In today’s digital world, we often overlook a big threat – internal threats. These come from employees, contractors, or others inside the company. They can be very dangerous. But do we really understand and deal with these threats well? The answer might surprise you.
While we hear a lot about cyber threats from outside, insider threats can be just as bad. These insiders know a lot about how the company works and can get to sensitive info. They can cause big data breaches, financial losses, and harm the company’s reputation. In fact, many people in business and IT are very worried about these threats, rating them very high.
Key Takeaways
- Internal threats are a big risk for companies, coming from employees, contractors, or others inside.
- These threats can lead to big problems like data breaches, financial losses, and damage to the company’s reputation.
- Many people in business and IT are very concerned about the risk of insider cyber attacks.
- Companies need to act to reduce these risks, as ignoring them can hurt the company’s security and health.
- Creating strong security plans, promoting a culture of security awareness, and using good access controls and monitoring are important to fight internal threats.
The Gravity of Insider Cybersecurity Threats
Insider threats are a big worry for healthcare groups. A recent survey by HIMSS Media showed many in the industry are very concerned. Most people in business and clinical roles worry a lot about these threats, giving them a score of 8.2 out of 10. Over half of them think these threats are very serious.
Also, 42% of IT experts share the same big worry. This shows how serious insiders are seen as in healthcare.
Insights from the Healthcare Industry
Many in healthcare now focus more on insider threats than on threats from outside. This shows how big of a deal insider risks are for healthcare. They can really hurt the trust patients have in these places.
Healthcare is getting more aware of how bad insider threats can be. This includes data breaches or misuse by people who are supposed to be trusted.
*Inside the Surveillance Industrial Complex | America’s Surveillance State: https://youtube.com/watch?v=HMMA0rkTT04
“Data breaches and cyber incidents have a profound effect on businesses, reputations, and livelihoods.”
Most insider threats don’t get caught, which makes the problem even bigger. This means healthcare groups need strong security and training for their staff. If they don’t, they could lose patient data, face big financial losses, and damage their reputation.
Types of Internal Threats to Customer Data
Organizations face many internal threats that can harm customer data security. These threats come from insiders who steal or misuse data on purpose, and from employees who accidentally expose data. In fact, 60% of data breaches are from insiders, and small companies spend about $8.13 million on these incidents. Insider threats have jumped by 44% from 2020 to 2022.
Most insider threats, about 56%, are due to employee or contractor carelessness. The FBI got nearly 20,000 Business Email Compromise (BEC) complaints in 2021, showing how insiders can be a big risk. To fight these risks, companies should watch who can see their data. They should also train employees regularly to keep up with new threats. Using tools from managed security providers can also help spot insider attacks.
- Malicious insiders who intentionally steal or misuse sensitive information
- Careless or negligent employees who inadvertently expose data through improper handling, unauthorized access, or weak security practices
- Contractors or other insiders with legitimate access to the organization’s systems and data
Type of Internal Threat Percentage of Insider Threats Malicious insider attacks 26% Employee or contractor negligence 56%
Insider threats can come from many places, like current or past employees, contractors, and others with access to the company’s data. These threats can be intentional data theft or accidental data exposure. Verizon found that 82% of data breaches involve people, showing how big a risk insiders are.
Recent big data breaches at Uber, Cash App Investing, and the city of Calgary show how serious insider threats are. Companies need to watch insiders closely and have strong security to protect customer data.
“Insider threats affect over 34% of businesses every year, and 66% think insider attacks are more likely. Insider incidents have gone up by 47% in the last two years.”
Why Internal Threats Shouldn’t Be Ignored
Organizations often focus on fighting external cyber threats. But, they shouldn’t ignore the growing issue of insider risk. These threats come from within and can seriously harm data protection and cybersecurity. Studies show that the average loss from an insider data breach is $15 million. Also, 55% of data breaches are caused by insiders. Since 2021, there’s been a 28% jump in insider-driven data leaks.
The Growing Problem of Insider Risk
Many organizations find it hard to tackle internal threats. Even though 99% of companies say they have data leakage prevention, 78% have lost valuable data. This shows we need a better way to handle insider risks. In fact, 60% of cyber attacks involve trusted insiders. Only 7% of companies feel they have good insider threat protection.
Dealing with internal threats needs a strategy that includes more than just tech. Good Insider Threat Programs need support from top management, enough money, and teamwork from IT, HR, Legal, and Security. It’s also key to know what data is critical, set clear rules, and build a security-aware culture.
New tech like ChatGPT makes insider threats worse. 87% of security leaders worry about employees not following the rules with tools like ChatGPT. We need a strong, proactive security plan to tackle these new threats.
Ignoring internal threats can lead to big problems like data breaches and financial losses. To avoid these risks, companies must focus on managing insider threats. This means using tech, having strong processes, and building a security culture. By tackling insider risk, organizations can improve their cybersecurity and protect their valuable assets.
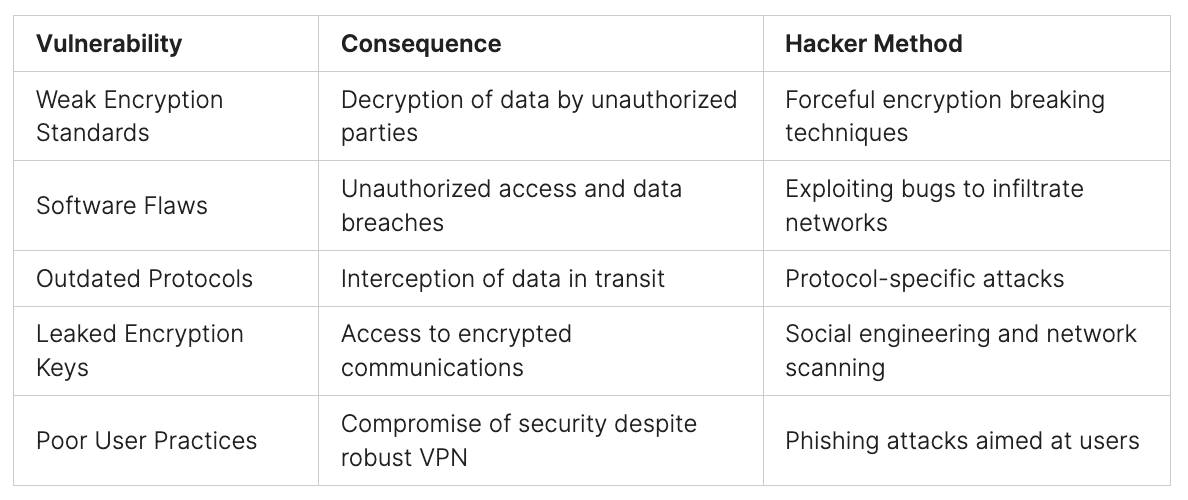
Vulnerabilities in Data Protection Measures
Protecting customer data is crucial for companies, but many don’t fully cover their data protection gaps. These gaps can come from poor access controls, not training employees enough, not watching user actions closely, and missing key data protection steps. It’s vital to fix these issues to stop insider threats from leaking customer info.
Human mistakes cause most data breaches, with 85% of them coming from this. This shows how important it is for companies to teach employees about cybersecurity. They need to know how to spot and stop phishing attacks to keep data safe. Also, new quantum computing tech could break into data, so companies must check how it affects their encrypted data.
Insider threats, like employees leaving or moving, are big risks for data. To fight this, companies need to have strict controls, like telling HR about changes and watching user actions closely. They also need to pay attention to IoT devices, which can be a weak spot in security.
Many companies don’t protect their data backups well, leaving sensitive info at risk. Using tokenization services can help keep data safe. Also, making sure data is encrypted when moving it is key, but often ignored.
Having too much data makes a company more vulnerable, making it harder to keep data safe. Companies should only collect and keep the data they really need to lessen this risk. They should also avoid using too much anonymized data, as it can be traced back to real people, and use data masking instead.
By fixing these data protection weaknesses, companies can protect customer data better and reduce risks from inside threats. This ensures the safety and privacy of important information.
Third-Party Risks and Regulatory Compliance
Companies face big risks from third-party vendors who can see sensitive customer data. Last year, 57% of manufacturers had a data breach because of these vendors. With an average of 67 vendors per company, each with many people accessing the network, the risk is high. Also, 44% of companies faced a breach due to too much access given to third parties. Not checking the security of these partners can lead to data breaches and legal problems.
Addressing Vendor Security and Legal Requirements
To lower these risks, companies need strong vendor management. Gartner says 60% of companies work with over 1,000 third parties, showing how big these networks are. It’s key to check their security regularly and make sure they follow data privacy laws. ProcessUnity is a leader in Third-Party Risk Management, showing its top performance in this area.
A big part of managing third-party risks is looking at more than just cybersecurity risks. This includes things like reputation, location, politics, strategy, money, operations, privacy, following the law, ethics, keeping business running, performance, and environmental risks. Using automation in TPRM helps with tasks like figuring out risks, picking risk owners, and sending updates.
The Third-Party Risk Management Lifecycle has steps like finding vendors, checking and picking them, assessing risks, fixing problems, making contracts, reporting, and keeping an eye on vendors. It also includes ending vendor relationships.
“Businesses today operate within extensive networks of third-party relationships, making vendor security and regulatory compliance critical priorities.”
Healthcare is often a target for cyber attacks, showing how vulnerable it is to security threats. The cost of cybercrime is expected to hit $24 trillion, showing the big financial hit from these risks. Manufacturing is a top target for cyber threats, as the World Economic Forum points out, making it a high-risk sector. Financial services and insurance were also big targets in 2022, showing the wide reach of cyber risks. The US hospitality market’s $4.1 trillion value in 2022 highlights its economic importance and the danger of cyber breaches.
Overlooked Physical Security Threats
Many organizations focus on fighting digital threats but often ignore physical security risks. Things like unsecured devices, throwing away sensitive papers, and not controlling who goes where can let insiders get to customer data and important assets.
A report pointed out the danger of water heaters near server rooms, which could cause water damage and data loss. Nathan Whittacre, CEO of Stimulus Technologies, told of a client whose office was broken into by former workers who went straight for the server room. This shows how easy it is for insiders to breach physical security. Companies often keep access and passwords for ex-employees too long, making it easier for them to cause trouble.
To fix these security gaps, simple steps like environmental monitoring systems can protect against fires, floods, or overheating. Using access control systems with keycards and cameras can also help keep offices and server rooms safe. It’s important to have a checklist for when employees leave to make sure they’re fully removed from the system.
Working together between physical security and IT teams is key to making sure both physical and cybersecurity work well together. Most organizations find moving systems and apps to the cloud hard and expensive. IT experts can make sure physical security gear works well with cloud systems and help choose the right physical security systems to keep everything secure.
It’s crucial to tackle physical security threats since most IT leaders worry about data breaches and 53% of breaches come from inside, like unauthorized access or throwing away papers the wrong way. By looking at both physical and digital security together, companies can lower the risk of insider threats and keep their important stuff safe.
Findings Percentage Organizations that suffered a data breach in the last 12 months 68% Data breaches in the healthcare sector caused by loss or stolen paper documents or devices 71% Data breaches caused by internal factors like unauthorized access or improper disposal 53% IT managers who stated that physical security isn’t optimized in their companies 77% Reported workplace injuries and fatalities due to violence in 2018 20,790 injuries and 453 fatalities
“Collaboration between physical security and IT teams leads to more effective converged security protections.”
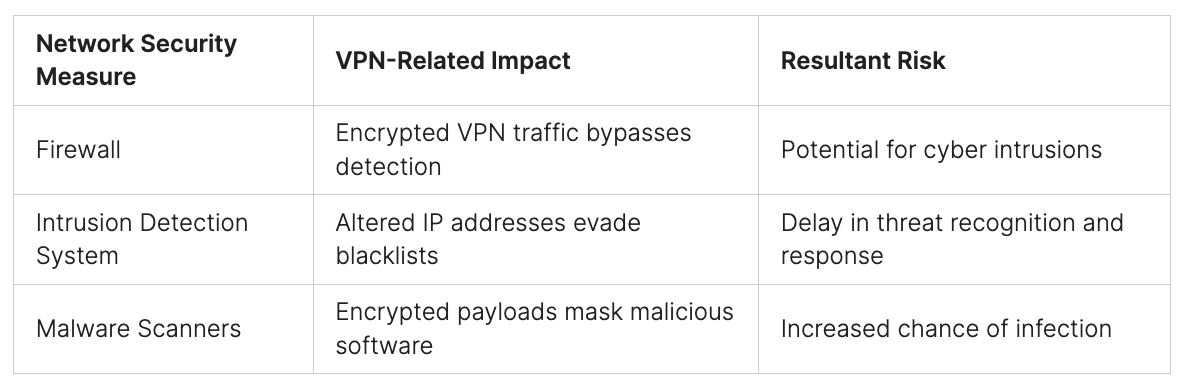
Access Management and User Behavior Monitoring
Keeping an eye on who can access what is key to stopping insider threats. Companies need strong access controls like multi-factor authentication and specific roles to keep sensitive info safe. Watching how users act, what they access, and what they do with data can spot odd behavior and insider threats.
Implementing Robust Access Controls and Analytics
Knowing what’s normal for each employee and watching for changes is vital to catch insider threats early. Deep analysis of user behavior gives insights to tackle insider risks.
Every company should focus on managing insider threats to reduce risks from both intentional and accidental insiders. To stop insider threats, companies should check new hires well, set clear rules, limit access to key info, use the least privilege model, and train employees on cybersecurity.
Training employees is key to stopping accidental insider threats. Topics can include spotting phishing emails, secure remote access, and how to act in a cyber attack. Watching for unusual actions, like unauthorized file sharing or odd network logins, can catch insider threats early.
Fostering a Culture of Security Awareness
Creating a strong security culture in the workplace is key to fighting internal threats. It’s all about employee training programs, security awareness campaigns, and sharing security policies and best practices. By teaching employees how to protect data, we make a security-conscious workforce. This team can spot and stop insider risks.
Many companies are not doing enough in this area. 40% of people said they don’t want to take security steps, and 53% haven’t had any cybersecurity training. Without security awareness, companies are open to insider threats. 41% of top leaders say their security efforts can’t keep up with new technology.
To build a strong security awareness culture, we need to make employees key players in protecting data and assets. This means regular training, fun learning activities, and clear info on security risks. By sharing the importance of security, we turn our team into a strong defense against cyber-attacks.
Building a security culture is a constant effort. It means working together and giving employees the power to act. This way, companies can improve their risk management and keep sensitive data safe.
Key Insights Statistics Motivation is the primary obstacle to employee security actions 40% of respondents identified motivation as the primary obstacle Lack of cybersecurity training for employees 53% of employees have not undergone any cybersecurity training Security initiatives not keeping pace with digital transformation 41% of executives stated that their security initiatives have not kept pace Employees unsure of reporting security incidents 45% of employees are unsure who they should report security incidents to Employees do not think they have a role in maintaining security Almost a third of employees do not think they have a role in maintaining security
“Employees should be seen as a line of defense (human firewall) against cyber-attacks, not the weakest link.”
Conclusion
Internal threats pose significant risks to companies, and overlooking them can lead to severe consequences. Malicious insiders or careless employees can expose sensitive customer data, resulting in substantial financial losses and damage to a company’s reputation.
To combat these threats, companies need a robust strategy that includes enhanced access controls, user behavior monitoring, and comprehensive employee security training. It’s equally important to assess third-party relationships and maintain strong physical security measures.
By addressing internal threats proactively, companies can better protect customer data and maintain trust with stakeholders. A clear understanding of risks allows organizations to focus on the most critical issues and avoid unnecessary disruptions.
Implementing strong security measures and adhering to cybersecurity best practices are essential in mitigating insider risks. Insider threat programs play a crucial role in detecting and preventing potential threats before they materialize, ensuring the safety of company assets.
For more insights and to explore our range of cybersecurity solutions, visit Peris.ai Cybersecurity. Safeguard your organization against internal and external threats with Peris.ai‘s comprehensive services and expertise.
FAQ
What are internal threats and why are they a significant concern for organizations?
Internal threats come from people inside an organization who act maliciously or carelessly. These actions can lead to data breaches and harm the company’s reputation. It’s vital for companies to understand and tackle these threats.
How concerned are healthcare organizations about insider cybersecurity threats?
Healthcare organizations are very worried about insider threats, scoring an 8.2 out of 10. A survey showed 52% of those in business and clinical roles are very concerned. Also, 43% think insider threats are a bigger worry than external ones.
What are the different types of internal threats that can compromise customer data?
There are many internal threats, like malicious insiders who steal data on purpose. Others are careless employees who accidentally expose data. These threats can come from current or former staff, contractors, and others with access to the company’s systems.
Why is the growing problem of insider risk often overlooked by organizations?
Companies often focus more on threats from outside. But insider threats are hard to spot and stop because they come from within. This makes them a big risk for organizations.
What are some common vulnerabilities in data protection measures that leave organizations susceptible to insider threats?
Many companies don’t protect their data well. They might not control access properly, train employees enough, or watch user behavior closely. They also might not have a strong plan to protect data. Fixing these issues is key to keeping customer data safe.
How can third-party relationships and physical security vulnerabilities contribute to insider threats?
Working with third-party vendors can be risky if they don’t protect data well. Not checking their security can lead to breaches. Also, not securing devices, throwing away documents wrong, and not controlling access to certain areas can be dangers from within.
What are the key measures organizations can take to mitigate insider threats?
To fight insider threats, managing access and watching user behavior is key. Use strong access controls and watch for unusual actions. Teaching employees about security is also important to stop threats from within.