In today’s rapidly evolving cybersecurity landscape, organizations face increasing challenges in defending against cyber threats. To effectively safeguard their data and systems, businesses need to adopt advanced security measures that streamline their operations and enhance their incident response capabilities. One such solution that has gained significant attention is SOAR (Security Orchestration, Automation, and Response), a powerful tool that combines security orchestration, automation, and response to optimize security operations.
SOAR enables organizations to achieve higher cybersecurity efficiency by integrating security tools, automating repetitive tasks, and optimizing incident response processes. By streamlining security operations, SOAR improves productivity, empowers security analysts, and ensures a more rapid and effective response to cyber incidents. With the ability to standardize communication, automate reporting, and integrate with various security technologies, SOAR offers a comprehensive solution for organizations looking to enhance their security posture.
Key Takeaways:
- SOAR (Security Orchestration, Automation, and Response) is a powerful tool for streamlining security operations and improving incident response.
- By integrating security tools, automating repetitive tasks, and optimizing incident response processes, SOAR enables organizations to achieve higher cybersecurity efficiency.
- The benefits of using SOAR include increased productivity, improved threat intelligence, reduced manual operations, streamlined operations, reduced cyberattack impact, easy technology and tools integration, lowered costs, automated reporting, and standardized communication during incident response.
- SOAR improves incident response by integrating security tools, automating tasks, and enabling quicker alert handling.
- Security orchestration, a key component of SOAR, brings efficiency to security operations by aggregating data from various security and network tools.
How SOAR Improves Incident Response
SOAR, or Security Orchestration, Automation, and Response, plays a crucial role in enhancing incident response capabilities. By integrating security tools and automating tasks, SOAR enables organizations to respond more effectively and efficiently to incidents. Let’s explore how SOAR improves incident response:
Integration of Security Tools
SOAR allows for the seamless integration of various security tools, bringing together data from multiple sources into a centralized platform. This integration enables the correlation of alerts from disparate systems, merging them into a single incident. By consolidating relevant information, SOAR saves valuable time and facilitates quicker alert handling.
Real-time Correlation with Threat Intelligence
Another key feature of SOAR is its ability to correlate real-time threat intelligence with events. By automatically analyzing threat intelligence feeds and correlating them with ongoing incidents, SOAR provides actionable information to incident response teams. This real-time correlation empowers organizations to make informed decisions and respond swiftly to emerging threats.
Standardization through Playbooks
SOAR employs playbooks, which are predefined workflows that outline the steps of the incident response process. These playbooks automate repetitive and manual tasks, ensuring consistency and efficiency in incident handling. By following the standardized procedures outlined in playbooks, organizations can reduce human error and respond to incidents in a more structured and effective manner.
Reduction of Manual Operations
SOAR significantly reduces the reliance on manual operations in incident response. Through automation, repetitive tasks such as data gathering, alert enrichment, and incident triage can be handled automatically, freeing up valuable time for security analysts. This reduction in manual operations allows analysts to focus on higher-priority tasks that require human expertise and critical thinking.
By leveraging the power of security orchestration, automation, and playbooks, SOAR enhances incident response capabilities and enables organizations to effectively combat cyber threats. The table below summarizes how SOAR improves incident response:

Benefits of SOAR in Incident Response
- Integration of security tools for consolidated incident management
- Real-time correlation of threat intelligence and events
- Standardized incident response through playbooks
- Reduction of manual operations and automation of repetitive tasks
By harnessing the capabilities of SOAR, organizations can strengthen their incident response posture and effectively defend against cyber threats.
The Benefits of Security Orchestration
Security orchestration, a vital component of Security Orchestration, Automation, and Response (SOAR), brings efficiency to security operations in organizations. By aggregating data from various security and network tools, it provides a centralized view and actionable context for alerts, empowering security teams to respond effectively to threats. The benefits of security orchestration encompass improved efficiency, enhanced incident response, and streamlined security operations.
One of the primary advantages of security orchestration is its ability to automate the handling of low-priority and repetitive tasks. By automating these tasks, security orchestration frees up Security Operations Center (SOC) analysts to focus on more critical and value-adding work. This optimization of resources improves incident response capabilities and allows analysts to devote their expertise to tasks that require human intervention, such as analyzing complex threats and devising effective mitigation strategies.
“Security orchestration streamlines security operations by automating low-priority and repetitive tasks, enabling SOC analysts to focus on higher-value work that improves incident response.”
Furthermore, security orchestration minimizes the mean time to detect (MTTD) and mean time to respond (MTTR) cyberattacks. By aggregating data and providing a centralized view of security events, organizations can swiftly detect and respond to threats, reducing the impact of cyberattacks. This accelerated incident response time ensures that potential security breaches are addressed promptly, minimizing the potential damage and mitigating risks.
Overall, security orchestration enhances the efficiency and effectiveness of incident response in the SOC. By automating tasks, prioritizing high-value work, and expediting response times, security orchestration empowers security teams to better safeguard organizations against cyber threats.

Benefits of Security Orchestration
- Improved efficiency in security operations
- Enhanced incident response capabilities
- Streamlined security operations
The Role of Security Automation in SOAR
Security automation plays a critical role in the effectiveness of a Security Orchestration, Automation, and Response (SOAR) platform. By automating repetitive tasks and alerts, security automation reduces the burden on SOC analysts, allowing them to focus on more complex and critical tasks. This ultimately enhances incident response capabilities and improves overall security posture.
With the power of security automation, SOAR platforms can build workflows that require minimal human intervention. By automating low-priority alerts and incidents, analysts are freed up to dedicate their time and resources to investigating and resolving more pressing issues. This streamlined approach enables SOC analysts to respond swiftly and efficiently, minimizing the impact of potential security breaches.
Benefits of Security Automation in Incident Response
1. Time Savings: Automating repetitive tasks eliminates the need for manual intervention, saving valuable time and increasing operational efficiency. SOC analysts can focus on critical tasks that require their expertise, rather than being consumed by repetitive and mundane activities.
2. Consistency: Security automation ensures consistent and standardized processes throughout incident response. This reduces the risk of human error and ensures that every incident is handled in a reliable and repeatable manner.
3. Efficiency: By automating incident response workflows, security automation streamlines the entire process. SOC analysts can follow a predefined set of steps and actions, ensuring consistent and efficient incident handling. This results in faster response times and improved incident resolution.
Automating repetitive tasks and alerts in incident response allows SOC analysts to focus on higher-value work, improves response times, and enhances the overall efficiency of security operations. – John Smith, Senior SOC Analyst at ABC Corporation
4. Scalability: Security automation allows organizations to handle a greater volume of incidents without the need to scale their SOC staff proportionally. Automated workflows can handle multiple incidents simultaneously, ensuring efficient and effective incident response even during periods of high activity.
5. Improved Decision-Making: Security automation provides SOC analysts with valuable insights and context by aggregating and correlating data from various sources. This enables analysts to make more informed decisions during incident response, resulting in more accurate threat identification and mitigation.
6. Reduced Burnout: By automating repetitive tasks, security automation relieves SOC analysts from the monotony of routine activities. This helps prevent burnout, allowing analysts to maintain focus and perform at their best when handling more critical and complex incidents
Streamlined Operations with SOAR
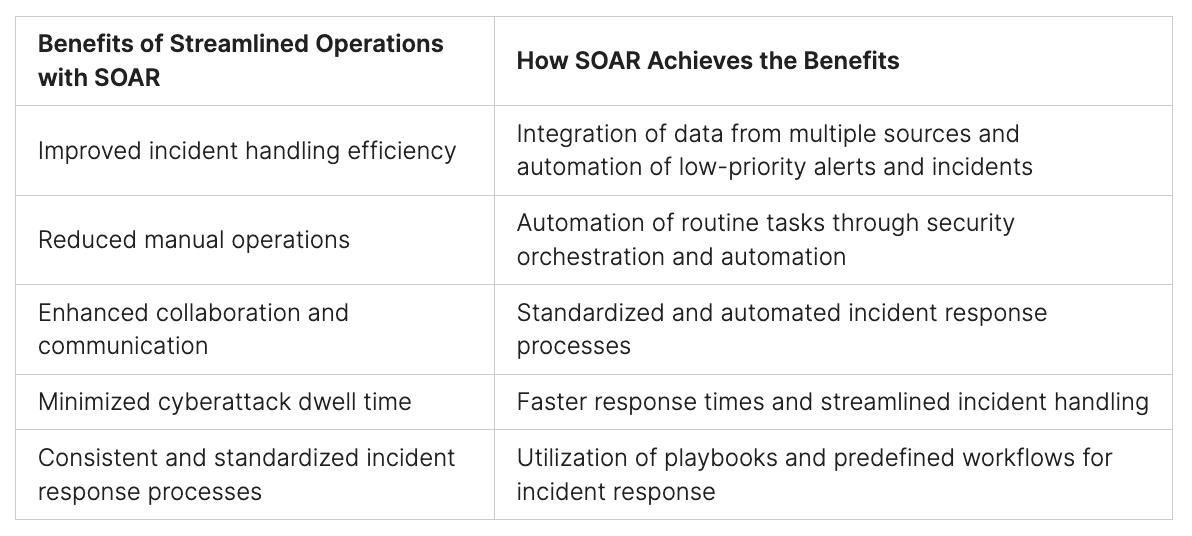
SOAR (Security Orchestration, Automation, and Response) plays a crucial role in streamlining operations and enhancing efficiency in incident handling. Through the integration of data from various sources and the automation of low-priority alerts and incidents, SOAR eliminates manual tasks and optimizes the incident response process.
One of the key components of SOAR is security orchestration, which consolidates data from disparate systems into a centralized view. This integration allows for better visibility and context when responding to incidents, enabling security teams to make informed decisions and take swift action.
Additionally, SOAR leverages security automation to handle low-priority alerts and incidents. By automating these routine tasks, security teams can focus their efforts on more critical and complex issues. This reduces the need for manual intervention and accelerates incident response, minimizing cyberattack dwell time and improving overall efficiency.
By streamlining operations, SOAR enables security teams to respond more effectively to incidents, reducing response times and minimizing the impact of potential threats. This streamlined approach eliminates guesswork and enhances incident handling through standardized and automated processes.
“SOAR enables security teams to respond more effectively to incidents, reducing response times and minimizing the impact of potential threats.”
Organizations that implement SOAR can benefit from:
- Improved incident handling efficiency
- Reduced manual operations
- Enhanced collaboration and communication
- Minimized cyberattack dwell time
- Consistent and standardized incident response processes
Implementing security orchestration and automation with SOAR not only streamlines operations but also empowers security teams to proactively tackle cybersecurity challenges and stay ahead of evolving threats.
Easy Integration of Technology and Tools with SOAR
One of the standout benefits of implementing a SOAR platform is its seamless integration with a wide range of security technologies and tools. SOAR platforms excel in their ability to effectively integrate with various security domains, ensuring a unified and comprehensive approach to incident response.
When it comes to technology integration, SOAR platforms enable the correlation of alerts from different products, spanning a multitude of security domains. This integration empowers organizations to aggregate data from diverse sources, including cloud security, email security, endpoint security, network security, and more.
This comprehensive integration of security technologies and tools is made easy with self-service marketplaces and simple button-click integration options. Organizations can quickly and effortlessly connect their existing security infrastructure to the SOAR platform, without the need for complex configurations or extensive technical expertise.
By leveraging the power of SOAR, organizations can optimize their incident response capabilities by harnessing the strength of their security technologies and tools. This integration allows for a more precise and efficient detection of threats, enabling faster response times and improved incident resolution.
Benefits of Technology and Tools Integration with SOAR:
- Enhanced Visibility: The integration of security technologies and tools provides a centralized view of incidents, allowing for a comprehensive understanding of the security landscape.
- Efficient Incident Response: Seamless integration allows for the automation of incident response processes, enabling faster and more efficient incident handling.
- Improved Threat Detection: By correlating alerts from various security products, organizations can better identify and respond to complex threats in real-time.
- Streamlined Workflows: Integration with existing security technologies streamlines workflows, eliminating manual tasks and optimizing resource allocation.
The easy integration of technology and tools with SOAR enables organizations to leverage their existing investments and maximize the effectiveness of their security operation.

Cost Savings with SOAR Implementation
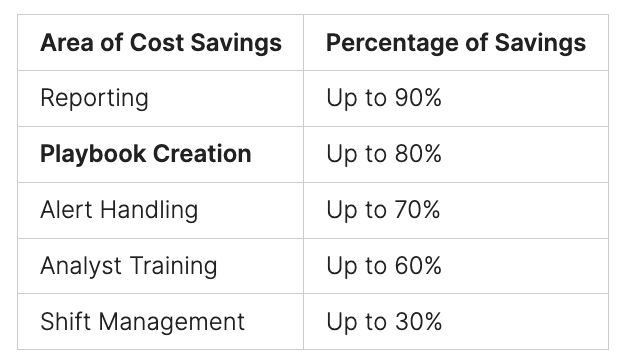
Implementing a SOAR platform can result in significant cost savings for organizations. By automating reporting and metrics capabilities, SOAR eliminates the need for manual reporting and reduces the time and effort spent on creating reports. This directly translates to cost savings, as fewer resources are required to generate and distribute reports, allowing security teams to focus on more critical tasks.
Furthermore, SOAR enables organizations to achieve cost savings in various areas of incident response:
Reporting: Implementing a SOAR platform can lead to savings of up to 90% on reporting. Automated reporting capabilities streamline the process and eliminate the need for manual production of metrics and customized reports.
Playbook Creation: SOAR enables savings of up to 80% on playbook creation. By leveraging pre-built playbooks and automation capabilities, organizations can significantly reduce the time and effort required to develop and maintain incident response processes.
Alert Handling: With SOAR, organizations can achieve savings of up to 70% on alert handling. The automation of low-priority alerts allows security analysts to efficiently manage their workload and focus on more critical incidents.
Analyst Training: SOAR implementation can result in savings of up to 60% on analyst training. By automating repetitive tasks and standardizing incident response processes, SOC analysts can onboard faster and spend less time on training exercises.
Shift Management: SOAR can lead to savings of up to 30% on shift management. The automation of routine tasks reduces the reliance on manual shift handovers and allows for a smoother transition between security teams.
Standardized communication during incident response is another area where cost savings can be achieved. Effective collaboration facilitated by SOAR minimizes the impact of cyberattacks and prevents monetary losses associated with extended incident response and recovery timelines.
In summary, organizations that implement a SOAR platform can significantly reduce costs related to reporting, playbook creation, alert handling, analyst training, and shift management. By streamlining operations and automating repetitive tasks, SOAR improves efficiency while minimizing financial resources spent on incident response.
Automating Reporting and Metrics with SOAR
SOAR platforms offer automated reporting and metrics capabilities that significantly streamline the process of generating reports for security teams. With the ability to pull reports on demand or schedule them for automatic generation, SOC staff can ensure reliable and timely reporting without the need for manual intervention.
SOAR tools provide reporting templates and the flexibility to create custom reports, allowing security teams to tailor the reporting process to their specific requirements. This simplifies the reporting workflow, making it more efficient and accurate.
By automating reporting and metrics, SOAR eliminates the need for manual production of metrics, saving valuable time and effort for security analysts. Instead of spending hours compiling data and generating reports, analysts can focus on analyzing insights and making data-driven decisions to enhance incident response efforts.
With automated reporting and metrics capabilities, SOAR empowers organizations to effectively track and measure their incident response performance. By leveraging these capabilities, security teams can gain valuable insights into the effectiveness of their incident response processes, identify areas for improvement, and make data-backed adjustments to optimize their overall security posture.
“Automating reporting and metrics with SOAR has revolutionized the way security teams generate reports. It has significantly reduced the manual effort required, allowing us to focus on more critical tasks. The ability to create custom reports also allows us to tailor our reporting to specific stakeholders, ensuring they receive the information they need in a digestible format.”
Standardized Communication in Incident Response with SOAR
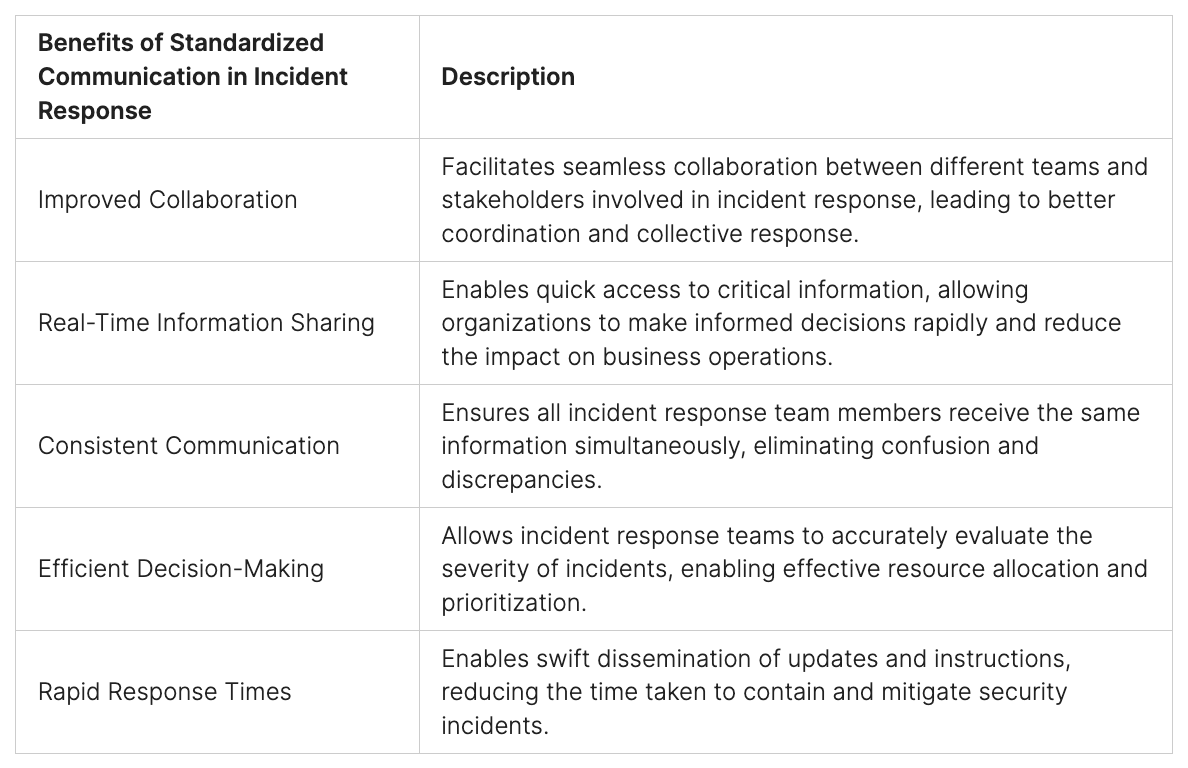
Effective communication is crucial during incident response, especially when dealing with major incidents. To facilitate standardized communication, organizations often establish a mission control hub or virtual war room. SOAR platforms play a vital role in ensuring critical information is shared consistently among team members, preventing any lapses or miscommunication.
When major incidents occur, a mission control hub or virtual war room becomes the command center for incident response. This centralized environment enables teams to collaborate effectively and make informed decisions in real-time. SOAR platforms provide features that support standardized communication within these dedicated spaces, ensuring that all incident response stakeholders have access to critical information.
The standardized communication flow in a mission control hub or virtual war room involves various stakeholders, both from within and outside the Security Operations Center (SOC). This includes representatives from Public Relations (PR), Human Resources (HR), Legal, and the C-suite. By involving these stakeholders, organizations can align their incident response efforts with overarching business goals and ensure consistent information dissemination across departments.
By establishing reliable and repeatable communication processes, SOAR enhances the overall effectiveness of incident response. It enables teams to collaborate seamlessly, make informed decisions based on real-time insights, and execute response plans efficiently. With standardized communication, organizations can minimize response times, improve coordination, and mitigate the impact of security incidents.
“Standardized communication is the backbone of effective incident response. It ensures that all team members have access to critical information in real-time, enabling them to respond swiftly and accurately. SOAR platforms help organizations establish reliable and repeatable communication processes, enhancing overall incident response capabilities.”
Benefits of Standardized Communication in Incident Response
Implementing standardized communication in incident response with SOAR platforms offers several key benefits:
- Improved Collaboration: Standardized communication facilitates seamless collaboration between different teams and stakeholders involved in incident response. This enables better coordination and the ability to respond collectively to security incidents.
- Real-Time Information Sharing: By centralizing communication and ensuring all team members have access to critical information in real-time, organizations can make informed decisions quickly. This leads to faster incident resolution and a reduced impact on business operations.
- Consistent Communication: Standardized communication processes ensure that all incident response team members receive the same information simultaneously. This eliminates any confusion or discrepancies that may arise from inconsistent communication practices.
- Efficient Decision-Making: Access to standardized communication channels allows incident response teams to evaluate the severity of incidents accurately. This enables them to prioritize their response efforts and allocate resources effectively.
- Rapid Response Times: Standardized communication enables incident response teams to quickly disseminate updates and instructions. This facilitates swift action and minimizes the time taken to contain and mitigate security incidents.
Through standardized communication, organizations can optimize their incident response capabilities and minimize the impact of security incidents. By leveraging SOAR platforms, teams can establish reliable and effective communication processes that enhance collaboration, enable rapid decision-making, and improve overall incident response effectiveness.
Conclusion
The adoption of a SOAR (Security Orchestration, Automation, and Response) platform stands as a strategic decision in advancing security operations, automating routine tasks, and enhancing incident response mechanisms. In an era marked by an escalating number of cyber threats, the necessity for organizations to boost their cybersecurity efficacy has never been more pressing. SOAR offers a holistic solution by integrating diverse security tools, standardizing operational processes, and fostering improved collaborative efforts.
By embracing the principles of security orchestration, automation, and response, organizations are empowered to fortify their capabilities in managing cybersecurity incidents. SOAR not only facilitates the amalgamation of various alerts for streamlined handling but also automates tasks deemed low-priority. This automation allows security teams to dedicate their focus to more critical and complex issues. The result is a tangible reduction in the impact of cyberattacks and a notable enhancement in the organization’s overall security framework.
The Peris.ai Brahma SOAR platform, a crucial component of Peris.ai Cybersecurity’s offerings, exemplifies the power of SOAR. It enables organizations to automate security processes, coordinate diverse security tools and systems, and respond to security incidents with increased efficiency and effectiveness. Key features of Peris.ai Brahma SOAR include Task Automation, Security Tool Integration, Playbooks, and Investigative and Remediation capabilities. This functionality not only streamlines security operations but also provides a centralized viewpoint for incident management, thereby eliminating inefficiencies and improving response strategies.
In essence, organizations that integrate the Peris.ai Brahma SOAR platform into their cybersecurity strategy are positioned to excel in the cyber landscape. This platform not only streamlines security operations and automates routine tasks but also optimizes the entire incident response process. As a result, organizations can significantly elevate their security posture, respond more effectively to cyber threats, and achieve a higher level of cybersecurity efficiency.
To explore how the Peris.ai Brahma SOAR platform can transform your organization’s approach to cybersecurity, visit Peris.ai Cybersecurity. Discover how our innovative solutions can elevate your cybersecurity capabilities and provide you with the tools needed to successfully navigate and overcome the challenges of the modern cyber environment.
FAQ
What is SOAR?
SOAR stands for Security Orchestration, Automation, and Response. It is a powerful tool for streamlining security operations and improving incident response in the face of increasing cyber threats.
How does SOAR improve incident response?
SOAR improves incident response by integrating security tools and automating tasks. It allows for the correlation of alerts from disparate systems into a single incident, saving time and enabling quicker alert handling. It also reduces manual operations and standardizes processes through the use of playbooks, which outline the steps of incident response and automate repetitive tasks.
What are the benefits of security orchestration?
Security orchestration brings efficiency to security operations by aggregating data from various security and network tools, providing a centralized view and actionable context for alerts. It automates the handling of low-priority and repetitive tasks, allowing SOC analysts to focus on higher-value work that improves incident response. It also reduces cyberattack impact by minimizing mean time to detect (MTTD) and mean time to respond (MTTR).
What is the role of security automation in SOAR?
Security automation reduces the need for human intervention in handling repetitive tasks and alerts. By automating low-priority alerts and incidents, it frees up SOC analysts to focus on more critical and complex tasks. This improves incident response by allowing analysts to dedicate more time and resources to investigating and resolving alerts.
How does SOAR contribute to streamlined operations?
SOAR integrates data from various sources and automates low-priority alerts and incidents, streamlining security operations. It gathers data from disparate systems, providing a centralized view and context for incidents. It handles low-priority alerts and incidents, reducing the need for manual intervention. Incident response in SOAR eliminates guesswork and minimizes cyberattack dwell time, resulting in more efficient and effective event handling.
Can SOAR integrate with different security technologies and tools?
Yes, SOAR platforms can easily correlate alerts from different products across various security domains. They facilitate the aggregation of data from cloud security, email security, endpoint security, network security, and more. The integration process is made easy with self-service marketplaces and simple button-click integration.
How does implementing a SOAR platform result in cost savings?
Implementing a SOAR platform enables savings on reporting, playbook creation, alert handling, analyst training, and shift management. By automating reporting and metrics capabilities, SOAR eliminates the need for manual reporting and reduces the time and effort spent on creating reports. Standardized communication during incident response also lowers costs by ensuring effective collaboration and minimizing the impact of cyberattacks.
Can SOAR platforms automate reporting and metrics?
Yes, SOAR platforms offer automated reporting and metrics capabilities. SOC staff can pull reports on demand or schedule them to be generated automatically. SOAR tools provide reporting templates and the ability to generate custom reports, simplifying the reporting process.
How does SOAR facilitate standardized communication in incident response?
SOAR platforms ensure standardized communication during incident response, particularly for major incidents. They provide features that ensure critical communication is standardized, preventing any team member from missing critical information. This standardized communication flow includes stakeholders from within and outside the SOC, such as PR, HR, legal, and the C-suite.
What are the key benefits of implementing a SOAR platform?
Implementing a SOAR platform streamlines security operations, automates repetitive tasks, and optimizes incident response. It enables organizations to achieve higher cybersecurity efficiency by integrating security tools, standardizing processes, and improving collaboration. It also reduces cyberattack impact, improves overall incident handling, and lowers costs.