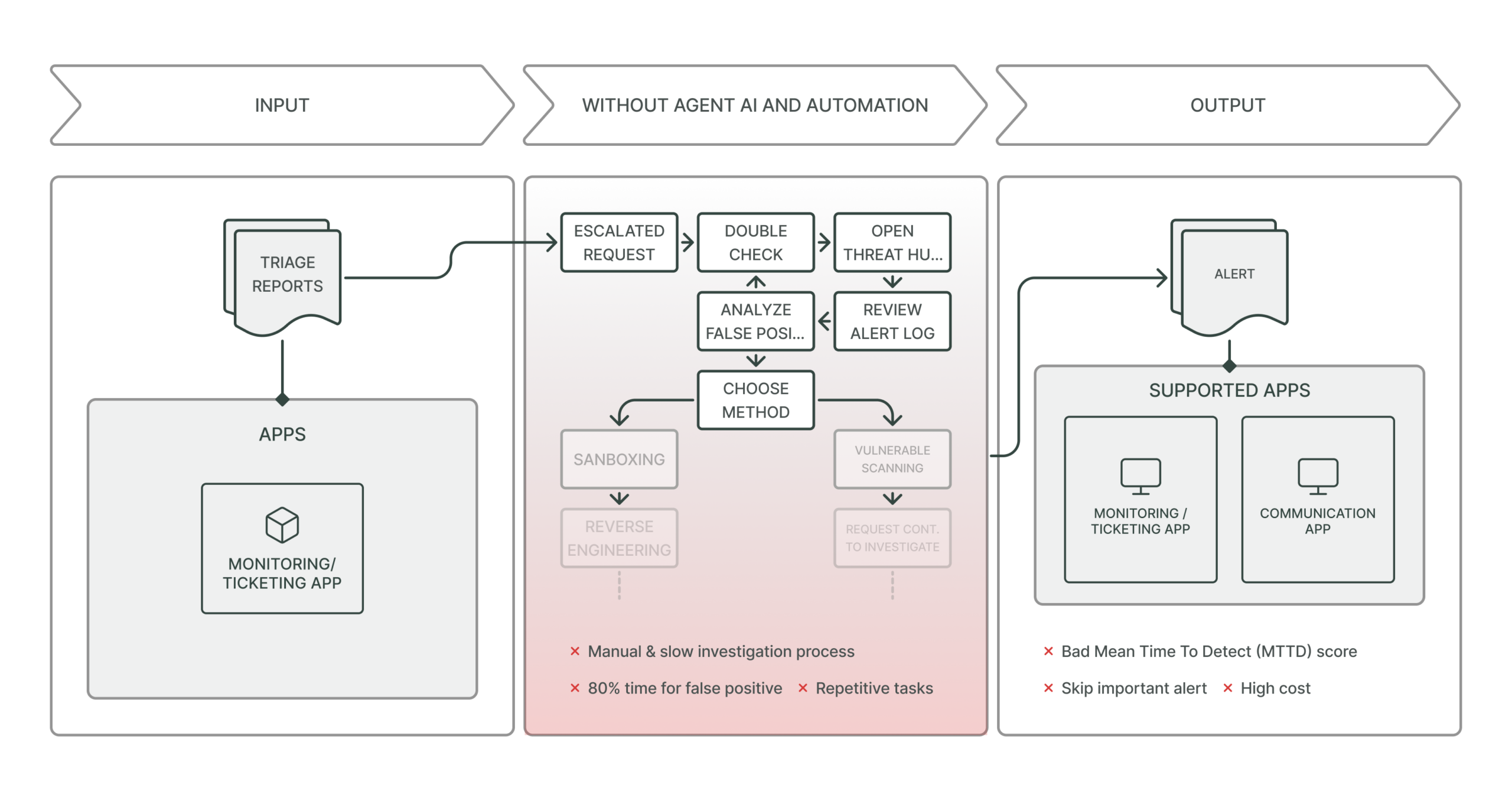
4. Threat Hunting
- Proactive search for indicators of compromise and attacker footholds
- Use of threat intelligence to identify trending social engineering campaigns
- Daily, weekly, or continuous hunts depending on organizational maturity
5. SIEM and Log Correlation
- Centralized analysis of user events across endpoints, network, and cloud
- Correlation with CTI (Cyber Threat Intelligence) to flag suspicious user behavior
- Alert prioritization and contextual enrichment for human-driven threats
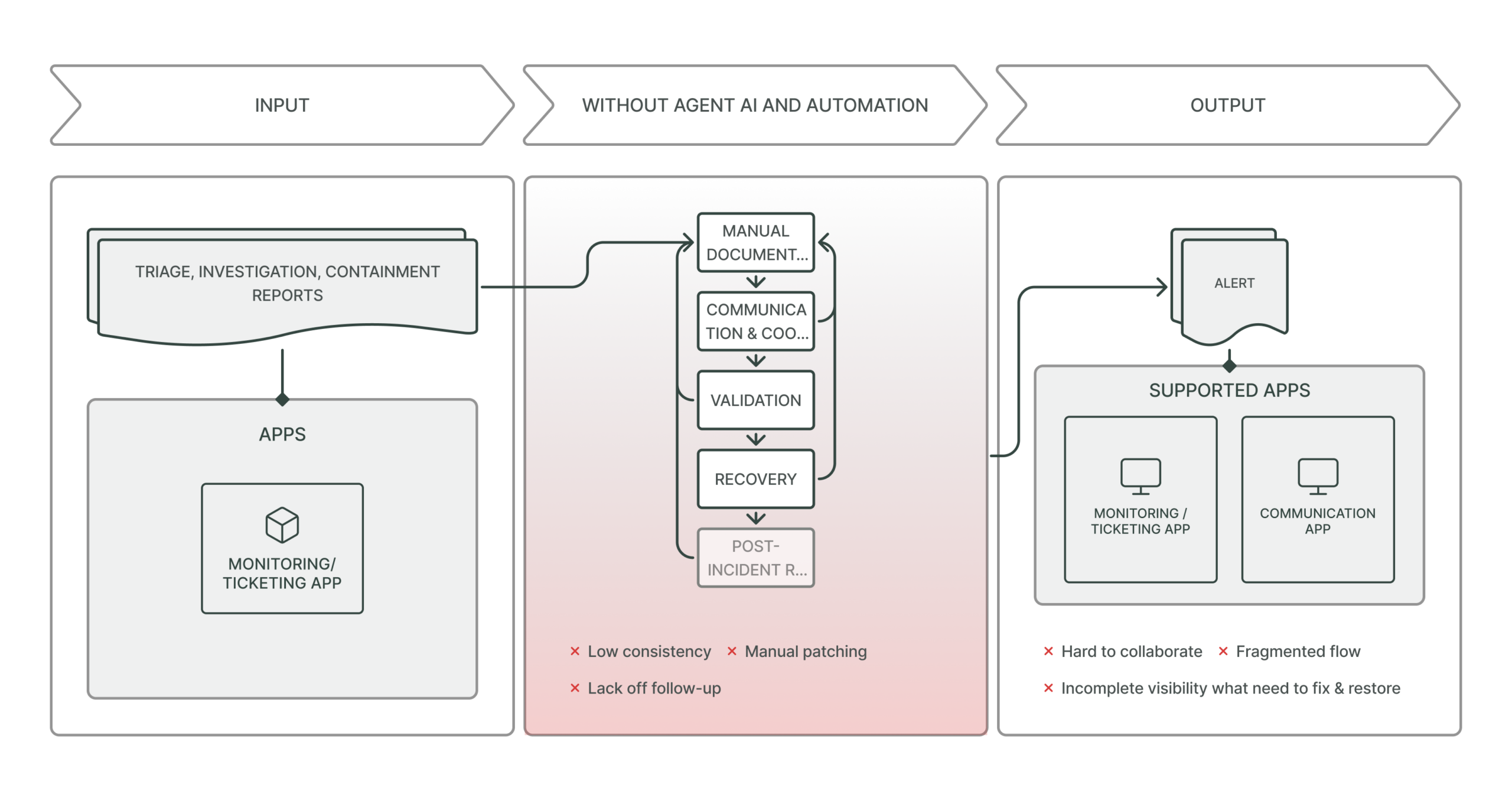
6. Incident Response and Recovery
- Rapid triage of suspected human-driven incidents
- Root cause analysis to determine if user error led to the compromise
- Remediation plans including containment, communication, and patching
How Peris.ai Blue Team Services Transform Human Risk into Resilience
Rather than treating users as the problem, Peris.ai builds a program that treats them as partners in defense. Here’s how:
Real-Time Behavioral Insight
Peris.ai integrates behavioral analytics into EDR and SIEM to understand normal vs. abnormal user activity. When an employee clicks a malicious link, we can:
- Detect the initial event
- Trace follow-up actions (downloads, process launches)
- Automatically isolate the device or disable credentials if needed
Phishing Resilience Program
Using dynamic simulation tools, we mimic real-world phishing attacks tailored to your:
- Business language
- Employee roles
- Local trends
This provides better data than generic awareness training and allows us to benchmark and improve user resilience over time.
Threat Detection + Human Context
By fusing CTI and UEBA (User and Entity Behavior Analytics), we detect:
- Business email compromise (BEC) attempts
- Credential abuse from reused or breached passwords
- Insider misuse patterns (e.g., exfiltrating files before resignation)
Response and Education Cycle
After an incident, we run a loop:
- Technical investigation and containment
- User interview to determine root cause
- Targeted training and system hardening
This ensures both technical and human remediation.
Complementing Red Team and SOC
While Red Team operations simulate attack paths, and SOCs monitor alerts, the Blue Team:
- Bridges simulation with real defense
- Focuses on the gray zone of user behavior
- Drives continuous improvement across the cyber defense lifecycle
With Peris.ai, Blue Team services operate in harmony with your:
- Existing detection platforms
- Incident response workflows
- Awareness programs
Getting Started: Building a Human-Centric Defense
- Assess Your Human Risk: Conduct phishing tests, password audits, and behavioral baselining
- Deploy Blue Team Services in Phases: Start with simulation and detection; expand to full threat hunting and IR
- Integrate with CTI and SOC: Feed human-risk insights into your broader defense ecosystem
- Report, Improve, Repeat: Measure outcomes, refine training, improve response
Conclusion: Empower Your Employees, Don’t Just Blame Them
Security failures due to human error are not a flaw in your people—they’re a flaw in your system. Blaming users leads to fear and non-reporting. Empowering them builds resilience.
Peris.ai’s Blue Team services are built on the idea that humans are not the weakest link when supported with the right tools, insight, and training.
With intelligent monitoring, realistic simulations, rapid response, and ongoing education, you can turn your people into a distributed human firewall that strengthens your cybersecurity posture.
When employees are your weakest link, Blue Team is your strongest answer.
Start building human-aware cyber defense at https://peris.ai