As technology continues to evolve, so make the cybersecurity threats. For companies and organizations, ensuring the safety and security of their data and systems is crucial to their success. Penetration testing is essential to any organization’s cybersecurity strategy, allowing them to identify and address vulnerabilities before attackers can exploit them.
Penetration testing, or “pen testing,” involves simulating a cyber attack on an organization’s systems and networks to identify weaknesses and vulnerabilities. By conducting this test, organizations can gain valuable insights into their security posture and make informed decisions about improving it. This article will explore penetration testing, how it works, and why organizations must include it in their cybersecurity measures. We will also discuss the different types of penetration testing and the benefits of conducting regular testing to ensure the security of your organization’s data and systems.
Overview of penetration testing
Penetration testing is a process that aims to identify and exploit vulnerabilities in an organization’s systems, networks, and applications. The testing process can be performed manually or through automated tools, and security experts typically conduct it with specialized knowledge and training in cybersecurity. The process can involve various techniques, including reconnaissance, scanning, and exploitation. It is designed to simulate a real-world attack scenario to identify potential weaknesses in an organization’s security posture. Once the testing is complete, a comprehensive report outlines the vulnerabilities discovered and provides recommendations for remediation. Overall, penetration testing is a critical cybersecurity practice that helps organizations proactively identify and mitigate potential security risks before malicious actors can exploit them.
Why Penetration Testing is Essential for Companies/Organizations?
Penetration testing is a critical component of cybersecurity for companies and organizations. By conducting regular penetration testing, organizations can identify vulnerabilities in their security measures before attackers can exploit them. This proactive approach to security enables organizations to take corrective actions to strengthen their security posture and protect their valuable data and assets. Additionally, penetration testing helps organizations maintain compliance with industry and regulatory standards. Failure to comply with these standards can result in significant financial and legal consequences, making it essential to conduct regular penetration testing. In summary, penetration testing is critical to any company or organization that values its security, compliance, and reputation. It helps identify vulnerabilities, strengthen security measures, and protect sensitive data and assets.
Protecting company data and assets
Protecting company data and assets is one of the main reasons why penetration testing is essential for companies and organizations. With the increasing sophistication of cyber attacks, organizations face a higher risk of cyber threats that can compromise their data and assets. By conducting regular penetration testing, organizations can identify vulnerabilities in their systems, networks, and applications and take corrective measures to strengthen their security posture. Penetration testing helps organizations stay one step ahead of attackers by identifying potential weaknesses before they can be exploited. Additionally, penetration testing enables organizations to simulate real-world attack scenarios, providing insights into the effectiveness of their security controls and enabling them to make informed decisions about future investments in cybersecurity.
Maintaining regulatory compliance
Maintaining regulatory compliance is another critical reason penetration testing is essential for companies and organizations. Industry and regulatory standards require organizations to implement appropriate security controls and conduct regular security assessments to protect sensitive data. Failure to comply with these standards can result in significant financial and legal consequences, including fines, legal action, and damage to an organization’s reputation. Penetration testing helps organizations maintain compliance with these standards by identifying vulnerabilities and weaknesses in their security controls and enabling them to take corrective actions before they are subject to regulatory scrutiny. By conducting regular penetration testing, organizations can demonstrate their commitment to security and compliance, build customer trust, and avoid potential legal and financial consequences.
Identifying vulnerabilities before attackers do
One of the critical reasons why penetration testing is essential for companies and organizations is to identify vulnerabilities before attackers do. The increasing sophistication of cyber-attacks means that organizations face a higher risk of data breaches, theft of sensitive information, and other forms of cybercrime. Regular penetration testing enables organizations to identify vulnerabilities and weaknesses in their security measures before attackers can exploit them. This proactive approach to security is critical in today’s threat landscape, where attackers are constantly developing new and more sophisticated methods to bypass security controls.
By identifying vulnerabilities before attackers do, organizations can take corrective actions to address these weaknesses, strengthen their security posture, and minimize the risk of a successful cyber attack. Penetration testing also provides valuable insights into the effectiveness of an organization’s security controls, enabling them to make informed decisions about future investments in cybersecurity. In summary, identifying vulnerabilities before attackers do is a critical reason why penetration testing is essential for companies and organizations. It enables organizations to stay one step ahead of attackers, protect sensitive data and assets, and maintain their reputation and customer trust.
Strengthening security posture
Strengthening security posture is another critical reason why penetration testing is essential for companies and organizations. Penetration testing comprehensively evaluates an organization’s security measures, including its policies, procedures, and technologies. By identifying weaknesses in these areas, organizations can take corrective actions to strengthen their security posture and minimize the risk of cyber attacks. Penetration testing also provides valuable insights into the effectiveness of an organization’s security controls, enabling them to make informed decisions about future investments in cybersecurity.
Strengthening security posture through penetration testing is critical in today’s evolving threat landscape, where attackers constantly develop new, more sophisticated methods to bypass security controls. A strong security posture minimizes the risk of a successful cyber attack and enables organizations to respond effectively to security incidents when they do occur. By conducting regular penetration testing and taking corrective actions to strengthen their security posture, organizations can demonstrate their commitment to security and build trust with customers and stakeholders. In summary, maintaining a security posture through penetration testing is a critical reason companies and organizations must prioritize this practice as part of their cybersecurity strategy.
What is Penetration Testing?
Penetration testing is a proactive and comprehensive approach to identifying and evaluating security vulnerabilities in a company or organization’s digital infrastructure. It involves simulating attacks to find exploitable weaknesses before malicious actors exploit them. This chapter defines penetration testing and how it differs from other cybersecurity services. Additionally, it covers the different types of penetration testing, including those focused on applications and content management systems. The phases of penetration testing and the methodologies and tools used are also discussed, providing a comprehensive understanding of the process.
Definition of penetration testing
Penetration testing is a security testing process that involves simulating a cyber attack on an organization’s systems, applications, or network infrastructure. Penetration testing aims to identify and exploit vulnerabilities that real-world attackers could leverage. The process is typically performed by a team of skilled cybersecurity professionals who use manual and automated techniques to identify vulnerabilities, assess the organization’s security posture, and provide recommendations for improving its security controls. Penetration testing is an essential component of any effective cybersecurity program, providing organizations with a comprehensive understanding of their risk profile and helping to prioritize and allocate resources for remediation. By regularly conducting penetration testing, organizations can proactively identify and address security weaknesses before malicious actors exploit them.
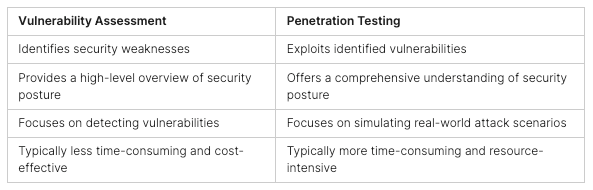
Comparison of penetration testing with other services in cybersecurity
There are several services in the cybersecurity industry, and while they all serve to protect organizations from cyber attacks, they differ in their approach and focus. Penetration testing, bug bounty programs, and Security Operations Centers (SOCs) are some of the most commonly used services in the industry.
Penetration testing involves simulating a real-world attack on an organization’s systems and infrastructure to identify vulnerabilities that attackers can exploit. The primary focus of penetration testing is to find weaknesses in an organization’s security posture before attackers do. On the other hand, Bug bounty programs are incentive-based programs that invite ethical hackers to find vulnerabilities in an organization’s systems and reward them for their findings. These programs are typically open to the public and can effectively identify vulnerabilities in an organization’s systems.
SOCs are dedicated teams responsible for monitoring and defending an organization’s systems against cyber threats. They use technology and human expertise to identify and respond to threats in real-time. The focus of SOC is to continuously monitor the organization’s systems and detect threats as quickly as possible to prevent or minimize the impact of cyber attacks.
While each service has unique approaches and benefits, penetration testing is often considered the most comprehensive approach to identifying and addressing vulnerabilities in an organization’s security posture. Penetration testing provides a detailed and in-depth assessment of an organization’s systems and infrastructure, whereas bug bounty programs and SOC may miss critical vulnerabilities.
Types of penetration testing
Penetration testing is a critical component of any cybersecurity program, and organizations can use several types of penetration testing to identify vulnerabilities in their systems. White box, black box, and grey box penetration testing provide different access levels and information to the tester, which can help uncover other vulnerabilities. Internal and external penetration testing simulates attacks from different perspectives, and both are important for identifying vulnerabilities in the organization’s network. Finally, manual and automated penetration testing approaches provide other advantages and disadvantages, with manual testing being more thorough and accurate but also slower and more labor-intensive. In contrast, automated testing can be faster and more efficient but may not identify all vulnerabilities. Choosing the correct type of penetration testing for an organization depends on various factors, including the organization’s goals, budget, and risk tolerance. It should be done in consultation with experienced cybersecurity professionals.
White/ Black/ Gray box penetration testing
There are three primary types of penetration testing: white-box, black-box, and grey-box testing. Each type of testing has its strengths and weaknesses, and the choice of testing methodology will depend on the organization’s specific needs.
White-box testing
White-box testing, or clear-box testing, is a penetration testing approach where the tester can access the system’s internal workings. This type of testing is usually performed by the development team or system administrators with detailed knowledge of the system architecture, programming code, and other system components. White-box testing gives the tester a comprehensive view of the system and allows them to evaluate its security from a technical perspective. This approach helps test complex systems where vulnerabilities may be hidden in the system architecture or source code. White-box testing can also help identify design and implementation flaws that may be missed in other testing methods.
Black-box testing
Black-box testing, also known as external testing, is a type of penetration testing where the tester has no prior knowledge about the system under test. This approach simulates the real-world scenario of an attacker without inside information about the target system. To identify potential attack vectors, the tester starts by performing reconnaissance activities such as information gathering and vulnerability scanning. Once the vulnerabilities are discovered, the tester exploits them to gain unauthorized access to the system. Black-box testing can help organizations identify vulnerabilities that may be missed during other types of testing, such as white-box testing. However, it can also be time-consuming and not provide a complete picture of the system’s security posture.
Gray-box testing
Gray-box testing is a combination of both white-box and black-box testing methodologies. In gray-box testing, the tester has limited knowledge of the system’s internal workings but has some understanding of its overall architecture and functionality. This testing type can be beneficial when the tester can access some system documentation or other information but not the complete source code. Gray-box testing can balance the in-depth analysis of white-box testing and the realistic assessment of black-box testing. This approach can help identify vulnerabilities that may not be apparent in black-box testing while allowing the tester to focus on the system’s most vulnerable areas.
Internal and External penetration testing
Penetration testing can be divided into two main types: internal and external testing. Both internal and external testing are essential components of a comprehensive penetration testing program, and each has unique benefits and challenges.
Internal testing
Internal testing is a type of penetration testing that simulates an attack from within the network or system being tested. Internal testing aims to identify vulnerabilities and weaknesses that an insider with legitimate access to the system could exploit. A tester typically conducts this testing with access to the internal network or design. It can help identify weak passwords, unpatched software, and misconfigured systems. Internal testing is essential for organizations to identify and mitigate risks posed by internal threats, including malicious insiders and accidental errors by employees. It helps organizations to strengthen their security posture and protect sensitive data from unauthorized access or disclosure.
External testing
External penetration testing involves testing the security of an organization’s assets from an external perspective, simulating an attack from a malicious actor on the internet. External testing aims to identify and exploit vulnerabilities in the organization’s perimeter defenses, such as firewalls, web application firewalls, intrusion detection systems, and other security technologies that protect the network from external threats. The external test is performed remotely, using tools and techniques that attackers might use, and tries to gain access to the organization’s network or applications without any prior knowledge of the system. The aim is to determine whether an attacker can access the organization’s strategies and sensitive data and to provide recommendations for improving the security posture of the organization’s perimeter defenses.
Manual and automated penetration testing
Manual and automated penetration testing are two different approaches used to test the security of a system or network. Manual and automated testing has advantages and limitations, and the choice between them depends on the specific needs and objectives of the penetration testing project. A combination of both approaches can be used to achieve the best results.
Manual testing
In penetration testing, a human tester manually searches for vulnerabilities in a system by attempting to exploit them. This method is proper when no automated tools are available for the specific procedure or the tester wants to understand the vulnerabilities more deeply. Manual testing allows testers to use their creativity and experience to identify vulnerabilities that automated tools may miss. However, manual testing is time-consuming, and there is a risk of human error. Additionally, manual testing can be expensive as it requires skilled personnel to carry out the testing. Manual testing is essential to penetration testing but should be combined with automated testing for maximum efficiency and accuracy.
Automated testing
Automated testing is a type of penetration testing that relies on software tools to identify and exploit vulnerabilities automatically. This approach to testing is often used to complement manual testing, as it can help identify a broader range of vulnerabilities and save time and effort. Automated tools typically perform tasks such as scanning networks, identifying open ports and services, and launching attacks to exploit known vulnerabilities. However, it’s important to note that automated tools are not foolproof and can miss specific vulnerabilities that may only be identified through manual testing. As such, manual and automated testing is often recommended for a more comprehensive and effective penetration testing strategy.
Apps and CMSs can be penetration testing
Application-based penetration testing and CMS penetration testing are essential aspects of penetration testing. Application-based penetration testing involves identifying and evaluating vulnerabilities in a specific application. This type of testing can be done through either black-box, white-box, or gray-box testing methods. On the other hand, CMS penetration testing is specifically focused on identifying and assessing the security of content management systems such as WordPress or Drupal. This type of testing evaluates the security of the CMS installation, plugins, themes, and application code. Both application-based and CMS penetration testing are crucial for ensuring the security of the application and the CMS system itself and can help to identify and address vulnerabilities before malicious actors can exploit them.
Application-based penetration testing
Application-based penetration testing is a type of testing that is focused on applications, including web applications, mobile applications, and other types of software. This testing method is designed to identify vulnerabilities within the application, such as cross-site scripting (XSS), SQL injection, and other potential issues that attackers could exploit. The goal of application-based penetration testing is to identify these vulnerabilities and provide recommendations on how to remediate them to improve the application’s overall security posture. The process typically involves manual testing and automated scanning tools and may be performed internally and externally.
Web application penetration testing
Web application penetration testing is a crucial process in ensuring the security of web applications. It involves comprehensively examining web applications to identify vulnerabilities and potential security breaches. During this process, various techniques are used to simulate attacks, identify weaknesses, and report them to developers for remediation. Web application penetration testing is necessary because web applications are often the primary entry points for cyber attackers. This type of testing can identify potential security gaps that hackers could exploit, including injection flaws, cross-site scripting, and broken authentication and session management. Once vulnerabilities are identified, developers can take appropriate steps to mitigate them and improve the application’s security.
Mobile penetration testing
Mobile penetration testing is a crucial aspect of application-based penetration testing. With the rapid development of mobile applications, the need to ensure their security has become increasingly important. Mobile penetration testing involves identifying security vulnerabilities and potential threats in applications running on different platforms, such as Android and iOS. The process involves analyzing the application and the underlying mobile device’s security to detect vulnerabilities and prevent unauthorized access. Common types of mobile application vulnerabilities include weak authentication, insecure data storage, and code injection. Penetration testing is vital for businesses that develop and use mobile applications to protect their data and ensure the security of their customers’ information.
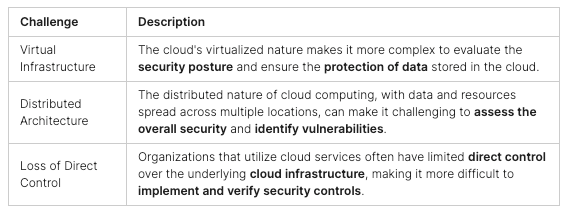
Cloud penetration testing
Cloud penetration testing is application-based testing that assesses the security of cloud-based services and infrastructure. With the increasing adoption of cloud computing, it has become essential for organizations to ensure the security of their cloud-based assets. Cloud penetration testing involves assessing the security posture of cloud-based systems, such as virtual machines, applications, and data storage services. The testing process includes identifying vulnerabilities and potential risks that attackers could exploit. Common areas assessed during cloud penetration testing include access controls, data security, encryption, and network security. Organizations can ensure their cloud-based systems and services are secure and protected against cyber threats by performing cloud penetration testing.
Network penetration testing
While application-based penetration testing primarily focuses on identifying vulnerabilities in web applications, network penetration testing takes a broader approach and assesses the security of an organization’s network infrastructure. It involves testing various network components such as routers, firewalls, switches, and other network devices to identify vulnerabilities that attackers could exploit to gain unauthorized access. Network penetration testing can be performed internally and externally. The goal is to identify security weaknesses in the network architecture and provide recommendations for improving the organization’s overall network security posture. The tests are conducted to simulate real-world cyberattacks and identify the effectiveness of network security measures.
API penetration testing
API (Application Programming Interface) penetration testing is a specialized type that focuses on identifying vulnerabilities and potential attacks in the API layer of an application. APIs facilitate communication between different software components and systems and play a critical role in the functionality of many modern applications. However, they can also introduce security risks if not adequately secured. API penetration testing involves assessing the security of APIs by testing their authentication mechanisms, authorization controls, input validation, and output encoding, among other factors. This type of testing can help organizations identify potential vulnerabilities and take steps to secure their APIs, reducing the risk of security breaches and other attacks.
Smart Contract penetration testing
Smart Contract penetration testing is an application-based penetration testing that focuses on identifying vulnerabilities in smart contracts. Smart contracts are self-executing digital contracts that are based on blockchain technology. Since they involve the exchange of valuable assets, such as cryptocurrencies, it is critical to ensure their security. Smart Contract penetration testing involves thoroughly analyzing the smart contract’s code to identify vulnerabilities attackers could exploit. The process involves using specialized tools and techniques to simulate attacks and identify weaknesses in the smart contract’s logic or code. This type of testing is essential for any organization that relies on smart contracts to ensure that they are secure and protect their assets.
CMS penetration testing
CMS penetration testing is critical for identifying security vulnerabilities in content management systems. Popular CMSs like Drupal, Joomla, WordPress, Magento, and Share are all susceptible to attacks if not adequately secured. Penetration testing for these platforms helps uncover vulnerabilities like cross-site scripting, SQL injection, insecure file uploads, etc. Drupal penetration testing can help discover configuration issues, while Joomla penetration testing can identify vulnerabilities like information leakage and file inclusions. WordPress penetration testing can help detect flawed custom code, insecure plugins, and themes, and Magento penetration testing can detect issues like insecure file permissions and lack of encryption. Share penetration testing can help identify flaws in its REST APIs and weak permissions. By conducting CMS penetration testing, organizations can ensure that their content management systems are secure and minimize the risk of potential cyber-attacks.
Drupal penetration testing
Drupal is a popular open-source content management system for developing various web applications. Drupal websites and applications are also susceptible to security vulnerabilities, so penetration testing is crucial to identify and address weaknesses. During Drupal penetration testing, a tester would comprehensively evaluate the website’s security posture to detect and exploit vulnerabilities, including outdated software, weak passwords, cross-site scripting, and other issues. The testing would be carried out using both manual and automated techniques to provide a thorough analysis of the Drupal site’s security. Once the testing is complete, the tester will provide a detailed report of the vulnerabilities found and recommendations for remediation.
Joomla penetration testing
Joomla is a popular content management system (CMS) used by many websites, and as with any other CMS, it is vulnerable to security threats. Joomla penetration testing involves testing the system for vulnerabilities, weaknesses, and configuration errors that attackers can exploit. The process of Joomla penetration testing includes identifying the website’s attack surface, scanning for vulnerabilities, testing for known and unknown vulnerabilities, exploiting vulnerabilities to determine the potential impact, and finally, providing recommendations for mitigation. Some common vulnerabilities in Joomla include cross-site scripting (XSS), SQL injection, file inclusion, and directory traversal. By performing Joomla penetration testing, website owners can identify and remediate security weaknesses before attackers exploit them.
WordPress penetration testing
WordPress is a popular content management system (CMS) that powers millions of websites. Due to its widespread usage, it has become a prime target for cyber attacks. Penetration testing for WordPress involves assessing the website’s security posture by simulating attacks that real-world threat actors could carry out. The testing focuses on identifying vulnerabilities in the WordPress installation, plugins, and themes used on the website. The testing methodology typically includes reconnaissance, vulnerability scanning, manual testing, and exploitation. Common vulnerabilities found in WordPress websites include weak passwords, outdated software versions, and vulnerable plugins. Organizations need to conduct regular WordPress penetration testing to ensure the security of their websites and protect against potential cyber-attacks.
Magento penetration testing
Magento is an open-source eCommerce platform that powers many online stores. Due to the sensitive customer and financial data it handles, it is crucial to ensure its security. Magento penetration testing is a way to identify potential security vulnerabilities that attackers can exploit. It involves testing the website’s vulnerabilities, such as SQL injection, cross-site scripting, and other web application security issues. Some critical areas of Magento penetration testing include testing the authentication and authorization mechanisms, code quality, server and application configuration, network architecture, and sensitive data storage. The main objective of Magento penetration testing is to identify security vulnerabilities and provide recommendations to fix them to secure the eCommerce platform.
Share penetration testing
SharePoint is a widely used content management system (CMS) that helps organizations manage their documents, data, and information. Due to its popularity, SharePoint can also become a potential cyber attack target. Penetration testing can help identify vulnerabilities in SharePoint deployments and assist in hardening security configurations. Penetration testing for SharePoint typically involves identifying misconfigurations, insecure access controls, and vulnerabilities in custom-developed SharePoint components. Standard testing techniques include a web application, authentication, authorization, and data exposure testing. It is crucial to conduct regular penetration testing of SharePoint deployments to ensure the security and integrity of sensitive organizational data.
Phases of penetration testing
Penetration testing typically consists of several distinct phases. These phases are crucial in ensuring the penetration test is thorough and accurately assesses the target system’s security posture.
Planning and reconnaissance
Planning and reconnaissance are the first phases of the penetration testing process. In this phase, the tester defines the scope of the test, identifies the target system or network, and gathers information about the system’s architecture and infrastructure. This information gathering may include identifying potential entry points for an attacker, such as open ports or services, and gathering information about the target system’s configuration, operating system, and applications. The tester may also research the target organization’s security policies and procedures to ensure compliance with relevant regulations and standards. The planning and reconnaissance phase is critical to the success of the penetration test, as it lays the groundwork for the subsequent steps and ensures that the test is conducted in a controlled and efficient manner. It also helps identify potential risks and vulnerabilities that could threaten the target system or network.
Scanning and enumeration
Scanning and enumeration is the second phase of the penetration testing process. In this phase, the tester performs scans of the target system or network to identify open ports, services, and vulnerabilities. This may involve using automated tools or manual techniques to identify potential vulnerabilities in the system. The tester may also enumerate, identify, and map the system’s resources and services. This phase can be time-consuming, but it is critical to the success of the penetration test, as it helps to identify potential entry points for attackers and vulnerabilities that can be exploited to gain access to the system. The information gathered in this phase is used to develop a plan of attack for the subsequent phases of the penetration test.
Gaining access
Gaining access is the third phase of the penetration testing process. In this phase, the tester exploits the vulnerabilities identified in the previous phases to gain access to the target system or network. This may involve using various tools and techniques, including password cracking, social engineering, or exploiting software vulnerabilities. This phase aims to gain access to the system and escalate privileges to gain further access to sensitive data or resources. The tester must ensure that they do not cause any damage to the system while attempting to gain access, and they must maintain a low profile to avoid detection. Once access is gained, the tester moves to the next phase of the penetration test.
Maintaining access
Maintaining access is the fourth phase of the penetration testing process. In this phase, the tester attempts to maintain access to the target system or network by escalating privileges or installing backdoors to ensure continued access. This phase aims to identify how long an attacker could maintain access to the system or network without being detected. The tester may attempt to access and exfiltrate sensitive data or resources, and they must ensure that they do not trigger any alarms or alerts that could lead to their detection. This phase can be particularly challenging, as the tester must remain undetected while attempting to maintain access to the system. Once the tester has achieved their objectives, they move on to the final phase of the penetration test.
Covering tracks
Covering tracks is the fifth and final phase of the penetration testing process. In this phase, the tester attempts to cover their tracks to avoid detection by deleting logs or other evidence of the penetration test. The objective of this phase is to leave the target system or network in the same state as before the penetration test. The tester must ensure that they do not leave any traces of their activities, as this could lead to their detection and compromise the integrity of the penetration test. This phase is critical to the success of the penetration test, as it ensures that the target organization is not left vulnerable to future attacks. The tester must also provide a detailed report of their findings and recommendations to the target organization, which can be used to improve the organization’s security posture.
Methodologies used in penetration testing
Penetration testing methodologies are a set of guidelines and procedures that are used to conduct comprehensive and structured penetration tests. These methodologies provide a step-by-step approach to identifying vulnerabilities and security weaknesses in systems and applications. The methodologies typically include various phases such as planning, reconnaissance, scanning, enumeration, gaining access, maintaining access, and covering tracks. Additionally, methodologies provide guidelines on documenting and reporting the penetration test findings, which can help organizations improve their security posture. The most widely used penetration testing methodologies include the Open Web Application Security Project (OWASP) and the National Institute of Standards and Technology (NIST). These methodologies provide a structured approach to penetration testing and help organizations identify vulnerabilities and weaknesses in their systems. By following these methodologies, organizations can ensure that their systems are tested comprehensively and structured, which can help identify potential vulnerabilities and improve their overall security posture.
Open Web Application Security Project (OWASP)
The Open Web Application Security Project (OWASP) is a non-profit organization dedicated to improving software security. The OWASP provides a range of resources for developers, security professionals, and organizations to improve the security of their software, including the OWASP Top Ten, a list of the most critical web application security risks. The OWASP also provides a comprehensive testing guide for web applications, which includes a methodology for conducting penetration tests on web applications. The OWASP testing guide provides a structured approach to testing web applications, which includes the planning, preparation, testing, analysis, and reporting phases. The OWASP testing guide includes various tools and techniques for testing web applications, including manual and automated testing approaches.
Organizations and security professionals widely use the OWASP methodology to conduct web application penetration tests. The methodology provides a comprehensive approach to testing web applications and ensures that all critical areas of the application are tested. The OWASP methodology includes several key steps, including identifying the target application, identifying the attack surface, identifying vulnerabilities, exploiting vulnerabilities, and reporting findings. The methodology also includes various tools and techniques for testing web applications, including automated scanning tools, manual testing approaches, and custom testing scripts. By following the OWASP methodology, organizations can ensure that their web applications are secure and protected from cyber-attacks.
National Institute of Standards and Technology (NIST)
The National Institute of Standards and Technology (NIST) is a non-regulatory agency of the United States Department of Commerce. The NIST provides standards and guidelines for various fields, including cybersecurity. The NIST has published Special Publication 800-115, which guides the planning and conducting of penetration testing. This publication provides a methodology that includes the planning, discovery, attack, and reporting phases. The methodology provides a structured approach to penetration testing and helps organizations identify vulnerabilities and weaknesses in their systems. The NIST methodology also emphasizes the importance of documenting and reporting the findings, which can help organizations improve their security posture.
Organizations and security professionals widely use the NIST methodology for conducting penetration testing. The methodology emphasizes the importance of collaboration between the organization and the testing team to ensure that the testing is aligned with the organization’s objectives. The NIST methodology also emphasizes the importance of understanding the system architecture and attack surface, which can help identify potential vulnerabilities. By following the NIST methodology, organizations can ensure that their systems are tested in a comprehensive and structured manner, which can help identify potential vulnerabilities and improve their overall security posture.
Tools used for penetration testing
Penetration testing is a crucial part of cybersecurity, requiring specialized tools to perform the tests effectively. Using these tools and others, penetration testers can simulate various attack scenarios and identify potential vulnerabilities that must be addressed.
Metasploit
Metasploit is one of the most popular and widely used penetration testing tools. It is a framework that offers a range of features for conducting penetration testing and can be used for manual and automated testing. Metasploit provides an extensive collection of exploits and payloads, making it easier for testers to simulate real-world attacks. It also offers a powerful scripting language and a web interface, which makes it easy to use even for those who need to become more familiar with command-line interfaces. With Metasploit, testers can identify vulnerabilities, exploit them, and gain access to systems, all while maintaining control and monitoring the entire process.
Nmap
Nmap is a network exploration and security auditing tool that is widely used in the field of penetration testing. It can be used to identify hosts and services on a network, as well as map out the network topology. Nmap can also detect open ports and vulnerabilities, making it an essential tool in the initial reconnaissance phase of a penetration testing engagement. Nmap’s scripting engine allows for the development of custom scripts that can automate various tasks, such as brute-force password cracking, service version detection, and vulnerability scanning. Overall, Nmap is a powerful and versatile tool that every penetration tester should be familiar with.
Burp Suite
Burp Suite is a popular penetration testing tool that detects and exploits web application vulnerabilities. It is a comprehensive platform with various tools such as a proxy, scanner, and intruder. It can test for vulnerabilities, including cross-site scripting (XSS), SQL injection, and session fixation attacks. Burp Suite allows testers to analyze web application traffic, identify vulnerabilities, and manipulate parameters to test how the application responds. It also has a feature for automating tasks to speed up testing. Overall, Burp Suite is a versatile and powerful tool that is widely used in the field of penetration testing.
OWASP ZAP
OWASP ZAP (Zed Attack Proxy) is a widely used open-source security testing tool to find security vulnerabilities in web applications. It can detect vulnerabilities like SQL injection, cross-site scripting (XSS), and buffer overflows. OWASP ZAP offers a user-friendly interface that makes it easy to use, even for those with limited experience in penetration testing. The tool can automate testing and generate reports, making it a valuable asset for developers and security professionals. OWASP ZAP is highly customizable, and users can extend its functionality with add-ons and scripts. Overall, OWASP ZAP is a powerful tool regularly updated to keep up with the latest security threats and vulnerabilities.
SQLmap
SQLmap is a powerful tool designed for automated SQL injection and database takeover. It is open source and can be used to detect and exploit SQL injection vulnerabilities in web applications. SQL injection is a technique used to exploit a vulnerability in a web application’s input validation, which allows an attacker to execute arbitrary SQL code and gain access to the database. SQLmap automates detecting SQL injection vulnerabilities, dumping the database contents, and taking control of the database server. It supports many database management systems, such as MySQL, Oracle, Microsoft SQL Server, and PostgreSQL. Penetration testers and security researchers frequently use SQLmap to identify and exploit SQL injection vulnerabilities and verify web application security.
Wireshark
Wireshark is a widely used network protocol analyzer tool for penetration testing to analyze network traffic. It allows testers to capture and view the data packets transmitted over the network and provides detailed information about the source and destination of the packets, as well as the packets’ contents. This information can be used to identify network vulnerabilities and determine whether there is any unauthorized access to sensitive data. Wireshark can also analyze traffic patterns and monitor network performance, making it a valuable tool for network administrators and security professionals.
Steps to Perform Penetration Testing
Penetration testing is critical in identifying a system’s vulnerabilities and weaknesses. The entire process requires a thorough understanding of the system and its potential vulnerabilities and the use of appropriate tools and techniques to ensure the accuracy and effectiveness of the testing process.
Preparation phase
The preparation phase is the first step in the penetration testing process. It involves defining the scope of the test, obtaining authorization and legal agreements, and gathering information about the system. The test scope should be clearly defined to ensure the penetration testers understand the systems in-scope and out-of-scope. Obtaining authorization and legal agreements ensures that penetration testing activities do not violate laws or regulations. Gathering information about the system is essential to help identify potential vulnerabilities and determine the best approach to testing. This information can be obtained through publicly available sources, such as company websites or social engineering tactics. The preparation phase lays the foundation for a successful penetration test and ensures that the testing activities are controlled and ethical.
Define the scope of the best
In the preparation phase of a penetration testing engagement, one of the critical steps is to define the scope of the test. This involves identifying the systems, applications, and network segments that will be tested and determining the specific objectives of the test. The scope should be clearly defined to ensure that the test is focused and that all relevant areas are covered. It is essential to consider legal or regulatory requirements when defining the scope and any potential impact on the organization’s operations. This helps to ensure that the test is practical and conducted safely and in a controlled manner.
Obtain authorization and legal agreements
Obtaining authorization and legal agreements is a crucial step in the preparation phase of penetration testing. The penetration tester must obtain written permission from the client or organization that owns the system to be tested. This permission should include clear guidelines on what the tester can do and what is out of scope. It is essential to ensure that the test does not disrupt or cause any damage to the system or network and that any potential legal or regulatory issues are addressed before starting the testing process. The legal agreements should outline the responsibilities and liabilities of both the tester and the client, ensuring that the testing is carried out within a legally and ethically acceptable framework.
Gather information about the system
The first step in the penetration testing preparation phase is gathering information about the tested system. This includes identifying the IP addresses, domain names, and network architecture. It also determines the operating systems, software applications, and services running on the target system. This information is critical in helping the penetration tester identify potential vulnerabilities that could be exploited during testing. Information gathering can be done through various techniques such as passive reconnaissance, active reconnaissance, and social engineering. Once this information has been gathered, the penetration tester can move on to the next step of the preparation phase, which is obtaining authorization and legal agreements.
Active testing phase
During the Active Testing phase of penetration testing, the team will use various tools and techniques to assess the target system’s security actively. Each of these steps will provide valuable insights into the system’s security posture and help identify areas for improvement. It is important to note that these tests should only be performed with proper authorization and carefully planned and executed to minimize any potential impact on the target system.
Vulnerability scanning
Vulnerability scanning is a critical component of the active testing phase in penetration testing. This process involves using automated tools to identify a system’s potential security flaws and weaknesses. These tools can scan the target system’s network, applications, and services to identify known vulnerabilities and security misconfigurations. Vulnerability scanning is essential to identify potential attack vectors and prioritize the risks before the exploitation phase. It can also help identify any unauthorized devices or services that may be present on the network. It is crucial to select the right tool and configure it correctly to ensure that all potential vulnerabilities are detected.
Exploitation
In the active penetration testing phase, exploitation refers to the attempt to gain unauthorized access to a system by taking advantage of a vulnerability or weakness. This process involves using different tools and techniques to exploit known vulnerabilities and misconfigurations in the system or application being tested. The goal is to gain access to sensitive information or elevate privileges to gain more control over the system. Exploitation requires much skill and knowledge to execute correctly, which can cause significant damage if done incorrectly. Therefore, penetration testers must be trained and experienced in the latest exploitation techniques to ensure that they can identify and exploit vulnerabilities effectively and safely.
Post-exploitation
In the active penetration testing phase, post-exploitation is when the tester tries to maintain access to the system after successfully penetrating it. The goal is to gain more privileged access and escalate privileges to perform more attacks or extract sensitive information from the target system. Post-exploitation techniques can include installing backdoors, modifying system configurations, establishing remote access tunnels, creating new user accounts, or installing keyloggers. The tester may use various tools and techniques to hide their tracks and avoid detection by security systems. This phase is essential to determine the extent of the damage an attacker can cause and how to prevent similar attacks from occurring in the future.
Password cracking
Password cracking is when penetration testers attempt to obtain valid user account credentials by guessing or cracking passwords. This can be done through various methods, such as brute force attacks, dictionary attacks, and rainbow table attacks. Password cracking aims to determine weak or easily guessable passwords that attackers could exploit to gain unauthorized access to the system. Penetration testers use tools like John the Ripper, Hashcat, and Hydra to crack passwords. It is important to note that password cracking should only be performed with proper authorization and only be used to access systems with proper consent.
Social engineering
Social engineering is a method of exploiting human psychology to gain access to sensitive information or systems. This technique involves manipulating people into divulging confidential information, such as usernames and passwords, or granting unauthorized access to computer systems. Social engineering can take many forms, including phishing emails, pretexting, baiting, and tailgating. As part of the active testing phase of penetration testing, social engineering techniques are used to test the effectiveness of an organization’s security policies and to identify areas where employee training and awareness can be improved. By simulating a social engineering attack, penetration testers can evaluate the ability of employees to recognize and respond appropriately to potential threats and make recommendations for strengthening the organization’s security posture.
Reporting and follow-up phase
The reporting and follow-up phase is a crucial step in penetration testing. This phase involves documenting the findings, presenting the report to management, and following up on the remediation of vulnerabilities. The report should include details on the scope of the test, methodologies used, vulnerabilities discovered, and recommended remediation strategies. The report should also include a risk rating for each vulnerability based on its impact and likelihood of exploitation. Once the report is presented to management, it is crucial to follow up on the remediation of vulnerabilities and retest to ensure that the identified vulnerabilities have been adequately addressed. This phase helps ensure that the identified vulnerabilities are appropriately remediated, reducing the risk of future attacks on the system.
Document findings
After conducting the active testing phase, it is essential that you document the findings clearly and thoroughly. This includes details on vulnerabilities discovered, the methods used to exploit them, and any sensitive data accessed. It is also essential to document any mitigations or workarounds identified during the testing. This document records the penetration testing process and its results, providing helpful information for future remediation efforts. It should also include recommendations for improving the system’s security posture, prioritizing the most critical issues based on the risk they pose to the organization.
Present the report to management
Presenting the report to management is a crucial step in penetration testing. The report should be clear and concise, highlighting all the vulnerabilities found during the testing phase. The report should provide a detailed explanation of the impact and risk level of each vulnerability, along with recommendations for remediation. It should also include technical details enabling the IT team to reproduce and fix the vulnerabilities. A good report will enable management to make informed decisions on improving the organization’s security posture. It is essential to ensure that the report is presented in a way that is easy to understand for all stakeholders, including non-technical management team members.
Remediation and retesting
Remediation and retesting are critical steps in penetration testing as they ensure that the identified vulnerabilities have been addressed and the system is secure. Once the penetration testing report has been presented to the management, the organization should immediately remediate the vulnerabilities. This could involve applying security patches, configuring firewalls, or implementing other security measures to mitigate the identified risks. After the remediation process, it is essential to conduct retesting to ensure that the vulnerabilities have been successfully addressed and the security measures have been effective. This step helps to identify any residual risks that were not remediated or any new vulnerabilities that may have been introduced during the remediation process. The remediation and retesting phase is vital to improve the organization’s security posture and protect the system against future attacks.
Challenges in Penetration Testing
Penetration testing can be challenging for many organizations, and several common obstacles can arise during the testing process. One major challenge is ethical and legal issues. It is crucial to ensure that testing is performed within the confines of the law and does not violate any ethical boundaries. Another challenge is the lack of skilled personnel, as penetration testing requires high technical expertise and knowledge. The limited scope can also be challenging, as it may be difficult to fully assess the security of all systems and assets within an organization. Additionally, false positives and negatives can occur during testing, making it challenging to identify vulnerabilities accurately. Finally, time and resource constraints can be a significant challenge, as organizations may need more resources for testing and remediation efforts.
Ethical and legal issues
Ethical and legal issues are some of the significant challenges that organizations face in penetration testing. Penetration testing involves testing the vulnerabilities of a system by simulating an attack, which could result in accessing sensitive data or causing damage to the system. Therefore, obtaining proper authorization and legal agreements is essential to ensure the testing does not violate any laws or regulations. Additionally, ethical issues can arise when testing ethical hackers need to be made aware of the boundaries between ethical and unethical behavior. As a result, it is crucial to establish clear ethical guidelines and codes of conduct for penetration testing to ensure that the testing is conducted ethically and legally.
Lack of skilled personnel
One of the main challenges of penetration testing is the lack of skilled personnel. Penetration testing requires a specific skill set, including knowledge of operating systems, programming languages, and networking protocols. Finding qualified professionals with experience in this field can be difficult, and the demand for such individuals continues to rise. As technology evolves, the skills required for effective penetration testing must also keep pace, leading to a skills gap that further exacerbates the problem. As a result, organizations may need to invest in training or outsourcing to ensure that their systems are adequately tested for vulnerabilities.
Limited Scope
One of the significant challenges in penetration testing is the limited scope. The scope of a penetration test determines the assets and systems that will be tested, which may not cover all possible vulnerabilities. In many cases, the scope of the test is determined by budget, time constraints, or other limitations. This means that some vulnerabilities may be missed, leading to security breaches. To overcome this challenge, it is crucial to thoroughly understand the systems and assets that need to be tested and to conduct the test to maximize the coverage of vulnerabilities. It may also be necessary to conduct multiple tests over time to identify and address all possible vulnerabilities.
False positives and false negatives
False positives and false negatives are common issues in penetration testing. False positives occur when a vulnerability is identified that does not exist, while false negatives occur when a vulnerability exists but is not detected by the testing process. These issues can be caused by various factors, including the complexity of the tested system, the testing tools’ limitations, and the testing personnel’s skill level. False positives can waste time and resources, while false negatives can leave security gaps that attackers may exploit. Testers must be aware of and minimize these issues, such as using multiple testing tools and approaches and thoroughly validating any identified vulnerabilities.
Time and resources constraints
One of the significant challenges in penetration testing is the limited time and resources available for conducting a thorough assessment. Penetration testing can be time-consuming and requires specialized skills, tools, and equipment. Companies often need more budgets and timeframes for conducting these assessments, which can result in incomplete testing or rushed evaluations. Additionally, false positives and negatives can be significant issues in penetration testing. False positives can lead to unnecessary remediation efforts, while false negatives can leave vulnerabilities unaddressed. To overcome these challenges, it’s essential for companies to allocate sufficient time and resources for penetration testing and to work with experienced and skilled professionals in the field.
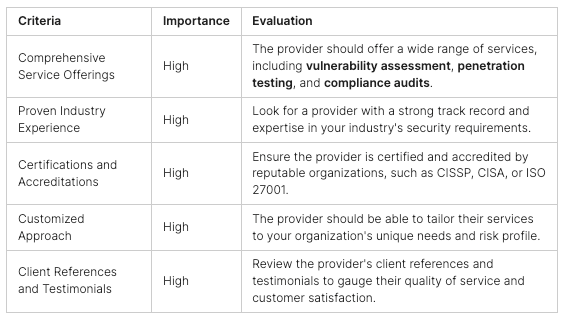
Choosing the Right Penetration Testing Provider
Choosing the right penetration testing provider is crucial to the success of a penetration testing project. Factors to consider when selecting a provider include their experience and expertise, the types of testing services they offer, their certifications and accreditations, and their reputation in the industry. It is also important to ask potential providers about their methodology, reporting process, and experience with similar projects. Red flags to watch out for include providers who promise unrealistic results or must provide a clear and detailed scope of work. Ultimately, choosing a provider who can provide the necessary expertise, resources, and communication to effectively and efficiently conduct a penetration testing project is essential.
Factors to consider when choosing a penetration testing provider
When choosing a penetration testing provider, several essential factors must be considered. Firstly, you should ensure that the provider has a good reputation and a track record of delivering high-quality services. It’s also important to consider the provider’s expertise and experience in your specific industry and the technologies you use. Additionally, looking for a provider that uses up-to-date testing methodologies and tools and has a clear understanding of compliance and regulatory requirements would be best. Finally, you should consider the provider’s communication and reporting capabilities, as clear and concise reporting is crucial for ensuring that any identified vulnerabilities are appropriately addressed.
Questions to ask potential providers
When choosing a penetration testing provider, you must ask various questions to ensure they meet your needs. Questions might include the provider’s experience, methodology, certifications, and approach to remediation and follow-up. Additionally, ask about the specific skills of the testing individuals and whether they have experience with your particular industry or technology. It is also essential to ask about the provider’s reporting process, including the level of detail and clarity you can expect. By asking these questions, you can better evaluate potential providers and make an informed decision.
Red flags to watch out for
When choosing a penetration testing provider, one must be aware of red flags indicating a less-than-reputable or competent provider. One red flag to watch out for is a provider that offers a one-size-fits-all approach to penetration testing rather than tailoring their approach to the specific needs and risks of the organization. Another red flag is a provider that guarantees a 100% success rate or offers unrealistic promises, as the nature of penetration testing means that there is always a possibility that some vulnerabilities will be missed. Additionally, providers that do not provide clear and transparent communication throughout the process or cannot provide references or case studies may also raise concerns. It is essential to thoroughly vet potential providers and ensure they have the experience, expertise, and reputation for providing high-quality and effective penetration testing services.
Conclusion
In conclusion, penetration testing is vital in ensuring the security and integrity of companies’ and organizations’ digital assets. It helps identify vulnerabilities and weaknesses in the system, which attackers can exploit. Regular penetration testing is necessary to maintain a strong security posture and prevent cyber attacks. As technology advances, the importance of cybersecurity in today’s digital landscape cannot be overstated. Companies and organizations must remain vigilant in protecting their digital assets by implementing robust cybersecurity measures and conducting regular penetration testing. Only then can they safeguard their reputation, customers, and sensitive data.
Recap of the importance of penetration testing for companies/organizations
Penetration testing is critical for companies and organizations to identify vulnerabilities in their systems and networks before cybercriminals exploit them. Penetration testing comprehensively evaluates an organization’s security posture, network infrastructure, software, and people. The process helps organizations determine whether their security measures are sufficient to protect against attacks, assess the effectiveness of their security policies and procedures, and identify any weaknesses in their security posture. Penetration testing is essential for organizations that handle sensitive data, such as financial institutions and healthcare providers. It is also a valuable tool for any organization that wants to improve cybersecurity.
Emphasize the need for regular penetration testing
penetration testing is crucial for companies and organizations to ensure the security and safety of their networks, systems, and data. It helps them identify vulnerabilities, weaknesses, and potential threats before attackers can exploit them. Regular penetration testing is necessary to maintain a strong security posture as new vulnerabilities, and threats emerge. It is important to remember that security is ongoing, and a one-time penetration test is insufficient to protect against constantly evolving cyber threats. Therefore, companies and organizations should prioritize regular and comprehensive penetration testing as a vital part of their cybersecurity strategy.
Final thoughts on the significance of cybersecurity in today’s digital landscape
In today’s digital landscape, cybersecurity has become increasingly crucial for companies and organizations of all sizes. The threat landscape constantly evolves, and cybercriminals are becoming more sophisticated in their attacks. Businesses must adopt proactive measures, such as regular penetration testing, to identify and address vulnerabilities before attackers can exploit them. The consequences of a successful cyber attack can be severe, including financial losses, reputation damage, and legal liabilities. Therefore, investing in cybersecurity is necessary and a wise business decision. Companies that prioritize cybersecurity will have a competitive advantage and gain the trust of their customers. Overall, the significance of cybersecurity cannot be overstated, and it should be a top priority for all organizations in today’s digital age.
You can take the first step in protecting your business from cyber threats. Our cybersecurity assessment and on-demand penetration testing platform can give you peace of mind knowing your systems are secure. You can visit our solution today to protect your company’s future. Don’t wait for a cyber attack; be proactive and prioritize your cybersecurity now!