Cybercrime is no longer a distant threat; it is a present and rapidly escalating reality. Every sector—from finance to healthcare to government—is now a target. Cyberattacks have evolved from simple malware infections into highly sophisticated, multi-vector campaigns causing massive financial, operational, and reputational damage.
Yet, despite increased cybersecurity spending, organizations continue to suffer costly breaches, ransomware attacks, insider threats, supply chain compromises, and regulatory penalties.
This article delves deep into the true corporate cost of cybercrime, highlights the vulnerabilities companies face, and explains how Peris.ai Cybersecurity’s integrated, AI-driven approach empowers organizations to fight back and build resilient defenses.
The Rising Financial Cost of Cybercrime
According to Cybersecurity Ventures, the global cost of cybercrime is projected to reach $10.5 trillion annually by 2025—up from $3 trillion in 2015. For corporations, the impact is felt across multiple dimensions:
1. Direct Financial Loss
- Ransomware payments
- Fraudulent fund transfers
- Intellectual property theft
2. Business Disruption
- Downtime and lost productivity
- Supply chain interruptions
- Delayed service delivery
3. Regulatory and Legal Penalties
- Non-compliance fines (GDPR, HIPAA, PCI DSS)
- Class action lawsuits
- Breach notification costs
4. Reputational Damage
- Loss of customer trust
- Stock price declines
- Brand degradation and market erosion
5. Long-Term Recovery Costs
- Incident response consulting and post-breach investigations
- System rebuilds and infrastructure upgrades
- Increased insurance premiums and reduced coverage terms
Insight: These financial impacts are often cumulative, meaning the total cost can multiply over months or even years after the initial breach.
Pain Points: Why Organizations Struggle Against Cybercrime
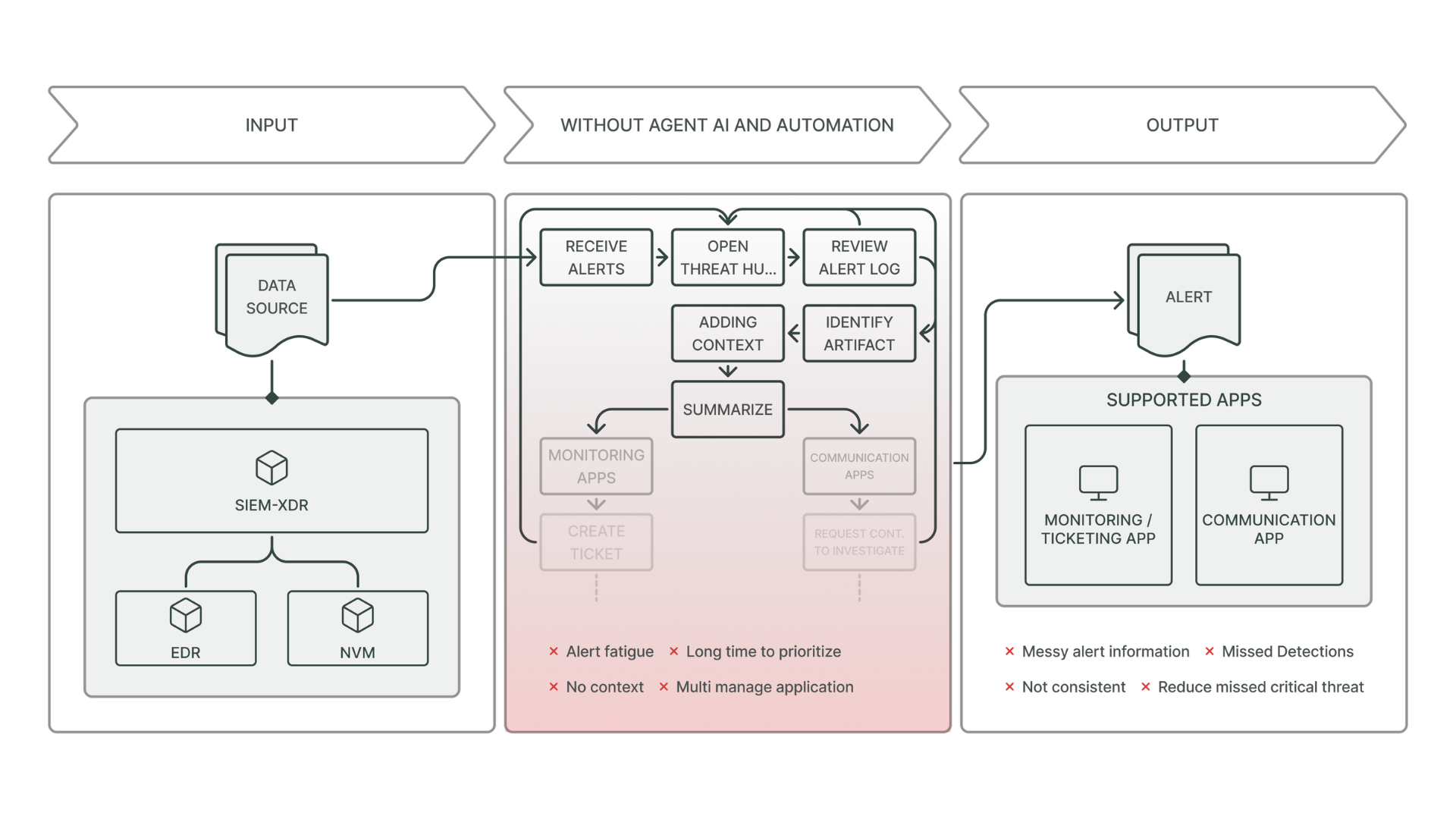
1. Fragmented Security Posture
Organizations often deploy dozens of cybersecurity tools that operate in silos, resulting in alert fatigue, visibility gaps, inefficient workflows, and missed threats.
2. Lack of Real-Time Visibility
You cannot protect what you cannot see. Shadow IT, cloud misconfigurations, undocumented APIs, and unmanaged third-party access often go undetected, leaving critical vulnerabilities exposed.
3. Resource Constraints
The global shortage of skilled cybersecurity professionals leaves security teams overwhelmed, stretched thin, and unable to maintain proactive defense at scale.
4. Slow Detection and Response
The average time to detect a breach remains over 200 days in many industries. During this dwell time, attackers can escalate privileges, pivot laterally across networks, and exfiltrate sensitive data unnoticed.
5. Third-Party and Supply Chain Risk
Organizations increasingly rely on third-party services and vendors—each representing a potential backdoor for attackers to exploit, bypassing traditional perimeter defenses.
Sector-Specific Impacts of Cybercrime
Finance
- Online banking fraud and credential stuffing attacks
- Compliance violations under regulations
- Growing exposure from third-party fintech providers
Healthcare
- Ransomware attacks locking critical Electronic Medical Records (EMR)
- HIPAA violations stemming from data breaches
- Vulnerabilities in connected medical devices
Retail & E-commerce
- Payment card data theft and Magecart attacks
- Account takeover (ATO) attacks through credential leaks
- Fraud targeting loyalty programs and rewards platforms
Government
- Nation-state espionage and cyber warfare operations
- Citizen data breaches through vulnerable portals
- Disruption of critical public infrastructure and services
Education
- Phishing attacks against students and faculty accounts
- Theft of sensitive research or intellectual property
- Attacks disrupting online learning platforms and systems
Hidden Costs of Cybercrime: Beyond the Obvious
While direct financial losses are highly visible, hidden costs often have a more enduring and corrosive impact:
- Customer Churn: Post-breach, trust is hard to regain; many customers leave permanently.
- Recruitment Challenges: Organizations with high-profile breaches struggle to attract top talent.
- Operational Drag: Increased audit requirements, compliance reporting, and cybersecurity insurance demands.
- Strategic Delays: Innovation projects and digital transformation initiatives are often paused or scaled back after breaches.
Insight: Hidden costs can silently undermine competitiveness for years after a breach.
How Peris.ai Helps Organizations Fight Back
Peris.ai offers a holistic, AI-driven cybersecurity platform, combining automation, deep threat intelligence, hyperautomation, and human expertise into a seamless defense ecosystem.
Brahma Fusion: Agentic-AI Hyperautomation for Cyber Defense
- Playbook-Driven Automation: Recreates analyst workflows for faster threat detection and response
- Agentic Decision-Making: Emulates experienced human reasoning to triage, prioritize, and act
- Cross-Stack Integration: Seamlessly connects EDR, SIEM, NVM, cloud security, ticketing, and case management tools
- Real-Time Orchestration: Automates containment, remediation, and documentation within minutes, not days
Brahma IRP: Unified Incident Response Platform
- Endpoint, Network, and Extended Detection: Holistic telemetry across infrastructure
- Built-In Digital Forensics: Rapid evidence preservation, chain-of-custody management, and root cause analysis
- Advanced Correlation Engine: Connects seemingly isolated events to reveal hidden attack paths
INDRA: Cyber Threat Intelligence (CTI) Engine
- Global Threat Feeds: Monitors dark web forums, malware campaigns, and APT activities
- Contextual Enrichment: Adds threat actor motivations, TTPs (Tactics, Techniques, and Procedures) to alerts
- Actionable Intelligence: Provides proactive detection indicators and hunting guides
BimaRed: Attack Surface Management (ASM)
- Continuous Asset Discovery: Maps all digital assets—known and unknown—across cloud, SaaS, IoT, and legacy environments
- Prioritized Risk Views: Highlights exposures based on real-world attack likelihood
- Shadow IT and Rogue Device Detection: Secures blind spots created by business units or partners
Pandava: Penetration Testing Platform
- Continuous Security Validation: Simulates active attacker behavior to uncover vulnerabilities
- Remediation Playbooks: Guides technical teams on closing high-risk gaps
- Retesting Workflows: Confirms the effectiveness of mitigation efforts through repeat validation
Korava: Bug Bounty Management
- Ethical Hacker Crowdsourcing: Expands vulnerability detection beyond internal resources
- Streamlined Submission Evaluation: Prioritizes critical findings quickly and efficiently
- Reward Management: Engages the cybersecurity community while controlling costs
Best Practices for Fighting Cybercrime
- Adopt Continuous Monitoring: Static defenses are outdated; threats evolve daily.
- Automate Wherever Possible: Free human analysts for strategic decision-making.
- Invest in Threat Intelligence: Know your adversaries, anticipate their tactics.
- Validate Defenses Regularly: Test your systems with ethical hacking and penetration testing.
- Foster a Security-First Culture: Train every employee to be part of your cyber defense perimeter.
The Strategic Value of Partnering with Peris.ai
Partnering with Peris.ai means:
- Achieving enterprise-grade cybersecurity through an integrated single-pane-of-glass platform
- Empowering small teams to defend at massive scale
- Adopting modular, AI-driven capabilities designed to evolve with future threats
- Turning cybersecurity from a cost center into a business enabler and competitive advantage
Conclusion: Cybercrime Is Inevitable—Impact Isn’t
Cyberattacks will continue to evolve, becoming faster, stealthier, and more damaging. No organization is immune. However, the scale of the damage is not predetermined.
With proactive monitoring, real-time response, continuous validation, and intelligent automation, the balance of power can shift in your favor.
Peris.ai equips organizations with not just visibility, but active defense, resilience, and foresight—building cybersecurity ecosystems prepared for tomorrow’s threats.
Cybercrime is costly. Resilience is priceless.
Learn how to fortify your organization with Peris.ai: https://peris.ai/