Security Operations Centers (SOCs) are facing a critical challenge. While cyber threats grow in complexity and volume, SOC analysts are inundated with an overwhelming number of alerts, dashboards, false positives, and manual triage tasks. This relentless pressure leads to mental fatigue, burnout, and high turnover rates. Recent studies indicate that up to 70% of SOC analysts experience severe stress, with 64% considering leaving their roles within a year.
This isn’t merely a talent retention issue; it’s a significant risk to organizational security. Overwhelmed and disengaged defenders provide adversaries with opportunities to exploit vulnerabilities.
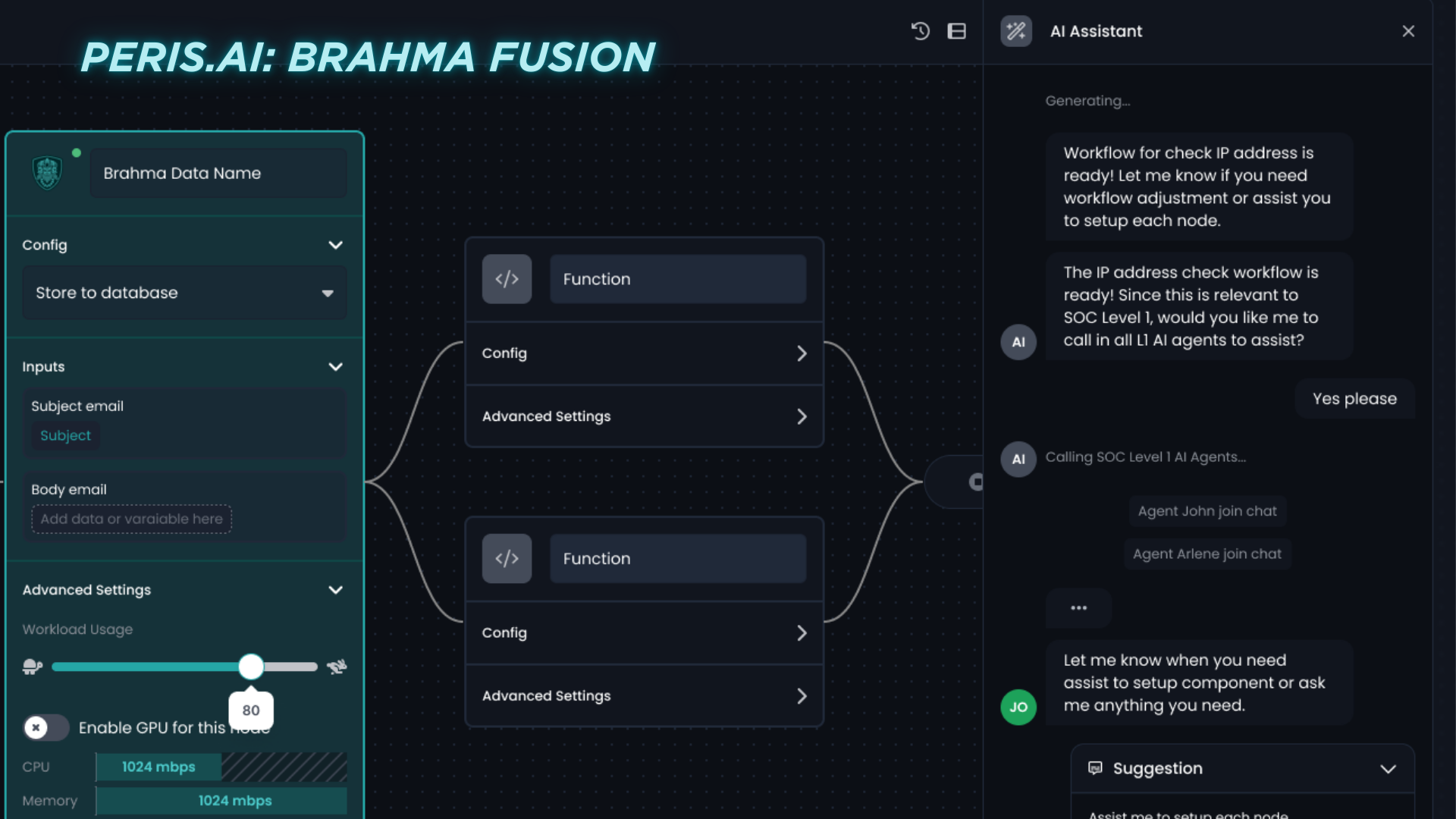
The solution lies in AI-powered playbooks that automate repetitive, time-consuming, and error-prone SOC tasks. Peris.ai’s Brahma Fusion enables SOCs to transition from reactive firefighting to intelligent, scalable operations.
The Burnout Equation: Why SOC Teams Are Struggling
1. Alert Overload
Modern SOCs handle thousands of alerts daily across SIEM, EDR, NDR, and cloud platforms. On average, SOC teams receive approximately 4,484 alerts per day, with analysts spending nearly 3 hours daily on manual triage.
2. Manual Triage Bottlenecks
Analysts dedicate significant time to pulling logs, correlating events, and classifying alerts, many of which turn out to be false positives.
3. Context Switching
Managing multiple tools and dashboards with varying interfaces and data structures leads to cognitive fatigue and inefficiencies.
4. Repetitive Tasks
Tasks such as enriching IOCs with threat intelligence, matching user behavior to baselines, checking logs for lateral movement, and ticket management consume valuable analyst time.
5. High Turnover and Low Morale
The monotonous nature of SOC work, combined with high stress, results in high turnover rates. Studies show that SOC analyst turnover rates can exceed 10% annually, with some organizations experiencing up to 25% turnover.
The Risk of Burnout: Security Suffers
- Delayed Response: Slower triage increases the dwell time of attackers within systems.
- Missed Threats: Fatigued analysts are more prone to overlook subtle anomalies.
- Inconsistent Workflows: High turnover leads to knowledge gaps and inconsistent processes.
- Decreased Innovation: Burned-out teams lack the capacity for proactive threat hunting and strategic improvements.
The AI Playbook Solution: Brahma Fusion from Peris.ai
Brahma Fusion offers intelligent automation through low-code, AI-powered playbooks that replicate and accelerate Tier-1 and Tier-2 SOC tasks.
What Is an AI Playbook?
An AI playbook is a dynamic, preconfigured sequence of detection, enrichment, triage, and response actions triggered by specific security events. Unlike rigid scripts, Brahma Fusion’s AI playbooks:
- Adapt to context
- Evolve with new threat intelligence
- Learn from analyst feedback
These playbooks free up human capacity and accelerate decision-making with consistency and scale.
How Brahma Fusion Helps Burnout-Proof Your SOC
1. Automated Alert Triage
- Suppresses low-fidelity alerts
- Enriches high-priority events with real-time threat intelligence from INDRA
- Scores alerts based on behavioral anomalies and threat actor patterns
2. One-Click Investigations
- Automatically collects logs from EDR, SIEM, firewall, and cloud platforms
- Builds visual timelines of incident-related activity
- Generates summary reports for analyst review
3. Proactive Response Actions
- Automatically isolates endpoints exhibiting ransomware behavior
- Revokes credentials for users with suspected compromise
- Blocks malicious IPs at firewall or cloud edge
4. Feedback-Driven Improvement
- Analysts can approve, modify, or reject AI decisions
- Brahma Fusion learns from every action to enhance future playbooks
Human + Machine, Not Human vs. Machine
Brahma Fusion doesn’t replace analysts; it amplifies them. The platform operates on the principle that:
- AI handles scale, speed, and routine tasks
- Humans handle judgment, intuition, and escalation
Together, they establish a sustainable, high-performance SOC model capable of scaling with threats without burning out talent.
How to Get Started
- Identify Burnout Hotspots: Determine which tasks are most draining for your team (e.g., phishing triage, false positive reviews).
- Deploy Prebuilt Playbooks: Start with common use cases: phishing, malware, credential abuse.
- Integrate Feedback Loops: Allow analysts to review and refine AI decisions.
- Measure and Share Wins: Report on saved analyst hours, reduced response times, and improved morale.
Conclusion: AI Isn’t Optional. It’s Essential.
The threat landscape continues to evolve, and alert volumes show no signs of decreasing. If your SOC is experiencing burnout, you’re not alone—but you are at risk.
With Peris.ai’s Brahma Fusion AI playbooks, you can:
- Alleviate alert fatigue
- Automate routine tasks effectively
- Refocus your analysts on critical issues
- Establish a resilient, sustainable, high-performing SOC
Don’t lose your best defenders to burnout. Let Peris.ai handle the noise, so your team can concentrate on the fight.
Learn more about Brahma Fusion at https://peris.ai