As we use more digital tech, keeping our cybersecurity up is key. Cybercriminals are always looking for new ways to trick people. A big 86% of companies hit by ransomware were attacked on holidays or weekends.
This shows hackers work all the time, and so should your security. Good cybersecurity is vital to keep your business safe from digital threats.
It’s important to invest in strong cybersecurity and online safety. With more complex cyber attacks, old defenses won’t cut it. You must stay alert and keep up with new threats.
By focusing on ongoing cybersecurity, you can shield your business from cyber attacks’ harm.
Key Takeaways
- Hackers often launch attacks on weekends or holidays, when security teams may be less vigilant.
- 86% of companies targeted by ransomware were attacked on a holiday or weekend.
- Continuous cybersecurity is essential to protecting your business from evolving threats.
- Robust online security measures can help prevent cyber attacks.
- Investing in cybersecurity can help safeguard your business from devastating consequences.
- Cyber attacks are highly targeted and sophisticated, making traditional defenses insufficient.
The Rising Tide of Weekend Cyber Attacks
Weekend cyber attacks are on the rise, with about 60% of all cyber incidents happening then. This is a big worry, showing we need strong network protection and IT security to stop data breaches.
More than 45% of cybersecurity experts say they’ve seen more attacks on Saturdays and Sundays. They also face a 30% longer wait to deal with cyber incidents on weekends. This delay can cost a lot, with weekend attacks causing an average loss of $1.4 million.
The following statistics show how serious this problem is:
- 70% of surveyed organizations have inadequate weekend security measures in place.
- 50% of companies do not have incident response teams operational during weekends.
- 80% of ransomware attacks start over the weekend, when they know organizations have fewer resources.
*US Gov says ‘Don’t use a VPN’. Should you trust it?: https://youtube.com/watch?v=AYrx2EfhzNc
To fight these threats, 90% of IT professionals suggest constant monitoring. By focusing on network protection and IT security, companies can lower the chance of data breaches. This also helps reduce the financial damage from weekend cyber attacks.

Meet Company X: A Target During Downtime
Company X is a top player in its field. Recently, hackers hit them during downtime. This attack led to a big information security breach, losing sensitive data and halting work.
This shows how vital secure websites and strong security are, even when not in use.
The breach at Company X was due to human mistakes and weak security. Stats show 88 percent of breaches come from human errors, costing $4.88 million on average. Hackers found a weak spot in the system, getting to sensitive info and causing big harm.
To avoid such breaches, companies must focus on information security and secure websites. They should set up strong security, check for vulnerabilities often, and train staff on cybersecurity. These actions help lower the risk of a breach and keep data safe.
Some important steps for better information security include: Doing regular security checks and risk assessments Using strong security tools like firewalls and intrusion detection Training employees on cybersecurity Investing in secure websites and solid security measures
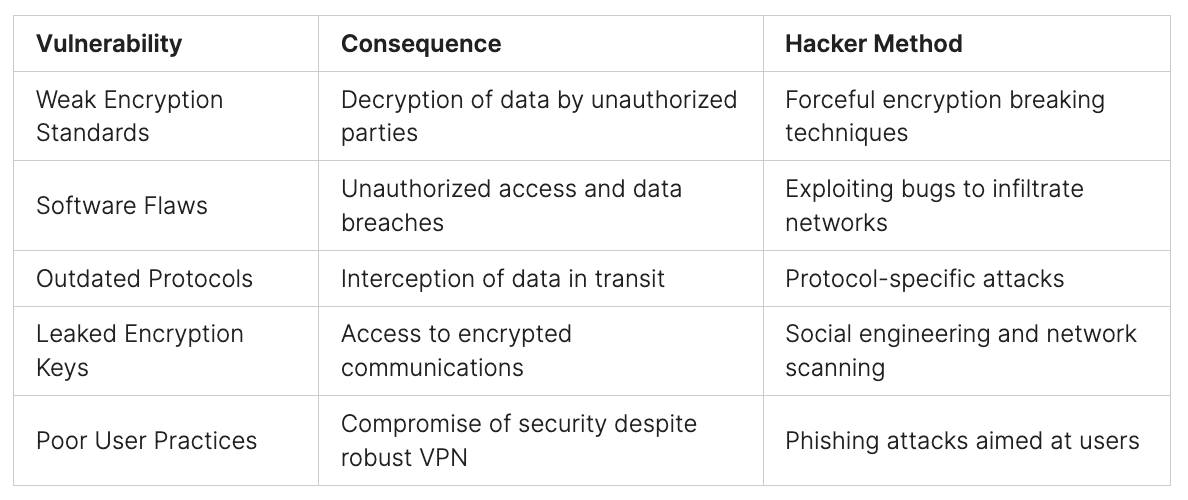
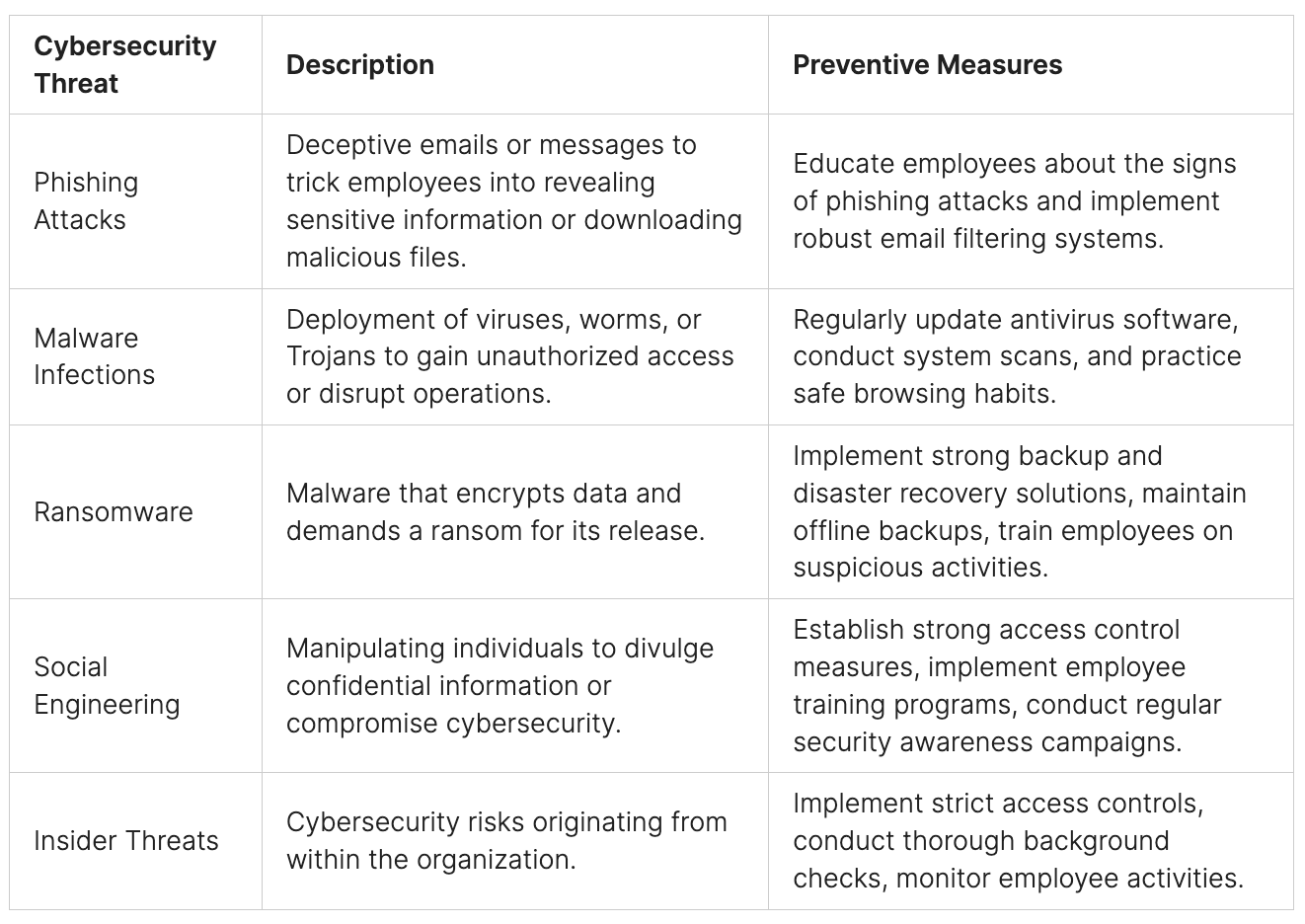
The Vulnerability Assessment
Doing a deep dive into vulnerability assessment is key to spotting security holes and weak spots. It’s about checking how well digital shields and cybersecurity steps work to stop breaches. With strong digital defenses, companies can cut down cyber attack risks and keep their data safe.
Risk analysis is a big part of this. It finds out what threats might hit and what to do first. It looks at how likely a breach is, how bad it could be, and how good current security is. With the right digital shields and cybersecurity know-how, companies can make a solid plan to tackle risks.
Initial Security Gaps
Security gaps often include old software, weak passwords, and poor network setup. These holes can let attackers sneak into a company’s systems and data. Fixing these weak spots with strong digital shields and cybersecurity can really lower breach risks and keep assets safe.
Risk Analysis Findings
Risk analysis shows the need for better digital shields and cybersecurity. This might mean getting new threat detection tools, doing regular security checks, and teaching employees about cybersecurity. By focusing on these, companies can make their cybersecurity stronger and lower breach risks.

Critical Points of Exposure
Critical weak spots are where a company’s digital shields and cybersecurity are most at risk. These might be old systems, unpatched bugs, or bad access controls. Fixing these weak spots can greatly lower breach risks and keep sensitive data safe.
Hackers Don’t Take Weekends Off: The Wake-Up Call
The need for constant cybersecurity is clear, as hackers don’t take weekends off. The FBI’s Internet Crime Complaint Center saw nearly 56,000 reports of personal data breaches in 2023. With about 100 different account passwords and logins, keeping everything secure is tough.
Some important stats show how serious this problem is:
- The Identity Theft Resource Center found victims of identity theft lost millions, mainly from crypto and romance scams.
- Many breaches come from automated or scalable attacks, not just direct financial theft.
- Nation-state attacks often aim to gather information for intelligence or to gain an edge, not always causing immediate financial loss for individuals.

Given these numbers, companies must act fast to protect themselves. They need to understand that hackers don’t take weekends off. By focusing on cybersecurity and using strong security measures, companies can lower the chance of data breaches. This helps keep their customers’ personal info safe.
Year: Number of Reports
- 2022 over 200,000
- 2023 nearly 56,000
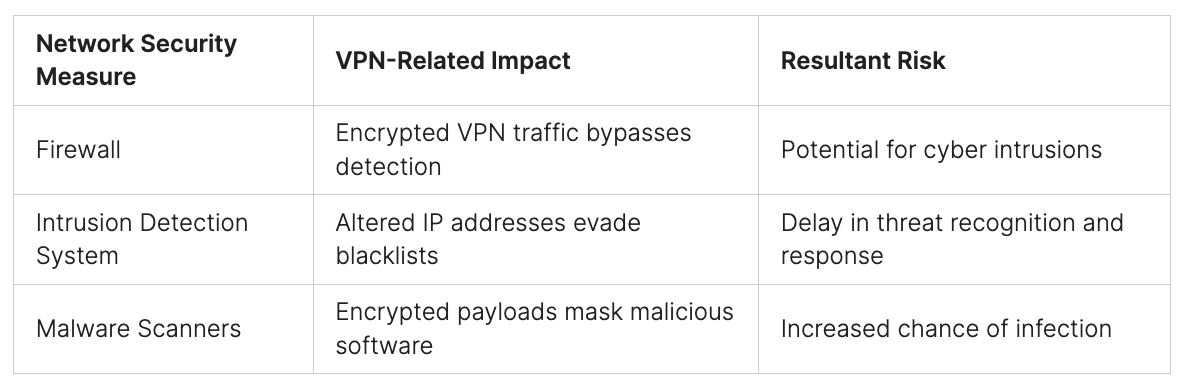
Implementing 24/7 Security Protocols
To keep your IT security and network safe, it’s key to have 24/7 security protocols. This means keeping your tech up to date, training your team, and having plans for emergencies. These steps help protect your organization from threats.
Here are some important steps for 24/7 security:
- Do regular security checks to find weak spots in your network and devices.
- Use firewalls and network security tools for constant protection.
- Have strong password rules and multi-factor authentication to stop hacks.
- Train your team regularly to make them security experts.
By focusing on IT security and network protection, you can lower the chance of data breaches and cyber attacks. As cybersecurity threats keep changing, it’s vital to stay ahead. With good security plans, your business can keep its systems and data safe, even when you’re not working.
*Data Exfiltration over TCP SSH HTTP(S) ICMP & DNS | TryHackMe | Part One: https://youtube.com/watch?v=qeDU-qyHy3s
Doing security audits and penetration tests helps find weak spots in your network. This lets you fix problems before they get used by hackers. Adding this to constant network watching and having a plan for security issues means your business is always ready to face any security problem.

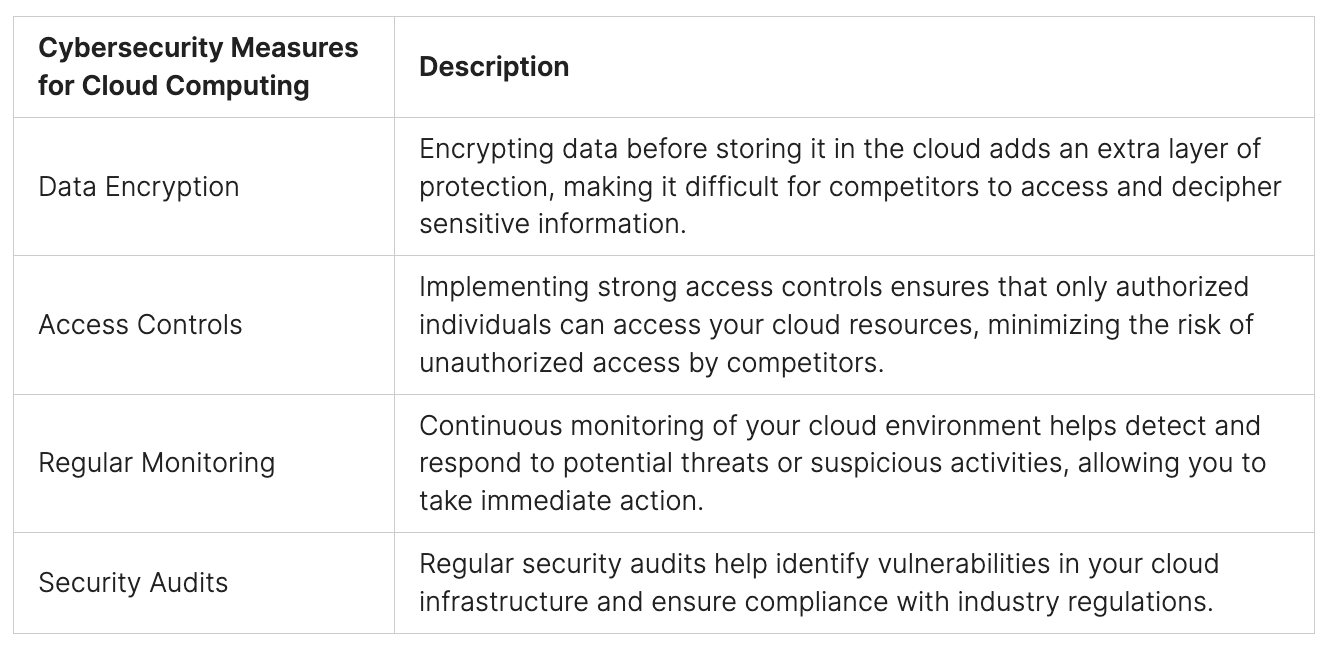
Continuous Monitoring Solutions
Continuous monitoring solutions are key in stopping cyber attacks. They help improve cybersecurity and online security. These tools give real-time insights, letting businesses quickly fix security issues before they become big problems.
Recent stats show cyber attacks went up by 30% in 2024. On average, a business faces 1,636 attacks every week.
Using these solutions can cut down on security incidents. For example, regular scans can find hidden malware or weaknesses. This lowers the chance of data breaches. Also, penetration testing can find and fix weaknesses fast, saving time and effort.
Some main benefits of these solutions are:
- Improved incident response efficiency by 95%
- Reduced detection times for breaches from weeks to minutes
- Enhanced security posture, resulting in fewer data breaches and lower costs
It’s vital for businesses to invest in continuous monitoring solutions. As online security keeps changing, staying ahead of threats is essential. With these solutions, businesses can keep their data safe, lowering the risk of cybersecurity breaches and costs.
*Have you been hacked? Hacker explains how to find out!: https://youtube.com/watch?v=bf-4ipD2S1M
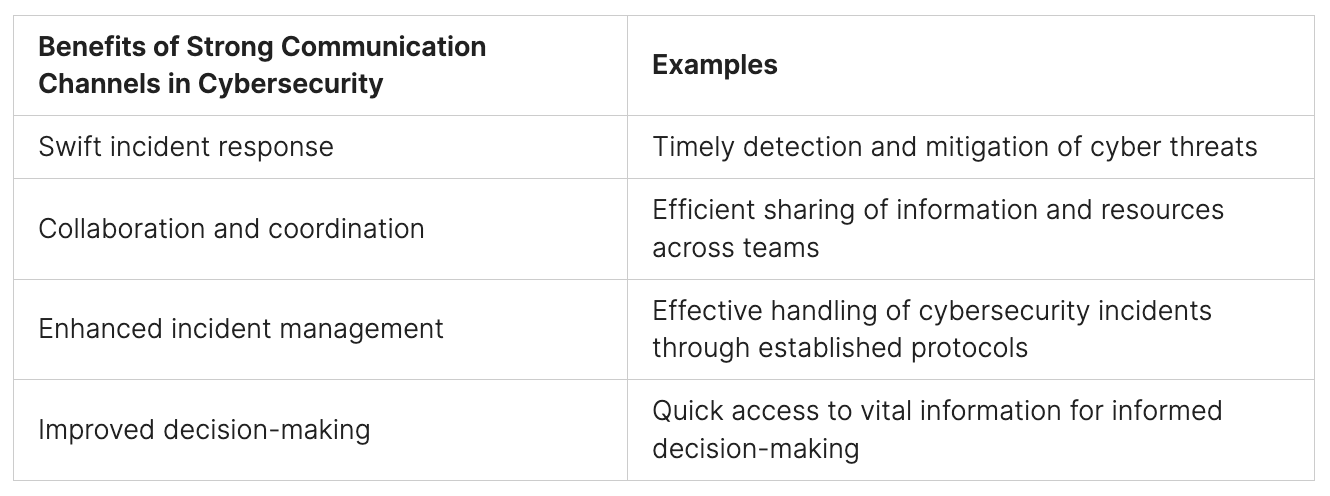
The Human Element in Round-the-Clock Security
In the world of round-the-clock security, people are key to keeping digital information safe. A culture that values security is critical today. This is because threats can pop up at any time.
To build a security-first culture, we need to train and educate staff. These programs should teach employees about the importance of digital safety. They should also give them the tools to spot and handle threats.
Staff Training and Awareness
Good staff training and awareness programs boost an organization’s security. By teaching employees about the latest threats and best practices, they can protect sensitive info. This makes them more proactive in keeping data safe.
Some important parts of staff training include:
- Regular security awareness training sessions
- Phishing simulation exercises
- Incident response planning and training
- Continuous monitoring and feedback mechanisms
By focusing on the human side of security, organizations can improve their defenses. This helps reduce the chance of security breaches and cyber threats.
Measuring Success: Security Metrics That Matter
To make sure cybersecurity and online security work well, it’s key to watch and study important metrics. This means keeping an eye on how many incidents happen, how fast we respond, and how they affect the company. Regular security audits and vulnerability scanning help spot risks and weak spots.
It’s also vital to check how good our incident response is. A 2022 IBM survey showed 68% of people often handle more than one incident at once. This shows we need quick and smart ways to deal with incidents. Also, a Sophos survey found 85% of people felt burned out, which hurts our security efforts.
Some key security metrics to keep an eye on are:
- Incident response time
- Number of incidents
- Types of incidents (e.g., phishing, ransomware)
- Employee training and awareness
- System updates and patch management
By watching these metrics and using good cybersecurity and online security, companies can lower the chance of problems.

Return on Security Investment
Investing in it security and network protection can greatly benefit a company’s finances. Studies show that 70% of organizations see a positive Return on Security Investment (ROSI) from their cybersecurity efforts. This is because strong security programs can cut breach costs by 24% on average.
Some key areas where it security and network protection offer a return include:
- Cost savings from fewer breach incidents
- Improved efficiency through security automation
- Enhanced reputation and customer trust
Also, investing in it security and network protection can save companies from the high costs of data breaches. The average cost of a data breach in the U.S. is $4.24 million. By investing in security, companies can lower the risk of a breach and avoid these costs.
In summary, investing in it security and network protection is vital for any company’s security strategy. It offers a return on investment, helping companies improve their finances while reducing the risk of expensive data breaches.

Future-Proofing: Beyond Traditional Security Hours
As cybersecurity threats grow, it’s key for companies to keep their security up to date. Hackers don’t take weekends off, and your security shouldn’t either. With more non-human identities and high-level access, cyber attacks are a bigger risk than ever.
One big issue in cybersecurity is infrastructure sprawl. It can cause security tool overlaps and increase risks. To outsmart hackers, companies need ongoing cybersecurity efforts. This includes regular password changes and AI for threat detection.
Some important stats show why cybersecurity awareness is critical:
- For every human user, there are 20 non-human identities, often with high-level privileges, posing significant risks.
- 53 percent of organizations take over 13 weeks to rotate passwords, creating unnecessary vulnerabilities.
- 80 percent of surveyed organizations responded to what they believe to be AI-based attacks or threats within the last 12 months.
By focusing on cybersecurity and keeping up with new threats, companies can defend against hackers who work all the time. It’s time to move beyond old security hours. Invest in a strong cybersecurity plan that can handle today’s threats.
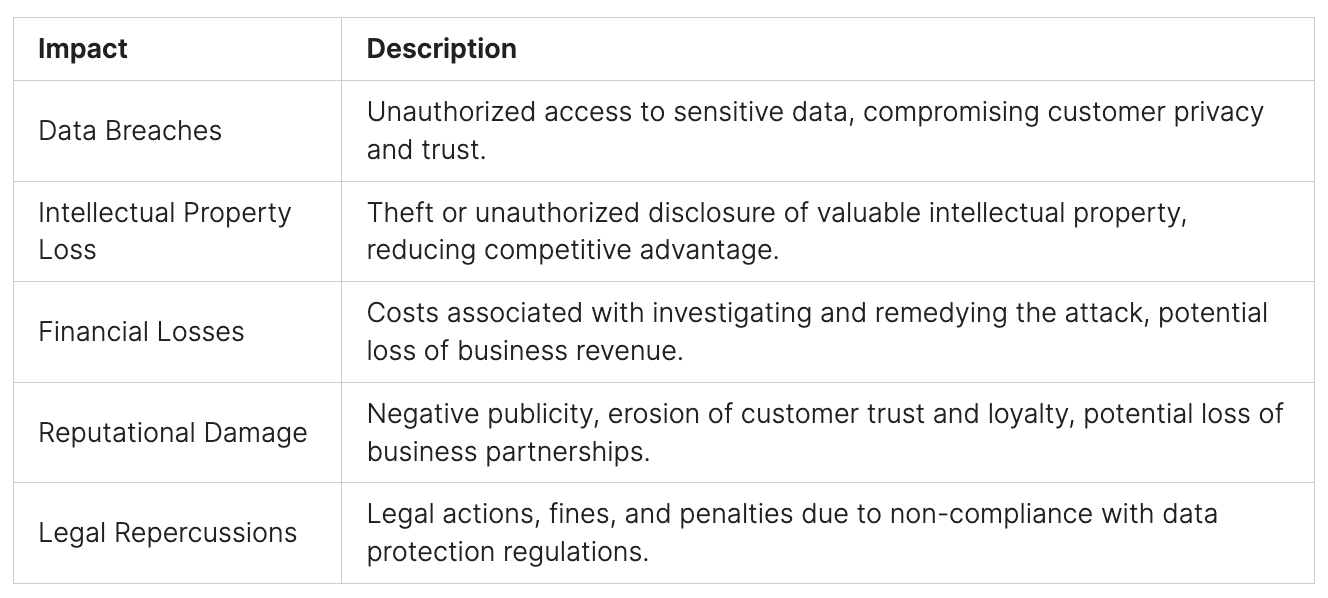
Conclusion: Securing Your Business Around the Clock
Cyber threats are evolving rapidly, and businesses must stay ahead with automation and orchestration to enhance their cybersecurity posture. With the average cost of a data breach reaching $4.88 million in 2024, organizations can no longer afford reactive security measures. Proactive automation is the key to minimizing risks and ensuring 24/7 protection against emerging threats.
Brahma Fusion empowers security teams by:
- Automating security workflows to reduce manual effort and human errors.
- Enhancing orchestration by seamlessly integrating security tools and platforms.
- Improving response times with real-time threat detection and incident management.
By leveraging customizable security responses, an intuitive drag-and-drop interface, and precision scripting, organizations can build a cybersecurity strategy that is resilient, scalable, and highly efficient.
Take control of your security operations with Brahma Fusion. Visit https://www.peris.ai/ to explore how automation and orchestration can transform your cybersecurity strategy.
FAQ
What is the significance of continuous cybersecurity, and how does it impact my business?
Continuous cybersecurity is key because hackers never stop. They often target companies on weekends or holidays. This shows the need for constant online security and cybersecurity measures.
Why do hackers target companies during off-hours, and what are the consequences of weekend vulnerabilities?
Hackers go after companies when they’re less protected. This is because network and IT security are weaker during off-hours. It makes it easier for them to breach data, leading to big financial losses and damage to reputation.
How can I ensure that my website is secure, and what role does information security play in protecting my business?
To keep your website safe, use information security steps. This includes encrypting data, using secure protocols, and updating software and plugins. These actions help prevent cyber attacks and protect your business from data breaches.
What is a vulnerability assessment, and how can it help identify security gaps in my business?
A vulnerability assessment finds and checks security gaps in your business’s digital defenses. It helps you take steps to fix these issues and prevent cyber attacks.
Why is it essential to implement 24/7 security protocols, and what measures can I take to improve my business’s IT security and network protection?
Having 24/7 security is vital. It includes updating technology, training staff, and having emergency plans. These steps improve IT security and network protection, helping to prevent attacks and breaches at any time.
How can continuous monitoring solutions help detect and prevent cyber attacks, and what benefits do they offer for my business’s online security?
Continuous monitoring solutions watch your online security in real-time. They help spot and stop cyber attacks quickly. This keeps your business safe from data breaches and other threats.
What role does the human element play in round-the-clock security, and how can I build a security-first culture in my business?
People are key in round-the-clock security. Building a security-first culture means training staff on digital safety. It also means creating a culture where everyone is aware and responsible for security.
How can I measure the success of my business’s security measures, and what security metrics should I use to evaluate their effectiveness?
To see if your security measures work, use important security metrics. Look at incident response times, attack detection rates, and data breach prevention. These help you see how well your cybersecurity is doing.
What is the return on security investment, and how can I analyze the cost savings and prevention vs. recovery economics of my business’s security measures?
The return on security investment is the savings and benefits from IT security. Analyzing the cost savings and prevention vs. recovery economics helps you see if your security investments are worth it. It guides your decisions on cybersecurity.
How can I future-proof my business’s security, and what measures can I take to stay ahead of hackers and cyber threats?
To keep your business secure, use continuous cybersecurity. Stay updated on the latest threats and trends. Always check and improve your digital safeguards to stay ahead of hackers and threats.