Supervisory Control and Data Acquisition (SCADA) systems are key to running critical infrastructure around the world. They help manage things like energy, water, manufacturing, and transportation. These systems make sure everything runs smoothly and efficiently.
But, SCADA systems are now more connected, making them easier targets for cyber attacks. With more remote access and internet use, they face more threats. If hacked, SCADA systems could lead to big problems, like messing with water supplies or shutting down power.
Key Takeaways
- SCADA systems are vital for managing critical infrastructure in many industries.
- More connections and remote access have made SCADA systems more vulnerable to cyber threats.
- Attacks on SCADA systems can cause serious disruptions and even loss of life.
- Fixing SCADA cybersecurity issues needs a detailed plan, including updates to old systems and better controls.
- Using the best security measures, like keeping systems visible and integrated, is key to protecting SCADA systems.
Introduction to SCADA Systems
SCADA (Supervisory Control and Data Acquisition) systems are key in many critical industries. They help improve how things work and keep systems running smoothly. These systems use computers, networks, and user interfaces to manage processes.
They also use special controllers to work with machines and plants. This helps companies save money, be more flexible, and work better.
What is a SCADA System?
A SCADA system is a network of parts that work together. It includes sensors, control devices, and a central system. This system collects data, analyzes it, and helps operators make good choices.
SCADA systems are used in many fields. These include food and drink, pharmaceuticals, water management, and more.
Importance of SCADA Systems in Critical Infrastructure
SCADA systems are vital for keeping critical infrastructure running well. They help monitor and control things like power grids and water treatment. This ensures services keep running and work better.
But, SCADA systems can be at risk of cyber attacks. These attacks can harm operations and infrastructure.
“SCADA security is crucial due to the vulnerabilities that can be exploited by cybercriminals, hackers, insider threats, and even terrorists.”
It’s very important to protect SCADA systems from cyber threats. A successful attack could harm businesses, communities, and national security.
Cyber Threats to SCADA Systems
The threat to Supervisory Control and Data Acquisition (SCADA) systems is growing. Recent attacks on critical infrastructure show how vulnerable and dangerous these systems are.
Recent Cyber Attacks on SCADA Systems
In February 2021, hackers hit a water treatment plant in Florida. They got into the system and tried to change the water’s chemical levels, making it unsafe. This shows how serious cyber threats can be for SCADA systems, which are key to our infrastructure.
Cybercriminals and state actors have been targeting SCADA systems in many areas. This includes manufacturing, energy, water, and commercial facilities. In 2020, the number of ICS vulnerabilities went up by 24.72%, with 449 new ones in the second half of the year.
More than 70% of ICS vulnerabilities in 2020 were high-risk, with scores of 7.0 or higher. Most of these can be exploited through the network and don’t need special conditions.
Consequences of Successful Cyber Attacks
Attacks on SCADA systems can cause big problems. They can disrupt services, change how things work, or mess with data. These issues can lead to safety risks, environmental harm, and big economic losses.
Groups like Hexane and Xenotime have been targeting sectors like oil and gas, water, and energy. The damage from these attacks can be huge. This shows why we need strong cybersecurity for SCADA systems and the infrastructure they protect.
Challenges in SCADA Cybersecurity
SCADA systems are key for managing critical infrastructure but face big cybersecurity challenges. One major issue is their legacy, built decades ago without security in mind. These old systems lack modern security tools like encryption and authentication. This makes them open to threats like hacking, viruses, worms, and denial-of-service attacks.
Legacy Systems and Outdated Technologies
SCADA systems rely on old technologies, which is a big cybersecurity challenge. These systems were made for reliability and functionality, not security. They don’t have the security features needed to fight off today’s cyber threats. Upgrading or replacing these systems is hard and expensive, adding to the security challenge.
IT/OT Convergence and Attack Surface Expansion
The blending of IT and OT systems in SCADA is another big challenge. This blending adds more ways for cyberattacks, making SCADA systems more at risk. IT security tools don’t work well in OT environments because of their unique needs. This makes it harder to protect SCADA systems.
To tackle these challenges, we need a wide-ranging approach. Good SCADA cybersecurity plans include thorough risk assessments, strong defense strategies, and regular updates. They also need secure remote access, and training for employees.

“One of the most complex security challenges in implementing SCADA systems is ensuring that the system is secure against unauthorized access.”
What Are SCADA Systems and How to Protect Them from Cyber Threats
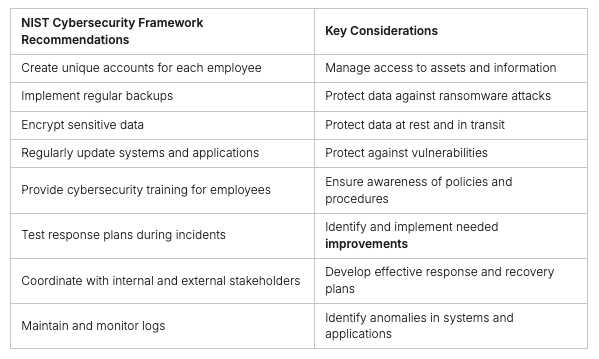
Supervisory Control and Data Acquisition (SCADA) systems are key to keeping critical infrastructure running smoothly. They help organizations make better decisions and reduce downtime. But, as they connect more, they face a growing risk of cyber attacks.
Recent breaches show the need for strong SCADA cybersecurity. It’s important to keep up with the changing cyber threats. By knowing the weaknesses and using the right security steps, we can protect our systems.
SCADA Cybersecurity Strategies for Critical Infrastructure Protection
Securing SCADA systems needs a mix of technical and human steps. Here are some key strategies:
- Use strong network segmentation to keep critical areas safe from outside threats.
- Keep software up to date with security patches to lower cyber attack risks.
- Boost SCADA security with firmware updates and secure coding.
- Do regular security checks to find and fix weaknesses.
- Use strict access controls and secure encryption to protect against SCADA threats.
- Train staff well to create a strong defense against cyber threats.
By taking a proactive and layered approach to SCADA security, we can keep our systems safe from cyber threats.
“Securing SCADA systems is not a one-time task, but an ongoing process that requires continuous vigilance and adaptation to the evolving threat landscape.”
SCADA Cybersecurity Best Practices
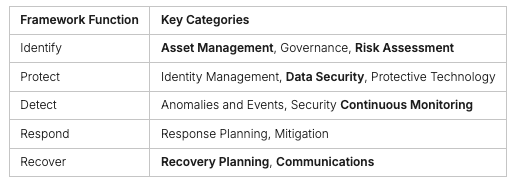
Security experts have created best practices to help organizations improve SCADA security. These practices focus on understanding the ICS environment, combining IT and OT security, and applying IT security to ICS. This helps address the unique challenges of industrial control systems and cyber-physical systems.
Gain Visibility into Your ICS Environment
Getting a full view of SCADA systems is key to securing them. SCADA systems have hardware like sensors and software for data management. Understanding this complex setup is vital for spotting vulnerabilities and threats.
Integrate Existing IT Tools and Workflows with OT
Organizations should link their IT security tools with OT. This can use network segmentation and strong authentication. It helps extend IT security to ICS, giving a better view of cyber-physical systems.
Extend IT Security Controls and Governance to ICS
It’s important to apply IT security to ICS. This includes network segmentation and access controls. Regular audits and employee training are also crucial. This way, organizations can protect their industrial infrastructure better.

“Comprehensive visibility, integrated IT-OT security, and extended governance are the cornerstones of effective SCADA cybersecurity.”
By following these best practices, organizations can make their industrial control systems more resilient. They can also reduce cyber threats and ensure their critical infrastructure operates securely.
Identifying and Evaluating SCADA Network Connections
Securing SCADA systems starts with knowing the network connections that could be at risk. The first step is to do a detailed risk analysis. This helps figure out which connections are necessary and which pose risks to the SCADA network.
Next, map out all connections, both inside and outside the network. This includes local networks, wide area networks, the internet, wireless devices, and links to business partners or regulatory agencies. By making a detailed list, organizations can focus on the most critical connections.
Then, use penetration testing and vulnerability analysis to check the security of these connections. This helps find weak spots and plan a strong defense strategy.

By checking SCADA network connections, organizations can better understand their risks. They can then plan a strong security strategy to protect their critical systems from cyber threats.
“Securing SCADA systems is a continuous process that requires a proactive and comprehensive approach. Identifying and evaluating network connections is the first crucial step in this journey.”
Hardening SCADA Networks
Protecting SCADA systems from cyber threats is key. Hardening SCADA networks is a major strategy. It involves proactive steps to reduce attack surface and enhance security across the SCADA infrastructure.
Removing Unnecessary Services and Connections
The first step is to remove unnecessary services and connections. This reduces vulnerabilities. Isolating the SCADA network from the internet lowers the risk of unauthorized access.
Implementing Security Features and Protocols
Organizations should implement the latest security features and protocols. This includes secure communication protocols like MQTT with TLS and client authentication. Protocols like DNP3 and Modbus with Security Extensions also offer encryption and data prioritization for secure data transmission.
Network segmentation and access control are also essential. This divides the SCADA network into subnetworks, limiting entry points for attackers. Role-based access control (RBAC) and multi-factor authentication (MFA) further enhance security by restricting access and verifying user identities.
Regular patching and updates are vital for SCADA network hardening. They address known vulnerabilities and reduce cyber threats. Intrusion detection systems (IDS) monitor for suspicious activities and provide early warnings.
Organizations should conduct regular security audits and assessments. These involve simulated scenarios and penetration tests. Assessments provide reports on vulnerabilities and recommendations for improvement, helping organizations enhance SCADA network security.
By taking a comprehensive approach to SCADA network hardening, organizations can reduce cyber threats. They protect their critical infrastructure and ensure the secure operation of their SCADA systems.
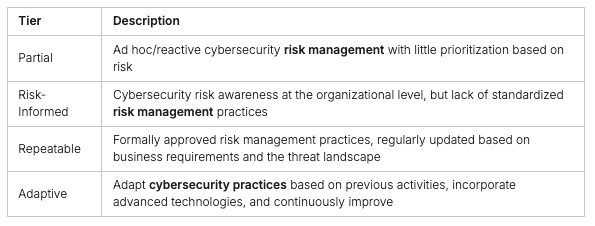
Risk Management and Defense-in-Depth Approach
SCADA cybersecurity needs a strong risk management process and a defense-in-depth strategy. It’s important to know what cybersecurity is needed, manage configurations well, and check for risks regularly.
Using a layered security approach is key. This means having many security controls at different levels to fight off various threats and keep systems cyber resilient. It includes rules, physical barriers, and technical tools to build a strong defense-in-depth strategy.
- Administrative controls are about policies, procedures, and training to lower risks.
- Physical controls help by locking down access to IT systems, like server rooms.
- Technical controls are the tools and services used to tackle security issues.
By using a defense-in-depth approach, companies can build strong security layers. This protects their vital SCADA systems and keeps them operationally resilient.

“Implementing a defense-in-depth strategy is crucial for ensuring the cyber resilience of critical SCADA systems and protecting against a wide range of cyber threats.”
Establishing Policies, Training, and Accountability
Protecting SCADA systems from cyber threats needs a complete plan. Senior leaders must set clear scada cybersecurity policies and make sure everyone follows them. It’s also key to have security awareness training for all. This training helps everyone know their part in keeping SCADA systems safe and understand the value of protecting sensitive info.
Having strong organizational accountability is vital for SCADA cybersecurity success. Well-defined roles, clear responsibilities, and strict rules for not following them create a secure culture. Regular checks, tests, and drills are needed to see if security policies work and find ways to get better.
- Make detailed scada cybersecurity policies that cover access, response to incidents, data safety, and following rules.
- Start security awareness training to teach people why SCADA system security is important and their roles in it.
- Put in place organizational accountability steps, like reviews and penalties, to make sure everyone sticks to security rules.
By having strong policies, good training, and a culture of organizational accountability, companies can greatly improve their SCADA system’s cybersecurity. This helps protect their critical infrastructure.
Conducting Audits and Assessments
Keeping SCADA systems safe and reliable is key. Regular security checks and assessments are vital. They should be done with the help of trusted third-party experts.
Technical Audits and Penetration Testing
Technical audits and penetration testing are crucial for SCADA security. They check the SCADA network, devices, and systems for vulnerabilities. Penetration testing mimics real attacks to find weaknesses and test security controls.
Physical Security Surveys and Remote Site Assessments
It’s also important to check the physical security of SCADA systems and remote sites. Physical security surveys look at access controls and surveillance. Remote sites need to be secure too, as they can be attack points.
Through these audits and assessments, organizations can understand their SCADA security better. They can find and fix weak spots. This makes their critical systems more secure.
“Regular security audits, penetration testing, and incident response plans are crucial elements in maintaining the security posture of SCADA systems.”
Working with skilled security experts for these assessments is very helpful. They offer valuable advice to protect against cyber threats.
Incident Monitoring and Disaster Recovery
To keep SCADA systems safe from cyber threats, organizations need strong incident monitoring and disaster recovery plans. Good SCADA incident response starts with constant monitoring. This lets teams quickly spot and fix security problems.
It’s key to watch SCADA systems all the time. This lets security teams tackle threats as they happen. Adding intrusion detection systems inside and outside helps a lot. It makes sure all bases are covered and responses are fast.
Organizations should also plan for disaster recovery and business continuity. These plans help lessen the blow of cyber attacks. They make sure important systems and services keep running.
Regular checks, like vulnerability scans and penetration tests, are very important. They find weak spots that hackers might use. Also, dividing networks and using strong access controls, like two-factor authentication, stop hackers from moving around and getting in where they shouldn’t.
Keeping software and firmware current is also key. It helps block known weaknesses that hackers might try to use. By always being ready and fixing security issues, organizations can make their SCADA systems stronger. This ensures they can keep delivering vital services.
“Cybersecurity is not a one-time event, but rather a continuous process of adaptation and improvement. By staying vigilant and implementing robust incident monitoring and disaster recovery strategies, organizations can effectively protect their SCADA systems and the critical infrastructure they support.”
Conclusion
SCADA systems are the backbone of many industries, such as manufacturing and energy, playing a vital role in controlling and monitoring critical operations. Since their inception in the 1960s, these systems have become more sophisticated and widely used.
However, with increased connectivity comes heightened vulnerability. SCADA systems now face more cyber threats than ever, risking disruptions to crucial operations and the integrity of sensitive data. To counter these risks, organizations need robust SCADA cybersecurity strategies.
Focusing on SCADA cybersecurity, safeguarding critical infrastructure, and proactively addressing cyber threats is essential for maintaining the safety of these vital systems. Staying vigilant and continually enhancing SCADA security measures is key to protecting the systems that support our modern world.
For tailored solutions and expert guidance on securing your SCADA systems, visit Peris.ai Cybersecurity. Let’s build a safer, more resilient future together.
FAQ
What are SCADA systems?
SCADA (Supervisory Control and Data Acquisition) systems manage and control processes. They use computers, networks, and user interfaces. They also include devices like PLCs and PID controllers to work with machinery.
Why are SCADA systems important for critical infrastructure?
SCADA systems are key in managing critical infrastructure like energy and water. They make operations more efficient, reduce downtime, and improve reliability.
What are the key cyber threats to SCADA systems?
SCADA systems face new cyber threats due to their increased connectivity. Cyberattacks have grown, causing disruptions and safety concerns. They can manipulate data and control processes.
What are the main challenges in SCADA cybersecurity?
SCADA systems are vulnerable due to outdated tech and the blending of IT and OT. Traditional security tools often can’t protect OT environments well.
What are the best practices for improving SCADA cybersecurity?
To improve SCADA security, start with a risk analysis. Isolate the network and harden it. Use a defense-in-depth strategy and clear policies. Regularly audit and monitor for incidents.